From RAMP to Ransom: Dissecting THE GENTLEMEN’s Operational Footprint
THE GENTLEMEN is a rapidly expanding ransomware operation that entered the cybercriminal landscape in mid-2025 and quickly established itself as an aggressive, service-driven enterprise. Unlike opportunistic extortion crews, the group presents itself as a structured RaaS provider, promoting high affiliate payouts, flexible build options, and multilingual outreach to attract a global pool of partners. Their victim set, spanning healthcare, manufacturing, education, construction, and other critical industries, shows no clear vertical preference, suggesting an operation that prioritizes scale over specialization.
What distinguishes THE GENTLMEN is the combination of minimal operational infrastructure and deliberate communication discipline. The group relies on a streamlined ecosystem centered around a dark-web leak site and Tox-based contact, projecting an image of efficiency while limiting their exposure footprint. As their activity accelerates, these design choices offer valuable insight into how the group organizes its services, engages affiliates, and maintains consistency across attacks.
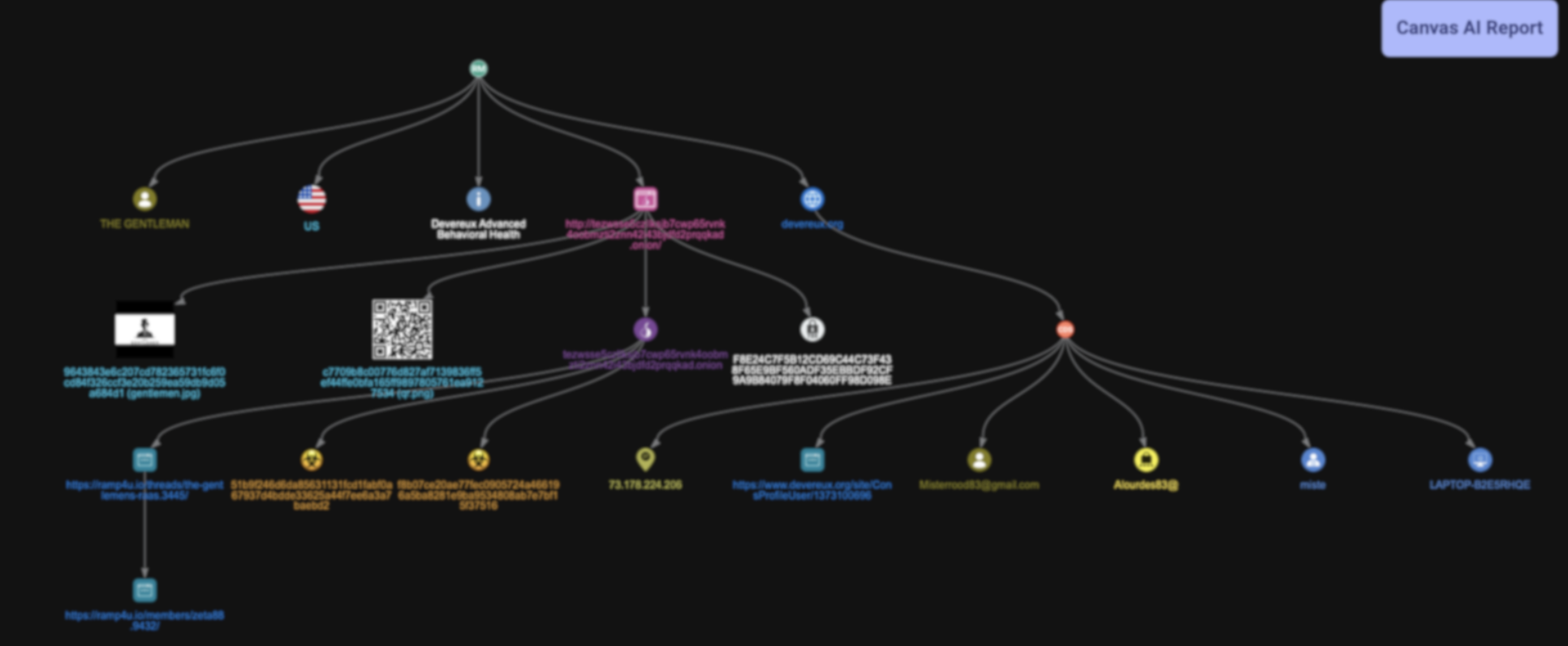
This report consolidates these evidence points into a structured mapping of THE GENTLEMEN’s infrastructure, capturing how their leak site, communication channels, malware artifacts, and affiliate processes intersect to form a functioning RaaS operation.
