Gunra’s Expanding Footprint: Ransomware Activity, Data Hosting, and Cross-Network Infrastructure
Gunra emerged in 2025 as a ransomware actor that does not fit neatly into the typical leak-site-and-extortion model. While its operations clearly involve ransomware deployment and data encryption, Gunra also maintains a parallel ecosystem focused on hosting and organizing exposed data under the label of “public data.” This dual posture, combining ransomware activity with persistent data hosting, sets Gunra apart from many short-lived or single-purpose ransomware groups.
Between April 2025 and December 2025, Gunra demonstrated sustained operational activity, targeting organizations across multiple sectors and regions. Rather than relying exclusively on public pressure through countdown timers or negotiations, Gunra invested in infrastructure that allowed long-term storage, categorization, and presentation of victim data. This infrastructure included Tor-based leak sites, dedicated chat portals, and communication identifiers reused across environments.
One of the most notable aspects of Gunra’s operation is its consistent effort to frame leaked material as non-ransom or legally obtained “shared” data. Despite this positioning, the exposed content observed during this investigation includes internal databases, billing systems, government-issued identification documents, and ransomware-encrypted files. These contradictions suggest deliberate narrative control rather than accidental mislabeling.
This report documents Gunra’s activity through a focused investigation initiated by a ransomware leak targeting a South Korean university. Using StealthMole’s ransomware monitoring and dark web tracking capabilities, the objective of this case is to reconstruct Gunra’s operational footprint, map its infrastructure, and assess how ransomware execution, data exposure, and communication channels intersect within a single threat actor ecosystem.
Incident Trigger and Initial Investigation
The investigation began on 29 December 2025, when StealthMole’s ransomware monitoring tool indexed a new ransomware leak attributed to Gunra. The listing identified a South Korean educational institution as a victim. The leak referenced internal university data and was hosted on Gunra’s Tor-based infrastructure.
- http://gunra****************************************4ad.onion/
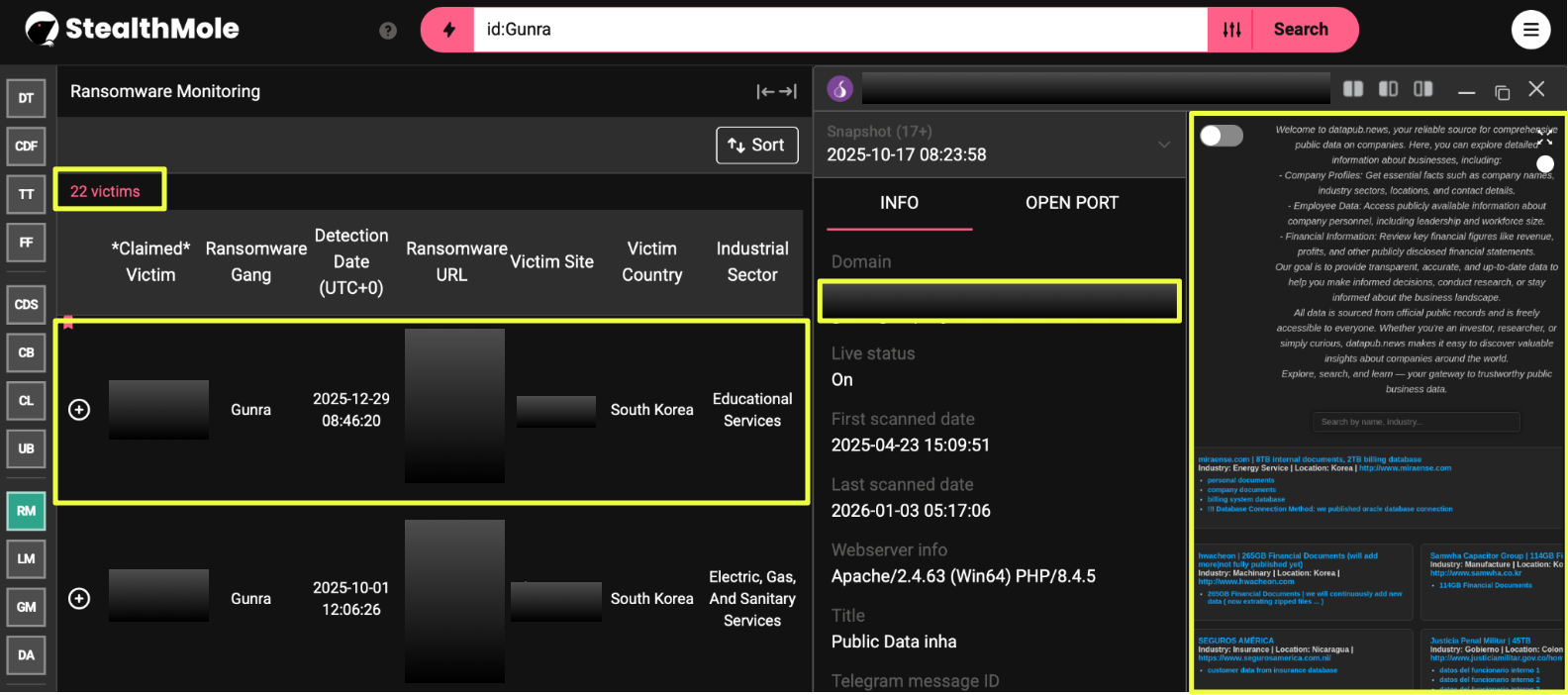
StealthMole’s ransomware monitoring further revealed that this incident was not isolated. Historical data showed that Gunra had targeted 22 victims between April 2025 and December 2025, indicating an active and ongoing operation rather than a single campaign. The time distribution of these incidents suggested operational continuity and a maintained infrastructure rather than sporadic attacks.
Initial inspection of the victim university directory showed database-related artifacts, including references to exported tables, sample records, and screenshots intended to demonstrate data access. Although the site explicitly stated that the data was “not related to any data breach or ransom,” the terminology used such as “internal main database” and “huge personal information database”, warranted deeper examination of Gunra’s broader activity.
