Old Data, New Actor: Investigating Solonik’s Alleged Instagram 17 M Leak
 |
In early January 2026, a threat actor operating under the name Solonik began gaining attention across dark web forums and Telegram channels after advertising a large-scale Instagram data leak allegedly tied to a “2024 API breach.” The dataset was marketed as containing 17 million Instagram user records, including usernames, emails, phone numbers, and internal IDs. Given Instagram’s global footprint and the scale claimed, the leak quickly drew interest from buyers and researchers alike.
At first glance, Solonik appeared to be a rapidly emerging actor. StealthMole monitoring showed a sharp spike in activity associated with his handle, with dozens of leaks posted in a short time frame and multiple distribution channels emerging almost simultaneously. The pace, volume, and confidence of Solonik’s claims suggested either privileged access to new data sources or a coordinated effort to appear established.
However, as the investigation progressed, inconsistencies began to surface. While the dataset was promoted as new and tied to a 2024–2026 breach window, early indicators suggested that identical data samples had circulated years earlier. This raised the possibility that the “new” Instagram leak was not a fresh compromise but a recycled dataset being reintroduced under a different narrative.
This report documents how StealthMole was used to trace the origins, movement, and rebranding of this dataset across forums, Telegram channels, and domains, ultimately challenging Solonik’s claims and highlighting the growing trend of breach recirculation under false timelines.
Incident Trigger and Initial Investigation
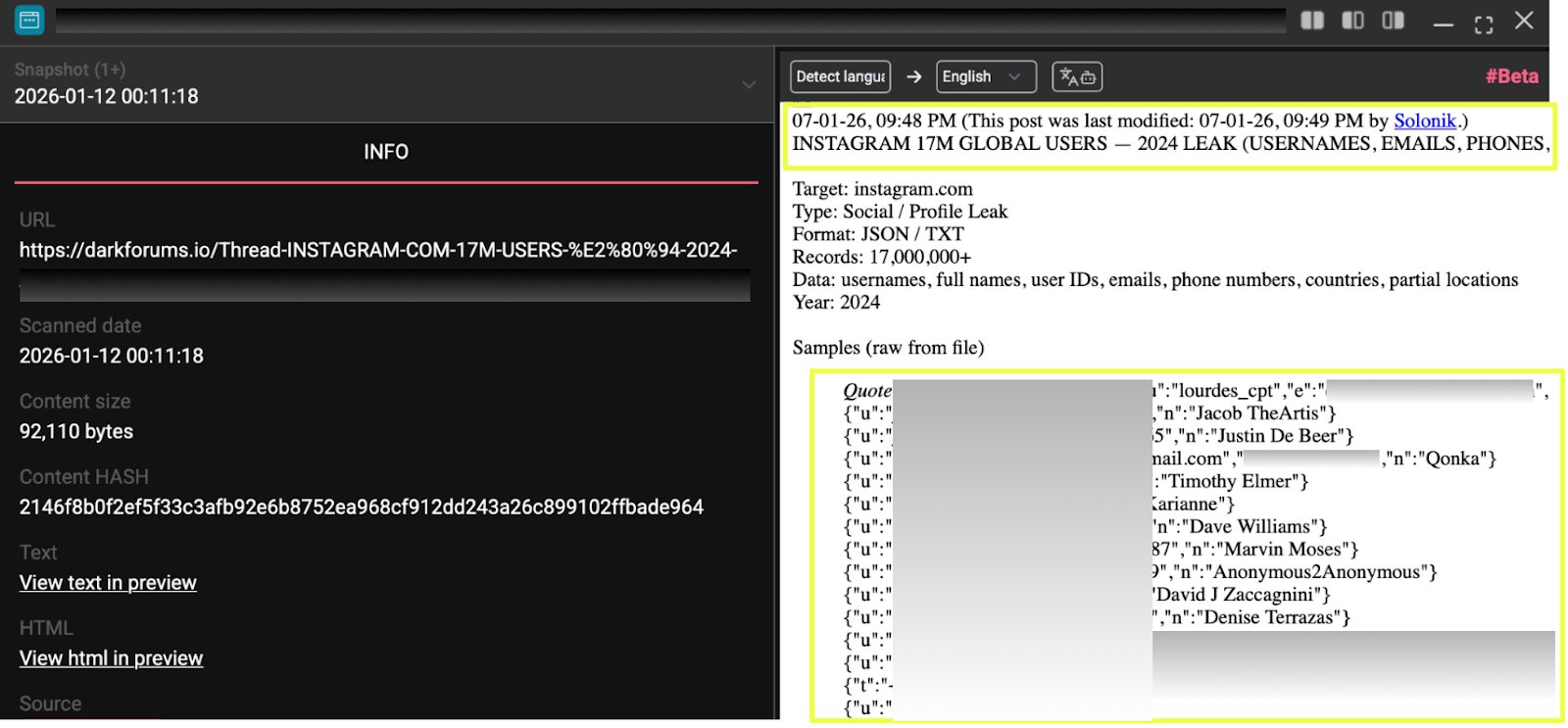
The investigation began when Solonik published a thread titled “INSTAGRAM.COM 17M USERS — 2024 API LEAK (USERNAMES, EMAILS, PHONES, IDS)” on Dark Forums.
- https://darkforums.****/Thread-INSTAGRAM-COM-17M****Solonik-****
To assess the actor’s credibility and scale, the identifier Solonik was queried through StealthMole’s Leaked Monitoring module. This revealed that between 7 January 2026 and 20 January 2026, Solonik had been associated with leaks affecting approximately 105 distinct victims, ranging from social media datasets to regional institutional records. This level of activity suggested either a highly active reseller or a coordinated operation.
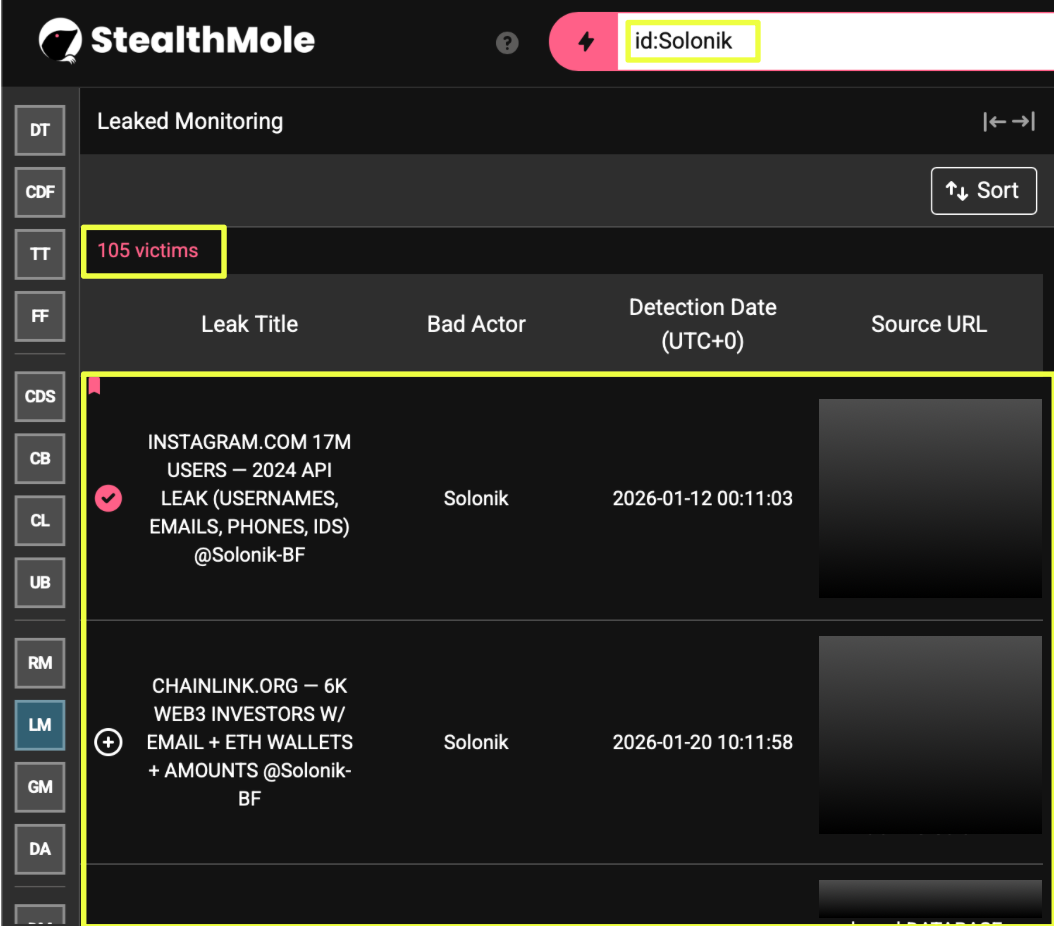 |
One of the earliest corroborating signals came from Solonik’s Telegram presence. Using StealthMole’s Telegram Tracker, the channel https://t.me/solonik_*****s was identified as a public-facing vouch and transaction channel. From there, StealthMole uncovered an additional invite-only Telegram group at https://t.me/+iS5*******k, where screenshots showed buyers negotiating prices, confirming cryptocurrency transactions, and receiving CSV database files.
