IndoHaxSec: Inside the Expanding Network of a Pro-Palestinian Hacktivist Collective
 |
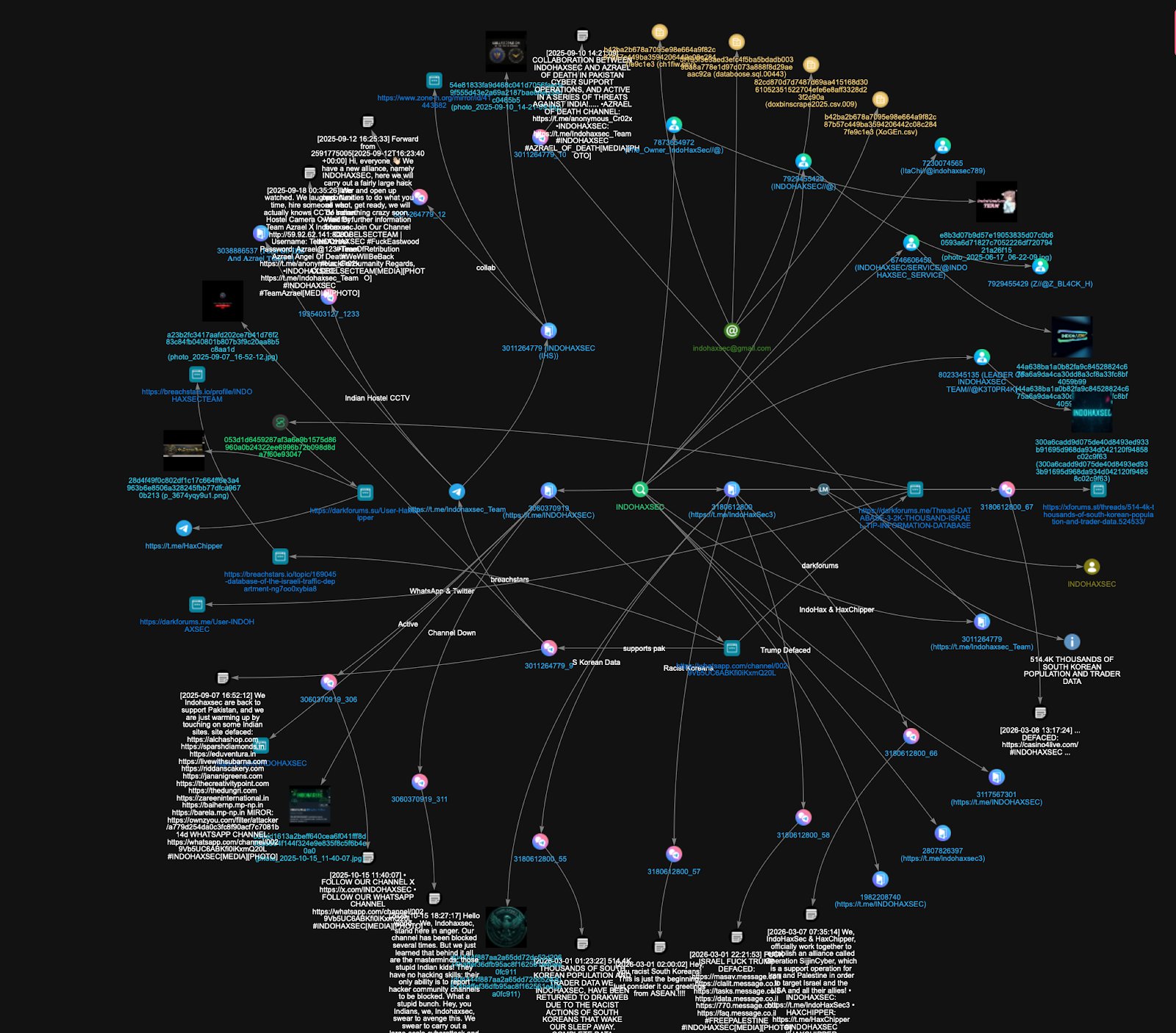
In recent years, hacktivist groups have increasingly emerged as visible actors in the broader landscape of cyber operations. Often forming around shared political or ideological motivations, these collectives use digital attacks, data leaks, and public messaging to amplify their narratives and demonstrate technical capability. Among the groups that have surfaced within this environment is IndoHaxSec, a collective that presents itself as an Indonesian hacktivist entity and publicly frames its activities around political causes, particularly those connected to the Israel–Palestine conflict.
IndoHaxSec has appeared across several online platforms where it promotes its identity, claims cyber operations, and communicates with supporters. Like many hacktivist groups, its presence is distributed across multiple channels rather than centralized in a single space. Messages, attack claims, and other artifacts are shared through social platforms, messaging channels, and underground forums, creating a scattered but traceable digital footprint.
While the group positions itself as a politically motivated actor, the extent of its operations, its alliances with other hacktivist collectives, and the broader network surrounding it remain relatively unclear. Public claims and online messaging often provide only a partial view of how such groups function or how their activities connect across platforms.
