From Exploit Tools to Account Sales: Mapping the Operational Model of ‘Quessts’
 |
The underground economy has evolved far beyond simple malware distribution. Today, exploit tools operate as structured products: packaged, branded, updated, and marketed across multiple platforms. What once circulated quietly in private circles now moves fluidly between GitHub repositories, Telegram channels, archived forum threads, and niche communities.
Exploit development is no longer confined to advanced threat actors. It has become accessible, modular, and increasingly commercialized. Tools are advertised with changelogs, version numbers, installation guides, and “educational” disclaimers. Distribution strategies mirror legitimate software releases: support servers, video tutorials, and update announcements across channels.
At the same time, these tools rarely exist in isolation. The same actors who develop or distribute exploit-based utilities often diversify: moving into account sales, modded applications, digital goods markets, and auxiliary services. The boundaries between technical experimentation, opportunistic monetization, and structured underground commerce have blurred.
What makes this ecosystem particularly interesting is not just the tools themselves, but the operational model behind them. How are these tools promoted? Where are they discussed? How are reputations built? And how does an actor transition from releasing an exploit-themed utility to selling verified accounts or digital access products?
This report does not focus solely on a single tool. Instead, it maps an operational pattern, tracing how one online persona navigates exploit development, distribution channels, community engagement, and monetization pathways across platforms.
Initial Investigation: APK Crypt Service and Android Evasion
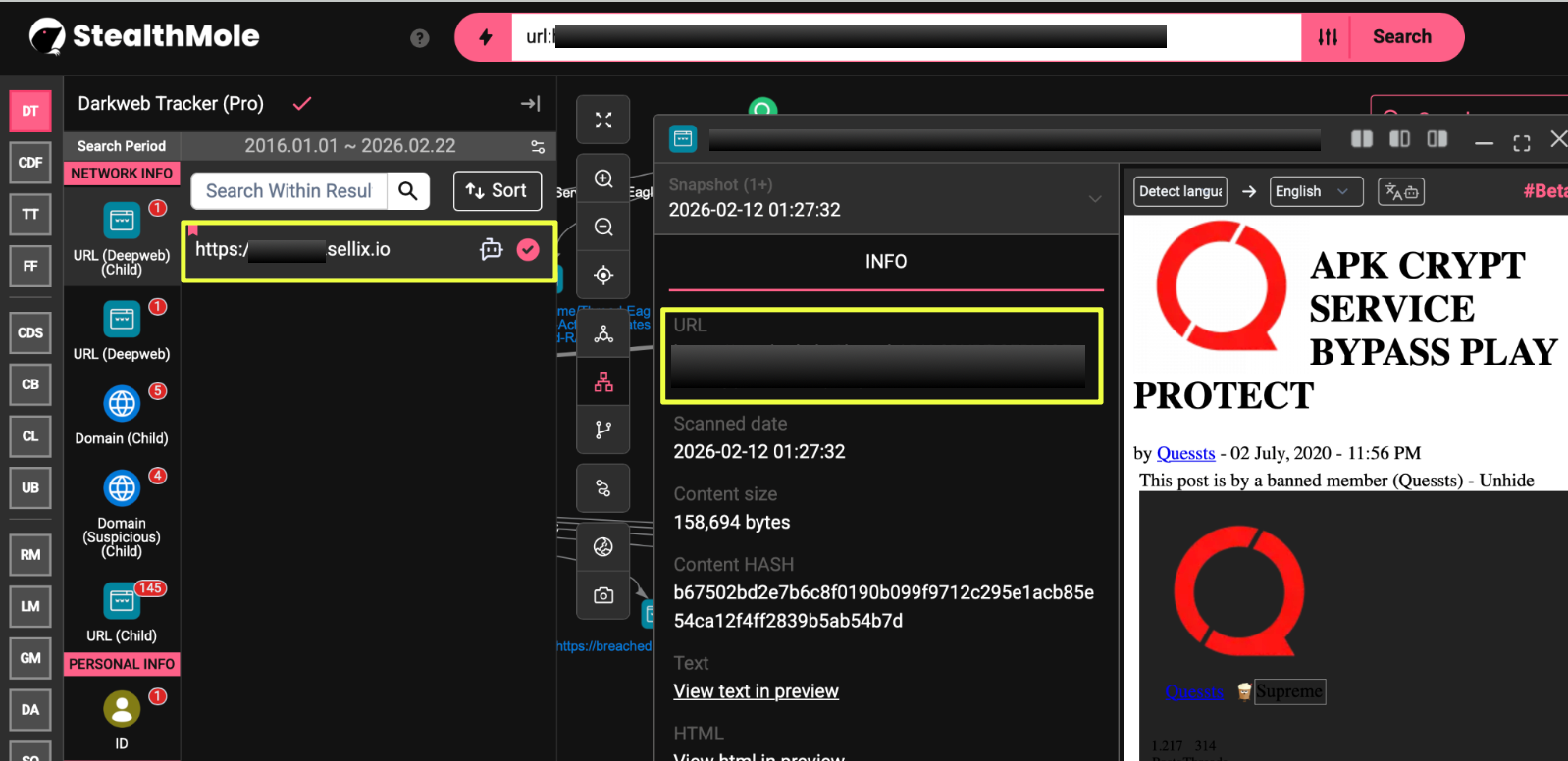
The investigation began within an Android-focused services thread rather than a standalone malware drop.
While monitoring exploit-related discussions, a post on cracked.sh surfaced advertising an “APK Crypt Service – Bypass Play Protect.” The offering positioned itself as a technical service designed to modify or encrypt Android applications in ways that could evade Google Play Protect detection mechanisms.
- https://cracked.sh/Thread-A*****************T
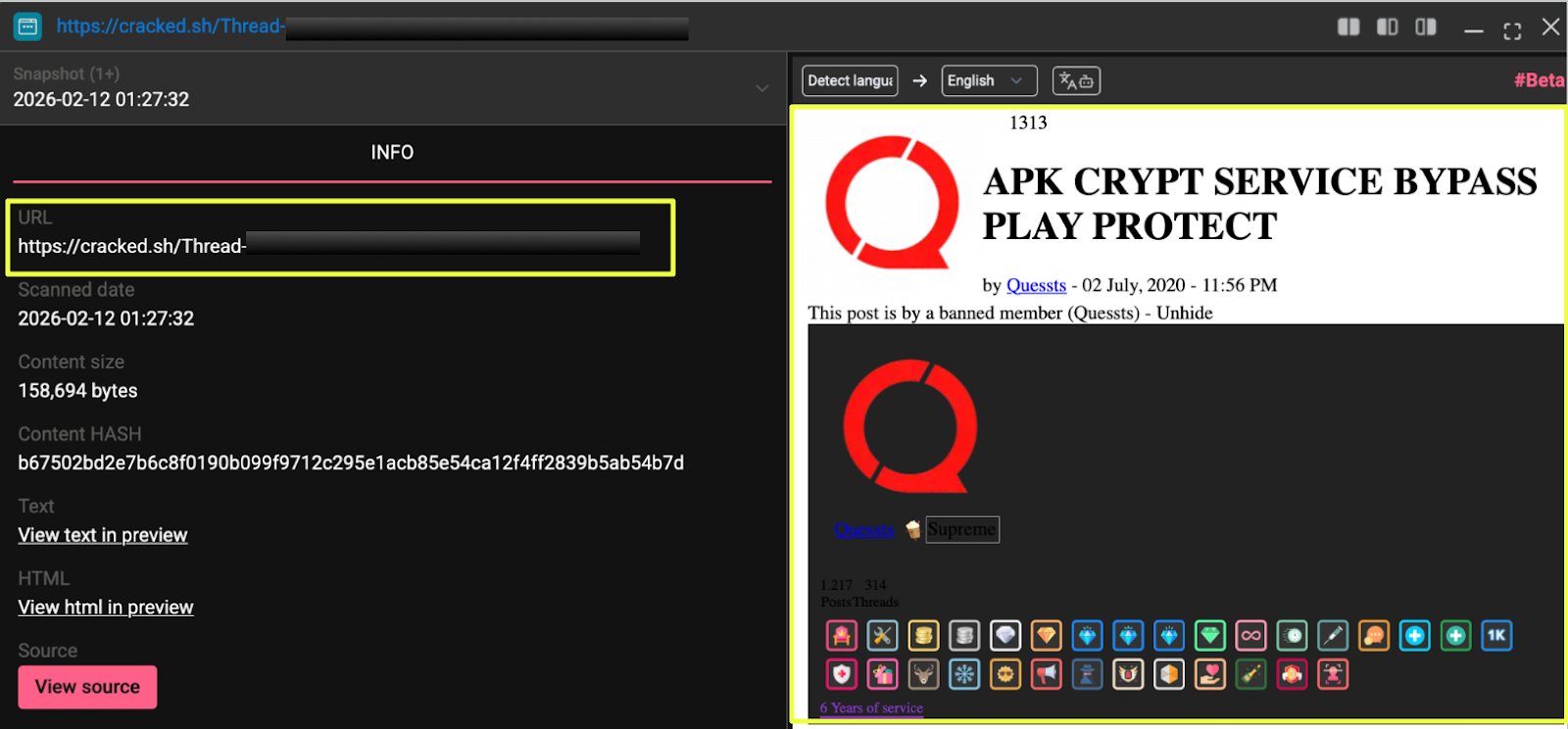 |
The thread was published under the alias “Quessts.” The thread also introduced a recurring visual identifier: a red Q logo associated with the alias. This branding would later appear across multiple platforms, suggesting intentional identity consistency.
Unlike one-off exploit releases, this post suggested a recurring operational model. It presented itself as a service: implying repeat clients, ongoing demand, and a monetization structure built around evasion. Rather than distributing a specific malicious payload, the offering focused on enabling others to deploy applications with reduced detection rates.
This distinction matters.
 |
Crypting services sit at a strategic layer of the Android underground ecosystem. They act as facilitators: supporting modded apps, gray-market distributions, and potentially malicious campaigns by helping them bypass automated security filters. Even without direct malware publication, such services contribute to broader threat enablement.