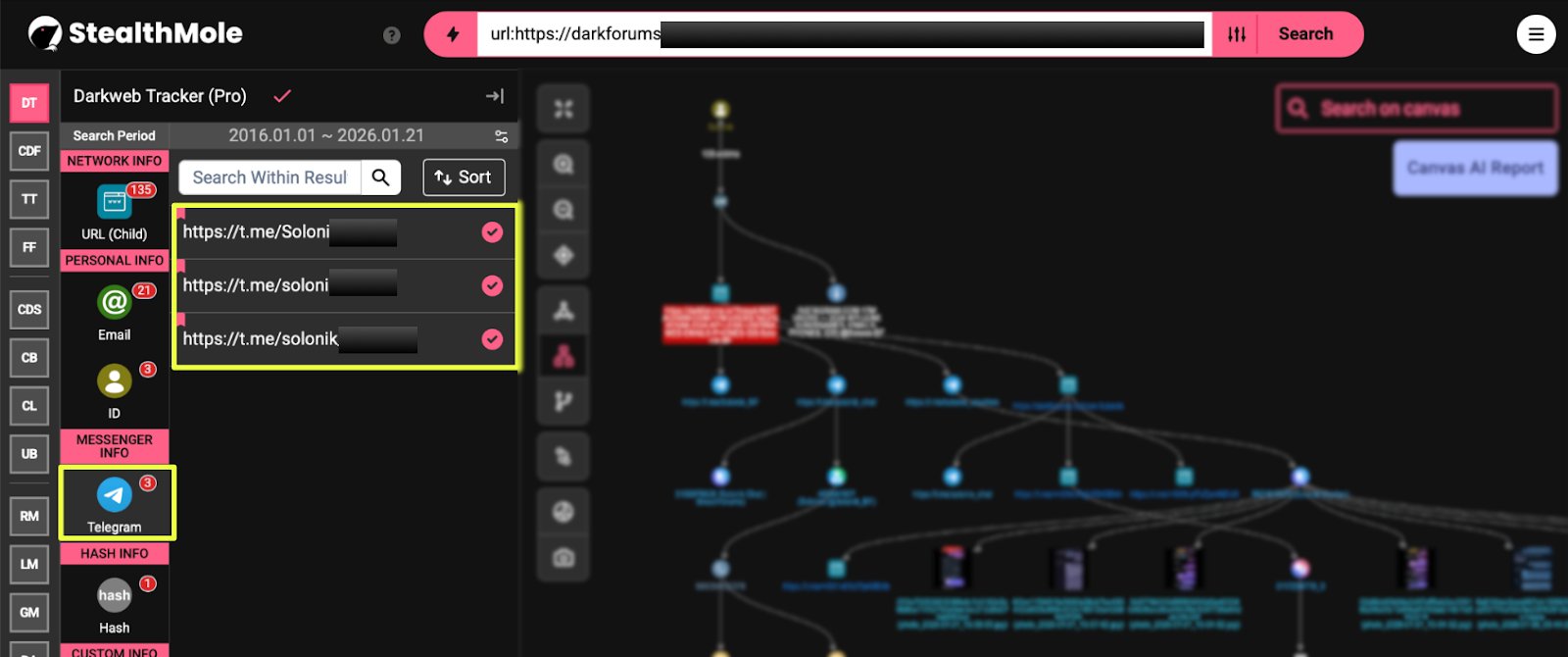 |
Notably, this Telegram infrastructure had already been indexed by StealthMole under CVE-2025-14847 and CVE-2026-21858 linking Solonik’s ecosystem to previously flagged malicious distribution activity. This connection established that the actor was not operating in isolation and had already intersected with known high-risk Telegram clusters.
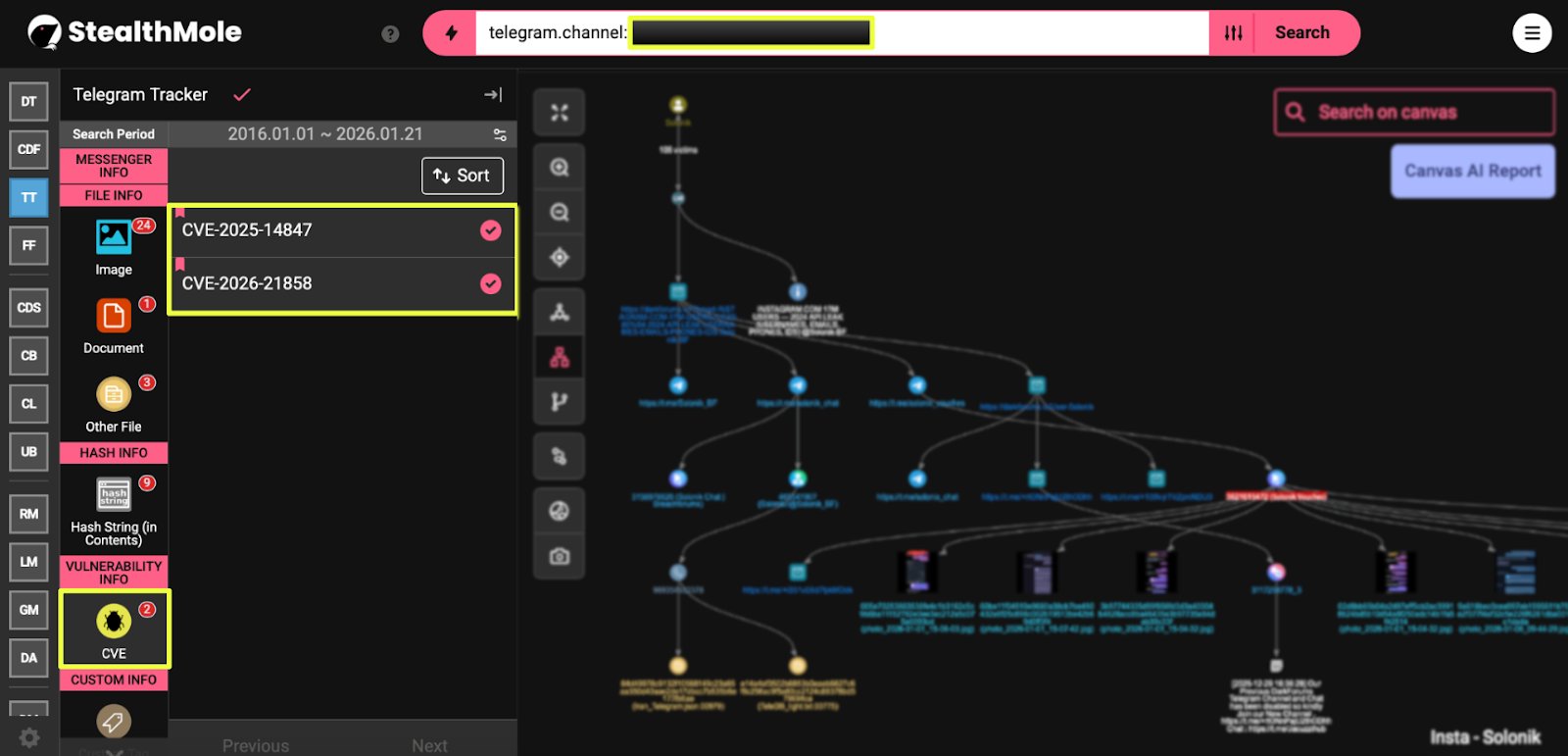 |
Expansion of Infrastructure and the “BAPHOMET” Reference
Further investigation into Solonik’s online footprint revealed the domain solonik.***, which was queried through StealthMole’s Darkweb Tracker. The results were significant: StealthMole indexed 999+ leaked files associated with this domain, many labeled with Instagram-related filenames such as Instagram@Solonik_BF.json.
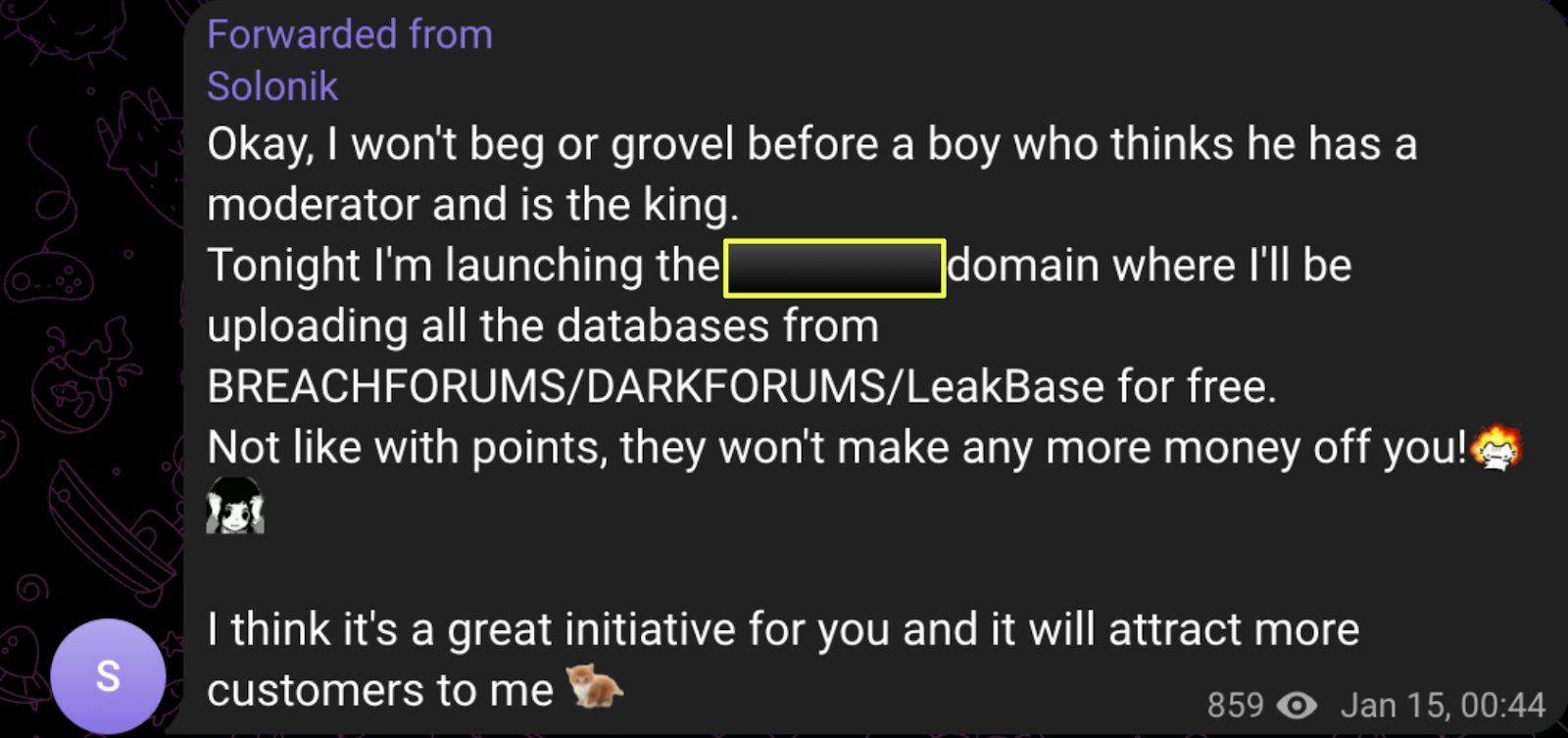 |
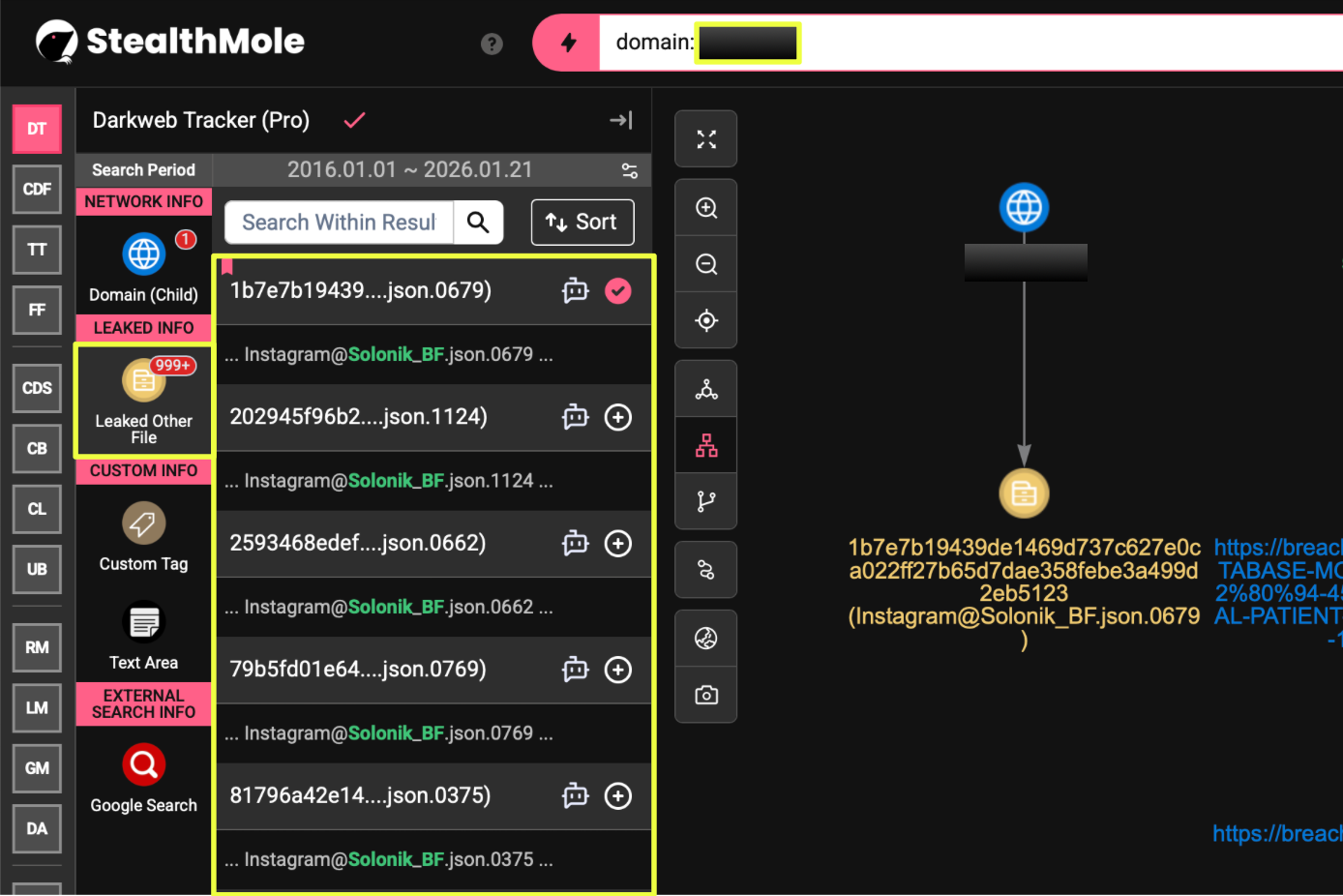 |
Among these results, a second Instagram-related leak surfaced on 14 January 2026, tied to a BreachForums thread advertising 45K Korean Hospital Patient & System Records. In Solonik’s forum bio on this thread, he included the phrase “blessed by BAPHOMET.”