Incident Trigger & Initial Discovery
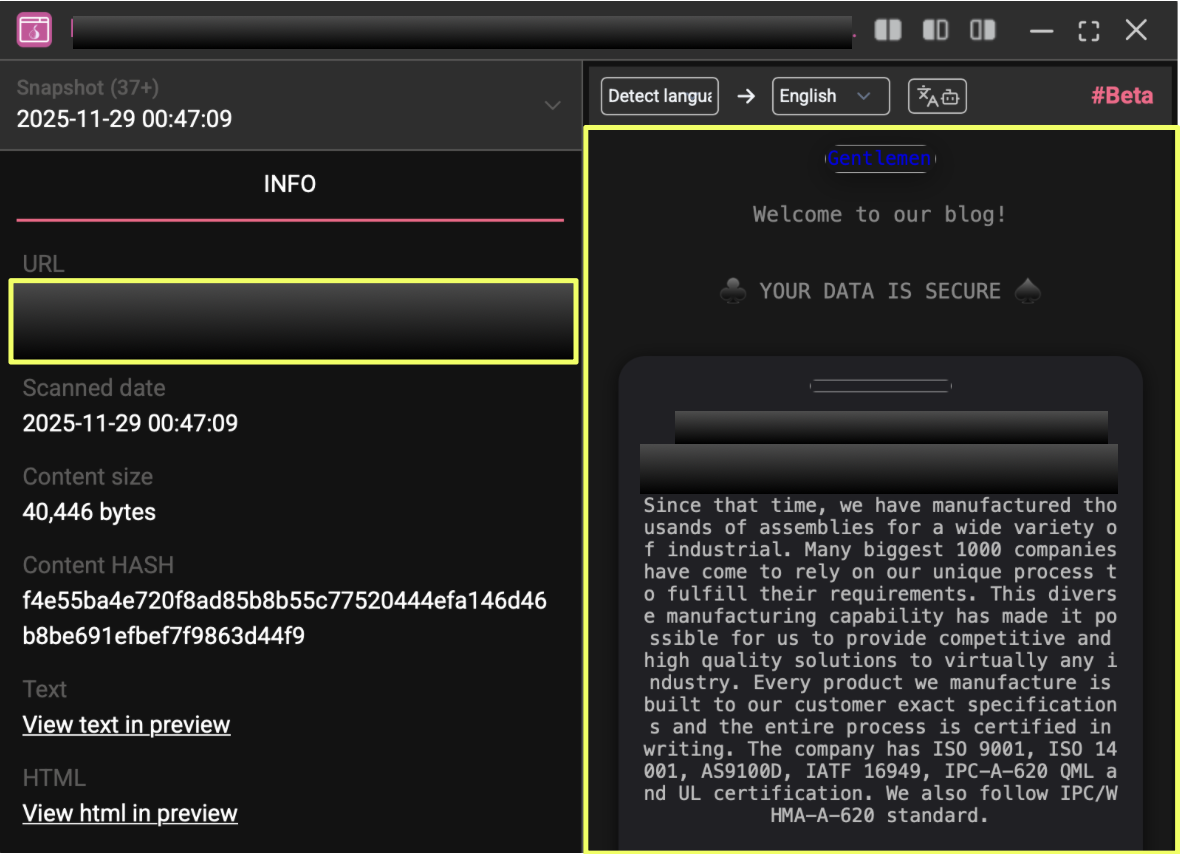
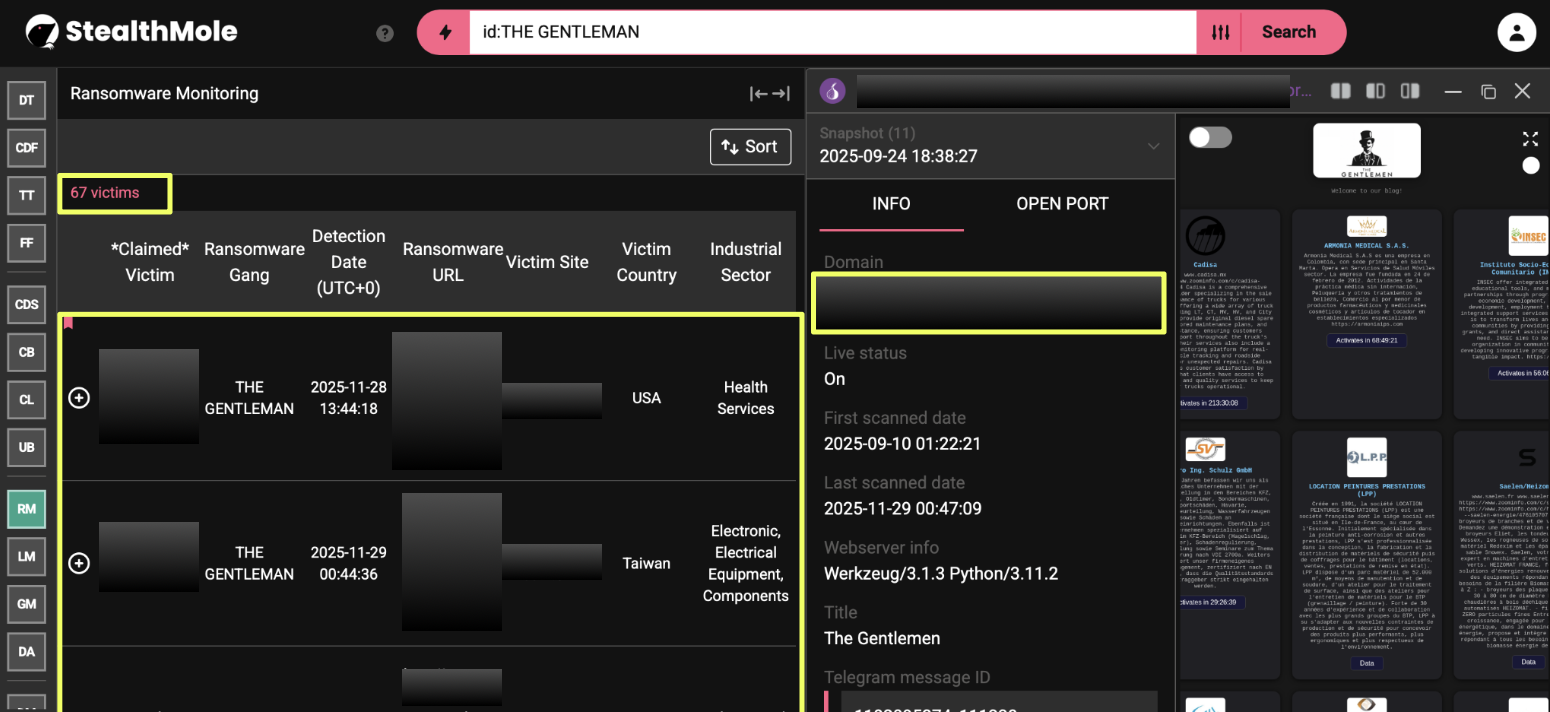
THE GENTLEMEN entered StealthMole’s radar again on 28 November 2025, when the Ransomware Monitoring module indexed a new victim in the healthcare sector. The listing matched the group’s established naming and publication pattern, marking the latest addition to their fast-expanding activity footprint. This detection reaffirmed that the operators remained active and continued publishing on their dedicated leak site.
- http://tezw**************************************qkad.onion/
This incident is part of a wider surge attributed to THE GENTLEMEN throughout mid-2025 onward, during which StealthMole has recorded 67 confirmed attacks across diverse sectors including healthcare, manufacturing, education, construction, and insurance. The consistent cadence of new victims suggested a structured operation rather than sporadic targeted breaches.
The late-November case provided a natural starting point for deeper analysis. Using the newly indexed entry as the pivot, the investigation expanded to examine how the group maintains its leak-site presence, organizes its victim disclosures, and signals ongoing activity. This incident served as the most recent indicator of their operational tempo and opened the path for mapping the broader ecosystem that supports THE GENTLEMEN’s ransomware service.
Infrastructure Mapping
Leak-Site Structure
THE GENTLEMEN maintains a dedicated dark-web leak site, which serves as the central hub for publishing victim announcements. The domain shows a consistent, template-driven layout used across all disclosed incidents. Each victim appears in a standardized card format, suggesting the group relies on an automated or semi-automated system for preparing and releasing posts. The site presents itself as a stable, long-term asset rather than a disposable service, which is typical of RaaS groups seeking to project reliability to affiliates.