Gunra Leak Infrastructure and Data Hosting
The primary Gunra leak site functions as a structured repository rather than a simple announcement page. Victim data is organized into directories by organization name, with subfolders containing database exports, document archives, screenshots, and sample files.
- http://gunra****************************************4ad.onion
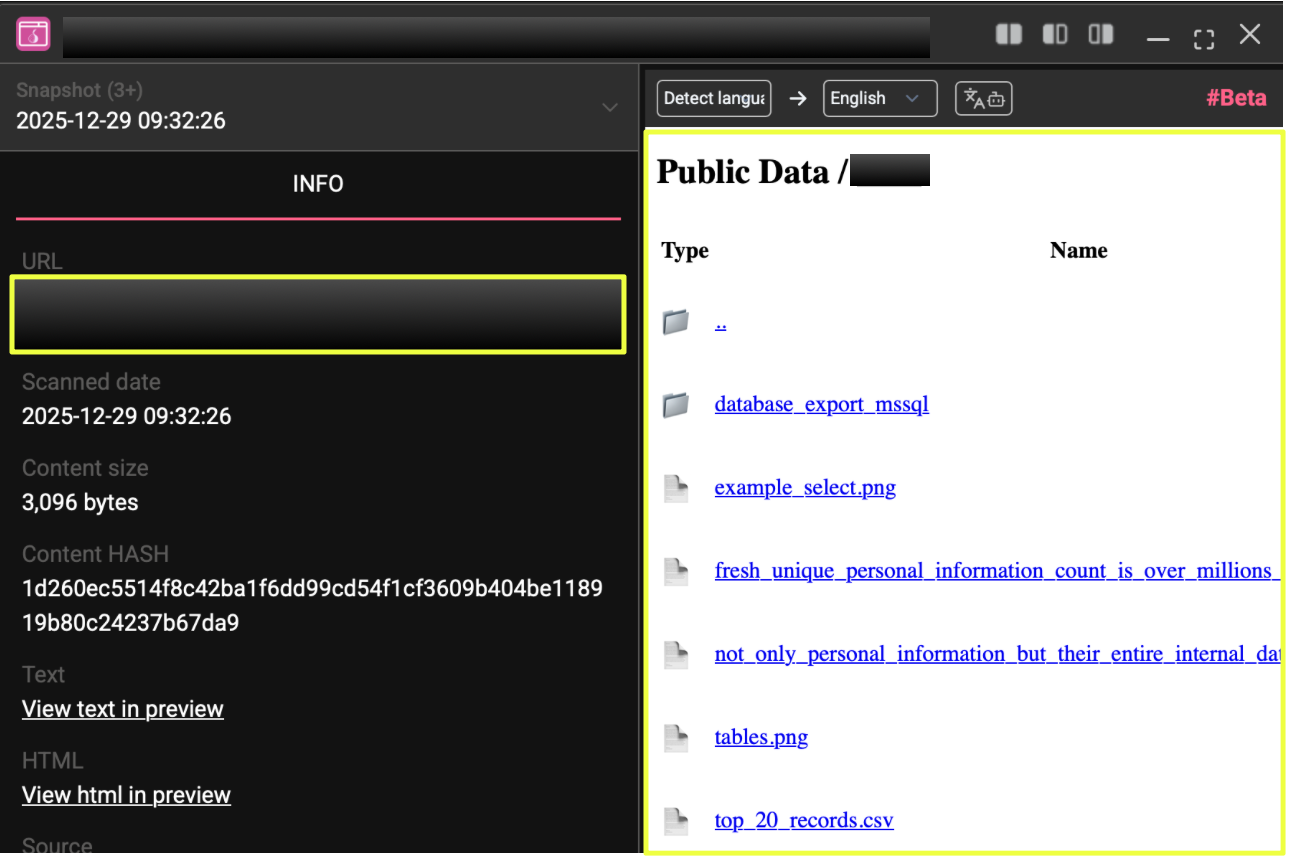
Within the university directory, the content included database export folders, image files showing table structures, and CSV samples of selected records. These materials appeared curated to demonstrate backend access rather than surface-level scraping. The consistent layout and naming conventions across directories indicate a standardized process for preparing and publishing victim data.
Beyond the South Korean university, the same leak infrastructure hosted data associated with organizations in other regions and sectors. The site’s persistent availability and repeated updates suggest that Gunra treats data hosting as a long-term operational component rather than a temporary pressure tactic.