This phrase prompted a deeper investigation. Through Telegram tracking, StealthMole identified a video circulating in one of Solonik’s channels in which he screen-recorded a BreachForums interaction. In the video, a user identified as BAPHOMET thanked Solonik for previously disclosing information about an SQL vulnerability in the forum’s structure, specifically referencing the my tabs column.
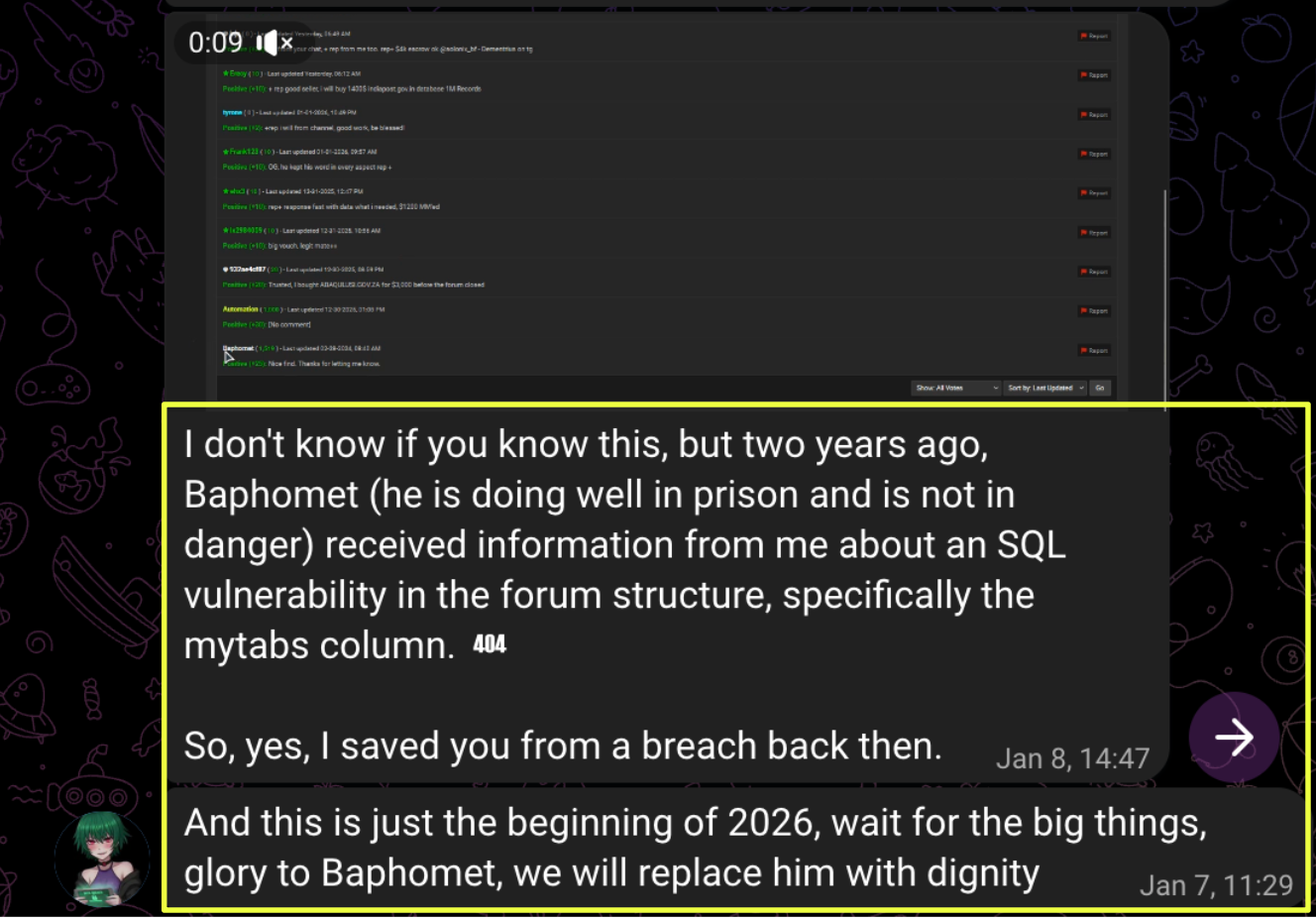 |
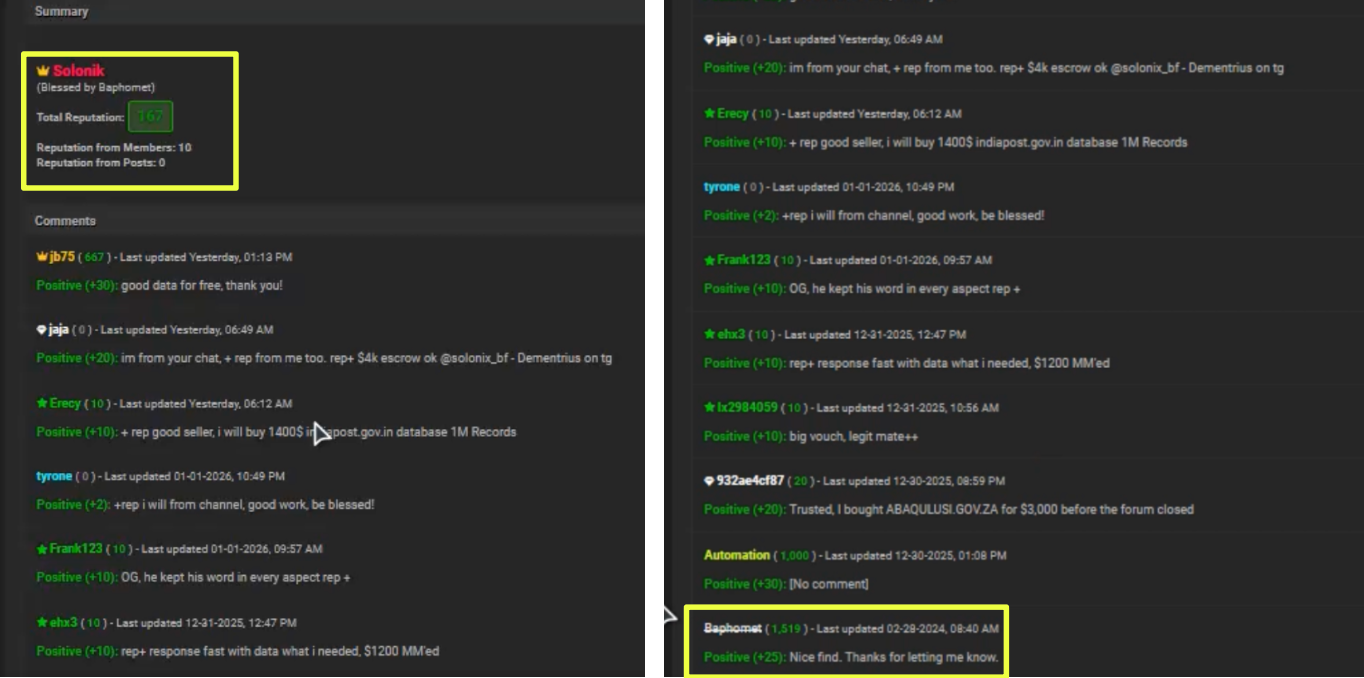 |
The video also displayed BAPHOMET’s BreachForums profile, showing the account as permanently banned, but historically influential. The message claimed that Solonik had “saved” the forum from a breach years earlier and framed their interaction as proof of legitimacy and insider status. While the claim itself could not be independently verified, its inclusion served as a credibility signal aimed at potential buyers.