At this stage, the key questions shifted:
Was this Android-focused service an isolated offering? Or was it part of a broader pattern of exploit development and commercialization under the same alias?
The next step was to examine where else the name “Quessts” appeared and whether similar tooling or services were being promoted beyond cracked.sh.
Pivot Through Leaked Data: Darkweb Tracker Findings
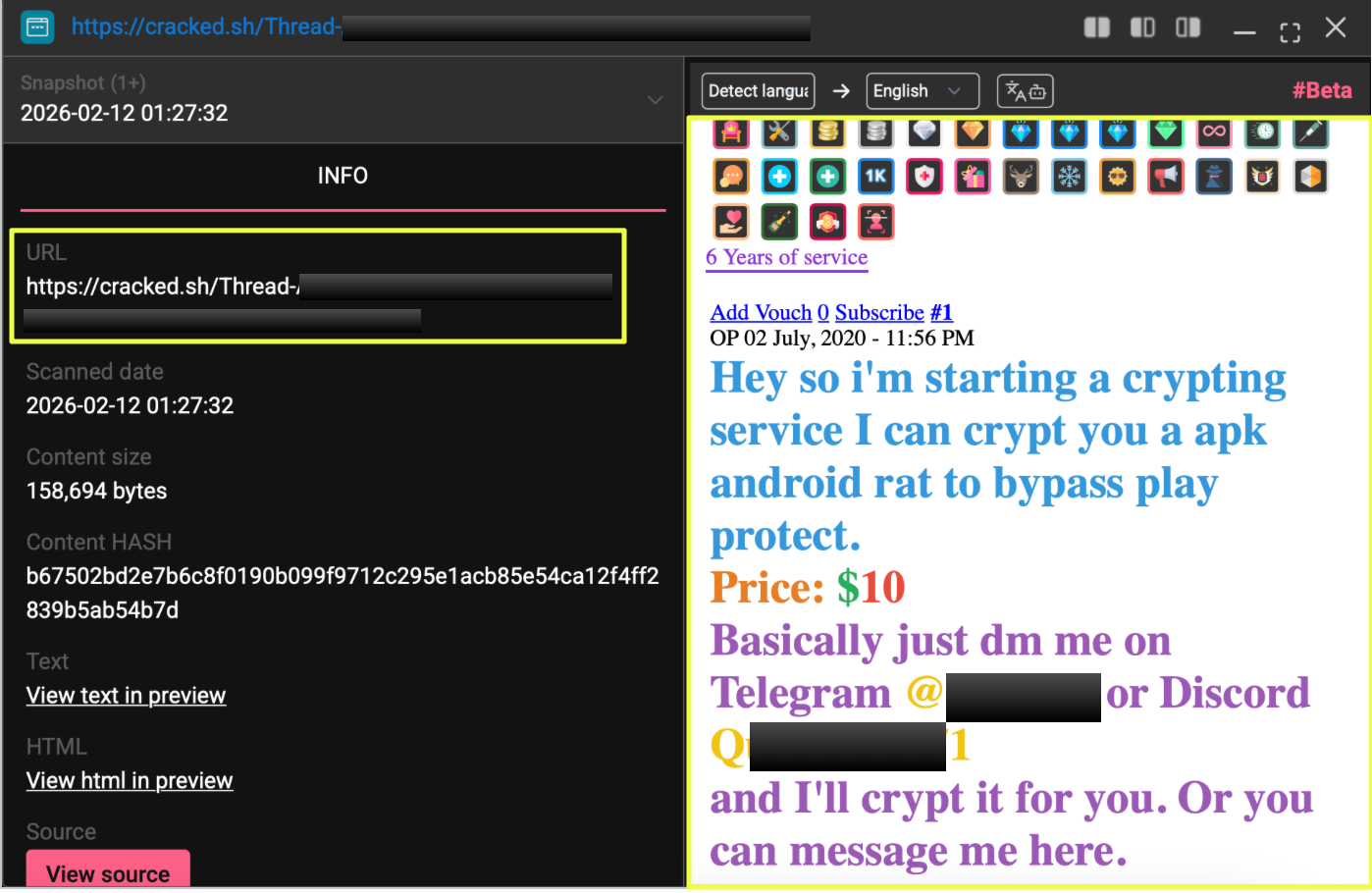
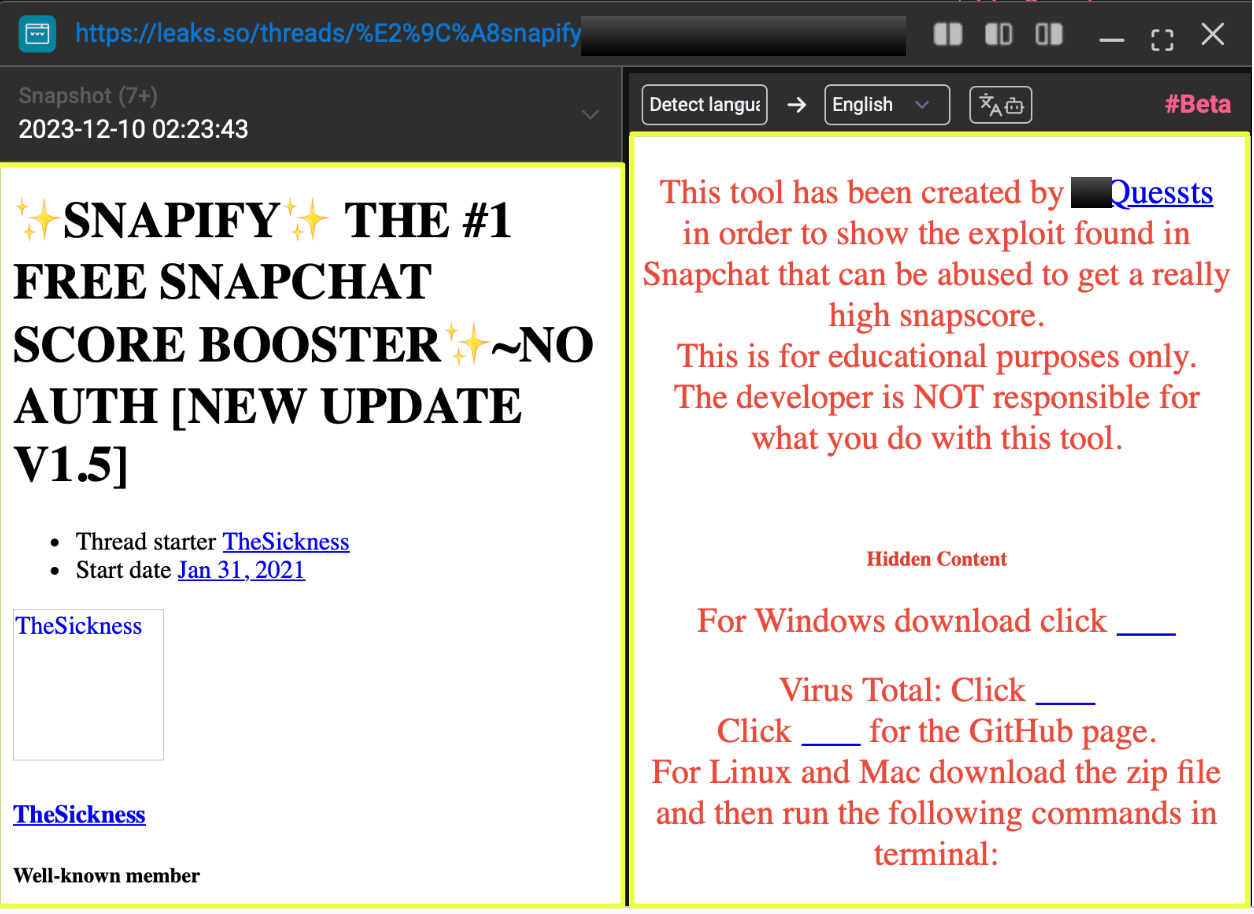
Following the discovery of the APK crypt service on cracked.sh, the next step was to pivot on the alias “Quessts” within StealthMole’s Darkweb Tracker.
This broader query returned hundreds of results: ranging from archived forum mentions to leaked datasets and exposed files. Rather than focusing on forum threads immediately, attention shifted to structured leak artifacts that could contain embedded identifiers.
Among these results were three leaked documents that referenced a GitHub repository associated with the same alias:
- https://github.com/*****/RD-Bypass-AV
 |
The repository was described within the leaked material as a Rubber Ducky script capable of downloading an executable externally while bypassing Windows antivirus protections and adding exclusions.
This finding was significant for two reasons.
First, it demonstrated that “Quessts” was associated not only with Android crypting services, but also with Windows-focused evasion tooling. This suggested broader exploit experimentation beyond mobile ecosystems.
Second, the GitHub URL served as a pivot anchor.
Rather than relying solely on forum presence, the investigation now had a direct infrastructure artifact tied to the alias.
