P4R4ZYT3 and DEFCOMX64 Escalation: From Government Data Breach to Public Campaign
 |
Brazil’s cyber threat landscape has evolved rapidly over the past few years. What was once dominated by financially motivated fraud schemes and banking malware has expanded into a more complex ecosystem: blending hacktivism, data leaks, politically motivated disruption, and reputational campaigns conducted through Telegram and underground forums.
State-level institutions, regional government departments, and public service agencies have increasingly appeared in defacement claims, breach announcements, and coordinated messaging campaigns. In many cases, the operational impact is difficult to measure immediately. What is easier to observe, however, is the shift in posture.
Actors are no longer operating solely for quiet monetization. They are signaling.
Telegram, in particular, has become the staging ground for these narratives. Channels emerge, disappear, rebrand, and resurface. Profile identities change. Symbols rotate. Messages escalate from cryptic commentary to declarative threats. In this environment, disruption does not always mean disappearance, it often signals reorganization.
It was within this broader context that a cluster of activity began to stand out.
What initially appeared to be routine underground interaction gradually aligned with more assertive messaging tied to government-linked targets. The trajectory did not unfold overnight. It evolved in fragments.
This report examines that evolution.
By tracing identity shifts, channel migrations, rhetorical changes, and platform behavior, we move from environmental context to actor-specific escalation. The objective is not only to document what has occurred but to understand how public signaling, post-disruption regrouping, and narrative framing intersect within Brazil’s current cyber threat environment.
Incident Trigger and Initial Investigation
The investigation began with a keyword search for “Brazil” within StealthMole’s Government Monitoring tool. The query returned 152 results, all linked to Brazilian government-related data breach references. Rather than reviewing each entry individually, the focus shifted toward identifying actors showing repeated activity against Brazilian public-sector entities.
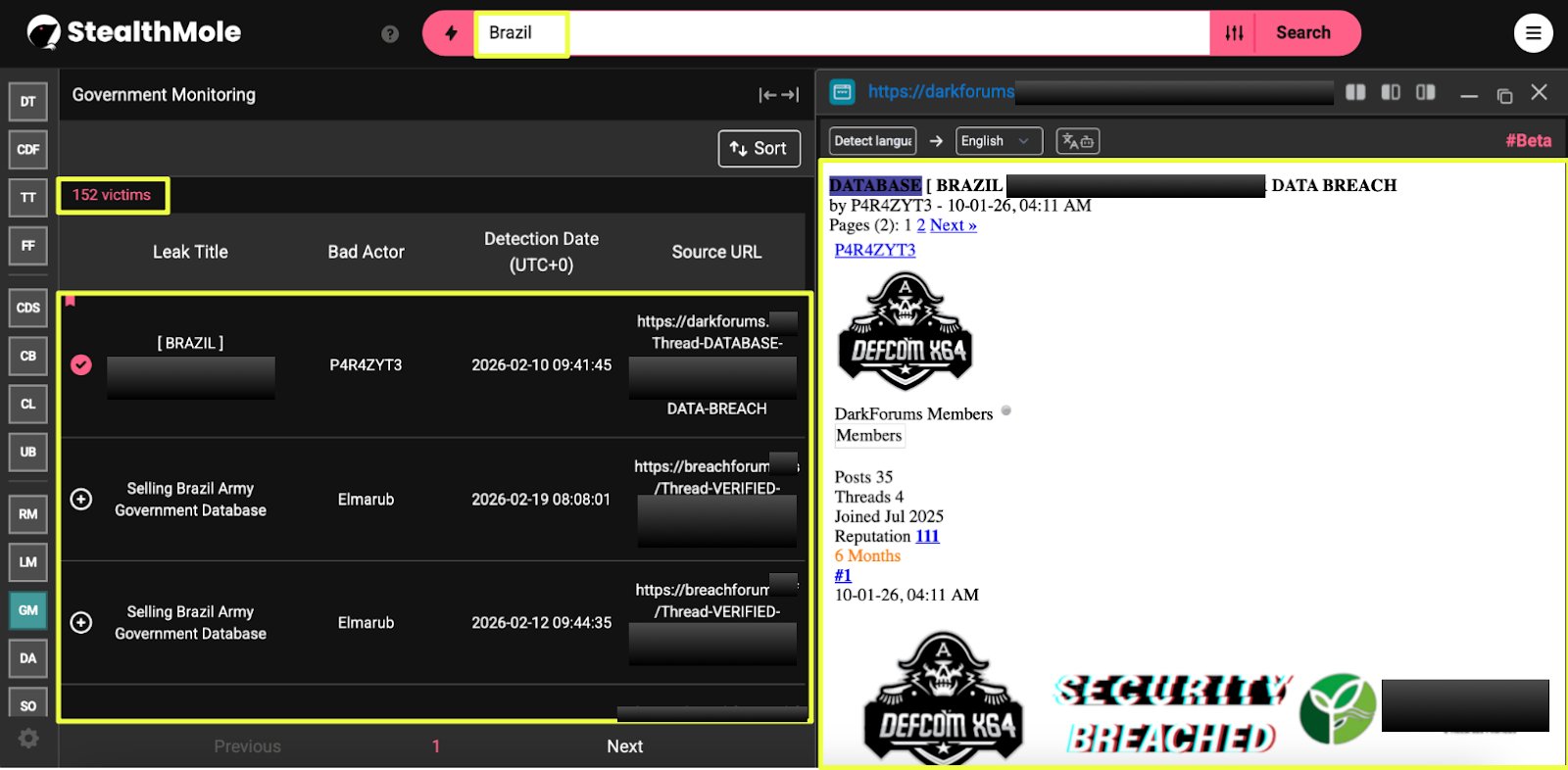 |
One name surfaced prominently: P4R4ZYT3.