- http://tezw*************************************qkad.onion/
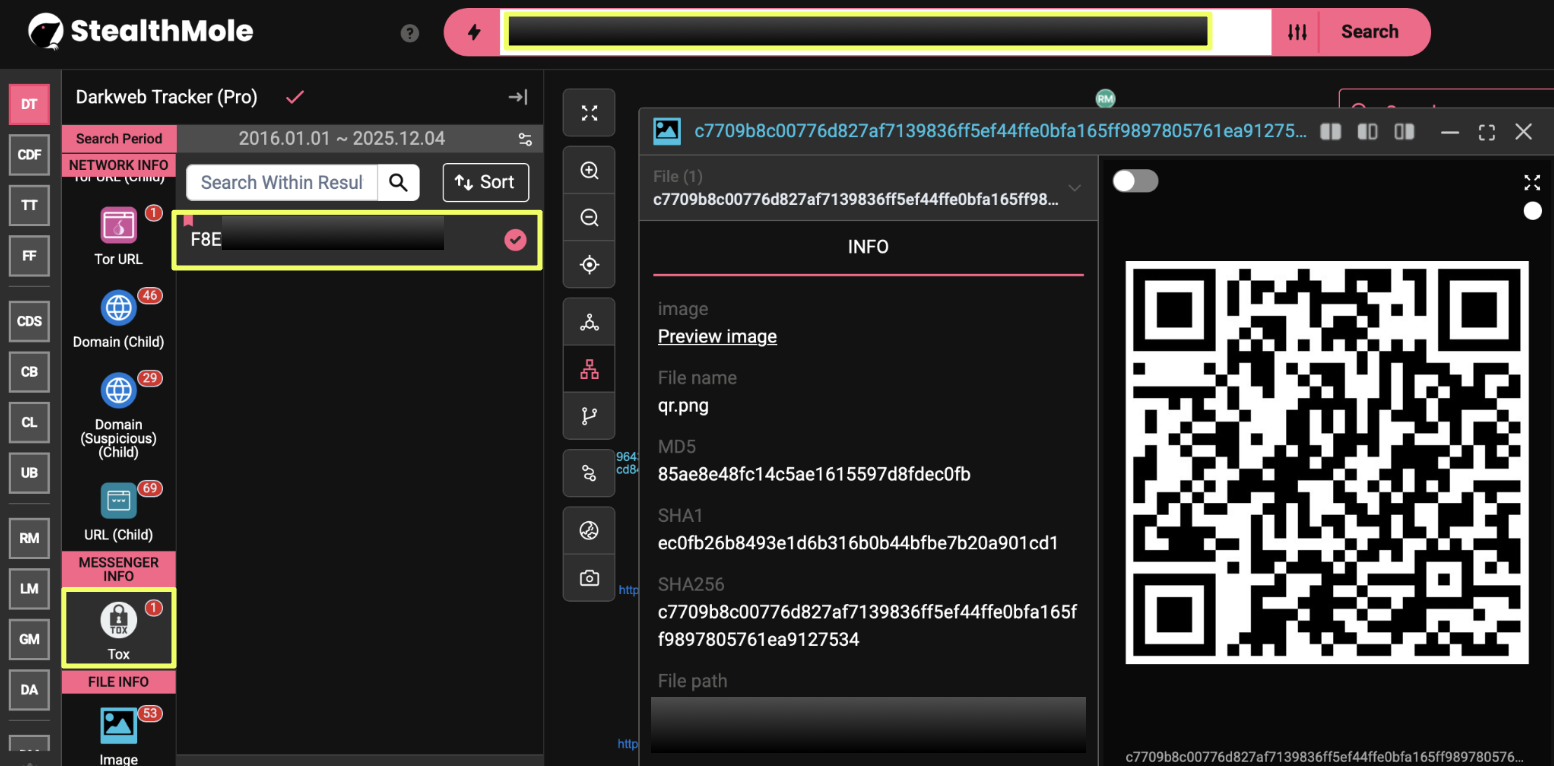
Communication Layer
The leak site includes a single visible communication channel: a TOX identifier presented directly on the page. The group does not use embedded chat portals or external negotiation panels, relying instead on a decentralized messaging system that limits traceability and infrastructure overhead.