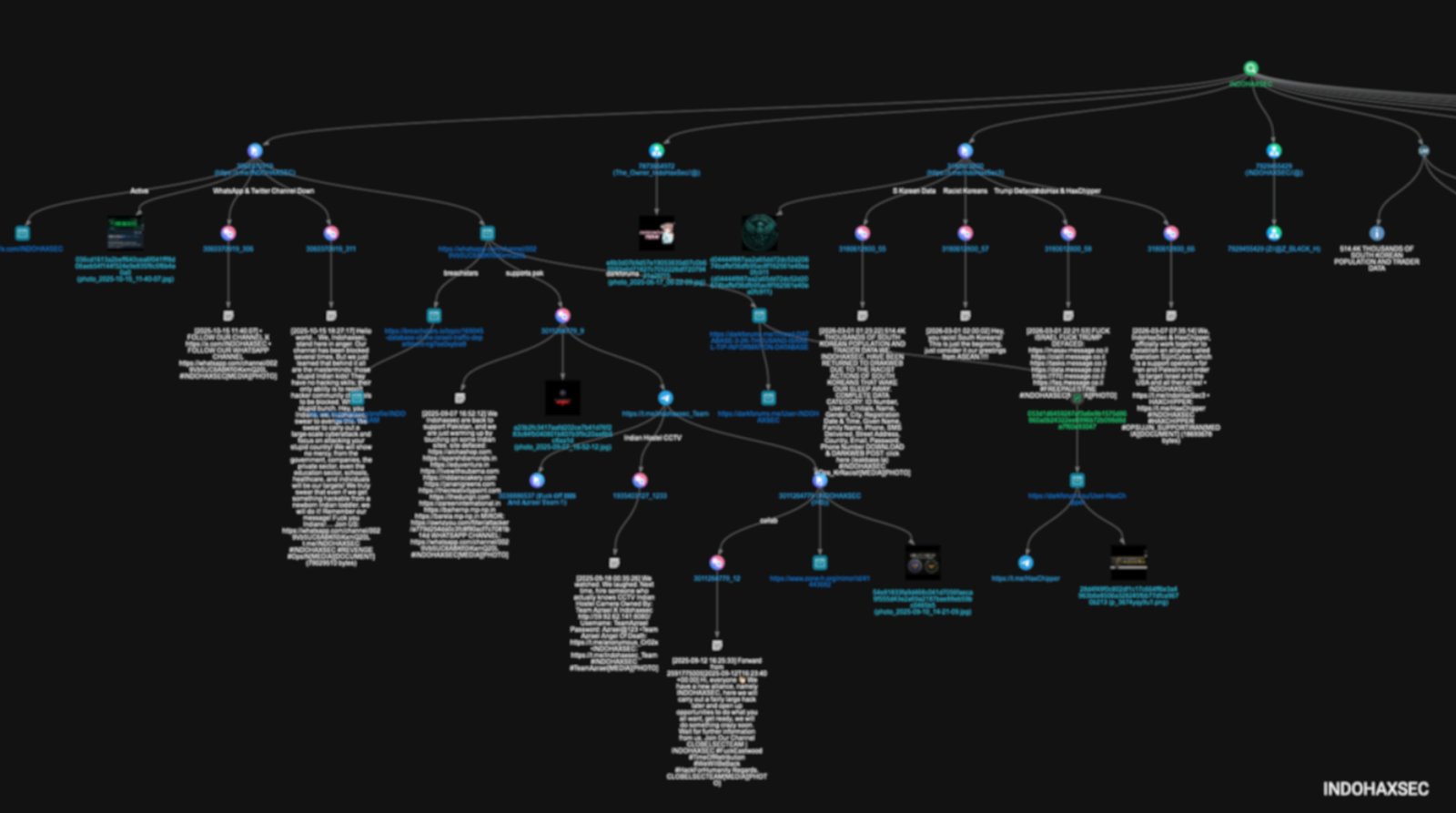
This report traces IndoHaxSec’s digital footprint across several platforms in order to better understand how the group operates, how it communicates, and how it positions itself within the wider hacktivist landscape. By piecing together artifacts from defacement monitoring tools, Telegram channels, leak forums, and other open sources, the investigation reveals an expanding network of activity that goes well beyond isolated attack claims.
Incident Trigger and Initial Investigation
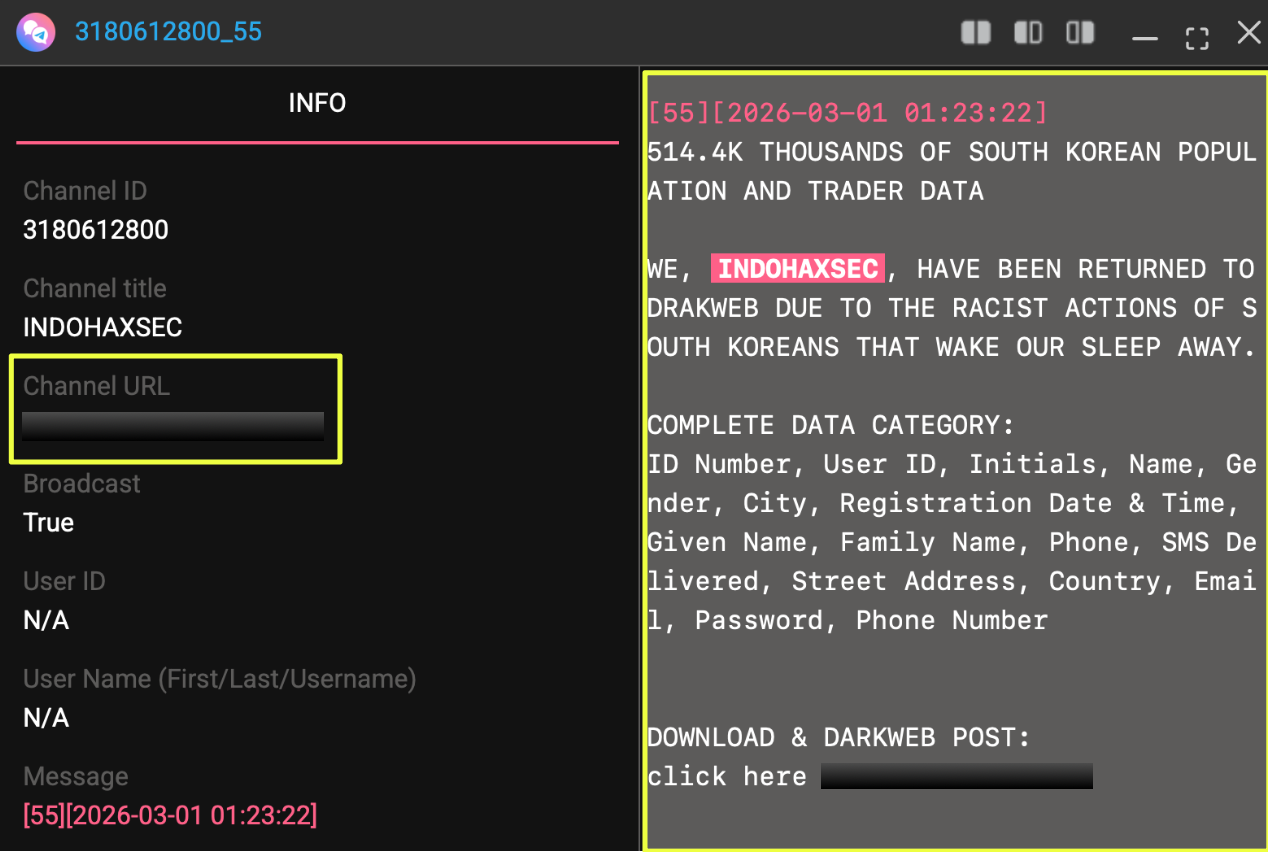
The investigation into IndoHaxSec began after the group appeared in connection with a data leak involving South Korean users. The breach, which was advertised online under the title “514.4K THOUSANDS OF SOUTH KOREAN POPULATION AND TRADER DATA,” drew attention due to both the scale of the dataset and the explicit attribution to IndoHaxSec.