From the leaked document reference, the investigation expanded to the full GitHub profile:
- https://github.com/******
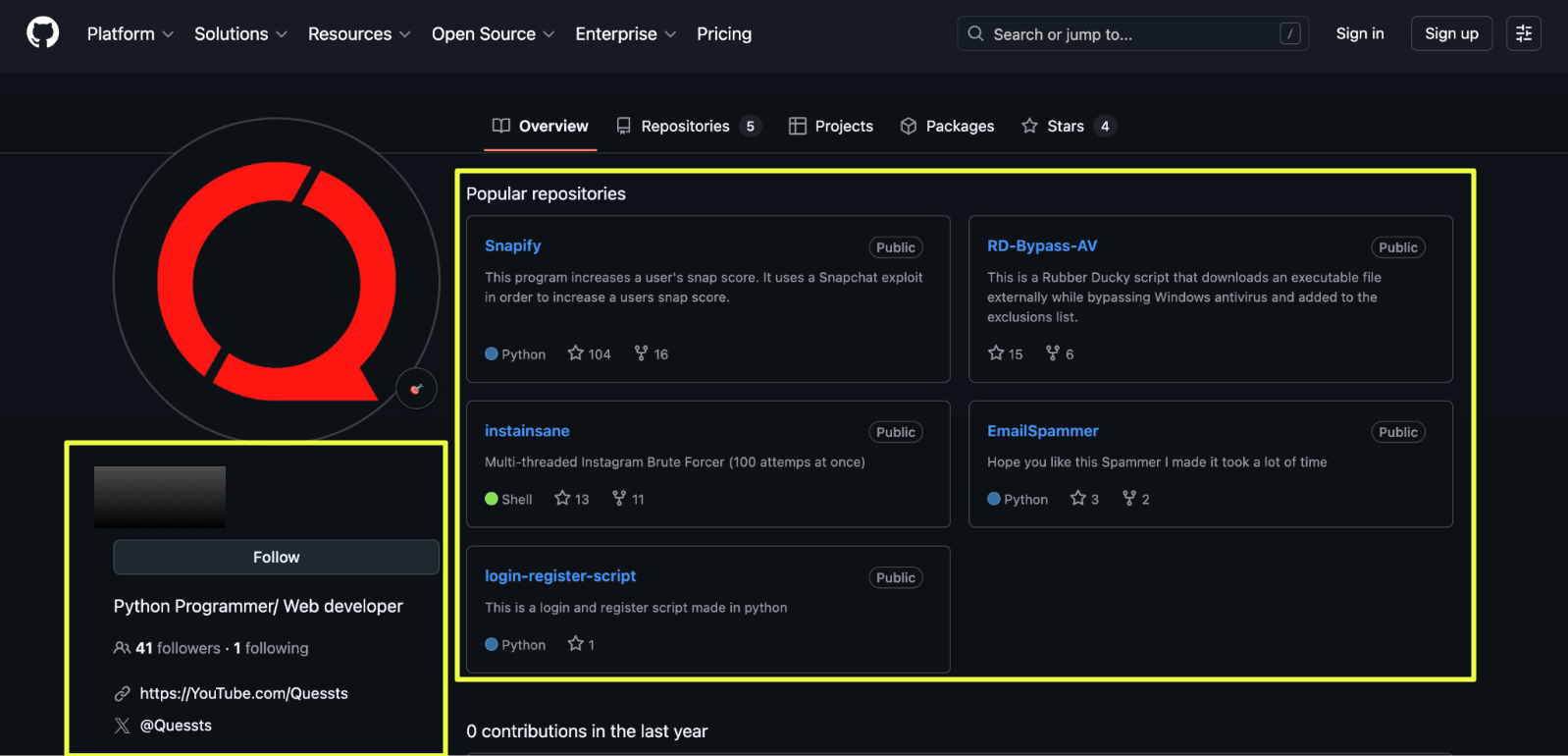 |
Consistent with the other platforms reviewed, this profile features the same red “Q” logo as its profile image. It also includes links to Quessts’ YouTube and Twitter (now X) accounts. However, both linked accounts are currently inactive.
- YouTube: https://YouTube.com/Quessts
- Twitter: https://x.com/Quessts
At this stage, the operational footprint began to widen. What initially appeared as an Android-focused crypting service was now linked to publicly accessible exploit-oriented code repositories.
The next step was to analyze the repositories themselves and determine whether this was an isolated script or part of a broader pattern of tool development and distribution.
GitHub Profile Expansion: From AV Bypass to Snapify
While reviewing the profile further, another project stood out: Snapify.
- https://github.com/******/Snapify
Unlike RD-Bypass-AV, which targeted endpoint security bypass, Snapify was positioned as a Snapchat exploit tool capable of artificially increasing Snap scores. The repository included structured installation instructions, platform compatibility notes, and usage documentation.
The layout resembled a conventional software release rather than an informal proof-of-concept drop. Dependencies were outlined. Execution instructions were clearly documented. The tone suggested accessibility, lowering the barrier for users who may not possess advanced technical knowledge.
 |
This progression reveals an important operational shift:
- The cracked.sh thread introduced an Android evasion service.
- The leaked documents revealed Windows AV bypass tooling.
- The GitHub profile demonstrated publicly accessible exploit utilities.
At this point, the investigation was no longer confined to Android crypting alone. The alias “Quessts” appeared to be operating across multiple exploit domains: mobile evasion, endpoint bypass, and social media abuse tooling.
Forum Amplification: Snapify and Cross-Community Promotion
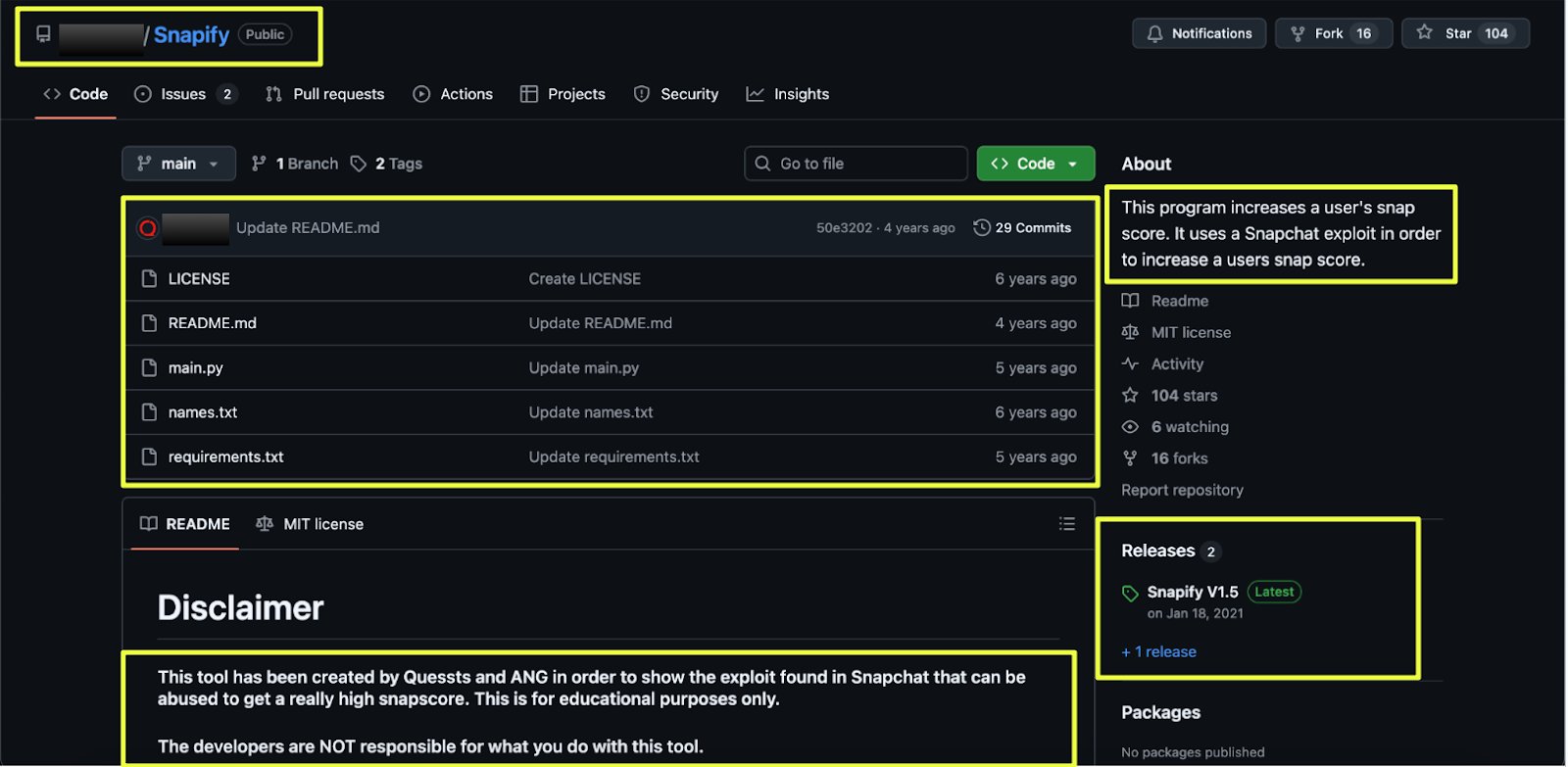
After identifying Snapify on GitHub, the next step was to determine whether the tool remained confined to open-source hosting or if it was being actively promoted within underground communities.
References to Snapify surfaced in forum discussions outside GitHub, indicating that the project was being distributed and discussed within exploit-oriented spaces.
- https://leaks.so/threads/%E2%9C%A8snapify***********9476/
 |
Although the thread was initiated by a different user (“TheSickness”), the post explicitly credited Quessts as the developer of the tool. The language mirrored the GitHub repository’s positioning, including references to updates and usage disclaimers.
This is a critical transition point.
Snapify was no longer just a repository, it was circulating within underground communities. Version updates were mentioned. Installation guidance was shared. The project was framed as a free exploit utility with ongoing improvements.
This pattern reflects deliberate promotion rather than passive hosting.
The recurring use of disclaimers, framing the tool as educational and distancing the developer from misuse, also mirrored earlier language patterns observed in other threads associated with the alias. The consistency suggests intentional messaging across platforms.
Beyond Snapify, additional forum activity under the same alias began to surface across multiple platforms, including:
- https://breached.vc/U******s
- https://breached.to/U******s
- https://breached.co/U******s
- https://cracked.io/Q*******s
- https://raidforums.com/U******s
- https://www.nulled.to/user/4******s
 |
The presence of the same alias across multiple major underground forums indicated long-term embedded participation rather than opportunistic posting.
At this stage, the investigation shifted toward mapping the breadth of activity across these platforms, including tool releases, account sales, and instructional content, to better understand whether Snapify was one of many offerings under a broader operational strategy.
Operational Diversification: Tool Releases and Account Sales
The broader forum footprint under the alias “Quessts” revealed activity extending well beyond Snapify or Android crypting services.