- F8E248****************************************************98E
A QR code is also hosted on the site, providing an alternative route for initiating contact. While the encoded content has not yet been analyzed, its placement indicates the group expects victims or intermediaries to rely on multiple self-directed communication options. Together, these elements reflect a deliberate design aimed at keeping their operational footprint minimal while maintaining accessibility.
File Artifacts and Malware Indicators
StealthMole’s inspection of the leak site identified two malware-related hashes associated with the Gentlemen’s infrastructure:
- f8b07ce20ae77fec0905724a466196a5ba8281e9ba9534808ab7e7bf15f37516
- 51b9f246d6da85631131fcd1fabf0a67937d4bdde33625a44f7ee6a3a7baebd2
These hashes indicate the presence of executable components or malware-adjacent files tied to the group’s online infrastructure. While the underlying files were not retrieved, their association with the leak site suggests that THE GENTLEMEN stores or references operational tools alongside their disclosure content. The presence of these artifacts supports the assessment that the site functions not only as a publication platform but also as a staging point within their broader ecosystem.
Leak-Site Activity Pattern
The leak site hosts victims from multiple sectors and retains past entries rather than cycling them out, creating a cumulative record of attacks. This persistent listing model aligns with the group’s reported activity volume, with 67 victims observed since mid-2025. The consistency of formatting and the recurrence of the same communication elements across different posts indicate a centralized process for preparing disclosures. The addition of the most recent healthcare-sector case in late November 2025 fits seamlessly into this pattern, reinforcing the conclusion that the leak site is a controlled, continuously managed asset integral to THE GENTLEMEN’s RaaS operation.
Actor Ecosystem & RaaS Model
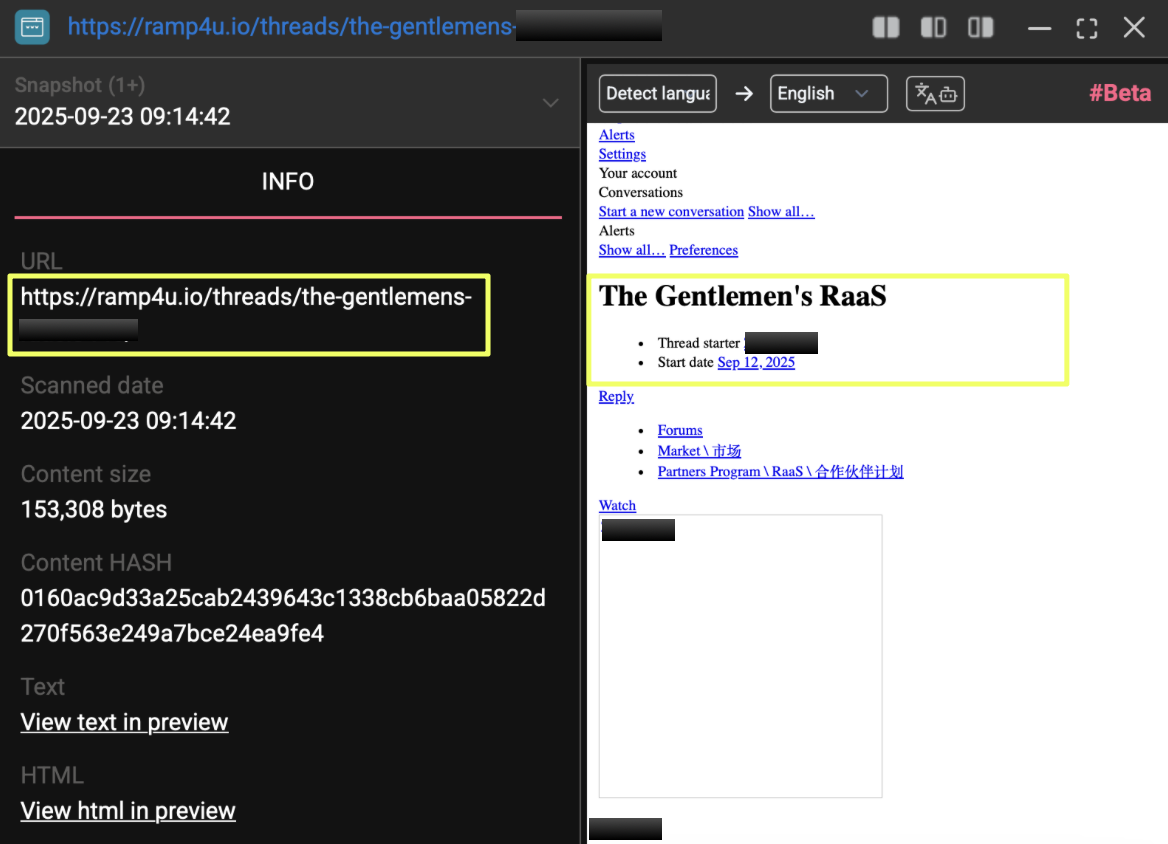
Affiliate Recruitment and Positioning on RAMP
THE GENTLEMEN articulate their service model openly through a recruitment thread posted on the RAMP cybercrime forum by a user operating under the handle “Z*****8”. The post, created on 12 September 2025, is presented in English, Russian, and Chinese, indicating an intent to attract a broad pool of affiliates rather than limiting themselves to a specific regional audience. The multi-language format also suggests that the group anticipates participation from operators with varying levels of technical maturity, and therefore seeks to make their offering accessible from the outset.