To understand the scope of this actor’s involvement, the next step was to examine their most recent indexed activity. The latest breach attributed to this alias was recorded on 10 February 2026, referencing an attack against F********H. However, further investigation revealed that this breach actually happened on 09 January 2026.
The breach was originally announced on DarkForums at:
- https://darkforums.**/Thread-DATABASE-BRAZIL-HTTPS****DATA-BREACH
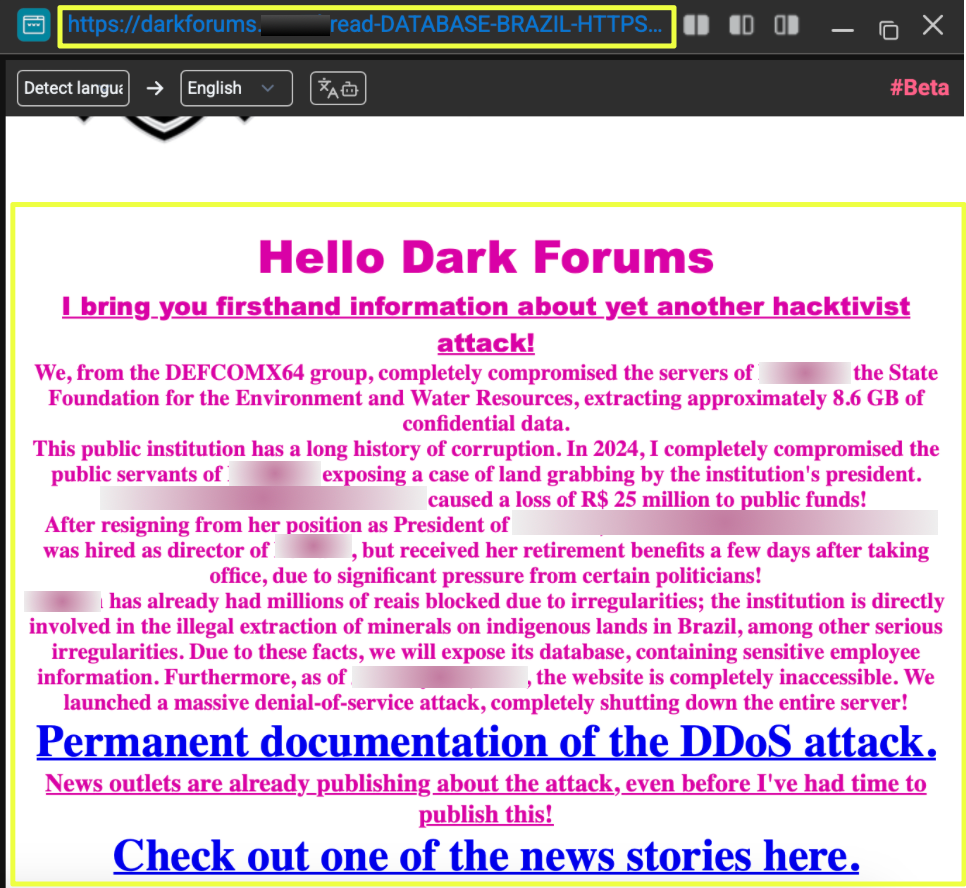 |
Visiting the thread revealed that the post was made under the username P4R4ZYT3, accompanied by the DEFCOMX64 logo as the profile image. The message was written in a declarative tone and framed as a collective action, stating that the operation was conducted by the DEFCOMX64 group.