- https://xforums.***/threads/514********************3/
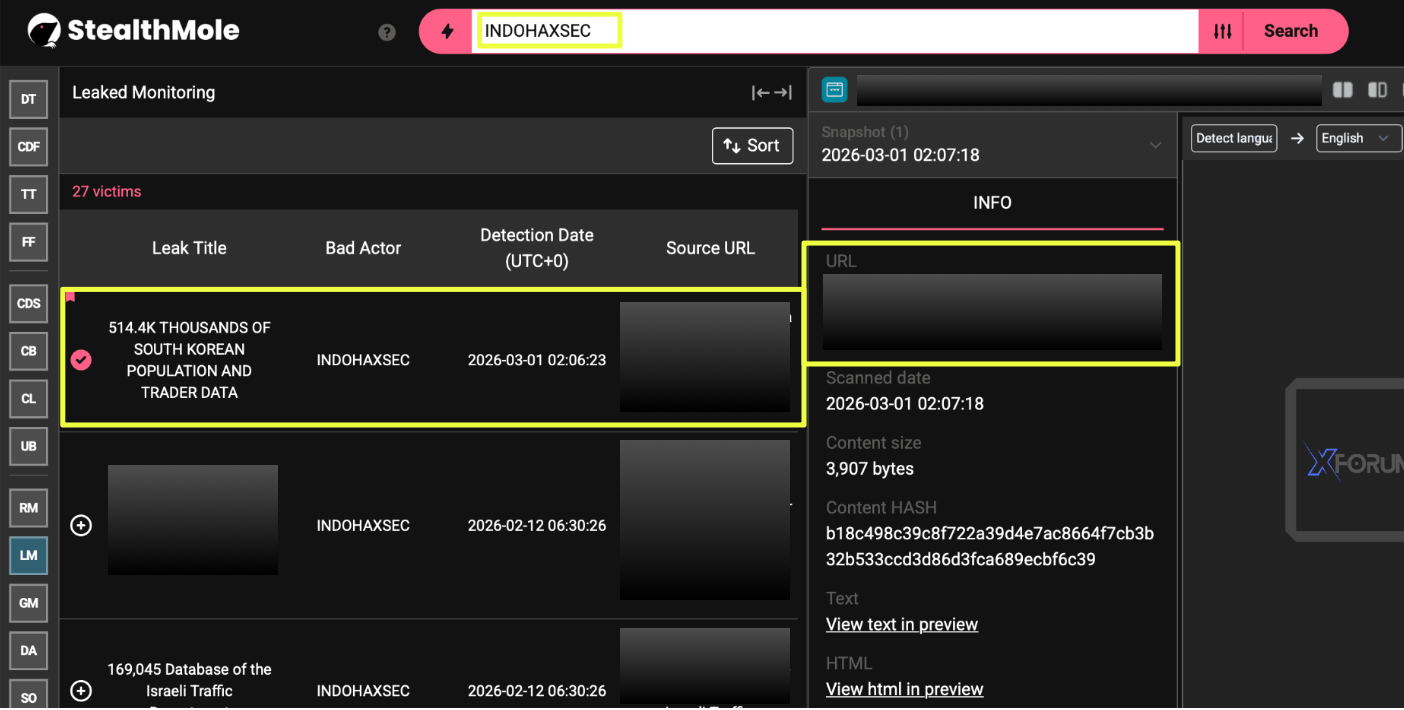 |
To better understand the scope of the group’s activity, the keyword “INDOHAXSEC” was queried across multiple modules within the StealthMole platform. The first step involved examining the Leaked Monitoring module, which indexes publicly advertised breaches, database leaks, and stolen data shared across underground forums and related platforms.
The search results quickly revealed that the South Korean dataset was not an isolated incident. StealthMole’s indexing showed that 27 separate leak-related entries associated with IndoHaxSec had been detected between December 2024 and March 2026. These entries included datasets allegedly originating from multiple countries and sectors, indicating that the group had been active across several leak forums and platforms over an extended period of time.
To further understand the nature of these activities, additional StealthMole modules were queried using the same keyword. This included the Defacement Alert module, which monitors website defacements, as well as Government Monitoring, which tracks incidents involving government-related data exposures. Together, these tools provided a broader view of the group’s publicly visible operations and helped establish an initial timeline of IndoHaxSec’s activity across different types of cyber incidents.
These early findings suggested that IndoHaxSec’s presence extended beyond a single breach claim and pointed toward a wider pattern of activity across multiple platforms. As a result, the investigation expanded to examine the group’s online infrastructure, including the messaging channels and forums where its operations and announcements were being promoted.
Mapping IndoHaxSec’s Online Presence
Following the initial findings from StealthMole’s monitoring modules, the investigation shifted toward identifying the online spaces where IndoHaxSec promotes its activities and communicates with its audience. Hacktivist groups often rely heavily on messaging platforms and social media to publicize attacks, share leaked data, and build alliances with other collectives. Tracing these channels therefore provides important insight into how such groups operate and how their narratives spread online.
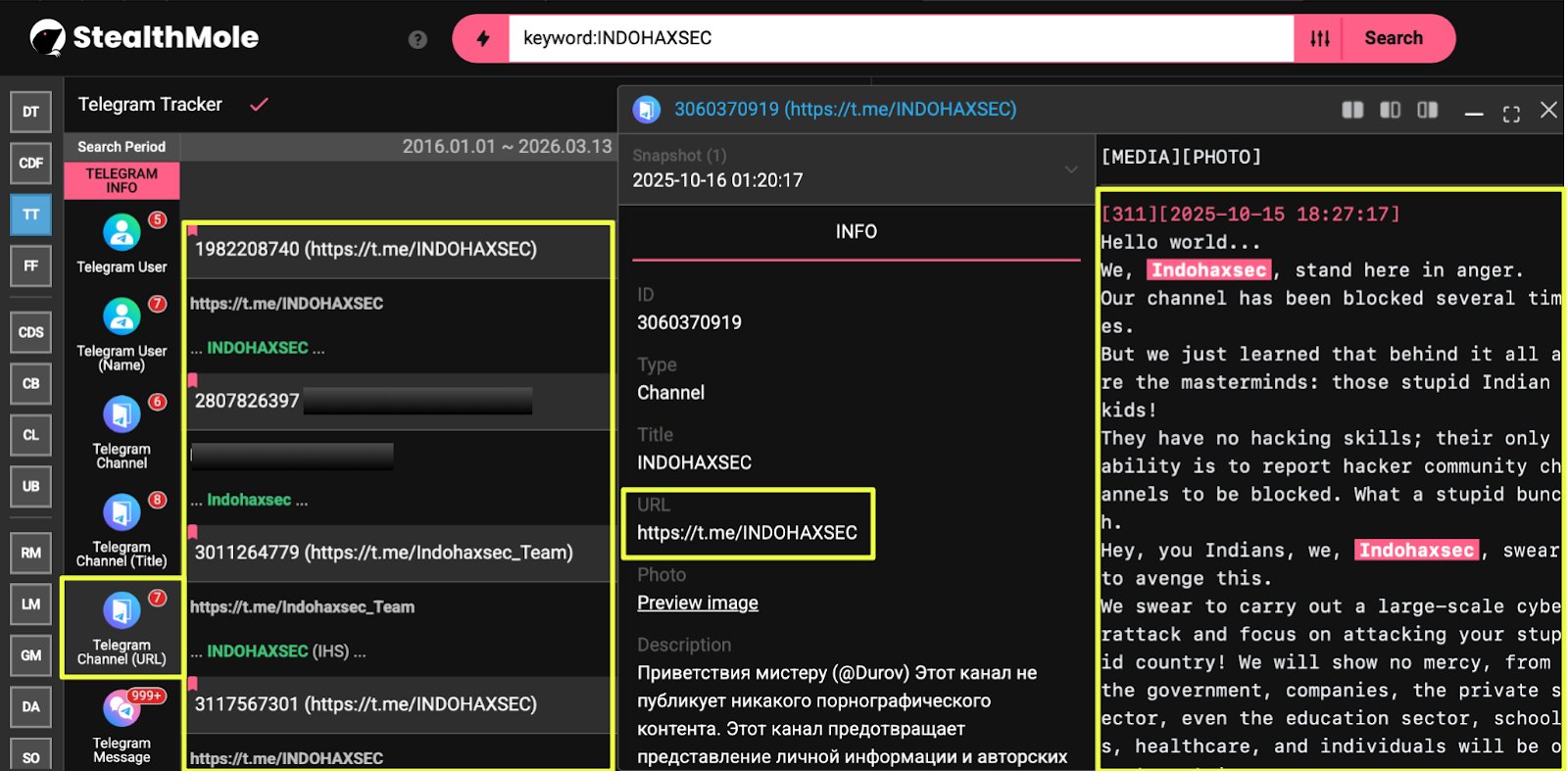
Using StealthMole’s Telegram Tracker, several Telegram accounts operating under the IndoHaxSec name were identified. These accounts appear to represent different roles within the group and openly reference IndoHaxSec in their profile descriptions or usernames.