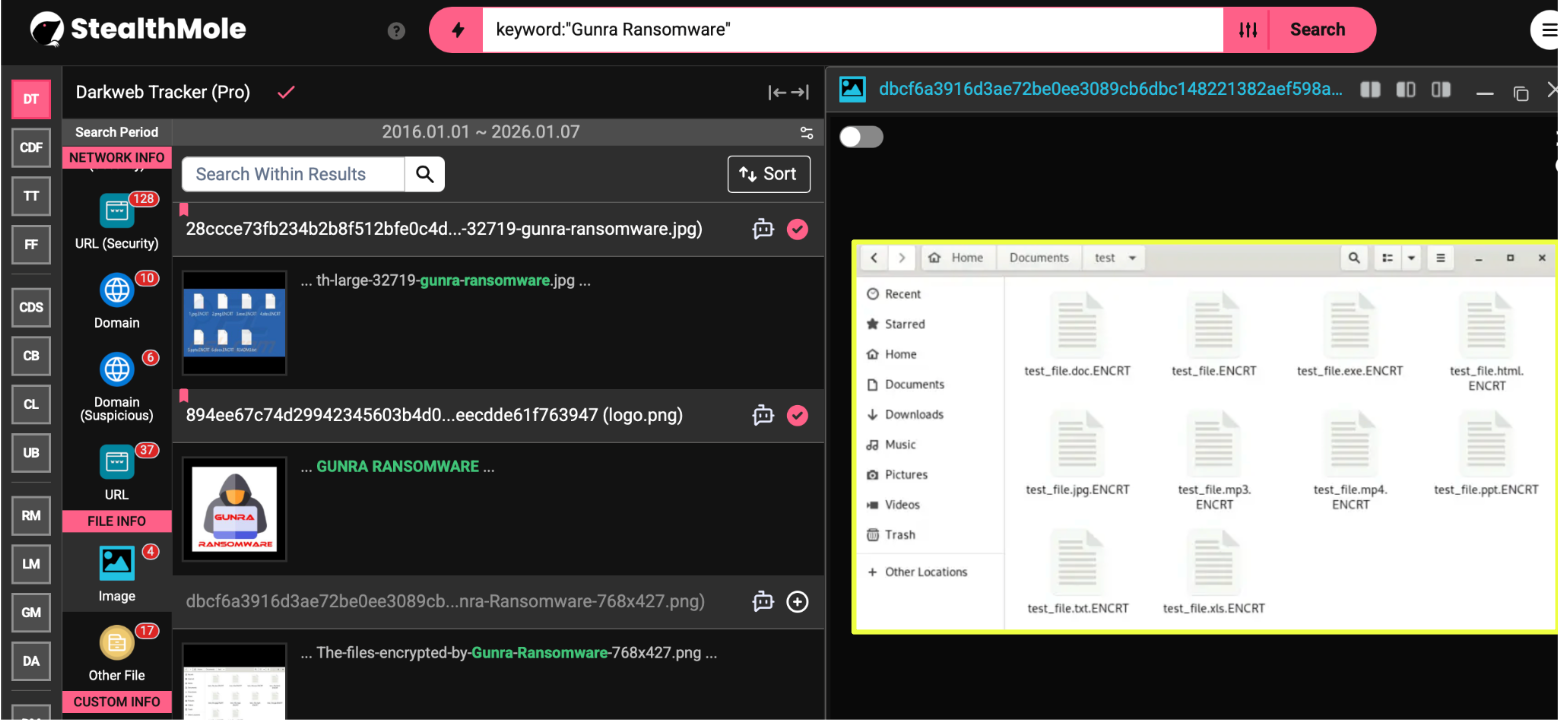
Notably, ransomware artifacts were also observed in connection with Gunra’s activity. Files encrypted with the .ENCRT extension and the presence of a ransom note named R3ADM3.txt were identified, reinforcing that encryption-based attacks are an active part of Gunra’s methodology, not merely implied.
Malware Artifacts and Chat Infrastructure Correlation
Using StealthMole’s dark web tracker, the investigation next pivoted from Gunra’s leak infrastructure toward executable artifacts associated with the operation. This process identified three distinct malware hashes that were directly linked to Gunra-controlled environments:
- 6d59bb6a9874b9b03ce6ab998def5b93f68dadedccad9b14433840c2c5c3a34e
- a82e496b7b5279cb6b93393ec167dd3f50aff1557366784b25f9e51cb23689d9
- 854e5f77f788bbbe6e224195e115c749172cd12302afca370d4f9e3d53d005fd
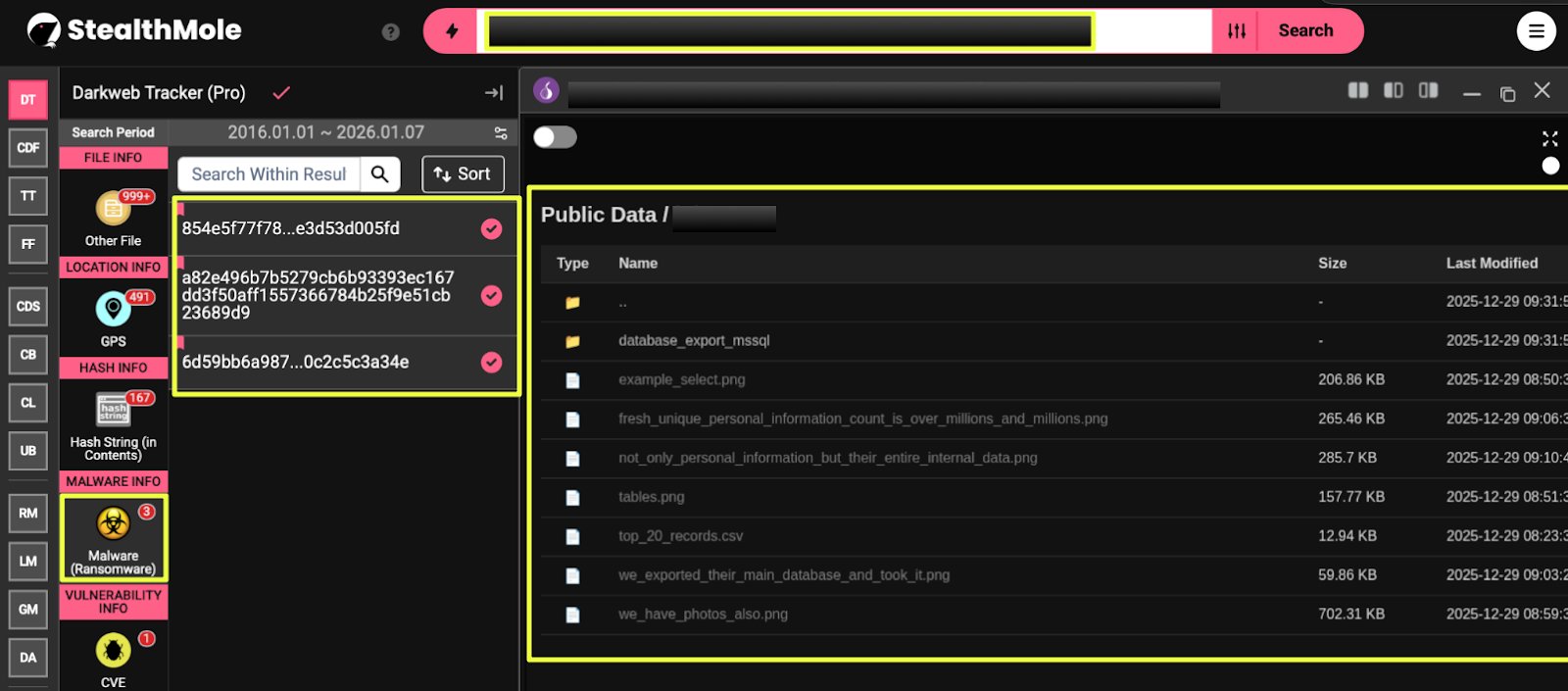
These hashes are significant because they move the investigation beyond surface-level leak site observation and into executable-level evidence. Rather than relying solely on what Gunra claims to host or publish, the presence of malware artifacts provides confirmation that ransomware deployment is an operational component of the group’s activity. This is particularly important given Gunra’s repeated attempts to frame its data as unrelated to breaches or ransom activity.