The thread included:
- Claims of full database compromise
- Stated extraction size of approximately 8.6 GB
- Politically framed commentary directed at state governance
- A recruitment-style “join us” message
- Embedded links referencing DEFCOMX64 Telegram infrastructure
- Sample datasets allegedly belonging to F*****H personnel
Two bio-style datasets were visible within the thread, containing structured personal information such as names, CPF numbers, contact details, and associated identifiers. These were presented as evidence of database access.
 |
The consistent presence of DEFCOMX64 branding, recruitment language, and cross-platform references suggested that this was not an isolated leak post but part of a broader identity ecosystem.
At this point, the investigation shifted from a single breach thread to the actor’s broader footprint.
Using StealthMole’s Defacement Alert tool, the username P4R4ZYT3 was queried to determine whether the actor had conducted website defacements in addition to database breaches. The search returned 12 defacement records, with victims primarily located in Brazil and Germany.
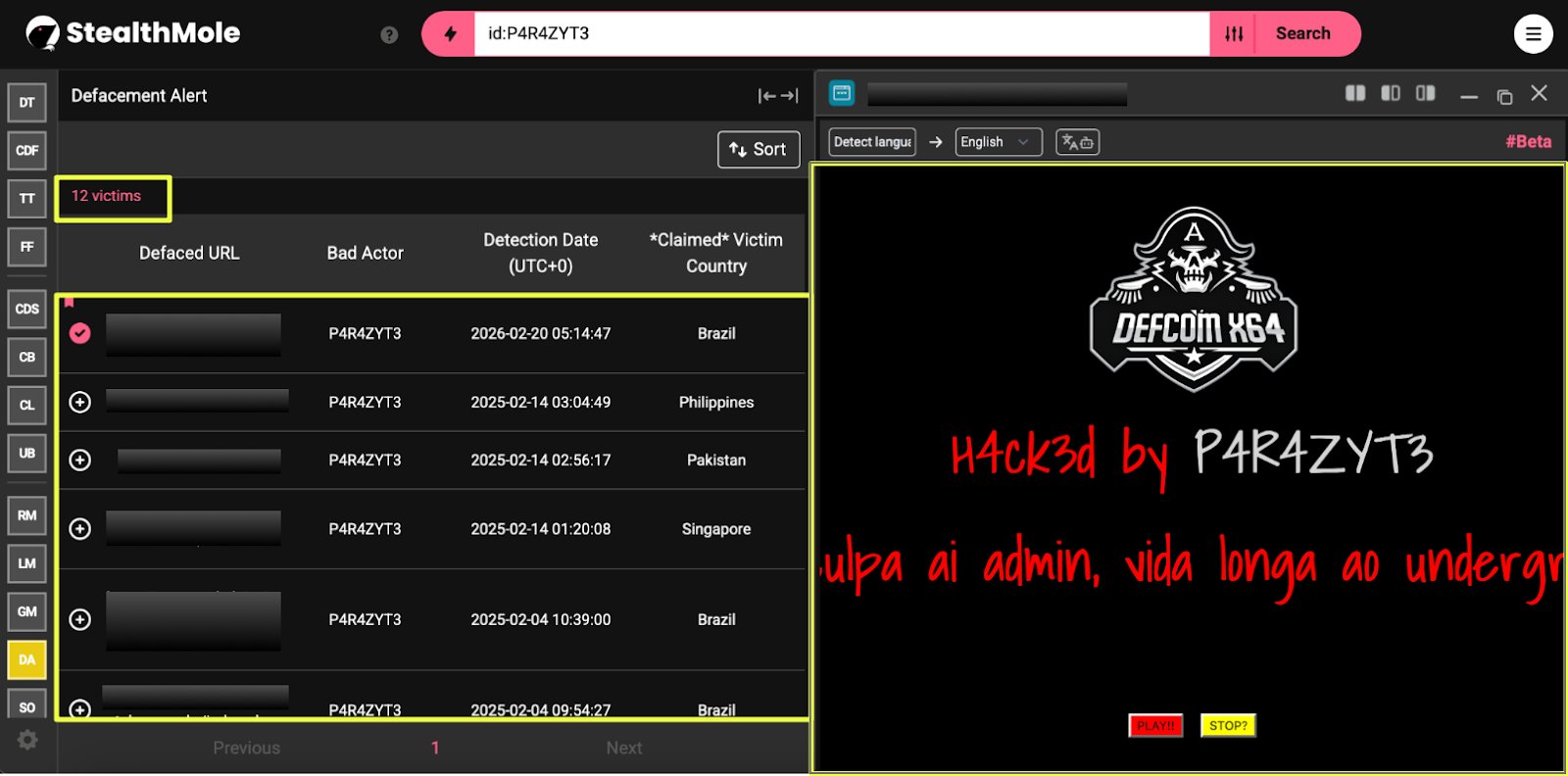 |
The visual consistency between the DarkForums thread and the defaced website, particularly the repeated DEFCOMX64 insignia, indicated coordinated branding across breach announcements and defacement operations.