The following Telegram accounts were identified during the investigation:
- Telegram ID: 80********5
- Display Name: LEADER OF INDOHAXSEC TEAM
- Username: @K3******K
- Telegram ID: 67******50
- Display Name: INDOHAXSEC SERVICE
- Username: @IN******E**S******E
- Telegram ID: 79********29
- Display Name: INDOHAXSEC
- Username: @hm*****7
- Telegram ID: 7873654972
- Display Name: The_Owner_IndoHaxSec
- Telegram ID: 7230074565
- Display Name: ItaChi
- Username: @indo******9
Historical indexing within StealthMole also showed that the account associated with Telegram ID: 7929455429 previously used the username @Z_BL4CK_H before switching to @hmei7 on 2025-12-05. The earlier alias resembles the name of another Indonesian hacktivist group, Z BL4CK H4T, although the available data does not confirm a direct connection between the two.
In addition to individual accounts, several Telegram channels associated with the group were discovered. These channels appear to function as public communication hubs where IndoHaxSec posts announcements, shares defacement claims, and promotes leaked datasets.
The following Telegram channels were identified during the investigation:
- https://t.me/INDOHAXSEC
- https://t.me/indo*****
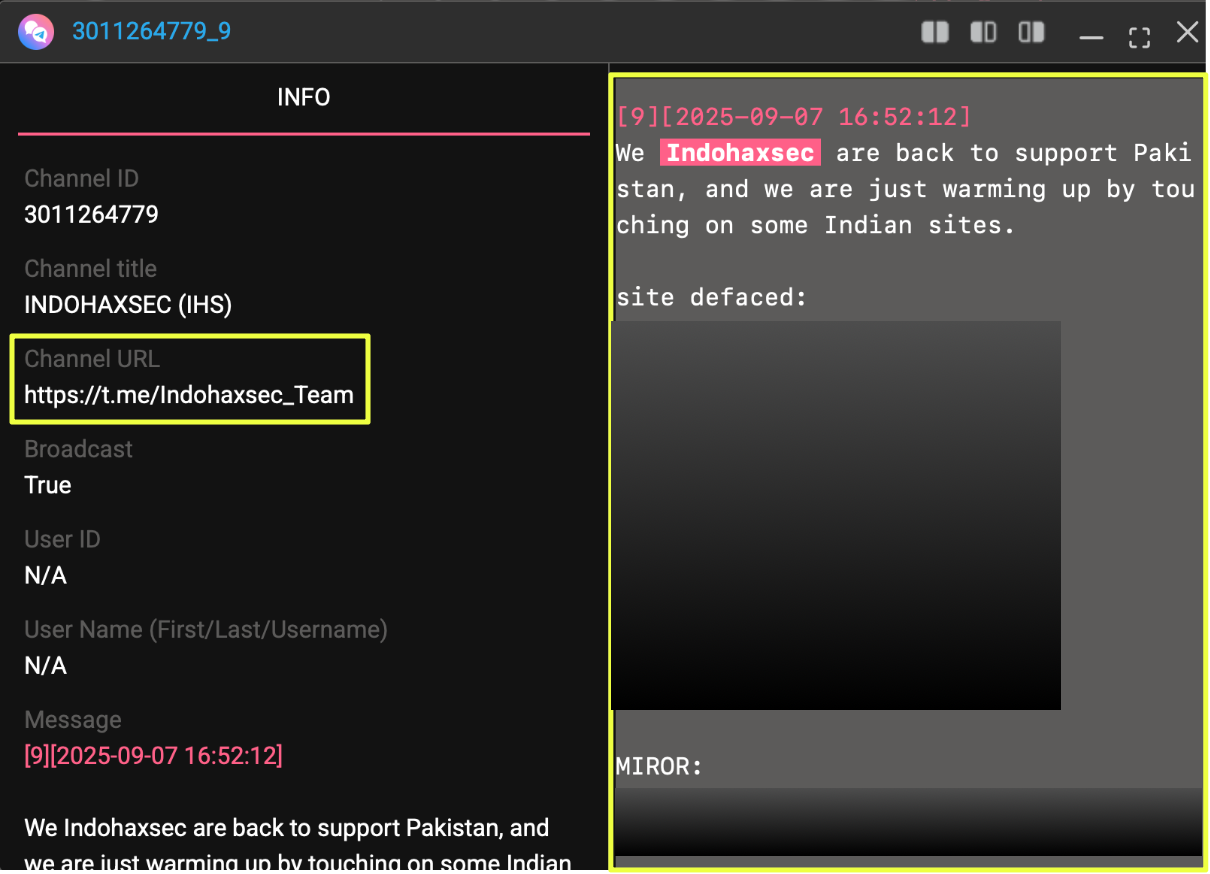
- https://t.me/Indohaxsec_Team
- https://t.me/Indo******
 |
Posts within these channels frequently included attack claims, ideological messages, and links to datasets hosted on underground forums. For example, one post promoted a dataset titled “600,000 Federal Bank of India Database”, accompanied by a link directing users to a thread on DarkForums.