The thread is unambiguous in its purpose: THE GENTLEMEN present themselves as a RaaS provider and invite “teams and solo pentesters” to collaborate. This offers clear insight into how the group views its ecosystem, affiliates execute intrusions, while the core operators supply tooling, infrastructure, and publication channels. Notably, the leak-site URL was also mentioned in this recruitment post, establishing an explicit link between the group’s dark-web presence and their underground advertising efforts.
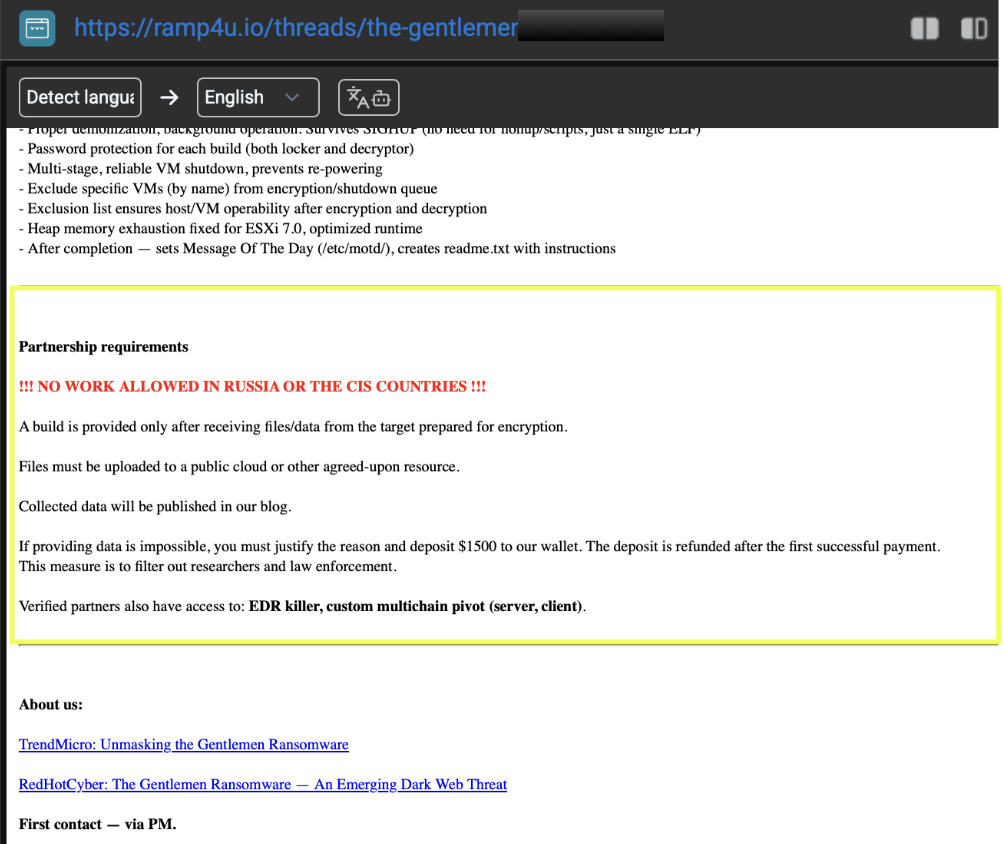
Operational Model and Partner Requirements
The group’s RaaS model is structured around a straightforward financial arrangement: affiliates retain 90% of ransom proceeds, while THE GENTLEMEN collects the remaining share. This high payout aligns with recruitment strategies used by newer RaaS programs seeking rapid expansion and market penetration. To maintain control over the operational workflow, the group requires partners to provide files or data from intended targets before receiving a build. If this is not possible, the affiliate is expected to justify the limitation and pay a $1500 deposit, which they state is refunded after the first successful payment. According to the post, this requirement exists to screen out researchers and law-enforcement actors attempting to access the tooling.