Actor Attribution and Cross-Platform Identity Mapping
With the F*******H breach and associated defacement activity linked to the alias P4R4ZYT3, the next step was to determine whether this identity existed beyond a single forum post.
Using StealthMole’s Dark Web Tracker, the username P4R4ZYT3 was queried across indexed underground platforms. The search revealed multiple profiles associated with the same alias across mirrored and related domains:
- https://umbra.**/P******3
- https://darkforums.**/U******3
- https://darkforums.**/U*****3
- https://darkforums.**/U******3
- https://hellofhackers.com/members/p*******7/
The DarkForums mirrors reflected consistent account metadata, including identical join dates and user ID references. The profile image matched the DEFCOMX64 logo observed in the F******H breach thread. This consistency suggested that the activity was not an impersonation across unrelated forums, but a unified identity replicated across mirrored infrastructure.
The Umbra profile added a critical layer of linkage. It referenced:
- Telegram channel: https://t.me/d*******
- Telegram username: P*******c
- Signature reference: DEFCOMX64
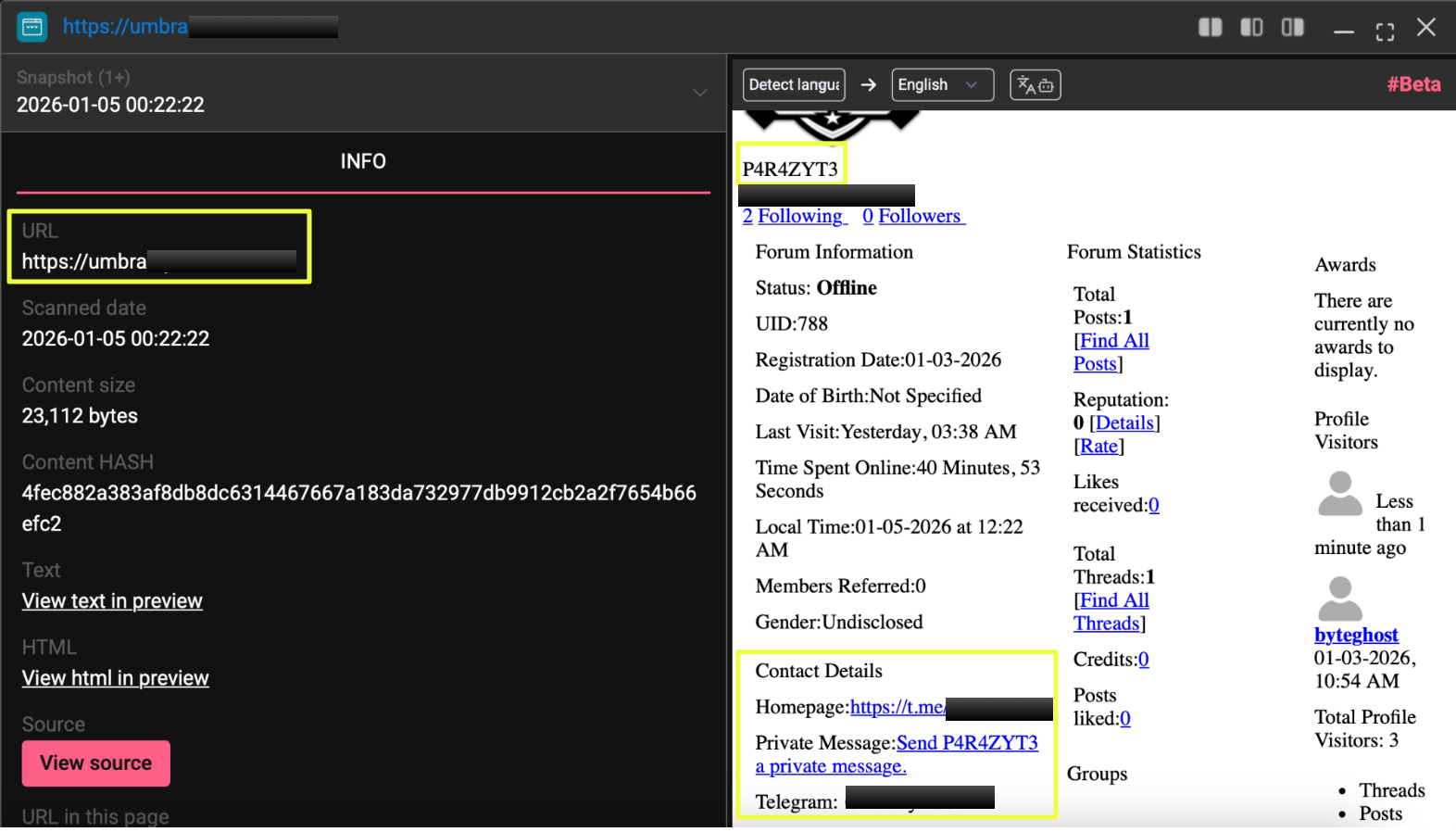 |
This connection bridged the forum identity to Telegram infrastructure.