Pivoting on these hashes revealed infrastructure overlap with two Tor-based chat servers:
- http://apdk7hpbbquomgoxbhutegxco6btrz2ara3x2weqnx65tt45ba3sclyd.onion
- http://jzbht********************************************xqd.onion
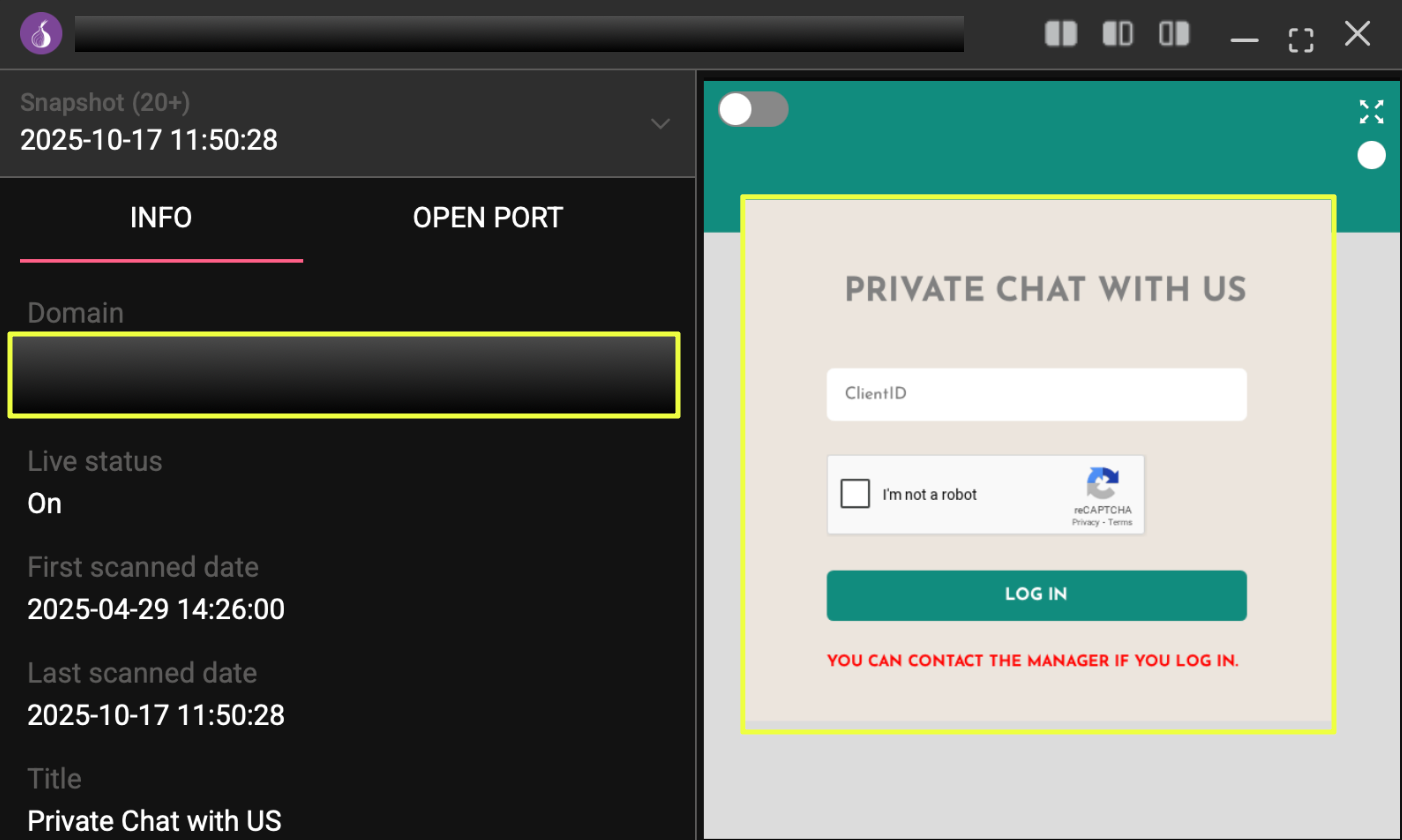
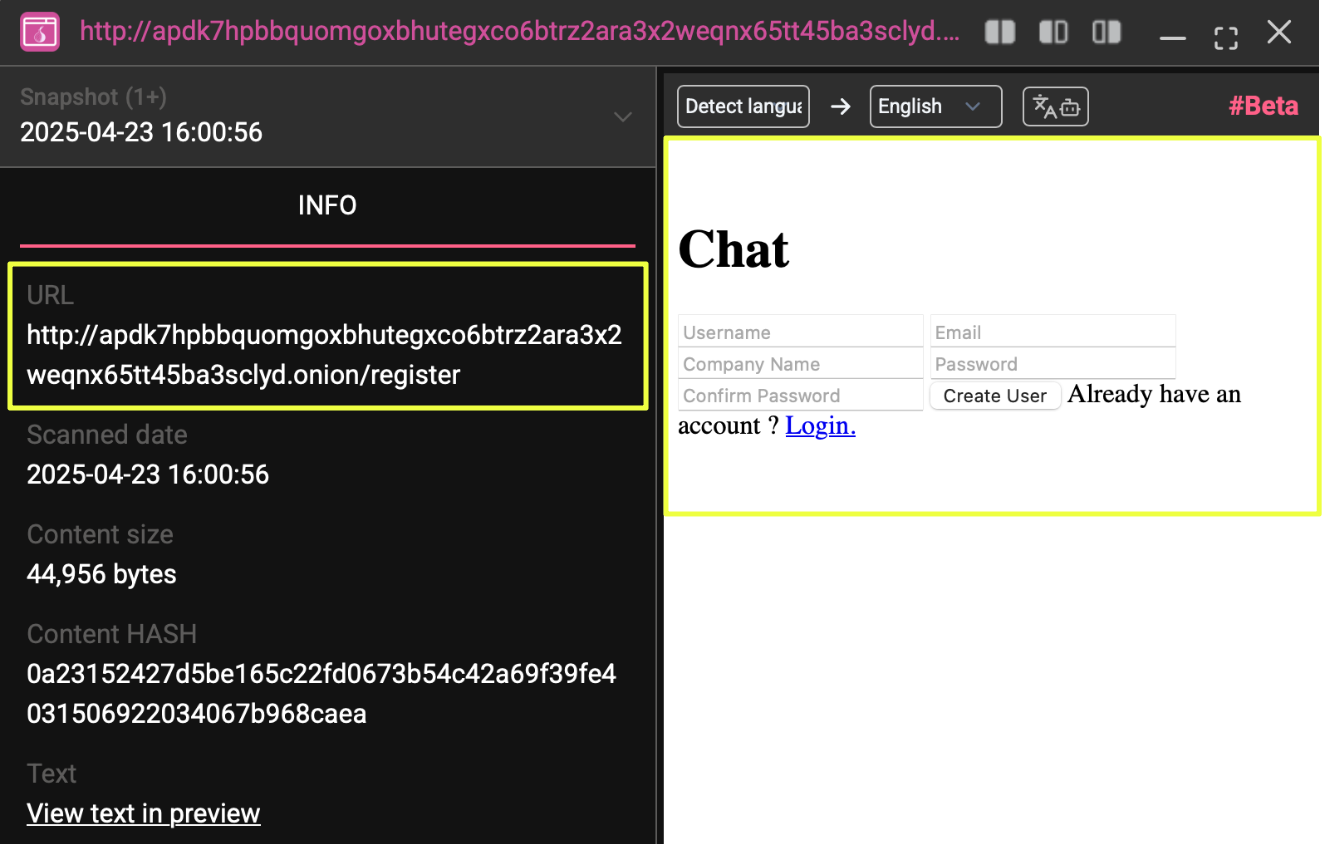
The correlation between malware hashes and communication infrastructure is a high-value intelligence finding. It demonstrates that the same operational ecosystem responsible for hosting victim data is also tied to channels used for negotiation or contact. This linkage reduces ambiguity around attribution at the infrastructure level, even without identifying individual operators.