The Telegram channels also served as entry points to other platforms maintained by the group. Several posts encouraged followers to join additional communication channels operated by IndoHaxSec, including:
- X account: https://x.com/INDO******C
- WhatsApp channel: https://whatsapp.com/channel/0029**************0L
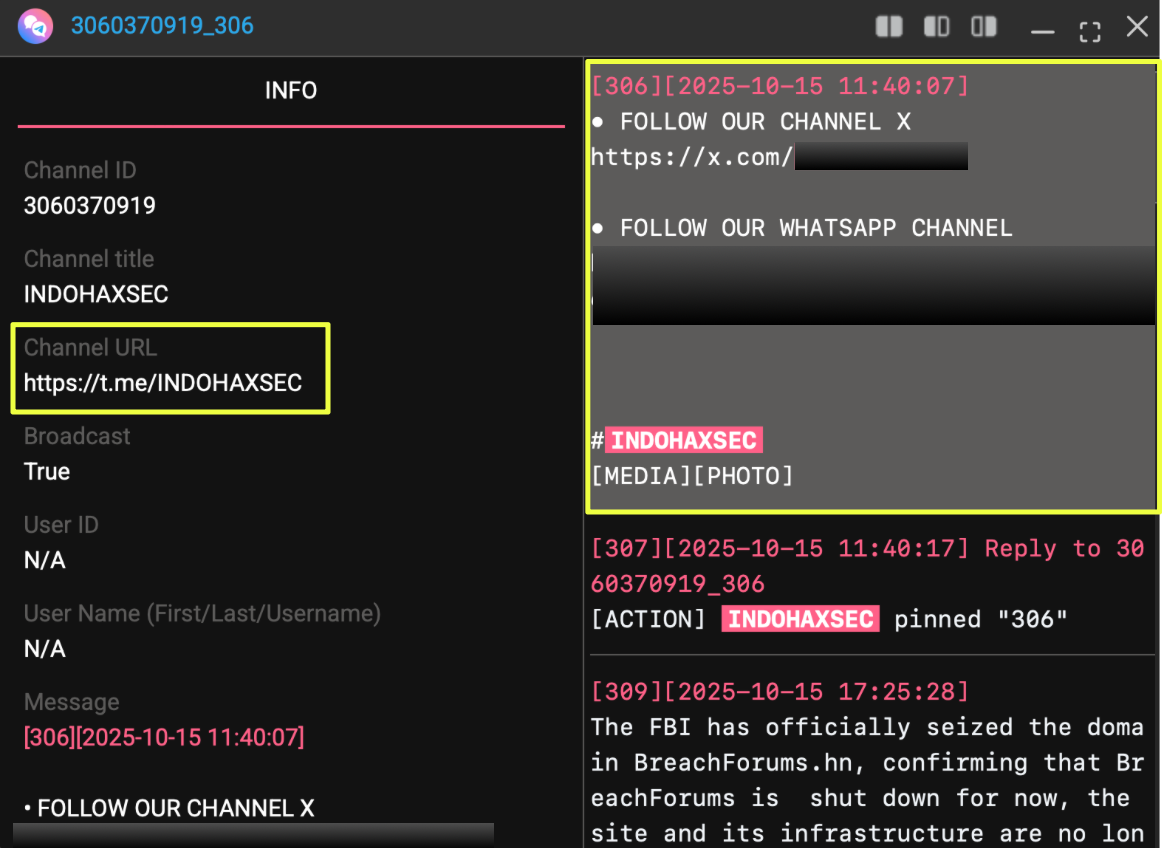 |
The presence of these cross-platform links suggests that IndoHaxSec attempts to maintain a distributed online presence rather than relying on a single communication platform. By directing followers across Telegram, X, and WhatsApp, the group appears to expand the reach of its messaging while ensuring that its announcements and propaganda can continue circulating even if individual channels are disrupted.
 |
Mapping these accounts and channels provides an initial view of the group’s communication infrastructure. These spaces serve not only as places where IndoHaxSec announces operations but also as hubs where alliances, ideological messaging, and leaked data are publicly promoted.
Telegram Messaging, Narratives, and Alliances
With IndoHaxSec’s communication channels identified, the investigation then focused on the content shared within these spaces. Telegram channels associated with the group provide a clearer view of how IndoHaxSec frames its activities, promotes its operations, and interacts with other hacktivist collectives. Many of the posts observed during the investigation combined attack claims with political messaging, suggesting that the group uses Telegram not only to publicize incidents but also to reinforce its ideological positioning.
Several posts within the channel https://t.me/Indo****** referenced attacks and defacement activity. In one instance, the channel announced a defacement targeting the website:
- https://casino4live.com/
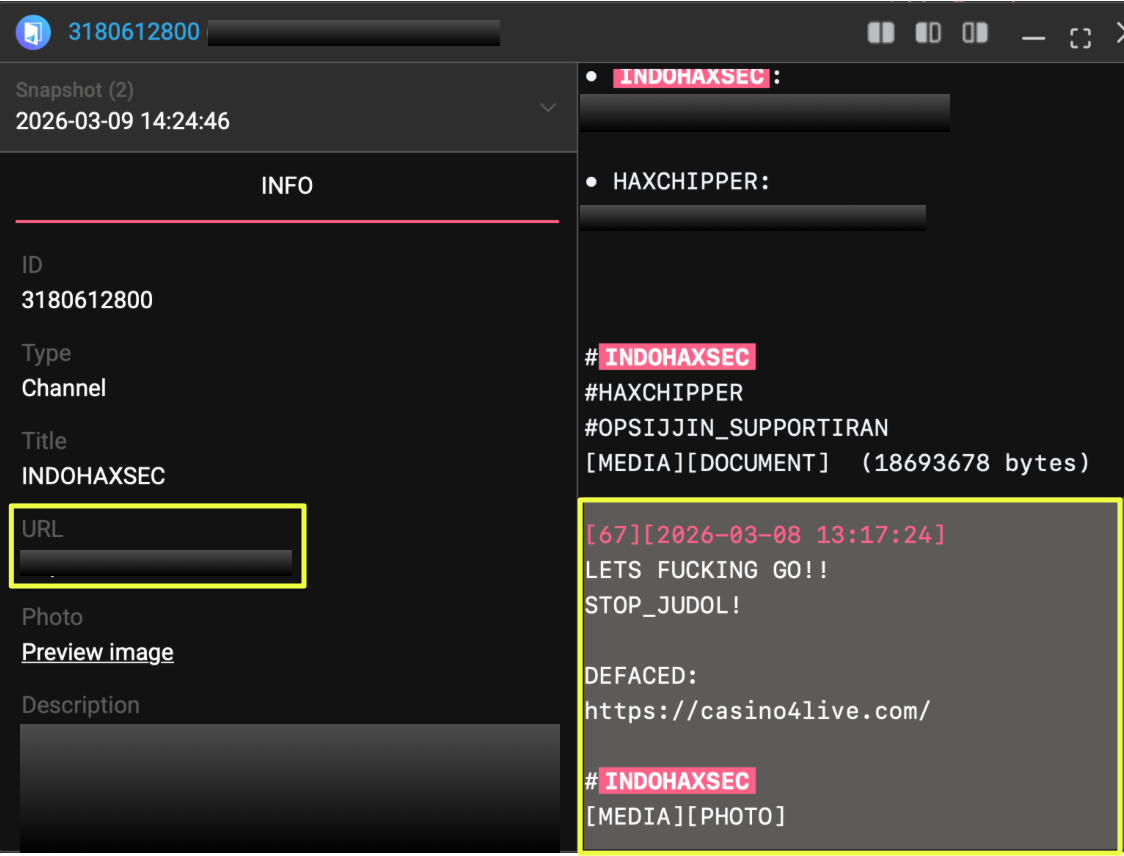 |
The message accompanying the claim included the text “LETS FUCKING GO!! STOP_JUDOL!”, followed by hashtags such as #INDOHAXSEC, #HAXCHIPPER, and #OPSIJJIN_SUPPORTIRAN. These posts illustrate how the group uses Telegram to publicly claim responsibility for website defacements while linking the activity to broader ideological narratives.