Further review of the Hell of Hackers platform revealed an earlier thread titled “DATABASE DUMPED IN BRAZIL.” In that post, P4R4ZYT3 claimed responsibility for compromising a Brazilian company via SQL injection and releasing customer and employee data. The message explicitly stated that the actor’s language was Portuguese and referenced Brazilian-specific identifiers such as CPF numbers. This activity predates the February 2026 F*****H breach, indicating that Brazil-focused data exposure was not a one-time occurrence.
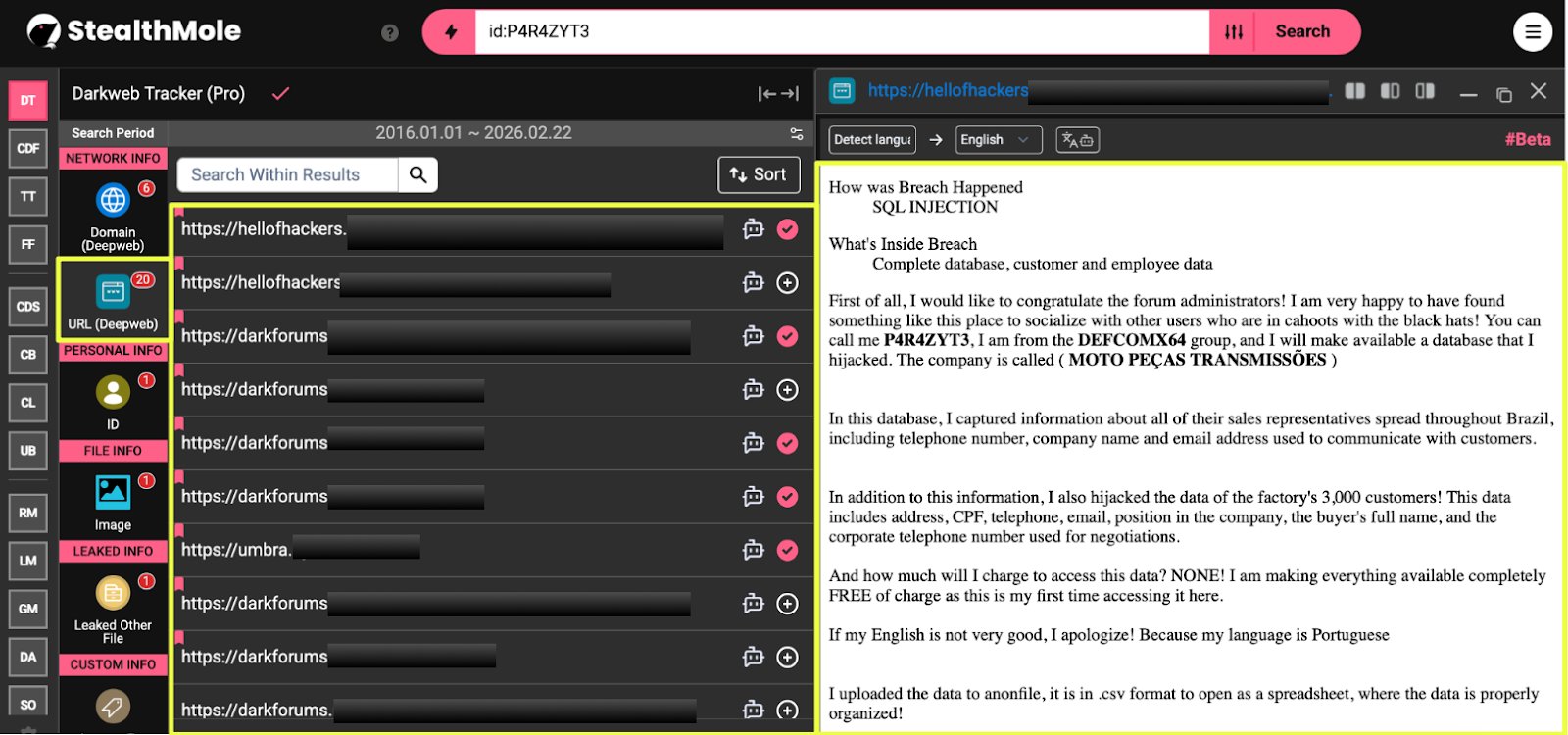 |
At this stage, three consistent elements emerged:
- The alias P4R4ZYT3
- The DEFCOMX64 branding
- The Telegram handle P*******c
Telegram Infrastructure and Identity Consolidation
With the forum footprint established, attention shifted to Telegram, where several references linked directly to the alias.