This was a critical turning point. The narrative was no longer just about a dataset, but about lineage, reputation, and implied authority within the breach ecosystem.
Data Lineage Analysis: Tracing the Instagram Dataset Backward
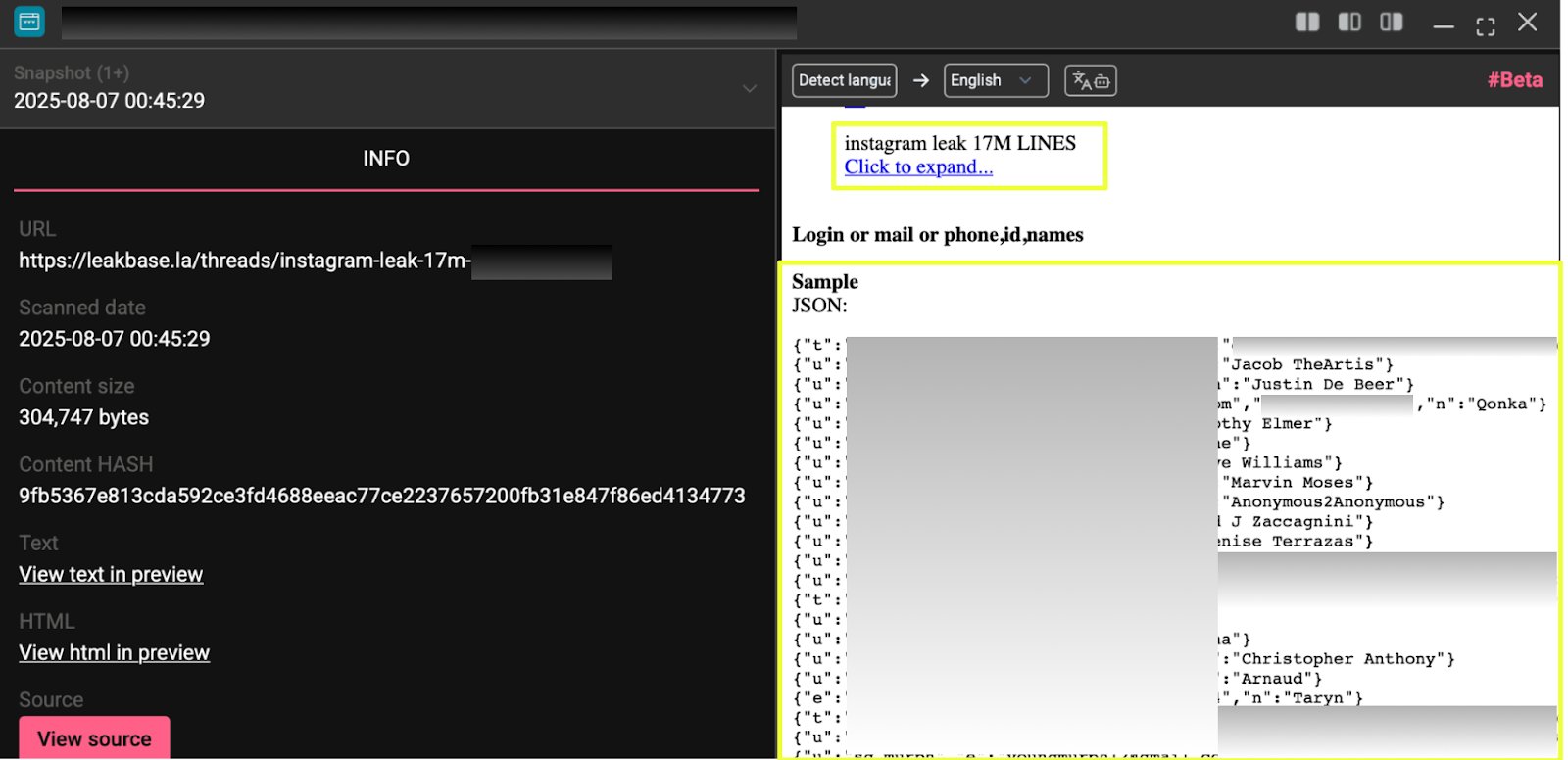
To validate Solonik’s claim that the Instagram data originated from a 2024 API breach, the dataset itself was examined. Using StealthMole’s Telegram Tracker, the keyword “Instagram Leak 17M Lines ⭐ ️” was queried across historical Telegram messages. This surfaced a forwarded message dated 2023-11-28, originating from the channel The Jacuzzi.
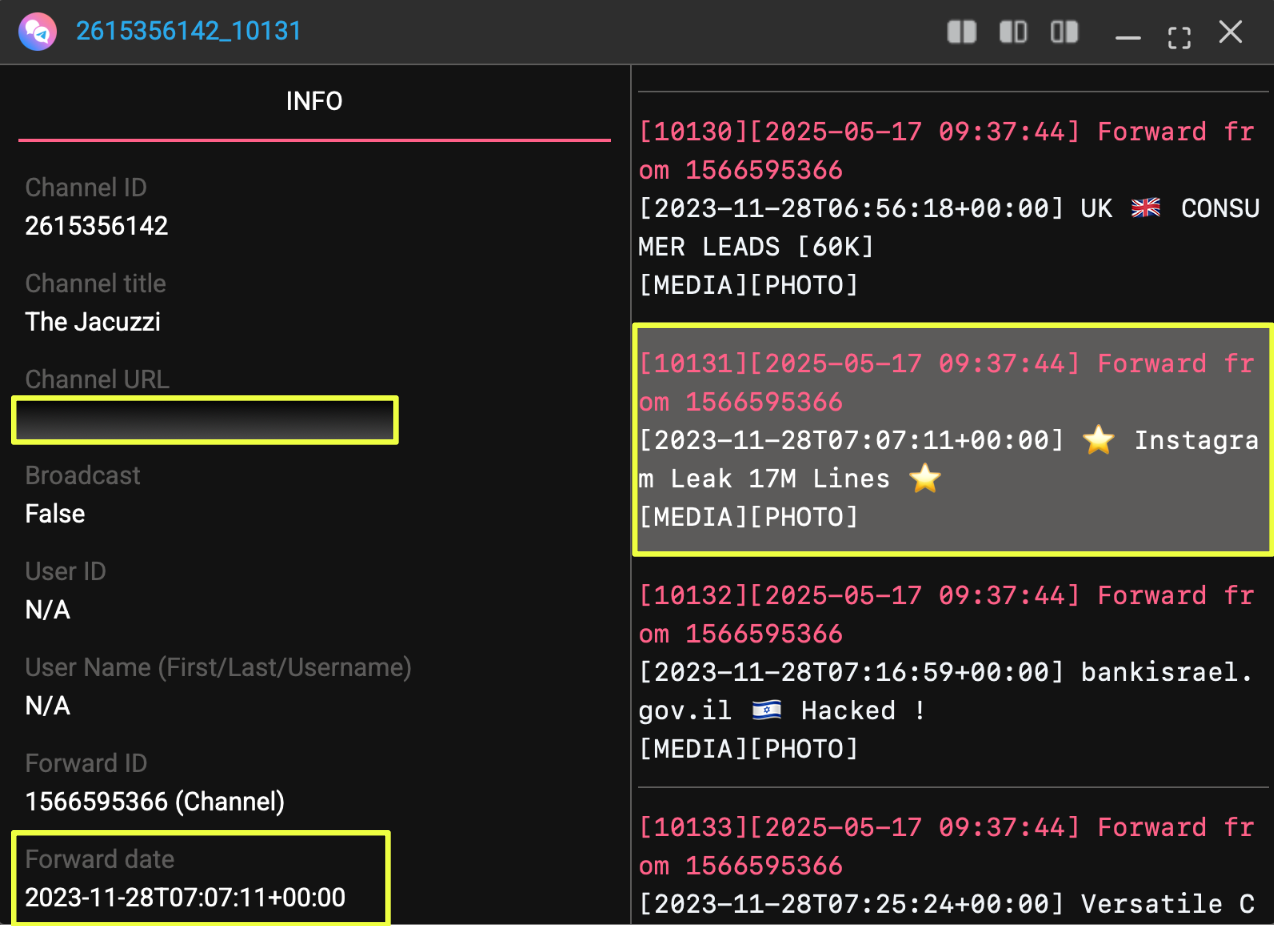 |
That forwarded message led directly to a LeakBase thread posted in March 2023 by a user named Chucky. The LeakBase snapshot showed the thread title “Json No Pass Cloud Instagram Leak 17M Lines”, with sample JSON entries containing usernames, emails, phone numbers, and IDs, structurally identical to the samples advertised by Solonik in 2026.