The same channel also contained a post referencing the previously identified South Korean dataset leak. The message advertised a dataset titled:
“514.4K THOUSANDS OF SOUTH KOREAN POPULATION AND TRADER DATA.”
Within the message, the group framed the breach as a response to alleged racism from South Koreans and suggested that the incident was intended as an initial warning. The post included the hashtag #Ops_KrRacist, indicating that the attack was presented as part of a broader campaign narrative.
 |
Beyond individual attack claims, Telegram posts also revealed collaborations between IndoHaxSec and other hacktivist groups. On 7 March 2026, the channel https://t.me/Indo****** announced an alliance between IndoHaxSec and another hacktivist collective known as HaxChipper. The message stated that the two groups would work together under an operation referred to as “Operation SijjinCyber,” which was described as supporting Iran and Palestine while targeting Israel, the United States, and their allies.
 |
Another collaboration appeared in the channel https://t.me/Indohaxsec_Team, where a post referenced a joint operation between IndoHaxSec and AZRAEL OF DEATH. The message described the activity as part of a “Pakistan Cyber Support Operation,” suggesting coordination between multiple hacktivist groups aligned around similar geopolitical narratives.
 |
Additional posts referenced collaboration with CLOBELSECTEAM, further indicating that IndoHaxSec operates within a broader network of hacktivist actors rather than functioning in isolation. These alliance announcements demonstrate how Telegram channels are used not only to claim attacks but also to signal partnerships and reinforce a sense of collective action within the hacktivist ecosystem.
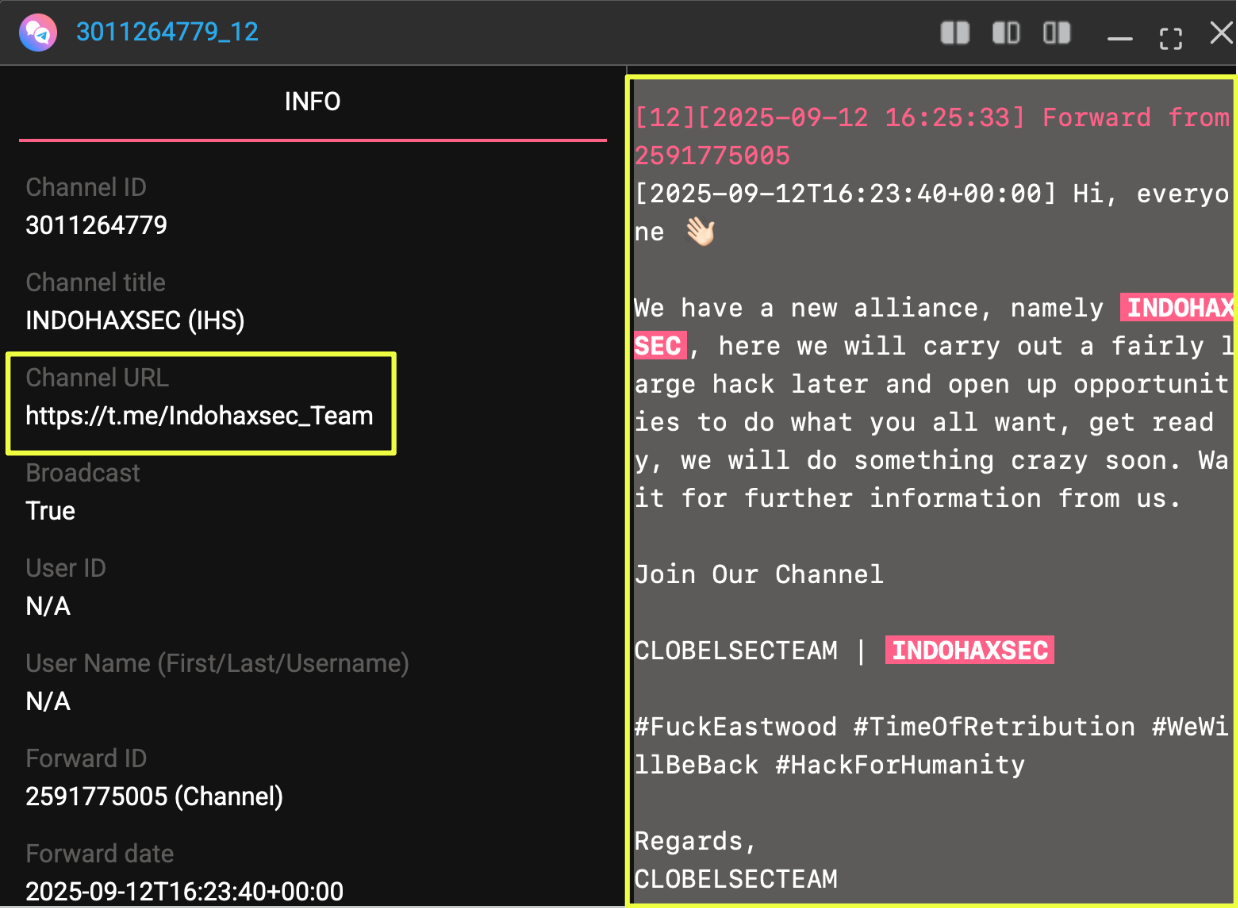 |
In several instances, the messaging also targeted specific countries or political actors. Posts included slogans such as “FUCK ISRAEL” and “FUCK TRUMP,” alongside lists of websites allegedly targeted during the same operation. In another message shared in the channel https://t.me/INDOHAXSEC, the group issued threats directed toward India, claiming that future attacks would target a wide range of sectors including government institutions, companies, and educational organizations.