Using StealthMole’s Telegram Tracker, the username was examined. The account displayed clear alignment with the previously identified alias P4R4ZYT3. The bio referenced DEFCOMX64, and the profile imagery evolved over time before stabilizing around the group’s branding.
- https://t.me/P**********c
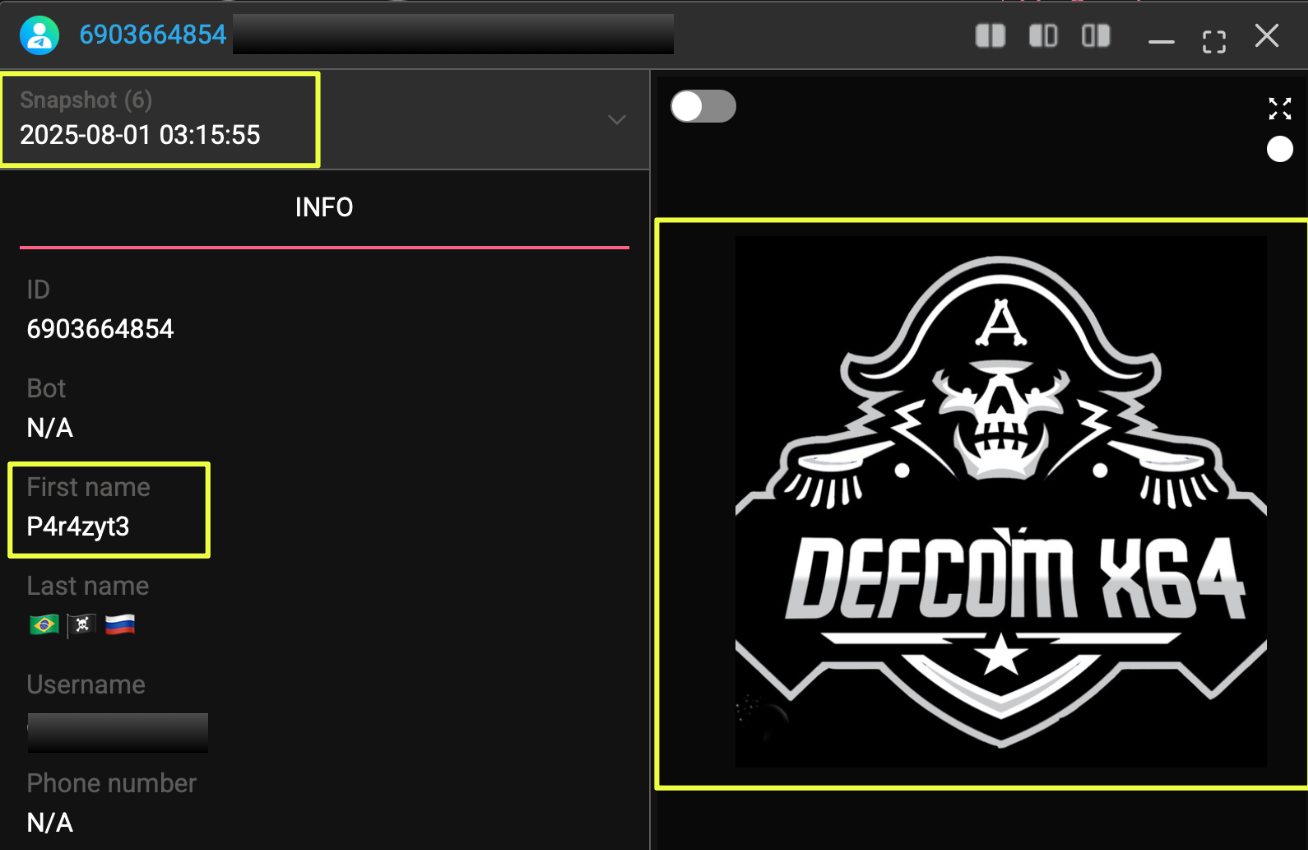 |
StealthMole’s historical indexing revealed five distinct profile changes during 2024. In June 2024, the profile used an anonymous-style mask. By August, the image shifted to a “Wizard Society” graphic. In December 2024, the bio incorporated different flag markers and new visual messaging. Over time, the profile transitioned toward consolidated DEFCOMX64 branding, accompanied by the Brazilian, pirate, and Russian flag emojis.