- https://leakbase.la/threads/instagram-leak-17*************/
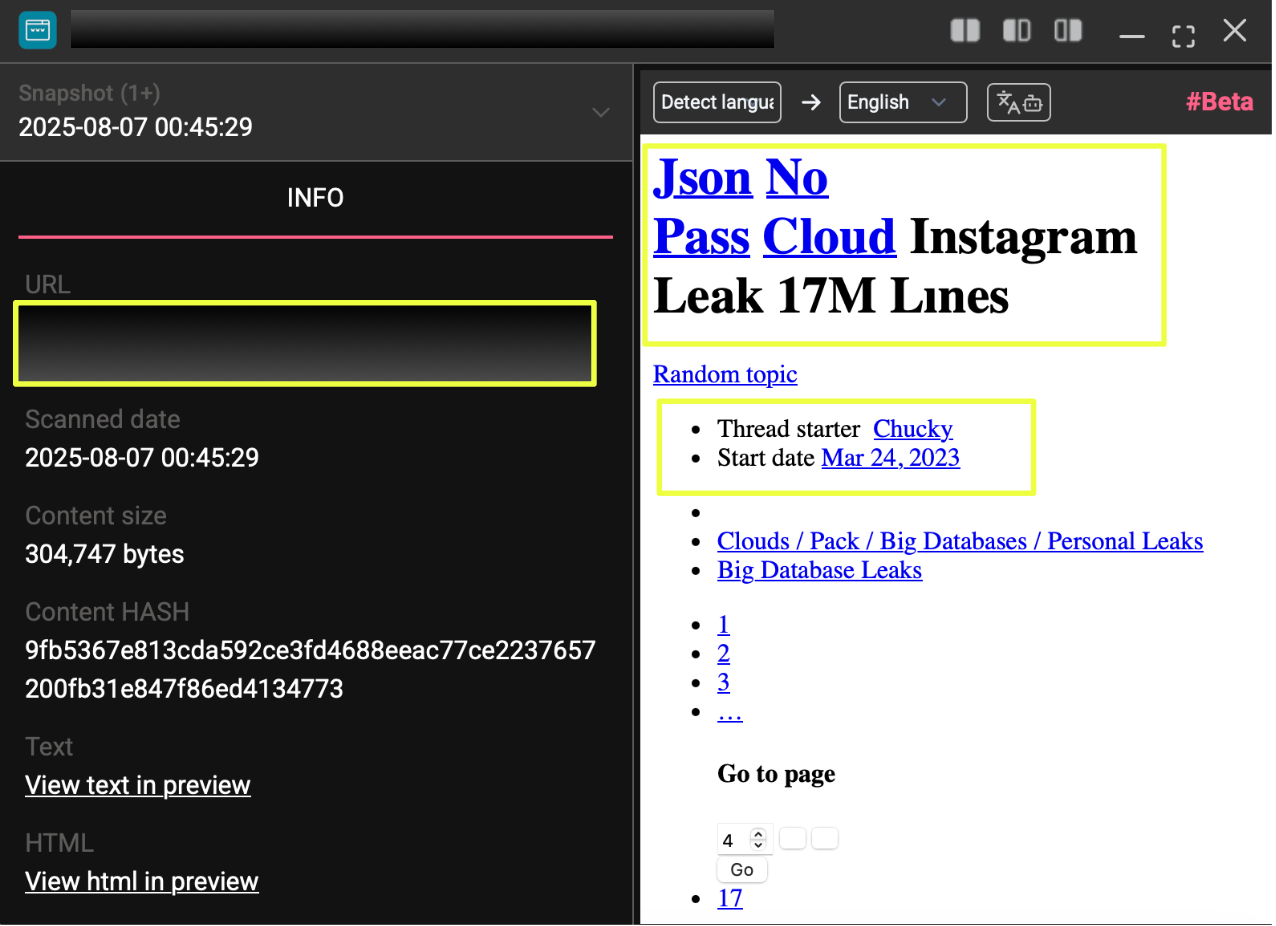 |
Further comparison confirmed that the raw data fields, ordering, and sample values matched across the 2023 LeakBase post and Solonik’s 2026 offering. No new columns, timestamps, or indicators suggested that the dataset had been refreshed or expanded.
 |
 |
This same dataset appeared again in 2024 on Hydra Forums, posted by administrator Pavlov under the title “Instagram Leak 17M Lines ⭐️”:
- https://hydraforums.io/Threads-*****************************8F
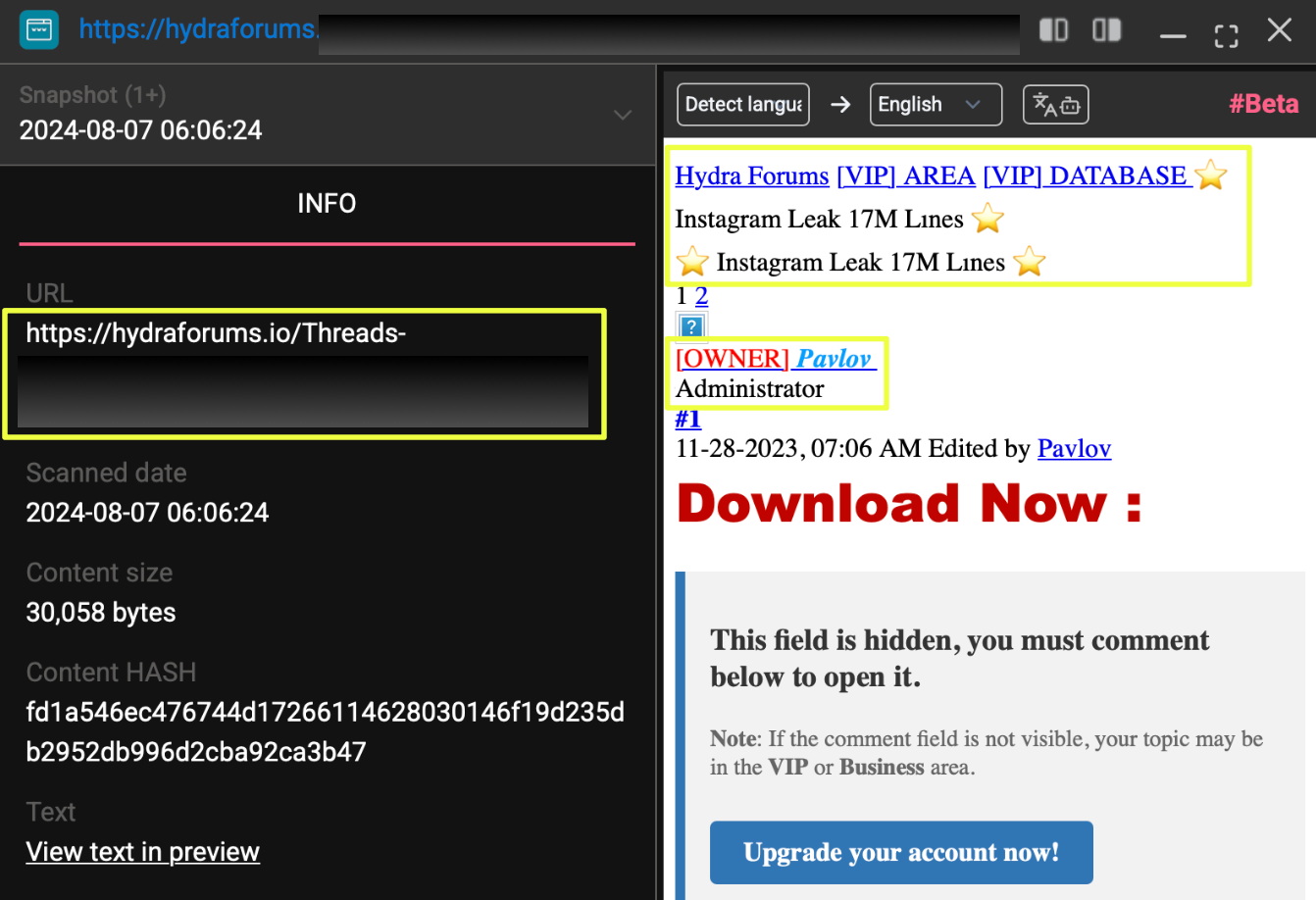 |
The Hydra Forums snapshot showed the same JSON samples, confirming that the data had circulated unchanged for at least three years.
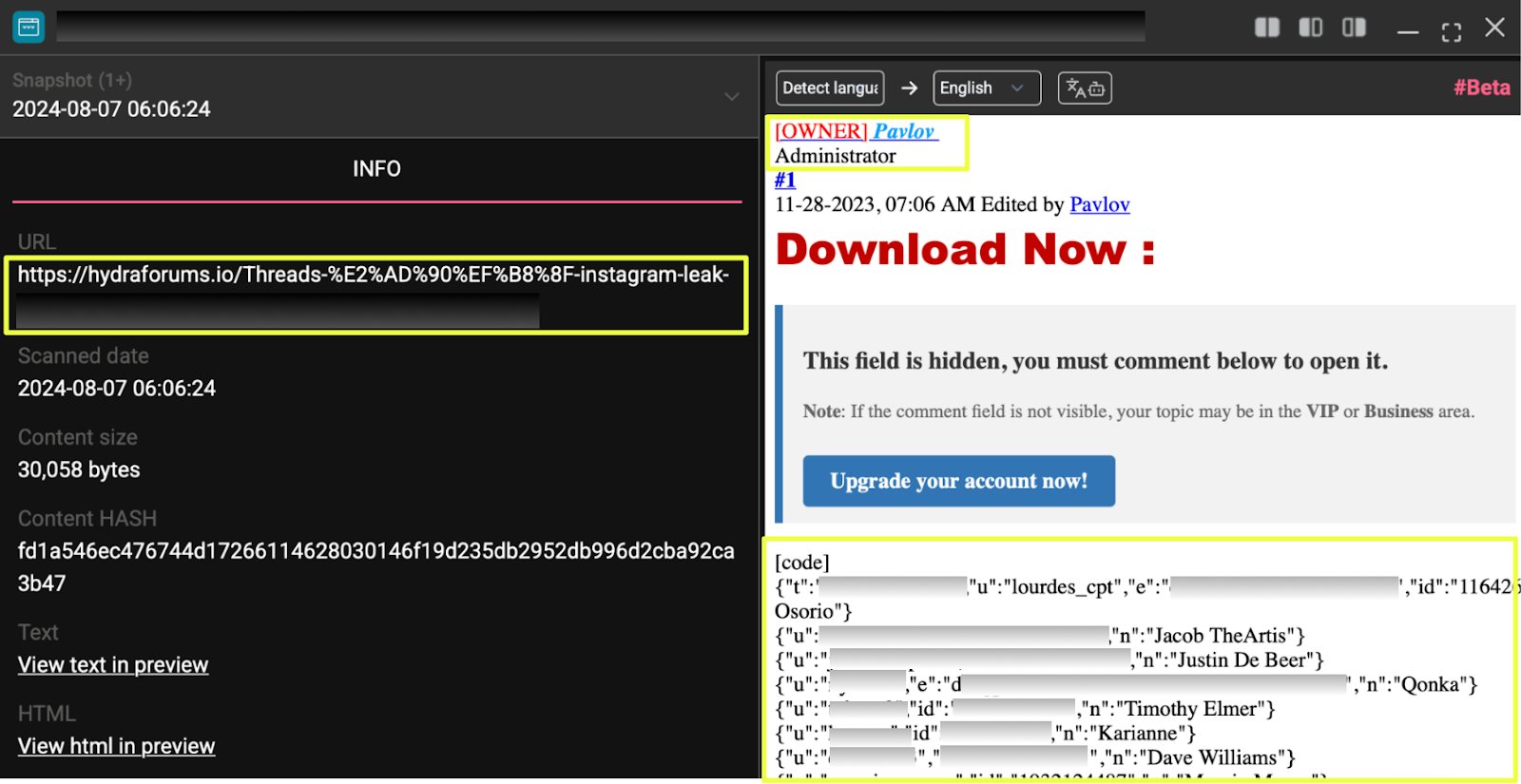 |
These findings directly contradicted Solonik’s framing of the leak as a “2024 API breach” and strongly indicated dataset recycling rather than a new compromise.