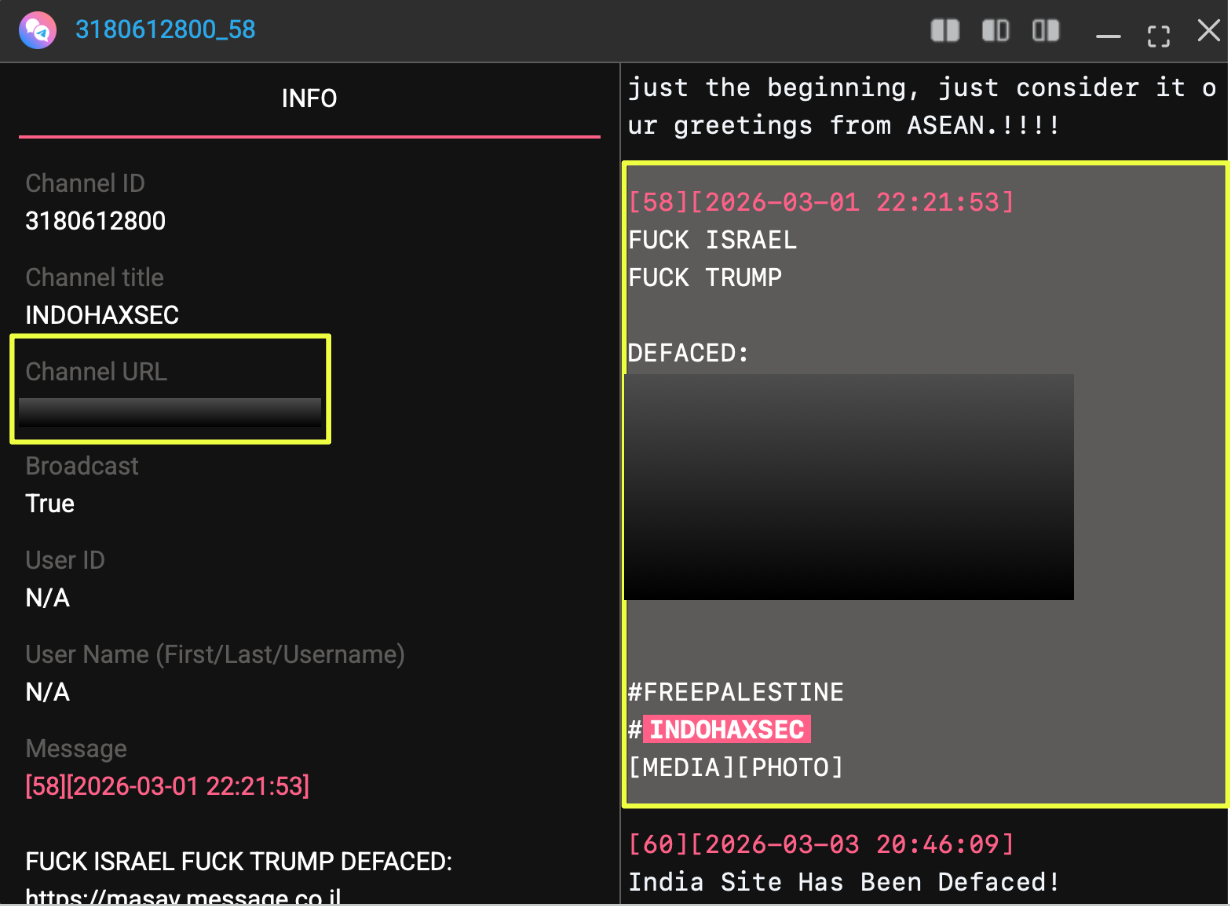 |
Overall, these posts provide insight into how IndoHaxSec uses Telegram to frame its operations within a broader narrative of political or ideological conflict. The platform appears to function as the group’s primary space for announcing attacks, promoting alliances, and amplifying the narratives that accompany its activities.
Underground Forum Activity and Data Leak Distribution
In addition to its messaging presence on Telegram, IndoHaxSec also appears to use underground forums to distribute and promote leaked datasets. These forums often serve as marketplaces or public repositories where threat actors advertise stolen databases, share proof samples, or direct users to download links. Investigating these spaces provided further insight into how the group publicizes its alleged breaches and interacts with the broader cybercrime ecosystem.
One such example was identified on the forum DarkForums, where a thread titled “DATABASE 3.2K THOUSAND ISRAEL TIP INFORMATION DATABASE” was posted. The thread was attributed to a user operating under the name INDOHAXSEC, suggesting that the group itself was responsible for publishing or promoting the dataset.
The thread can be accessed through the following link:
- https://darkforums.***/Thread*********************DATABASE
From this post, the corresponding user profile associated with the thread was identified:
- https://darkforums.me/User-I**********C
The investigation also revealed a session identifier associated with the activity:
- 053d1*****************************************93047
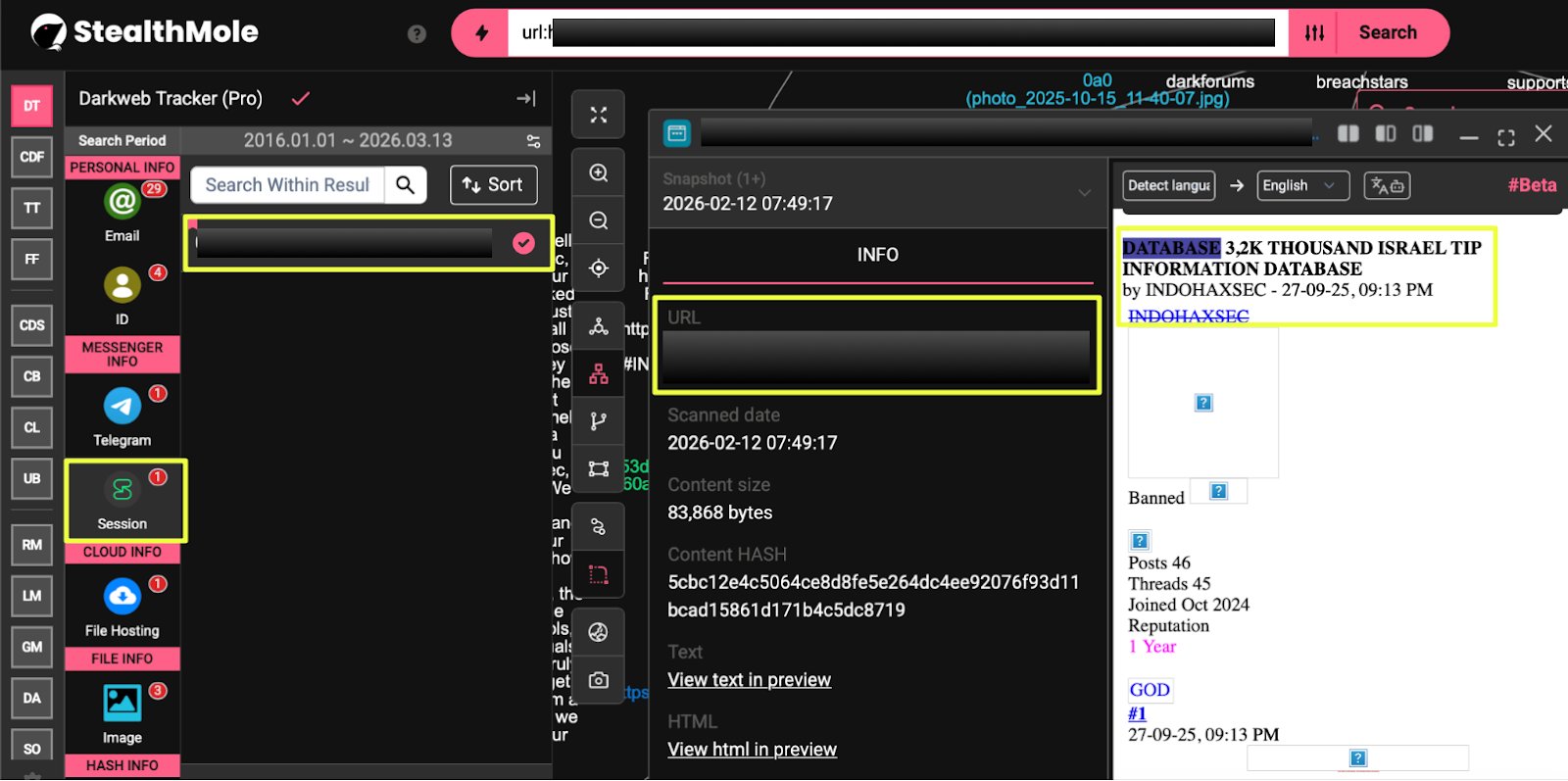 |
The presence of this thread suggests that IndoHaxSec uses underground forums as a distribution channel for datasets it claims to have obtained. Such forums provide visibility among cybercrime communities while also allowing actors to promote their operations to a wider audience.