The recruitment thread also outlines a geographical restriction: affiliates are prohibited from conducting operations in Russia or the CIS region. This is a common rule in cybercriminal communities but is presented by THE GENTLEMEN as an explicit operational boundary. The presence of such restrictions, combined with their screening deposit, reflects a structured attempt to control the behavior of affiliates and minimize unwanted exposure.
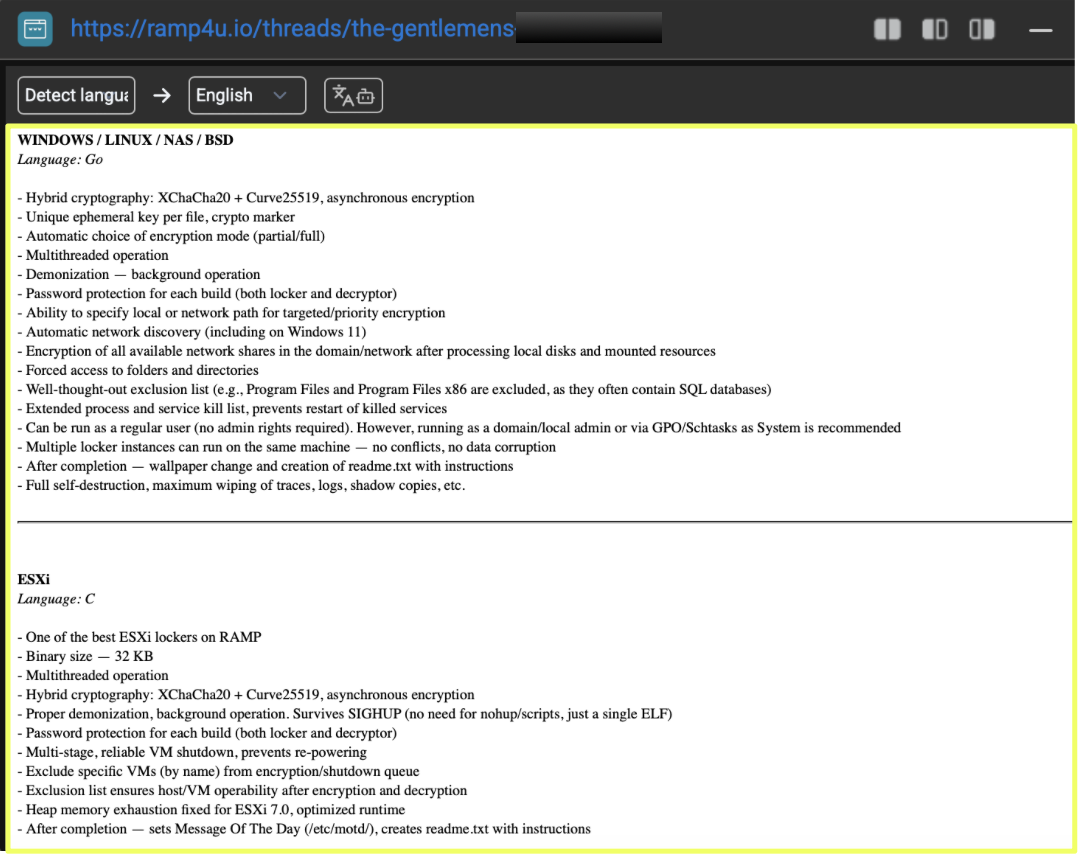
Technical Capabilities as Advertised
The thread provides a high-level overview of the ransomware tooling THE GENTLEMEN supply to their affiliates. The operators emphasize that multiple operating systems are supported, including Windows, Linux, NAS environments, BSD-based systems, and ESXi hosts. They describe their locker variants as multi-threaded, capable of running without elevated privileges, and designed to function reliably across different deployment scenarios. The listing also references features such as ephemeral encryption keys, self-deletion behavior, network-aware functionality, and the ability to operate as multiple lockers within a single system.