On RaidForums, multiple threads were identified spanning different categories, including exploit tooling, instructional content, and direct marketplace sales.
One thread focused on a leaked DDoS script, referencing “SAPHYRA” and claiming prior high-profile usage. The post included a disclaimer advising users not to misuse the tool. This language pattern mirrored disclaimers observed in other posts linked to the alias, positioning releases as informational or educational while still distributing operational tooling.
- https://raidforums.com/Thread-SAPHYRA*************T
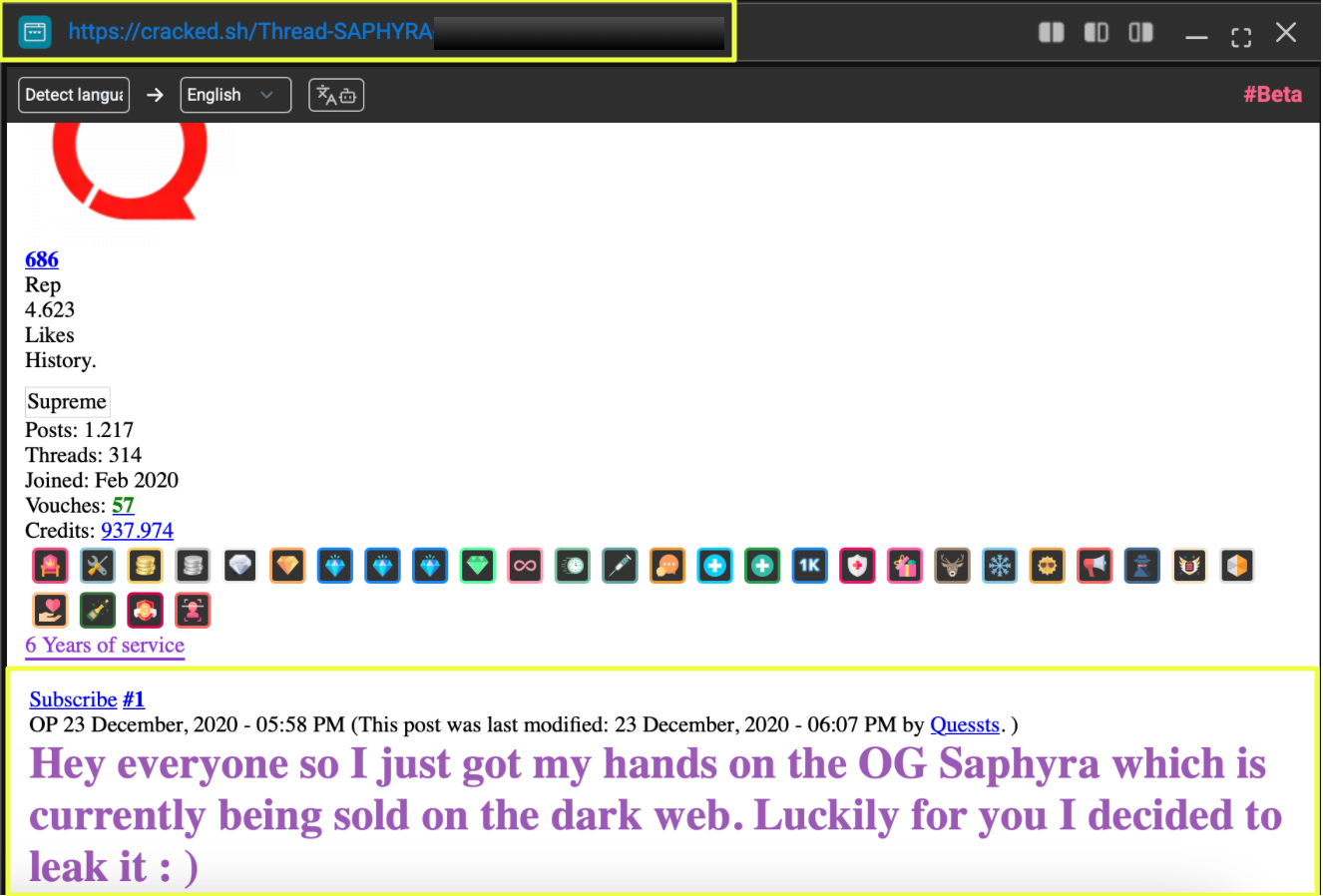 |
Additional activity on RaidForums demonstrated instructional engagement. Threads discussing Linux installation and technical setup indicated an effort to build credibility within the community beyond pure sales activity.
More notably, a marketplace-oriented thread advertised the sale of fully verified Paxful accounts:
- https://raidforums.com/Thread-SELLING******PAXFUL****ACCOUNTS
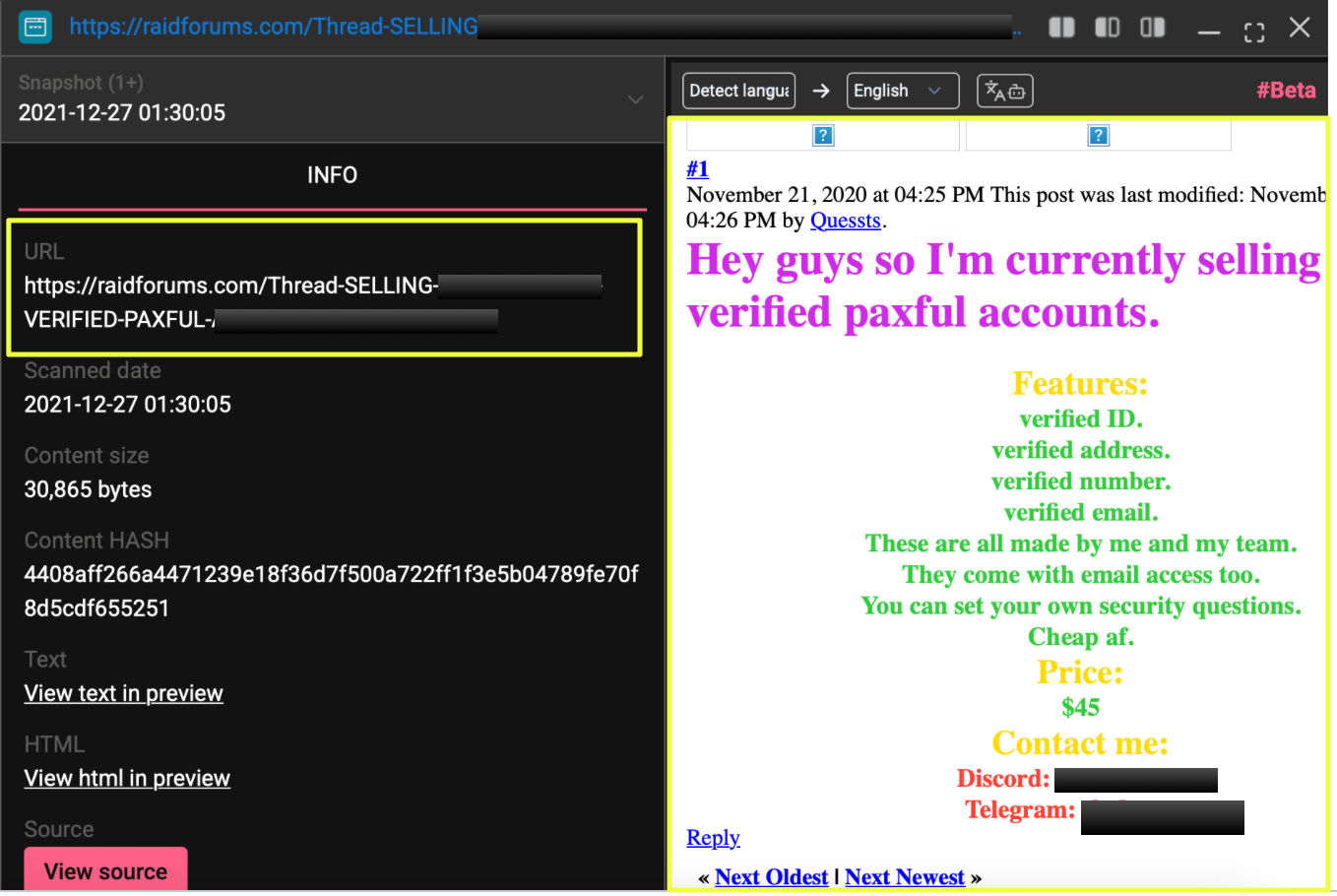 |
The post described accounts verified with identification documents, phone numbers, and address details. Contact methods listed in the thread included:
- Discord: Q******1
- Telegram: @Q******s
 |
This artifact is significant because it links the exploit developer persona to direct account monetization. Unlike Snapify, which operated as a publicly distributed tool, the Paxful thread demonstrates structured revenue generation through access sales.
In parallel, additional content under the alias included Android-related modifications and adult cam tool releases, indicating involvement in modded application ecosystems:
- https://raidforums.com/Thread-Pu************18
 |
The combination of exploit tools, account sales, and modded applications reflects a hybrid operational model. Rather than specializing in a single niche, the alias appears to move fluidly between:
- Exploit development
- Tool distribution
- Account marketplace activity
- Community engagement
At this point, the investigation began to show a recurring pattern: consistent alias usage, recurring contact infrastructure, and multi-category participation across underground forums.
Real-Time Distribution: Telegram Presence and Community Activity
After mapping forum-based activity, the next logical pivot was Telegram, a platform frequently used for exploit promotion, file distribution, and direct client communication.
A Telegram account using the same alias was identified. The account displayed consistent branding, including the same logo previously observed in forum threads. This continuity reinforced identity persistence across platforms.