One of the chat servers explicitly presented itself as a controlled “Private Chat with Us” portal rather than a public negotiation page. This design choice suggests Gunra favors selective, managed communication over open victim engagement, aligning with its broader strategy of minimizing public extortion theatrics while maintaining leverage through data exposure.
From an intelligence perspective, these malware-to-chat correlations are particularly valuable because they provide durable pivot points. Even if Gunra removes victim listings or rotates leak domains, malware hashes and associated communication servers often persist longer and reappear across campaigns. Tracking these artifacts enables continued monitoring of Gunra’s activity beyond individual incidents, strengthening long-term visibility into the group’s operations.
Communication Identifiers and Cross-Network Exposure
Further analysis of the Gunra leak site uncovered a TOX identifier:
- 2507318**************************************************B22
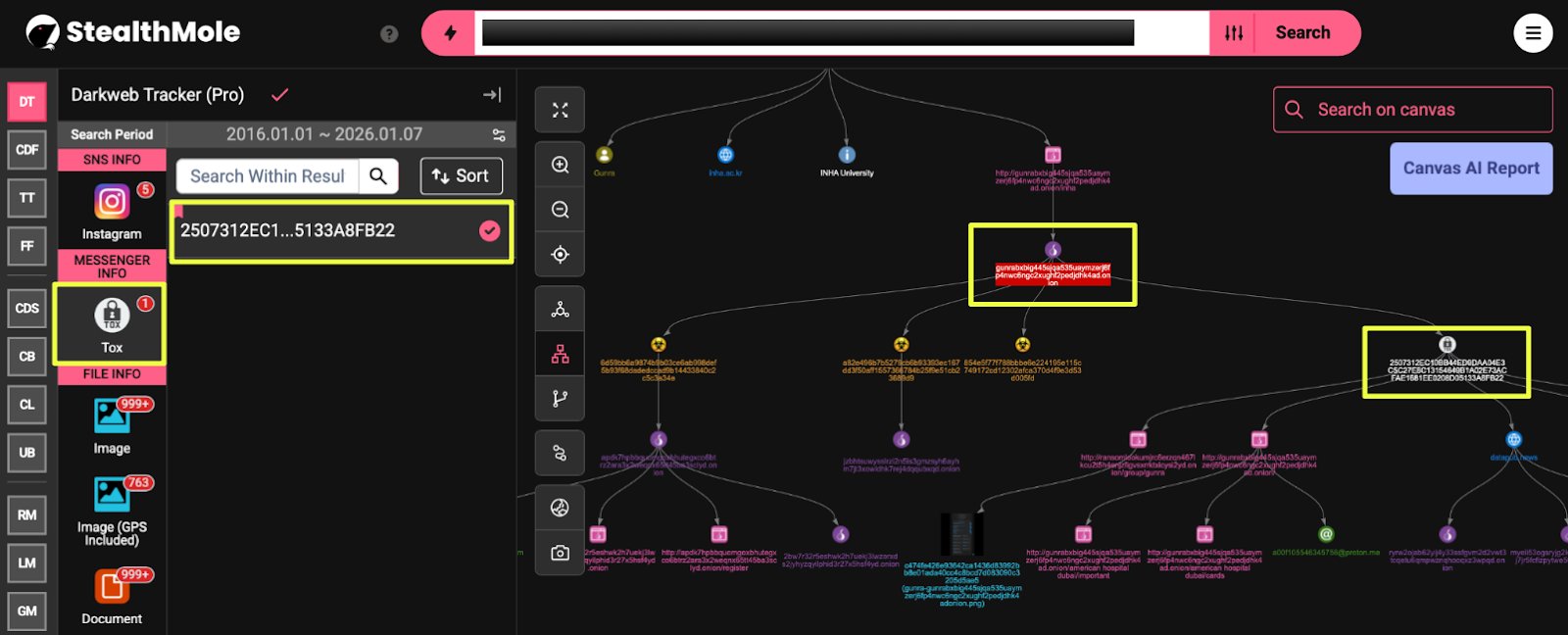
Pivoting on this TOX ID led beyond Tor-only infrastructure. Two surface-accessible websites were identified:
- https://86.**.**.**6
- https://d*******.n***s
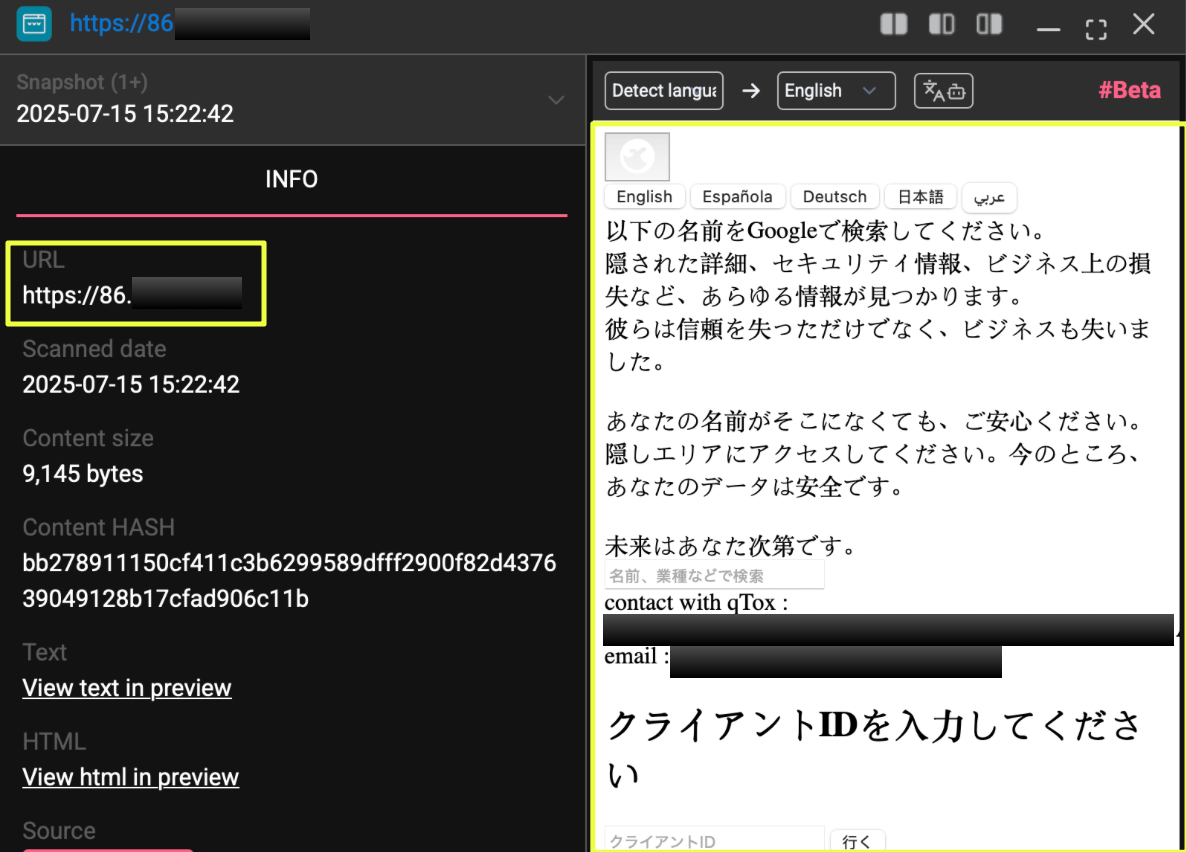
The site at https://d*****.*****s presents itself as a public business information platform, claiming to aggregate data from official public records. However, further investigation revealed that this domain was linked to additional Tor sites displaying the same language, layout, and victim references observed on Gunra’s leak infrastructure.