Chucky, Chucky_lucky, and Identity Overlap
Solonik later claimed in Telegram messages that his previous BreachForums account, “Chucky_lucky,” had been taken down by a moderator named L****i. To assess this claim, Chucky_lucky was queried in StealthMole’s Leaked Monitoring module. The results showed five victims, including a global jewellery brand breach from 2023.
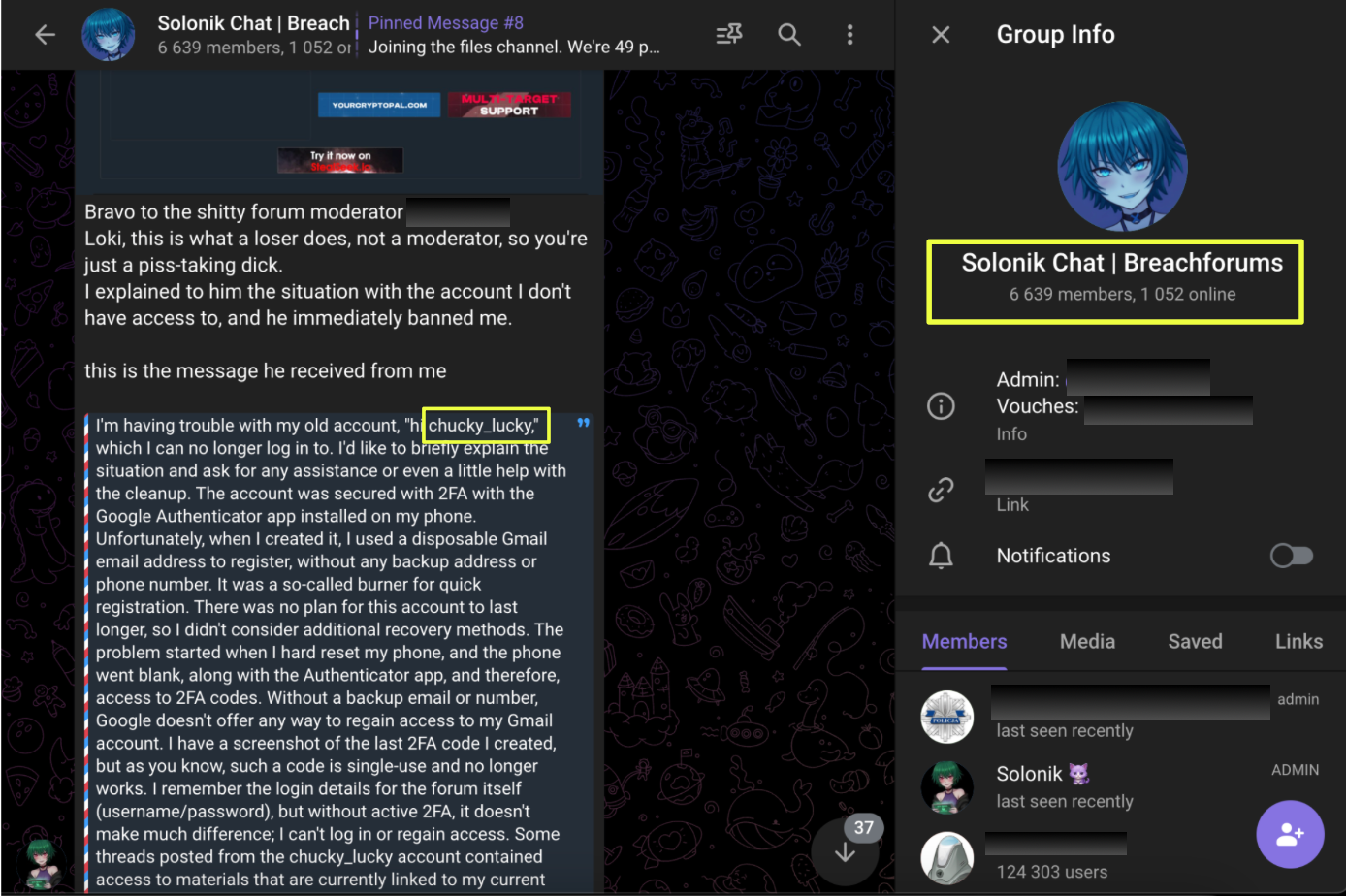 |
This activity aligned temporally with the original LeakBase Instagram post by Chucky, strengthening the hypothesis that Chucky, Chucky_lucky, and Solonik may be connected. Additional Telegram channels reinforced this pattern, including https://t.me/chucky***f and https://t.me/chucky_*******a, where screenshots showed Chucky listed among the “richest users” on a forum consistent with BreachForums.
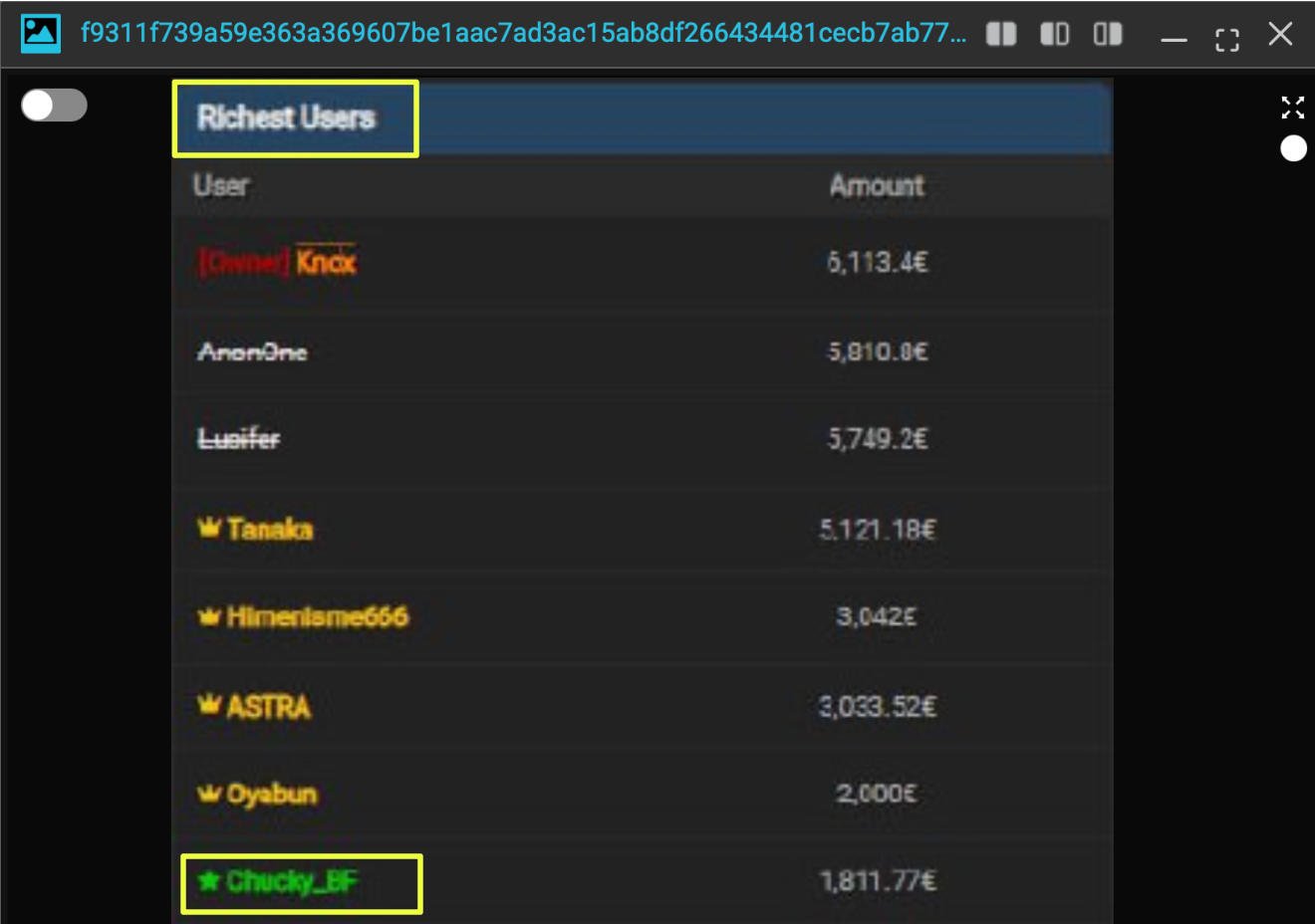 |
These overlaps do not conclusively prove shared ownership, but they demonstrate continuity in datasets, platforms, and monetization strategies. The repeated appearance of the same Instagram data under different aliases across years suggests deliberate rebranding rather than independent rediscovery.
Telegram Attribution and Iranian Infrastructure
The investigation expanded further when the Telegram channel https://t.me/solonik***t was analyzed. StealthMole identified a user Solonik BF. From this channel, a phone number was extracted: +98 9*********8. While usernames on Telegram are easily changed, user IDs are persistent, making this identifier particularly valuable for further analysis.