- https://t.me/Q********s
Beyond the direct user profile, references to Snapify were located in Telegram channels where installation instructions and promotional messaging were shared. One such channel was:
- https://t.me/ev******t
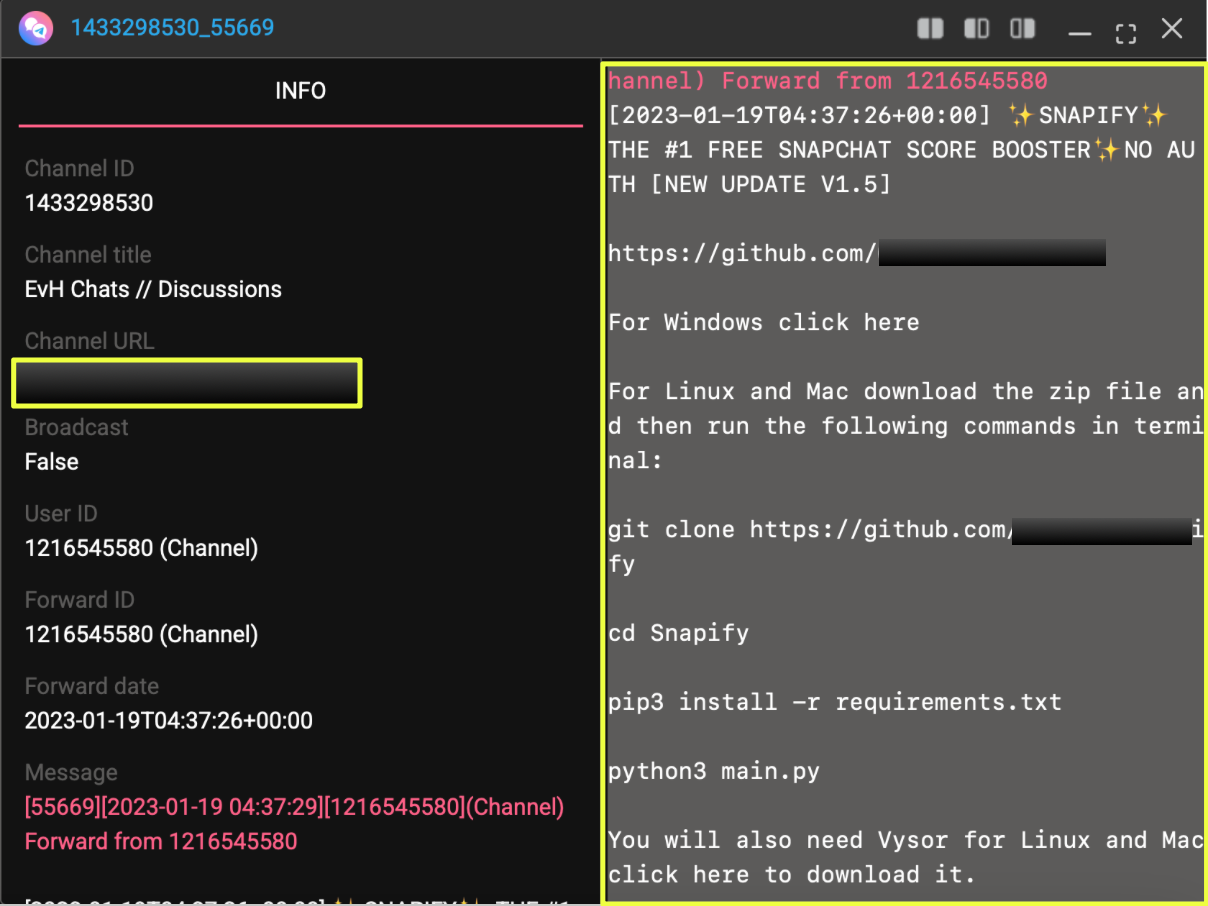 |
In this channel, Snapify was promoted alongside its GitHub repository:
- https://github.com/*******/Snapify
The messaging included update references and installation guidance, mirroring content found in forum posts. This suggests deliberate cross-platform amplification rather than organic redistribution.
Additional activity was observed within a Telegram channel titled “Doxbin,” where the alias engaged in discussions and technical exchanges:
- https://t.me/+V**************eM
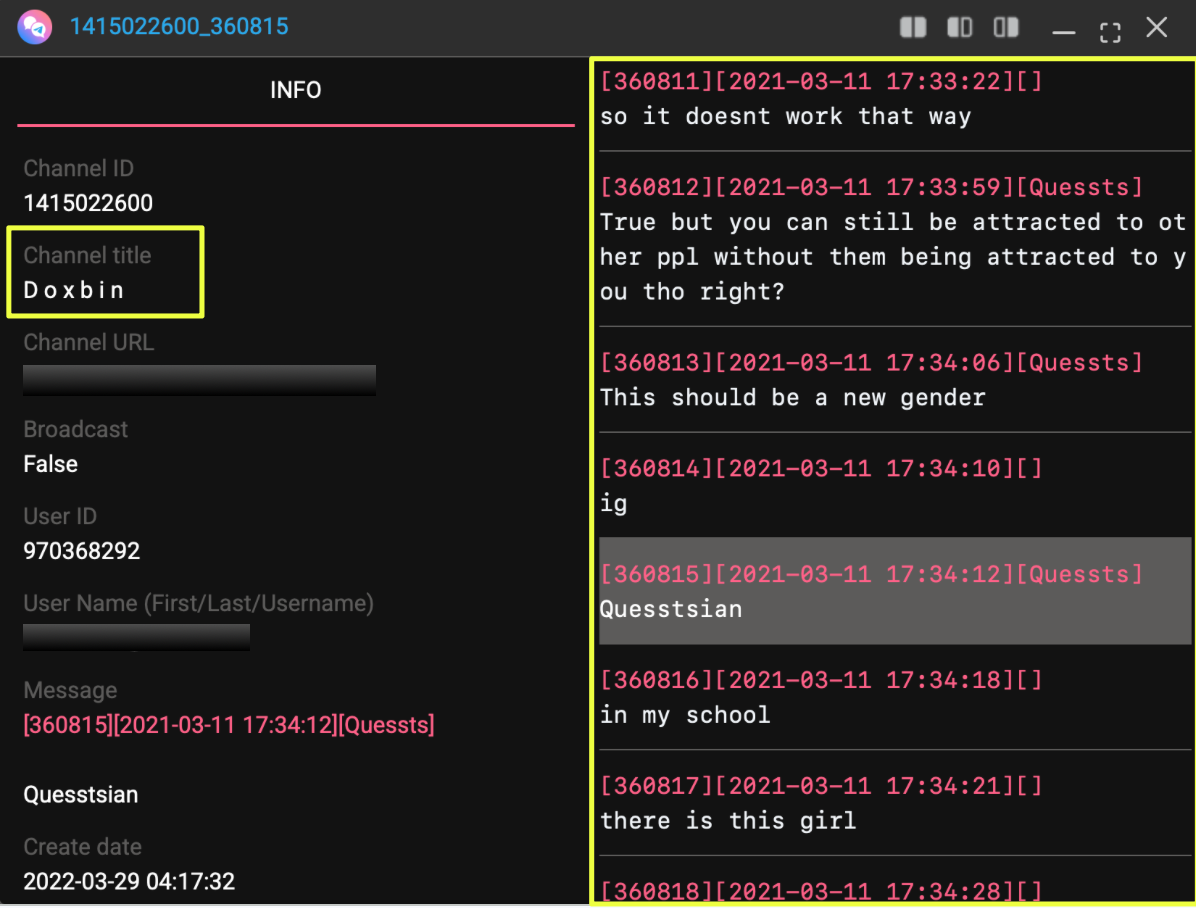 |
Participation extended beyond tool promotion. The account was active in discussions within exploit-focused and bug bounty groups, offering technical input and engaging with other users. This behavior indicates community embedding rather than purely transactional presence.
Notably, within Telegram conversations, references to Sellix.io were made in the context of purchasing digital goods such as VMware keys. This aligns with earlier Sellix storefront mentions tied to the alias and reinforces monetization familiarity.
Telegram activity demonstrates three important operational characteristics:
- Direct tool promotion beyond static forums
- Real-time engagement with exploit-oriented communities
- Continued use of consistent alias branding
By this stage, the alias “Quessts” appeared active across:
- Underground forums
- GitHub repositories
- Telegram channels
- Marketplace ecosystems
The investigation was no longer centered on a single exploit or service offering. Instead, it revealed a recurring pattern of tool release, cross-platform promotion, and monetization under a unified online persona.
Monetization Layer: Cryptocurrency Activity and Sellix Infrastructure
Beyond forum promotion and tool distribution, the alias “Quessts” demonstrated structured monetization behavior.