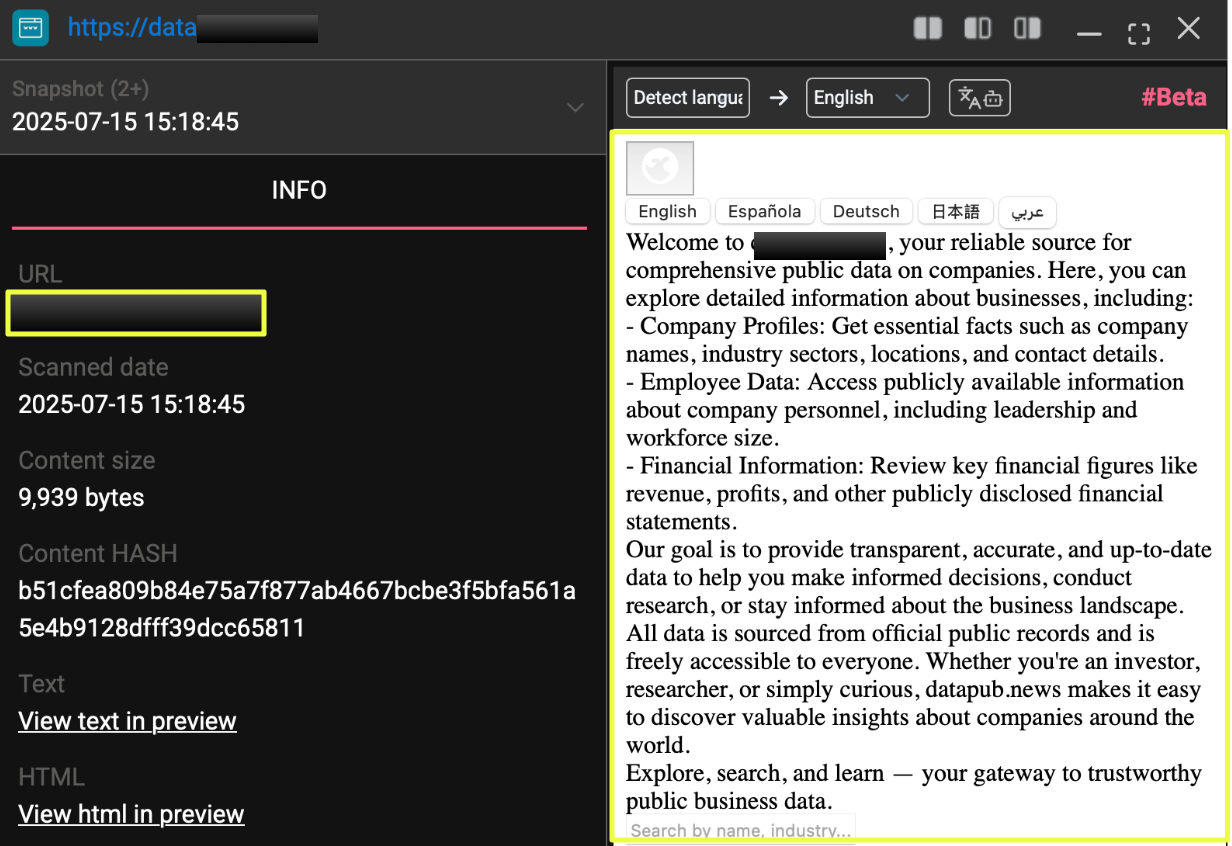
These associated onion domains included:
- ryrw2************************************************pqd.onion
- tgsst************************************************5ad.onion
- myeli************************************************xyd.onion
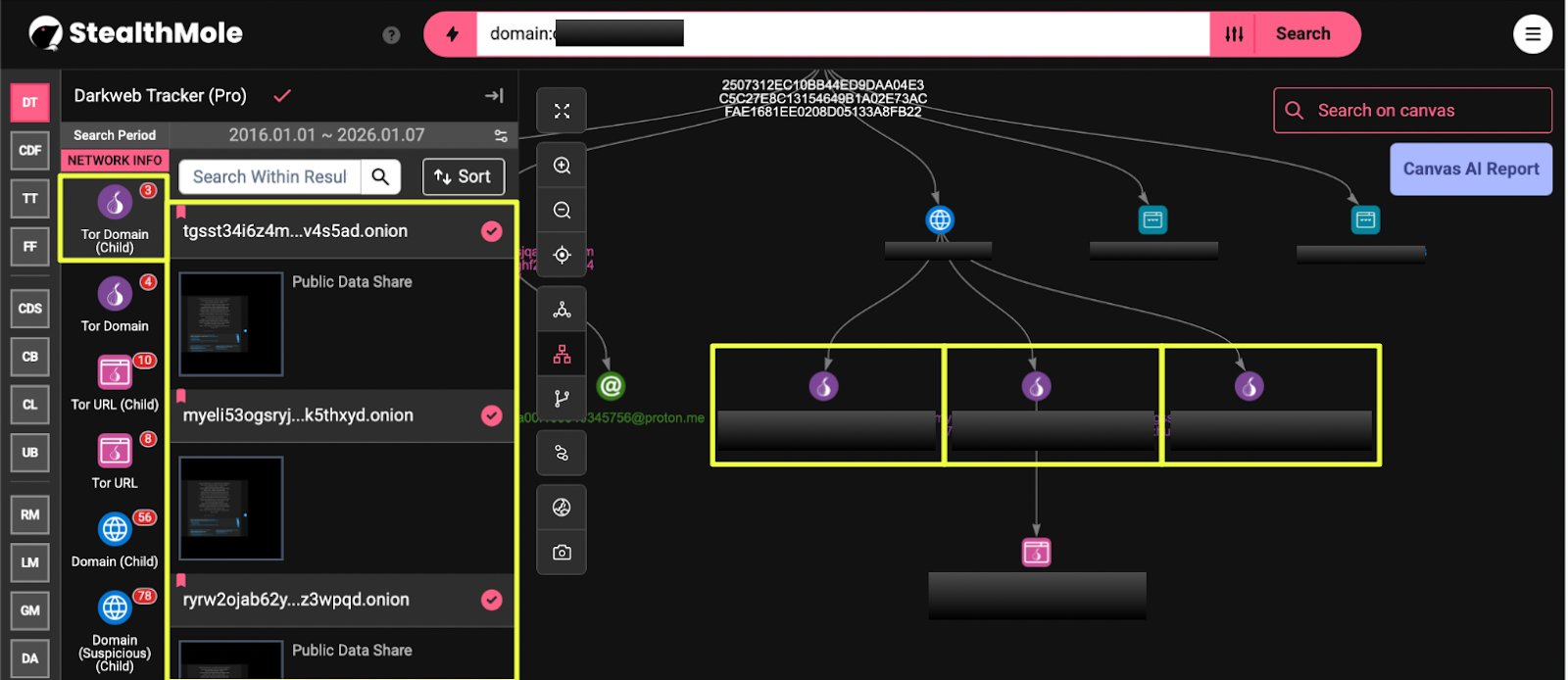
All three sites displayed “Public Data Share” branding and hosted content referencing internal corporate documents and databases. The reuse of presentation style and content across these domains suggests coordinated deployment rather than independent activity.
An additional email address, a0********6@proton.me, was also identified in association with Gunra’s infrastructure, further expanding the set of communication channels tied to the operation.
High-Impact Target: Dubai Hospital
Among the 22 identified victims, a Dubai Hospital stood out due to the nature and sensitivity of the exposed data. Dedicated directories hosted on Gunra’s infrastructure contained a range of files associated with the hospital.