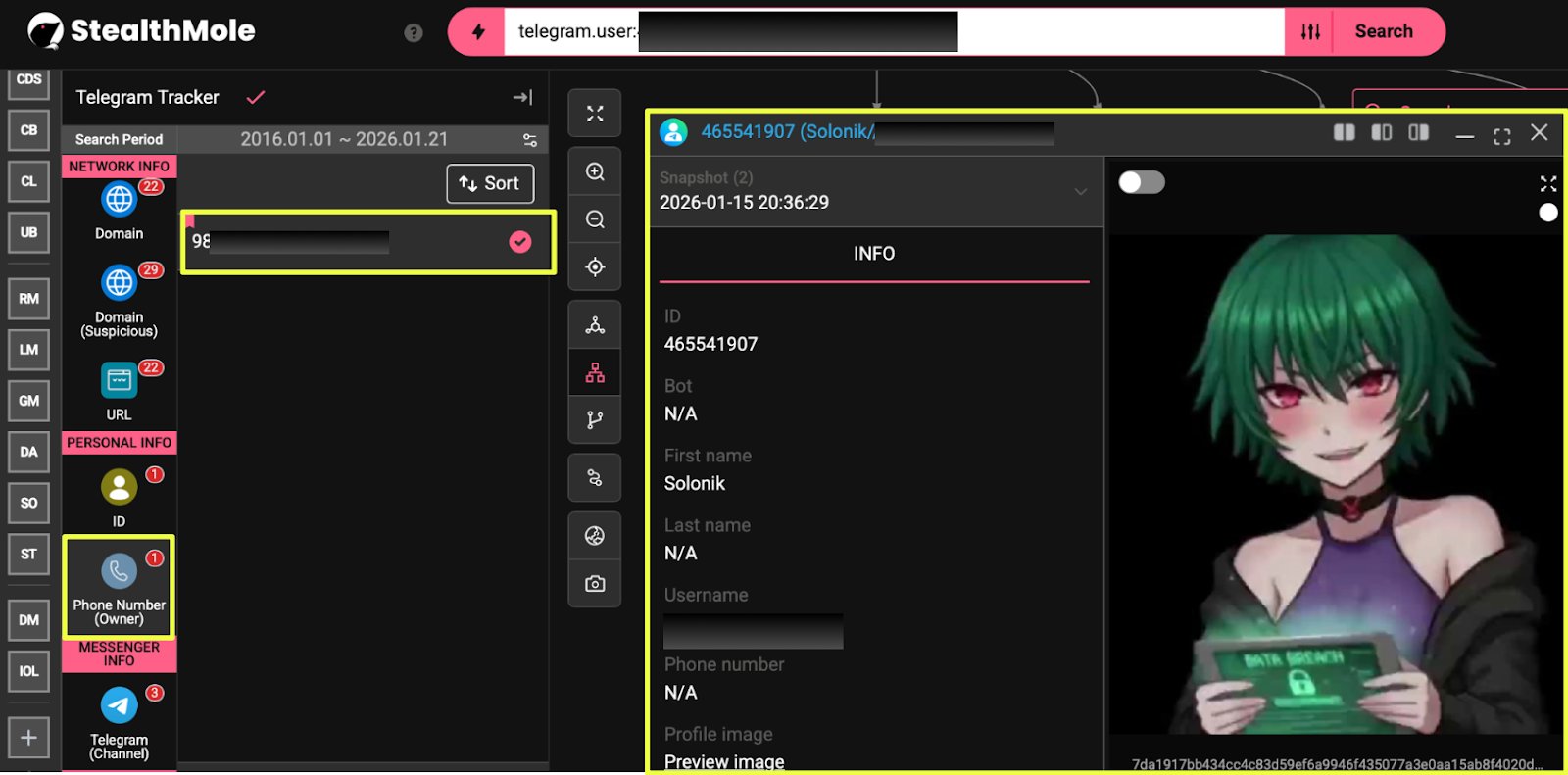 |
The country code +98 indicates Iran. When this number was queried through StealthMole’s Darkweb Tracker, it appeared in a file labeled Iran_Telegram.json, part of previously leaked Iranian Telegram datasets. This does not confirm Solonik’s physical location, but it provides a rare infrastructural linkage between his Telegram presence and known leaked data repositories.
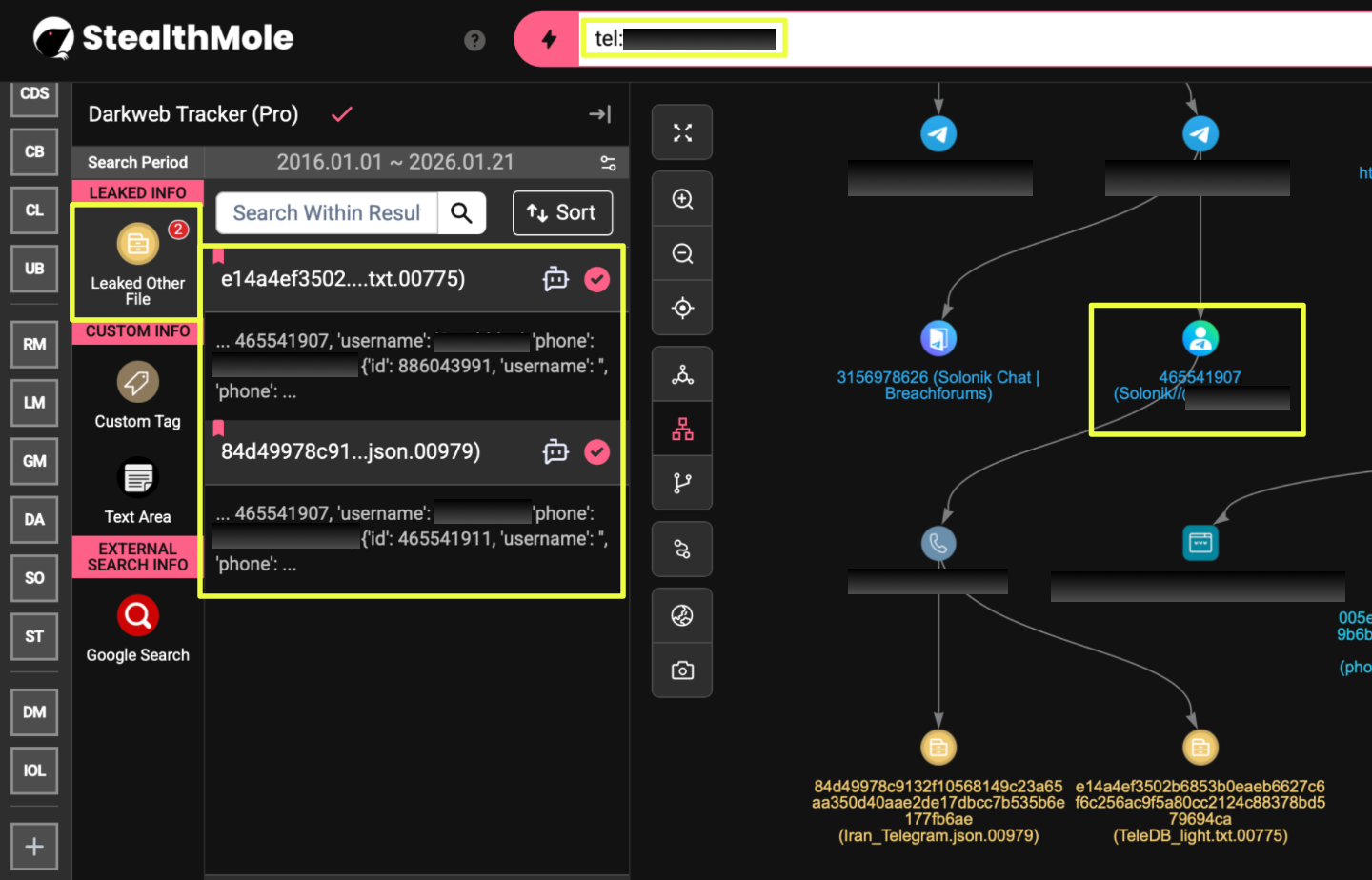 |
This file is part of a broader collection of leaked Iranian Telegram user data and contains structured records linking phone numbers to Telegram usernames and internal user IDs. Within this dataset, the number is explicitly associated with the username Sa*****n, once again tied to user ID 46******7, conclusively linking the Iranian Telegram leak data to the same account now operating as @Solonik*****F.
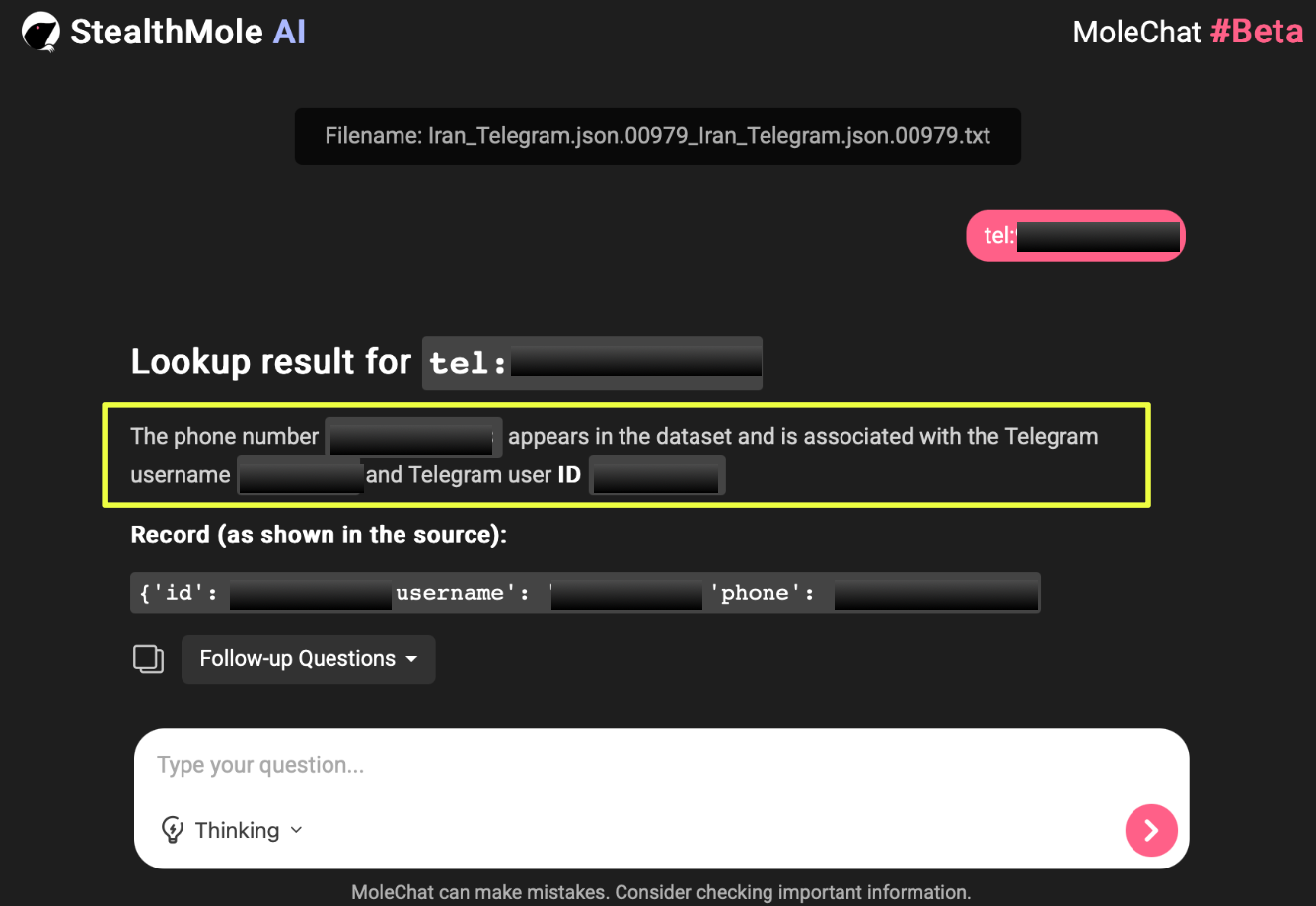 |
Historical analysis of this Telegram user ID provided additional context. When user ID 4********7 was pivoted through StealthMole’s Telegram Tracker, earlier activity associated with the same identifier was identified. Records dating back to October 2022 show the account operating under the username @Sa*****n, with display names recorded as S**** / T***t. This confirms that the identity linked to Solonik predates the 2026 Instagram leak claims by several years, suggesting a long-standing Telegram presence rather than a newly created persona.