On the cracked.sh profile, a Bitcoin address was publicly listed:
- BTC Address: 1Ag*********************rt
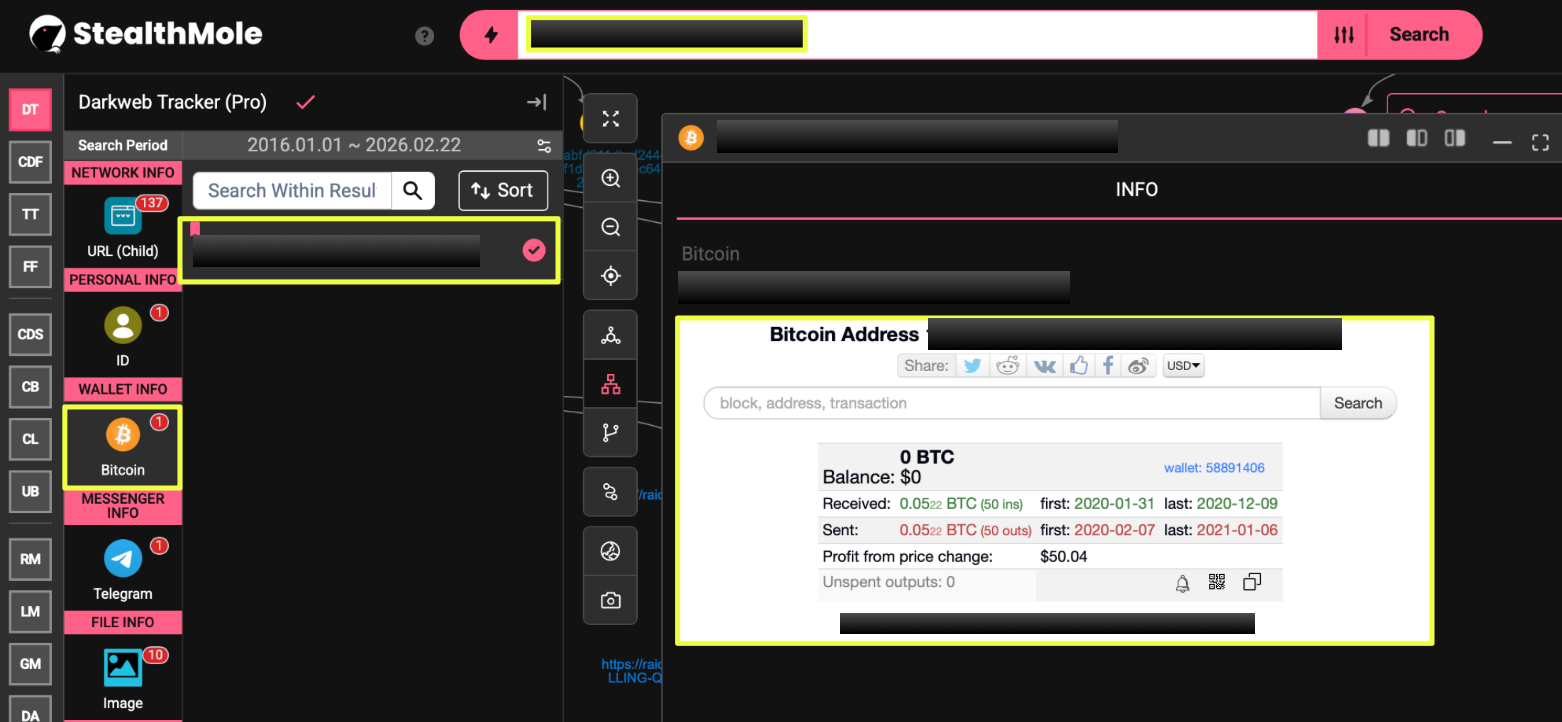 |
Blockchain analysis of this address revealed transaction activity between 2019 and 2021. The wallet received multiple small-value transactions consistent with low-cost service payments. The cumulative transaction pattern suggested repeated inbound transfers rather than a single lump-sum payment, aligning with the pricing model of services such as APK crypting.
Notably, the wallet balance was later fully transferred out, indicating consolidation behavior rather than passive holding.
In parallel, a Sellix storefront associated with the alias was identified:
- https://q*********s.sellix.io
 |
Sellix is commonly used for selling digital goods, keys, accounts, and software tools. The presence of a dedicated storefront reinforces the service-oriented operational model observed in forum threads. Rather than relying solely on private messaging or informal transfers, the storefront suggests structured productization.
Overall, the BTC wallet and Sellix infrastructure demonstrate that the activity under the alias was not limited to experimentation or reputation-building. It reflected a revenue-generating model integrated into underground commerce platforms.
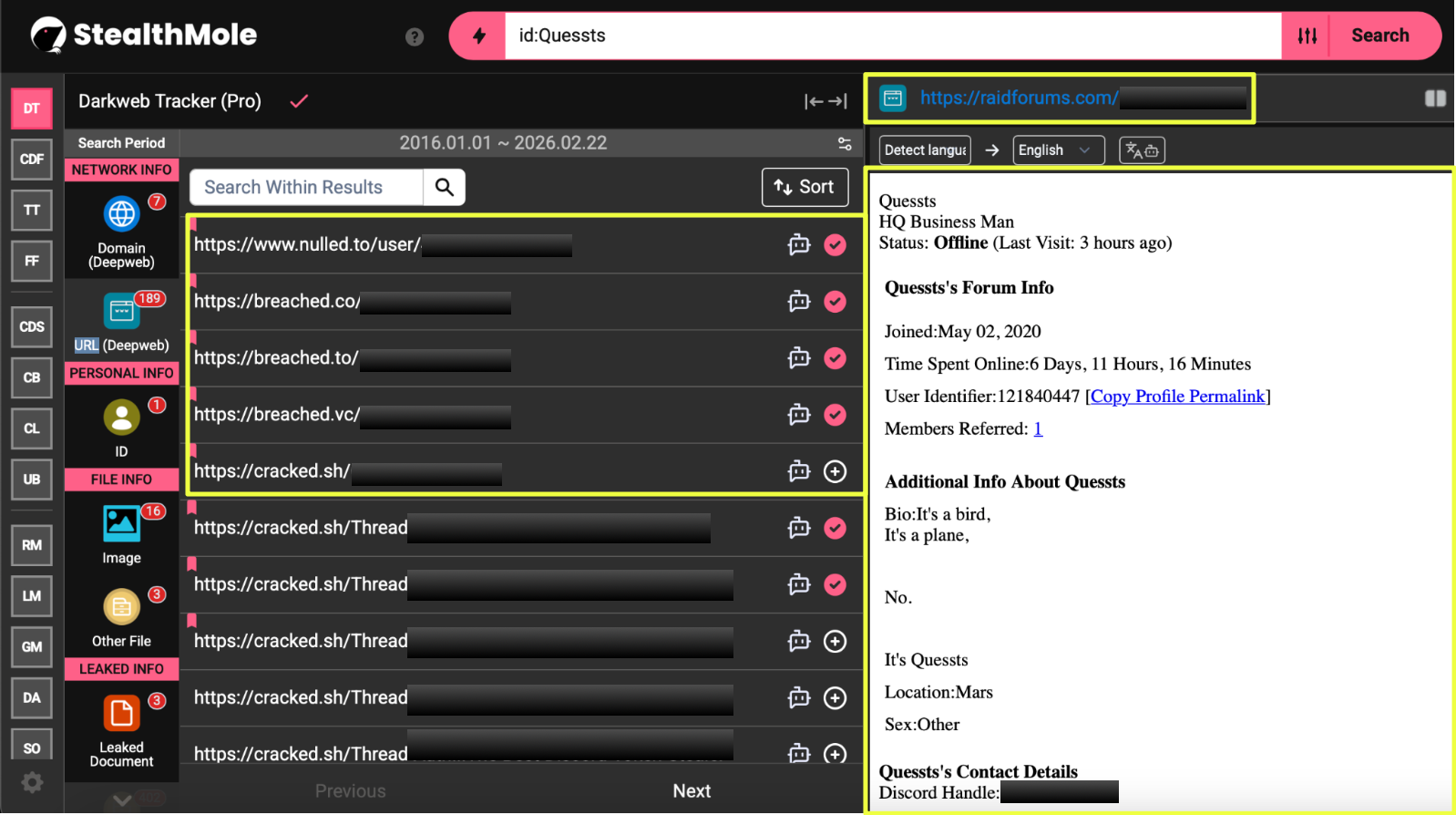
Identity Correlation: Leaked Datasets and Email Artifacts
With cross-platform activity established across forums, GitHub, and Telegram, the investigation returned to StealthMole’s Darkweb Tracker to examine whether the alias “Quessts” appeared within structured leak datasets.
A broader query of the username surfaced hundreds of results, including database leaks and archived SQL files. While many references were repetitive or contextually unrelated, several structured leak files contained identifiable artifacts.
As mentioned earlier, three leaked documents referenced the GitHub repository. These references reinforced the association between the alias and Windows AV bypass tooling. However, they did not yet reveal personal identifiers.
Further analysis of additional leaked datasets produced more concrete linkage. Within a RaidForums SQL leak, a user record under the alias “Quessts” contained the following artifacts:
- Email: m********1@gmail.com
- Discord: Q********1
- Date of Birth (as stored in database): 6-9-2000
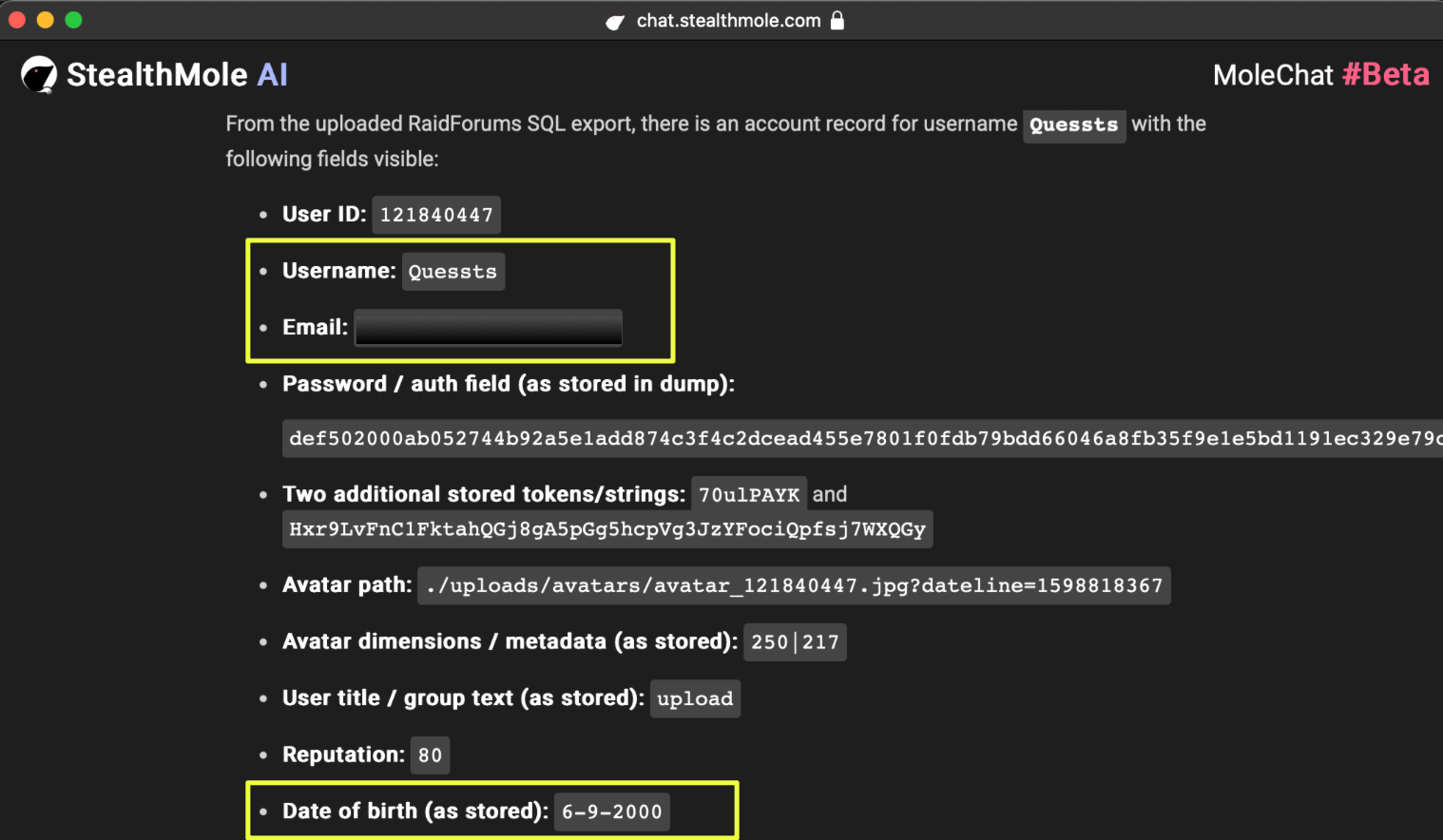 |
The presence of the Discord handle Q*****1 was particularly significant, as the same contact information appeared in earlier marketplace threads, including the Paxful account sales post.