Another dataset advertisement linked to the group was discovered on the forum BreachStars. In this case, the post referenced a database described as “169,045 Database of the Israeli Traffic Department.” The post was attributed to a user named INDOHAXSECTEAM, which appears to be another variation of the group’s name used across platforms.
The associated user profile was identified at:
- https://breachstars.***/profile/INDOHAXSECTEAM
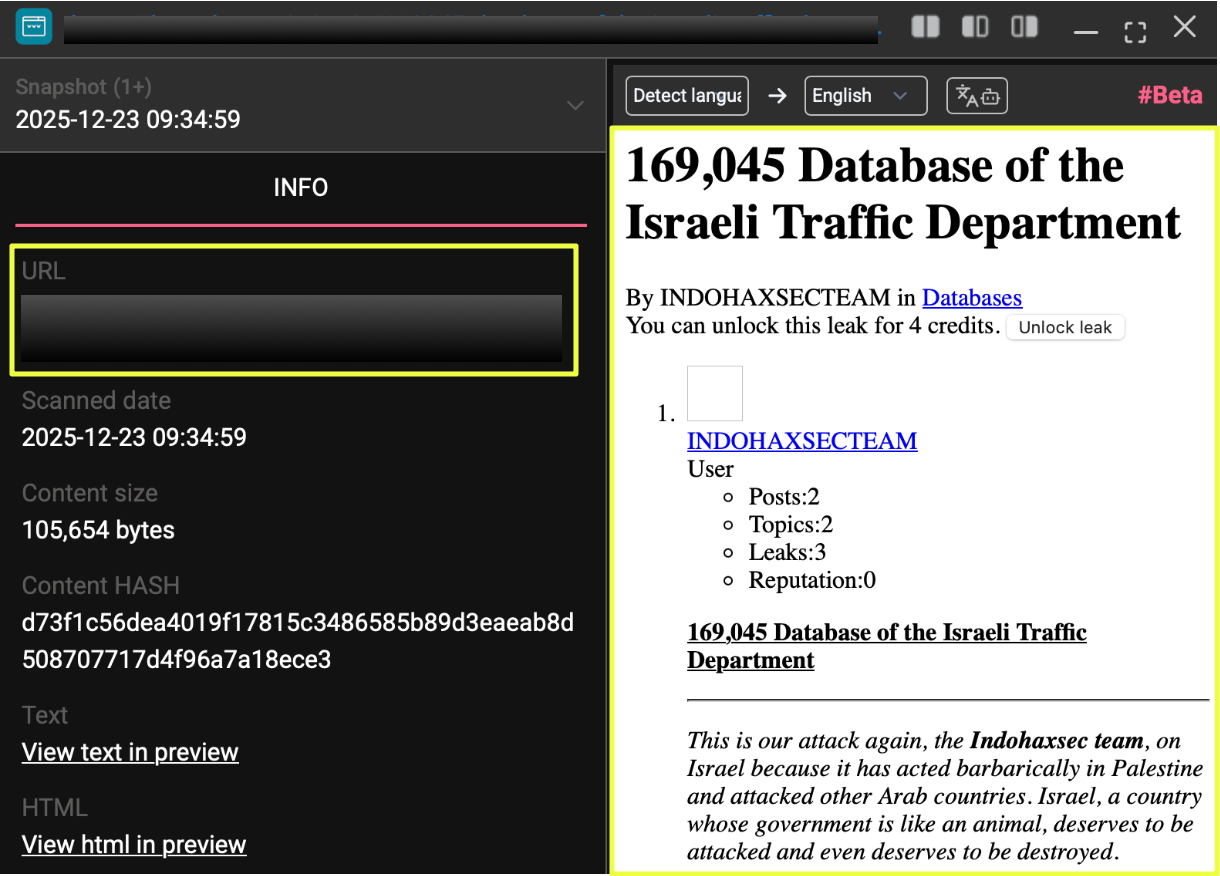 |
While the usernames differ slightly across platforms, the naming convention strongly reflects the IndoHaxSec branding observed throughout Telegram channels and other artifacts identified during the investigation.
 |
Together, these forum posts illustrate how IndoHaxSec extends its activity beyond social messaging platforms. Telegram channels appear to be used to promote attacks and share announcements, while underground forums provide a space where datasets can be distributed or advertised to audiences already engaged in cybercrime communities. This combination of messaging platforms and forum activity reflects a common pattern among hacktivist groups seeking both publicity and recognition for their operations.
Conclusion
This investigation set out to better understand the online footprint of IndoHaxSec by tracing the group’s presence across multiple digital platforms. Through analysis of artifacts collected from StealthMole monitoring tools, Telegram channels, underground forums, and related communication platforms, the investigation reveals a hacktivist collective that maintains a distributed but visible online ecosystem.
IndoHaxSec’s activity appears to revolve around a combination of messaging, attack claims, and data leak promotion. Telegram channels serve as the central point where the group announces operations, shares ideological narratives, and promotes links to external platforms hosting datasets or forum threads. Underground forums such as DarkForums and BreachStars provide an additional layer where data attributed to the group is advertised and distributed.
The group’s messaging frequently references geopolitical issues, particularly those connected to the Israel–Palestine conflict, while also directing rhetoric toward other countries and political actors. Alliance announcements involving groups such as HaxChipper, AZRAEL OF DEATH, and CLOBELSECTEAM further suggest that IndoHaxSec operates within a broader ecosystem of loosely connected hacktivist collectives.
While the investigation uncovered a wide range of artifacts associated with the group, the nature of hacktivist activity makes it difficult to determine the precise scale or authenticity of every claim. Some attacks may be genuine compromises, while others may represent exaggeration, reposted leaks, or activity carried out by affiliated actors rather than a single coordinated organization.
Nevertheless, the collection of digital traces identified during this investigation provides a clearer picture of how IndoHaxSec maintains its online presence, promotes its operations, and positions itself within the evolving landscape of hacktivism.
Editorial Note
Investigations into hacktivist groups rarely produce a complete or definitive picture of the actors involved. Online identities shift, channels disappear or reappear under new names, and claims of responsibility may be exaggerated or shared between loosely connected participants. As a result, attribution in these environments often remains fluid.
The IndoHaxSec case illustrates how piecing together fragments from multiple sources, monitoring tools, messaging platforms, and underground forums, can help reveal patterns that might otherwise remain hidden. By navigating these fragmented digital spaces, platforms like StealthMole enable investigators to connect disparate signals and better understand how emerging hacktivist groups operate within the broader cyber threat landscape.
To access the unmasked report or full details, please reach out to us separately.
Contact us: support@stealthmole.com
Labels: Featured, Hacktivist Group
.svg)
.svg)
.svg)