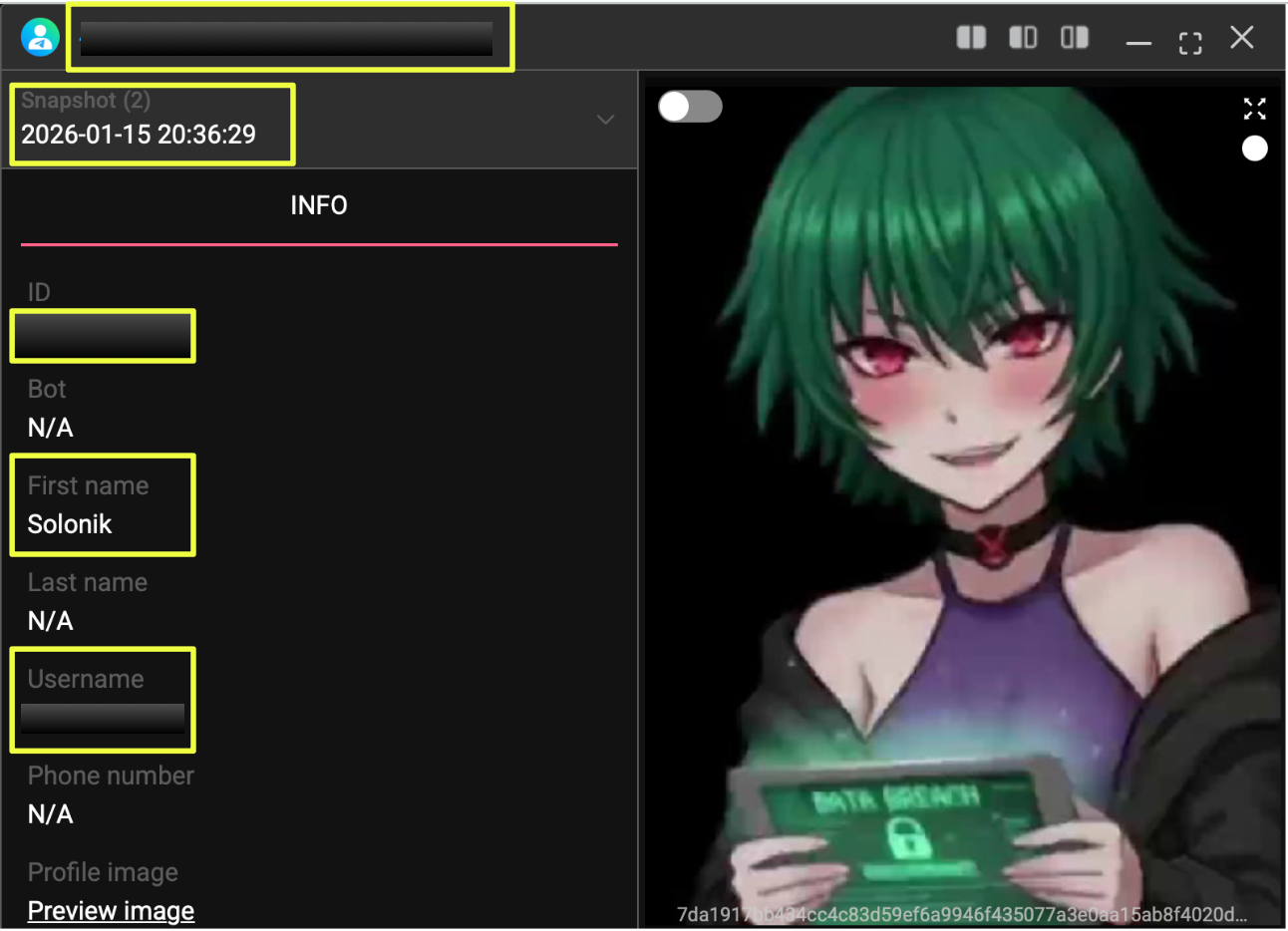 |
Further examination of historical Telegram data showed that this account had been active as early as October 2020, based on StealthMole’s historical indexing. This timeline places the operator well before the emergence of the Instagram dataset later circulated in 2023, 2024, and 2026. The persistence of the same user ID across multiple usernames reinforces the continuity of control over the account, even as outward-facing identities evolved over time.
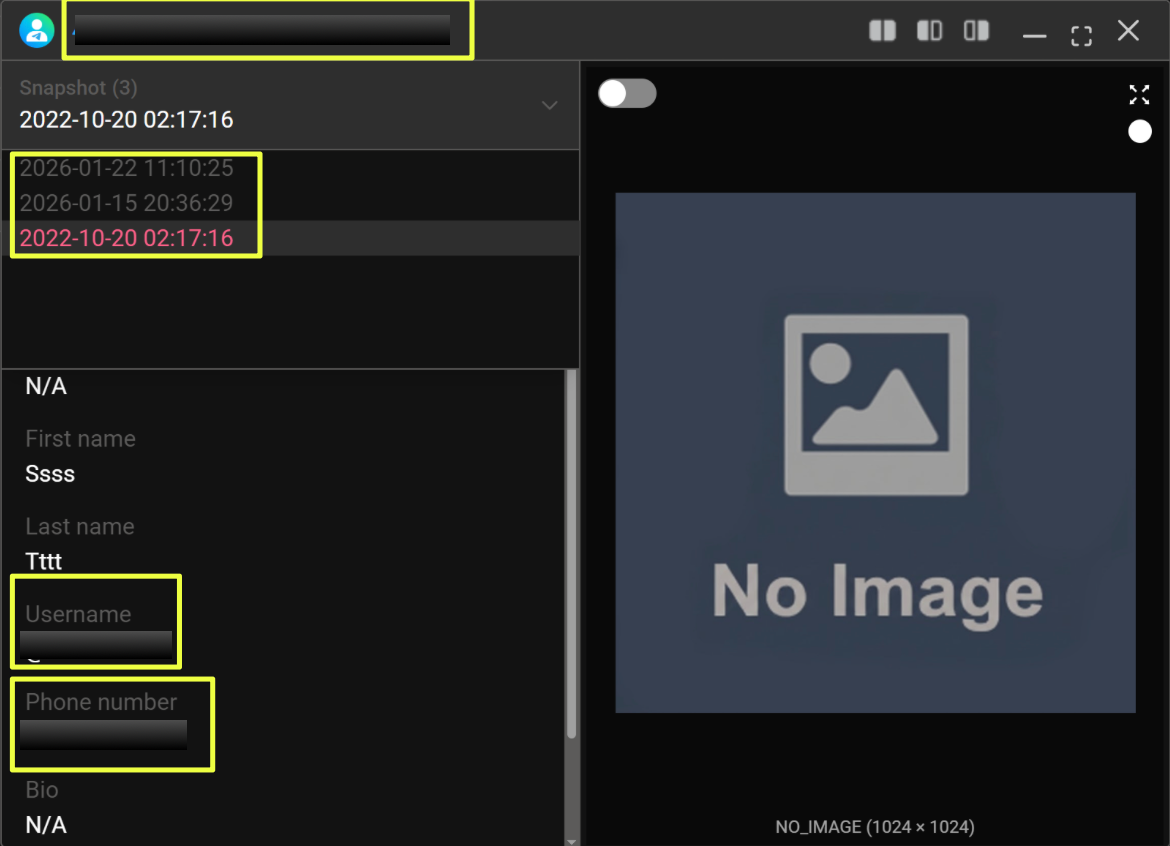 |
Additional contextual signals emerged when this Telegram identity was traced across group interactions. The same user ID was referenced within a Persian-speaking Telegram group titled Tavern Club, accessible at https://t.me/g*******b. While participation in such groups does not independently confirm attribution, it further situated the account within an Iranian-language Telegram ecosystem.
 |
Taken together, these findings strengthen the infrastructural linkage between Solonik’s Telegram presence and Iranian-linked Telegram data exposure. The reuse of the same Telegram user ID across multiple usernames, its appearance in leaked Iranian Telegram datasets, and its interaction within regionally aligned Telegram groups suggest operational continuity rather than coincidence. This infrastructure-level overlap does not definitively attribute Solonik to a specific individual or location, but it provides a consistent and traceable framework that aligns with other elements observed throughout the investigation.
Conclusion
The investigation demonstrates that the Instagram “17M users” dataset advertised by Solonik in January 2026 is not new. Through StealthMole’s historical indexing and cross-platform tracking, the data can be traced back to at least March 2023, with confirmed appearances in 2023 (LeakBase) and 2024 (Hydra Forums) before resurfacing in 2026.
Instagram has publicly denied any 2026 breach, further undermining Solonik’s claims. While Solonik has successfully leveraged volume, presentation, and reputation signaling to attract buyers, the underlying data tells a different story, one of recirculation rather than compromise.
Whether Solonik is the same individual as Chucky or Chucky_lucky cannot be stated with certainty. However, the continuity of datasets, platforms, Telegram infrastructure, and monetization patterns strongly suggests either direct identity overlap or close operational alignment.
Editorial Note
Attribution in dark web investigations is rarely absolute. Actors reuse data, identities fragments, and narratives are intentionally blurred. This case underscores how easily old breaches can be reframed as new incidents and how critical longitudinal visibility is in cutting through those claims. By correlating historical leaks, Telegram activity, and infrastructure signals, StealthMole enabled a clearer understanding of what was genuinely new, what was recycled, and where uncertainty still remains.
To access the unmasked report or full details, please reach out to us separately.
Contact us: support@stealthmole.com
.svg)
.svg)
.svg)