This established a high-confidence linkage between:
- Forum alias “Quessts”
- Discord contact: Q*********1
- Email: m********1@gmail.com
To evaluate further correlation, the email address m*******1@gmail.com was analyzed through StealthMole’s Combo Binder. The results indicated credential exposure, including a password string matching the alias “Quessts.”
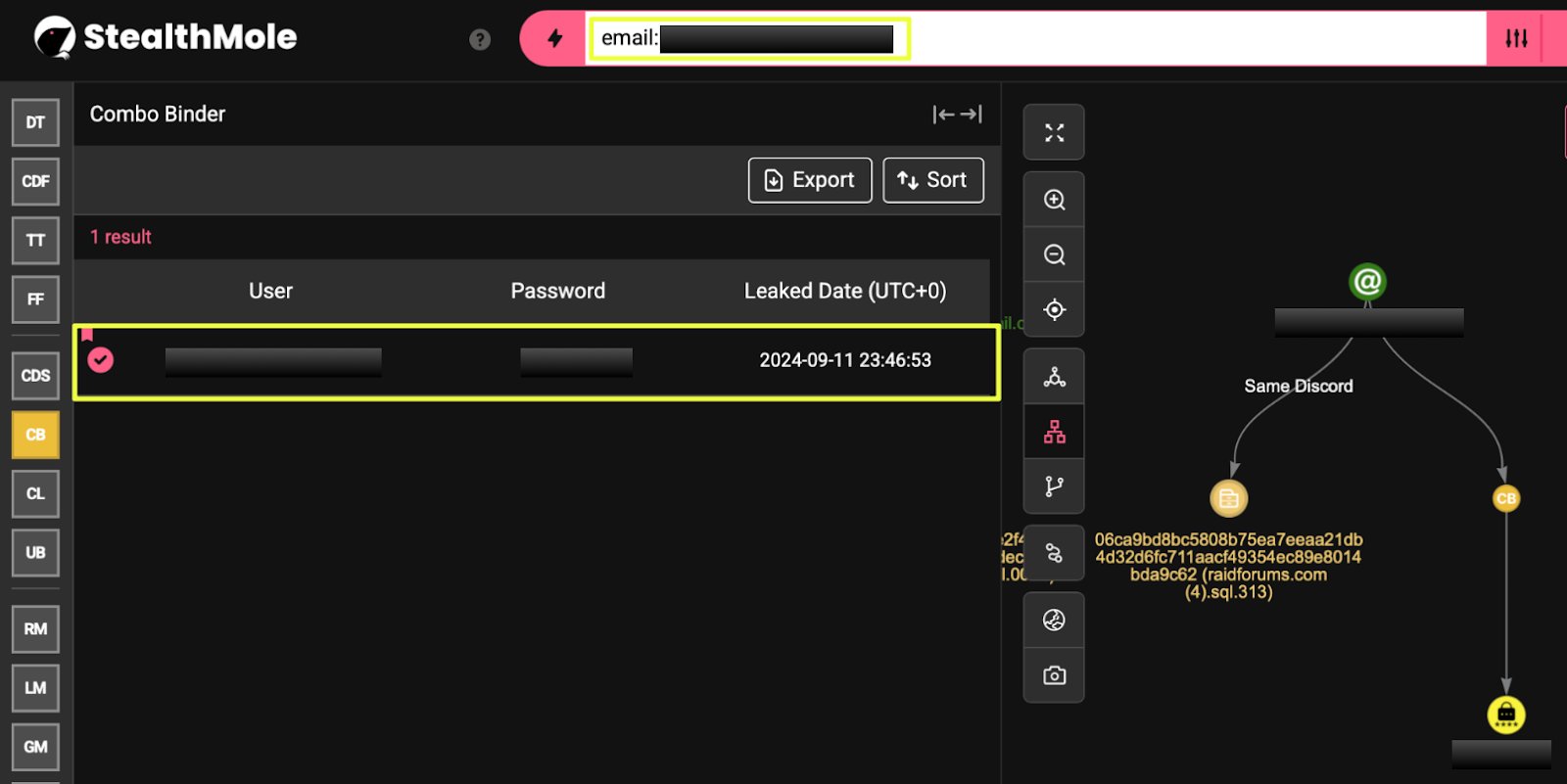 |
However, additional datasets revealed a second email address exhibiting naming similarity:
- al******f2002@gmail.com
Initially, this appeared to be a naming similarity. However, further analysis significantly strengthened the correlation.
When al*****f2002@gmail.com was queried in StealthMole’s Darkweb Tracker, a leaked document was identified in which the email was directly associated with the username: Quessts. This moved the linkage beyond similarity into documented alias association.
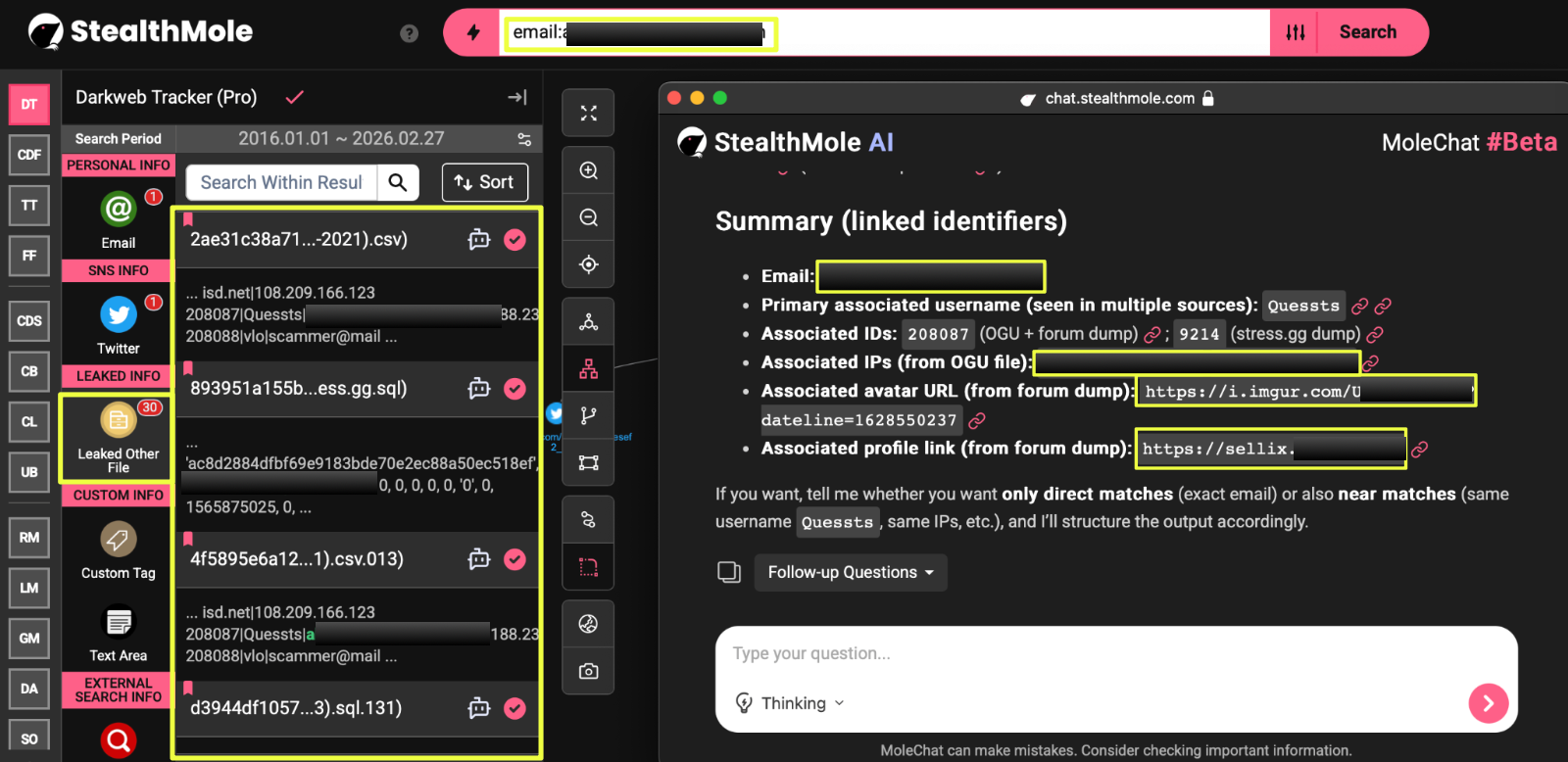 |
Additional artifacts extracted from the same dataset included two IP addresses:
- 1*8.**6.**9.**2 (Kuwait)
- 3*.*9.**9.**2
The geographic reference to Kuwait is notable when viewed alongside the broader identity indicators, though IP-based inference remains limited without temporal validation.