For affiliates who qualify for deeper collaboration, THE GENTLEMEN offer additional tooling, including an EDR killer and a custom pivoting solution. Although the post does not provide technical detail beyond naming these components, their inclusion demonstrates that the core operators seek to present themselves not merely as ransomware developers but as full-service providers capable of supporting lateral movement and defense evasion when necessary.
Assessment
THE GENTLEMEN operate with an intentionally narrow digital footprint, maintaining only a single leak site and a TOX-based communication channel while avoiding the broader cybercriminal ecosystems where many ransomware groups sustain their presence. Their absence from platforms such as Telegram, underground chat communities, or multi-domain leak mirrors reflects a conscious strategy to limit exposure and control the environments in which they interact. This minimal surface does not indicate immaturity; rather, it reveals a calculated model where leanness is used as a protective measure. With fewer communication assets and auxiliary platforms, there are fewer points at which operational details can leak, be monitored, or be disrupted.
Within this constrained footprint, the discovery of malware hashes linked directly to the leak-site environment is particularly important. Ransomware leak sites often function only as publication channels, but the presence of executable-linked indicators tied to THE GENTLEMEN’s infrastructure suggests that operational components and disclosure infrastructure may coexist within the same ecosystem. This introduces an additional dimension to the group’s architecture: the leak site is not merely a staging point for victim announcements but may also reflect aspects of how their tooling is distributed, tested, or organized internally. Even without retrieving the underlying files, the association of these hashes with the group’s domain gives analysts a starting point for correlating THE GENTLEMEN’s tooling with external malware databases, sandbox reports, or unrelated intrusions where these hashes may later surface. Such cross-correlation is a critical component in mapping a RaaS operation whose operators deliberately limit their outward communications.
Despite their limited footprint, THE GENTLEMEN have maintained a high operational tempo, with 67 recorded victims since mid-2025 across a wide range of sectors. Their infrastructure behaves with the predictability of a controlled service rather than a loose affiliate collective: a single leak site, consistent formatting, a uniform communication method, and a recruitment model that favors stability and screening over broad outreach. The combination of a streamlined infrastructure and steady attack volume indicates a mature operation that has chosen discretion over visibility. At the same time, their dependence on a small number of assets creates inherent vulnerabilities; if their leak site becomes inaccessible, their communication pathways and public-facing presence are significantly diminished.
Overall, THE GENTLEMEN’s behavior reflects a deliberate effort to balance growth with operational discipline. Their minimal external presence makes attribution and monitoring more difficult, while the malware-related indicators discovered within their leak-site ecosystem offer rare, meaningful entry points into tracking their tooling and internal workflows. Together, these elements reinforce the view of a group that seeks efficiency and concealment, maintaining a scalable RaaS model without adopting the broader communication networks used by more prominent ransomware brands.
Conclusion
THE GENTLEMEN’s emergence reflects a shift toward ransomware operations that prioritize controlled exposure over broad visibility. Their infrastructure is compact, deliberately curated, and built to function with as few external dependencies as possible. Even with this limited footprint, the group has managed to establish a steady operational rhythm and attract affiliates, demonstrating that visibility is not a prerequisite for impact. What stands out most in this case is the presence of technical artifacts, such as the malware hashes identified within their leak-site environment, that offer rare insight into a group that otherwise reveals very little about its internal mechanisms.
This investigation shows that small, stable infrastructure choices can still support large-scale ransomware activity when combined with consistent tooling and predictable disclosure practices. For defenders and analysts, this means detection opportunities may come less from the group’s outward communications and more from subtle technical markers that surface during monitoring. Continued tracking of THE GENTLEMEN will rely on identifying these quiet signals, as the group’s streamlined design leaves few other entry points into their operations.
Editorial Note
As with all dark-web investigations, the findings presented here reflect what could be observed and correlated at the time of analysis. Threat-actor infrastructure is fluid, often shifting without warning, and visibility into hidden services is never absolute. This report illustrates how StealthMole helps analysts to work within those limitations, piecing together meaningful insights from constrained data points and identifying operational patterns in groups that intentionally keep their footprint small.
To access the unmasked report or full details, please reach out to us separately.
Contact us: support@stealthmole.com
Labels: Ransomware


.svg)
.svg)
.svg)