Observed content included:
- Government-issued identification documents (Emirates ID PDFs)
- Passport files
- Personal photographs
- Spreadsheet files containing individual records
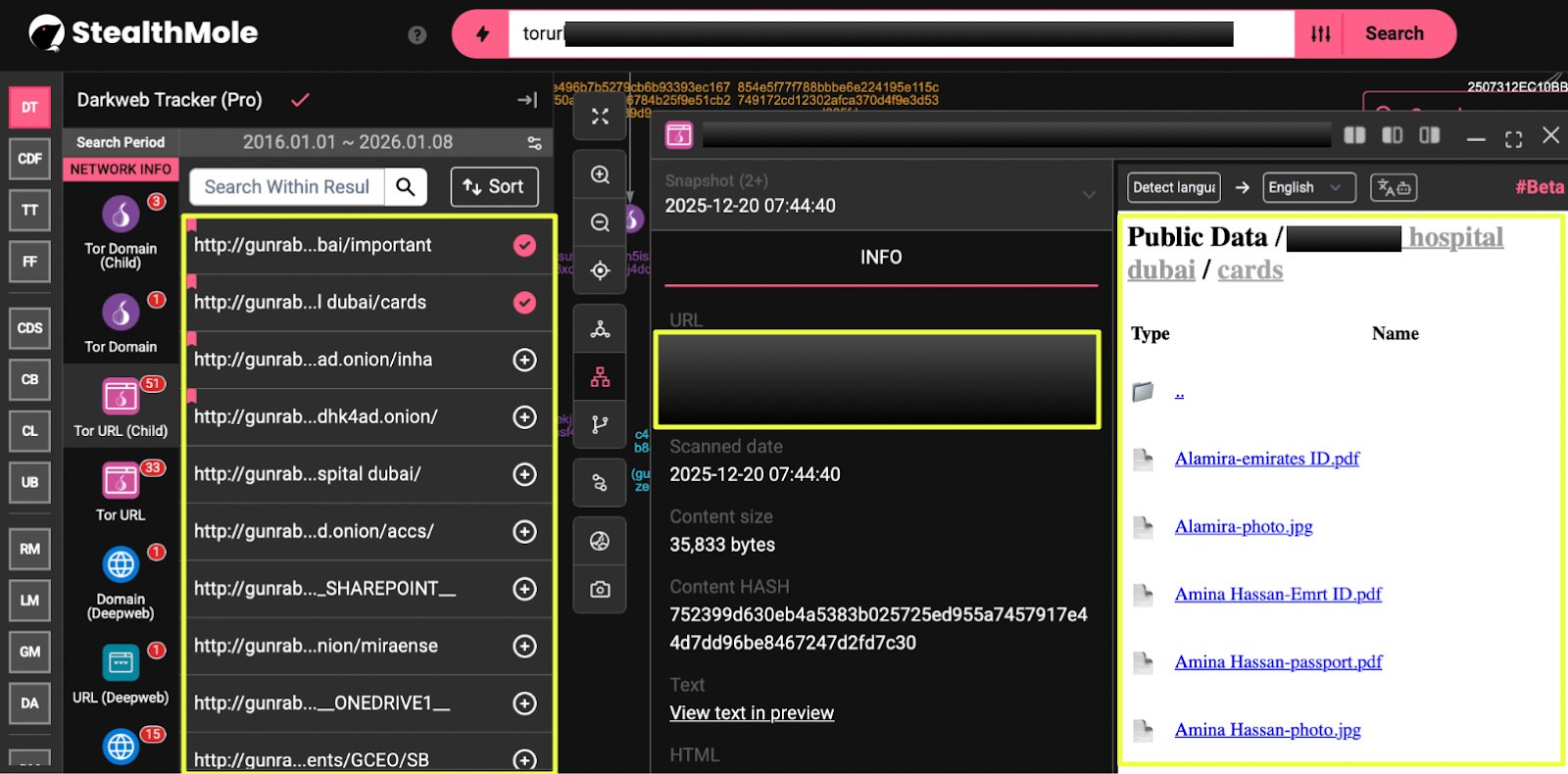
These files were organized under paths such as:
- /****** hospital dubai/cards
The exposure of identity documents and personal data elevates this incident beyond typical corporate document leaks. The presence of healthcare-related personal information introduces heightened privacy and regulatory implications, even without naming or confirming specific individuals.
This case demonstrates that Gunra’s activity extends beyond educational institutions and industrial targets into healthcare environments, where the potential impact of data exposure is significantly higher.
Conclusion
This investigation shows that Gunra operates as a hybrid ransomware actor, combining traditional encryption-based attacks with a structured and persistent data hosting ecosystem. The group’s activity between April and December 2025 reflects continuity, infrastructure investment, and deliberate presentation rather than opportunistic or short-lived campaigns.
By correlating ransomware leaks, malware hashes, chat servers, communication identifiers, and surface-accessible sites, this case highlights how Gunra maintains multiple layers of exposure and contact. The reuse of identifiers such as TOX IDs and the replication of content across Tor and clearnet environments point to operational overlap rather than strict compartmentalization.
The targeting of entities from educational institutions to hospitals illustrate the breadth of Gunra’s victim profile and the varying degrees of sensitivity in the exposed data. While Gunra consistently labels its hosted material as “public data,” the evidence observed during this investigation suggests a more complex and concerning reality.
Ultimately, this case reinforces the importance of tracking ransomware operations beyond single leak pages. By following infrastructure, artifacts, and communication paths, StealthMole enables analysts to move from isolated incidents to a broader understanding of how threat actors like Gunra operate across networks and over time.
Editorial Note
Dark web and ransomware investigations rarely provide absolute clarity. Infrastructure is reused, narratives are manipulated, and operators deliberately blur the line between legality and illegitimacy. This case reflects those uncertainties, while also demonstrating how StealthMole’s monitoring and pivoting capabilities help analysts navigate fragmented data, validate connections, and build defensible intelligence assessments in an environment designed to obscure them.
To access the unmasked report or full details, please reach out to us separately.
Contact us: support@stealthmole.com
Labels: Ransomware

.svg)
.svg)
.svg)