Further convergence was identified through an associated avatar URL found in the forum dump:
- https://i.imgur.com/U******0.jpg?dateline=1628550237
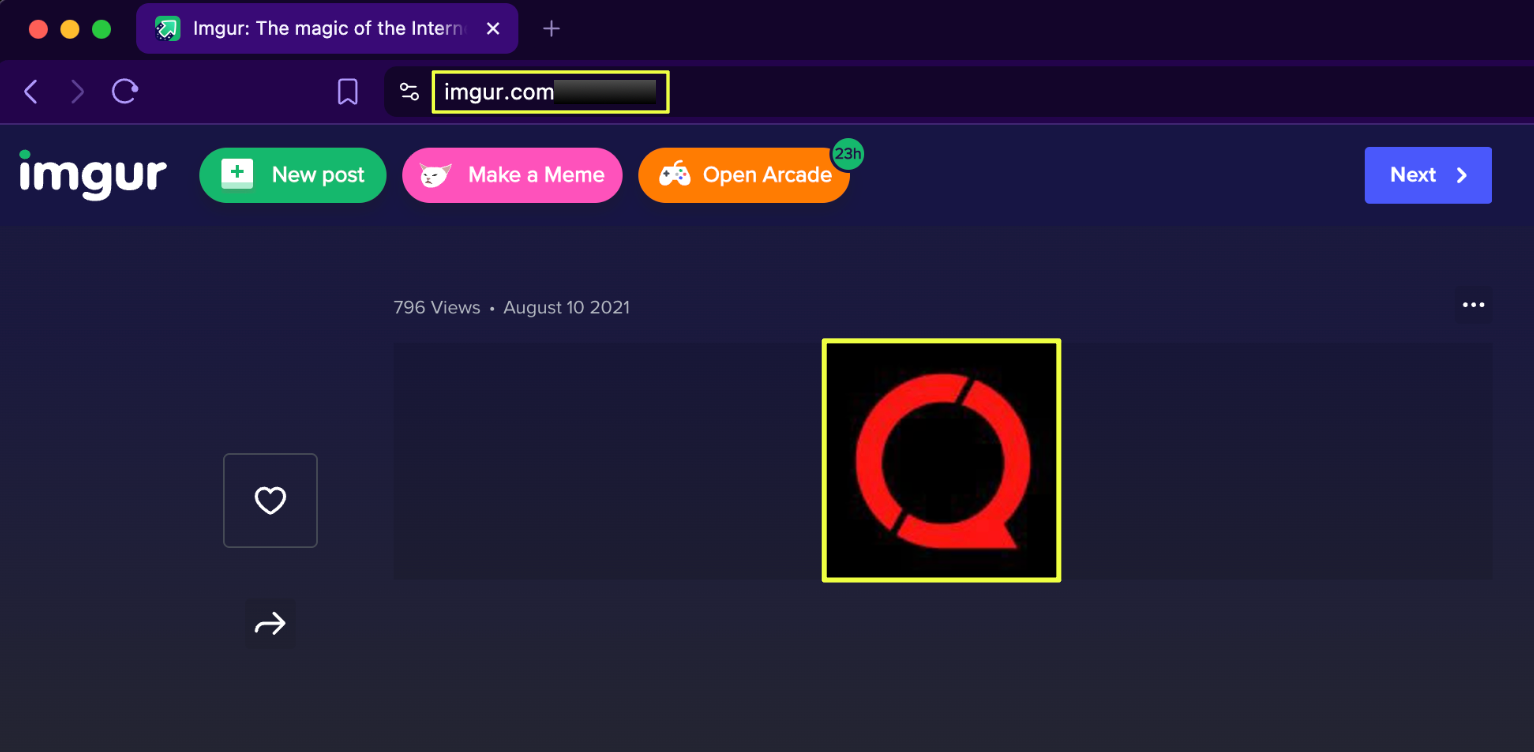 |
When accessed, the image displayed the same red circular “Q” logo consistently observed across:
- Cracked.sh thread branding
- GitHub profile imagery
- Telegram profile imagery
This visual continuity strengthens infrastructure-level identity persistence.
In addition, the email al*******f2002@gmail.com was found linked to the Sellix storefront:
- https://sellix.io/Quessts
This directly connects the secondary email cluster to the monetization infrastructure previously attributed to the alias. Additional correlation further indicated that the email al******f2002@gmail.com was associated with a Twitter account:
- https://twitter.com/Mo*******f2_
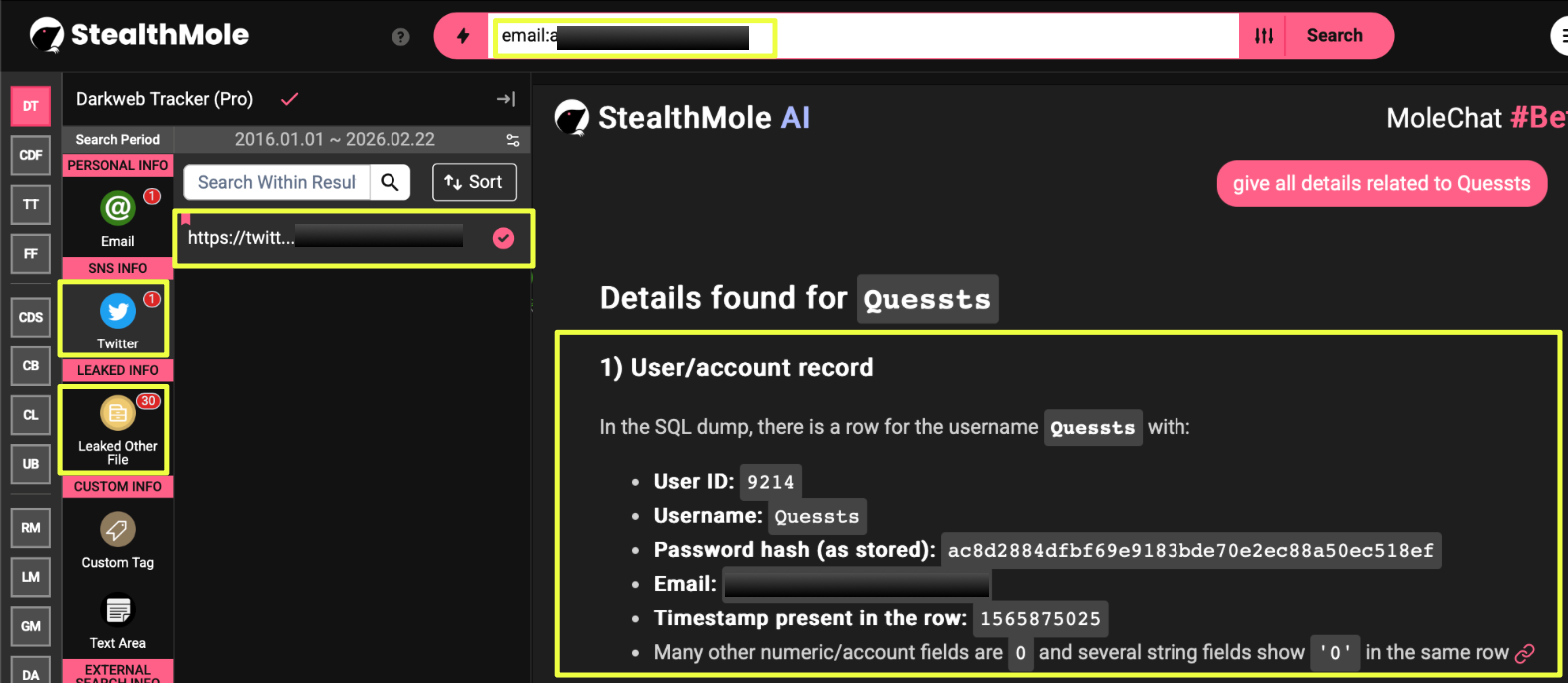 |
Although the account is currently inactive, the username suggests a possible personal identity reference consistent with the naming pattern observed in both Gmail addresses.
Conclusion
The investigation into the alias “Quessts” reveals a consistent and structured operational pattern rather than isolated experimentation. Beginning with an Android-focused APK crypting service, the activity expanded into Windows AV bypass tooling, social media exploit utilities, account sales, and cross-platform promotion.
What stands out is not any single tool, but the model itself. The same alias appeared across forums, GitHub repositories, Telegram channels, and monetization platforms with consistent branding and recurring contact infrastructure. Exploit development, community engagement, and revenue generation operated in parallel.
Identity analysis further strengthened the case. Leaked datasets linked the alias to multiple email addresses, shared avatar artifacts, IP references, and storefront infrastructure, forming a converging identity cluster rather than fragmented associations. While cautious attribution discipline remains necessary, the weight of overlapping technical and credential-based artifacts supports a unified operational persona.
The case illustrates how modern underground operators do not confine themselves to a single niche. Instead, they move fluidly between exploit tooling, account marketplaces, and distribution ecosystems, leveraging visibility and reputation to sustain activity across multiple platforms.
Editorial Note
Investigations within underground ecosystems rarely offer absolute certainty. Aliases evolve, datasets are fragmented, and identity overlaps can blur boundaries between confirmed linkage and plausible association. This case demonstrates how StealthMole enables structured mapping of operational behavior even when full attribution remains unresolved.
To access the unmasked report or full details, please reach out to us separately.
Contact us: support@stealthmole.com
Labels: Threat Actor
.svg)
.svg)
.svg)