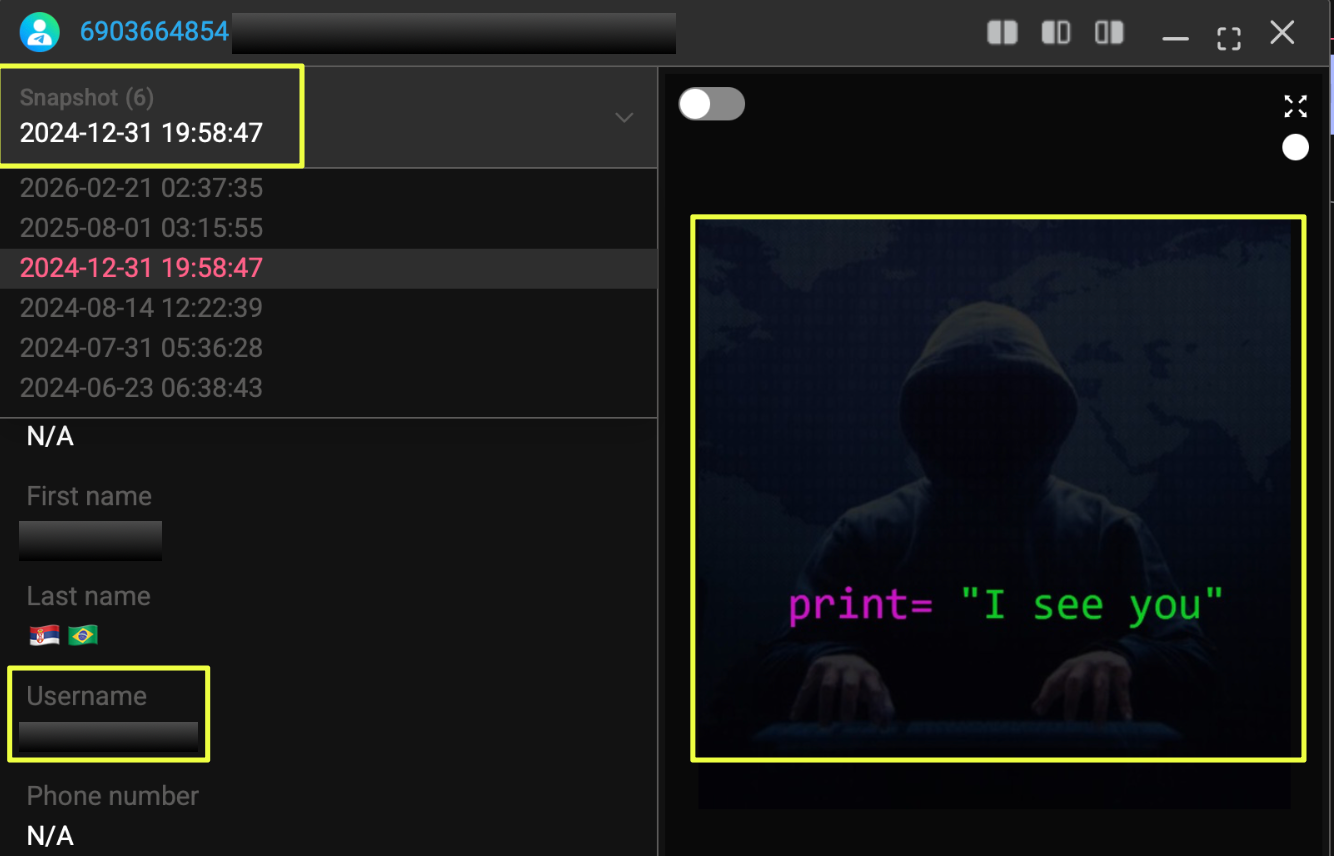 |
 |
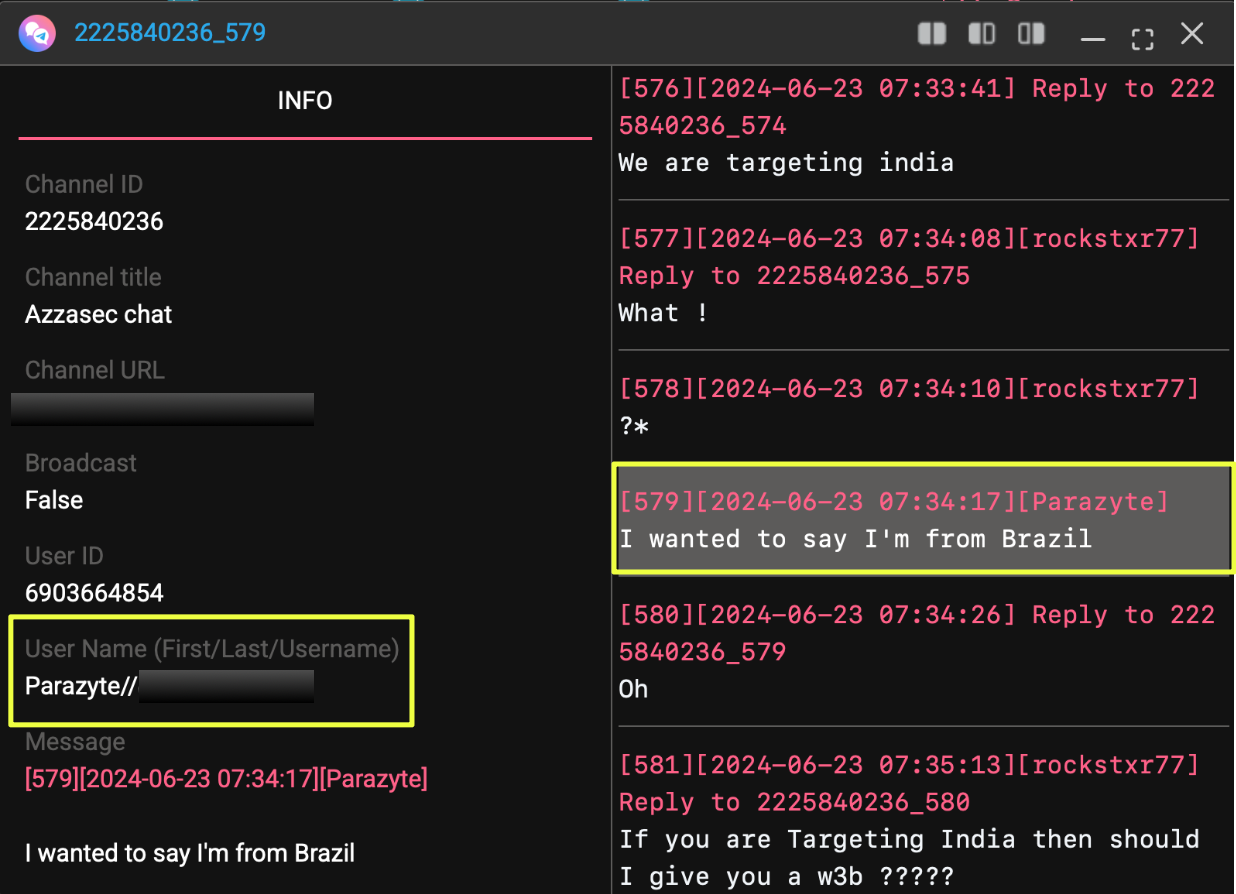
Archived Telegram group activity further strengthened attribution.
In a June 2024 discussion within the “Azzasec Chat,” the user explicitly stated that they were from Brazil. In separate conversations within the “Jacuzzi” channel, the alias referenced having made a Brazilian database publicly available on a forum and directed users to search for the name P4R4ZYT3.
 |
The account was also observed requesting access to XWorm, a commercially distributed remote access tool frequently discussed in underground channels. While this does not confirm operational deployment, it demonstrates awareness of and interest in offensive tooling.
Beyond the personal account, Telegram infrastructure extended to a channel:
- https://t.me/de********s
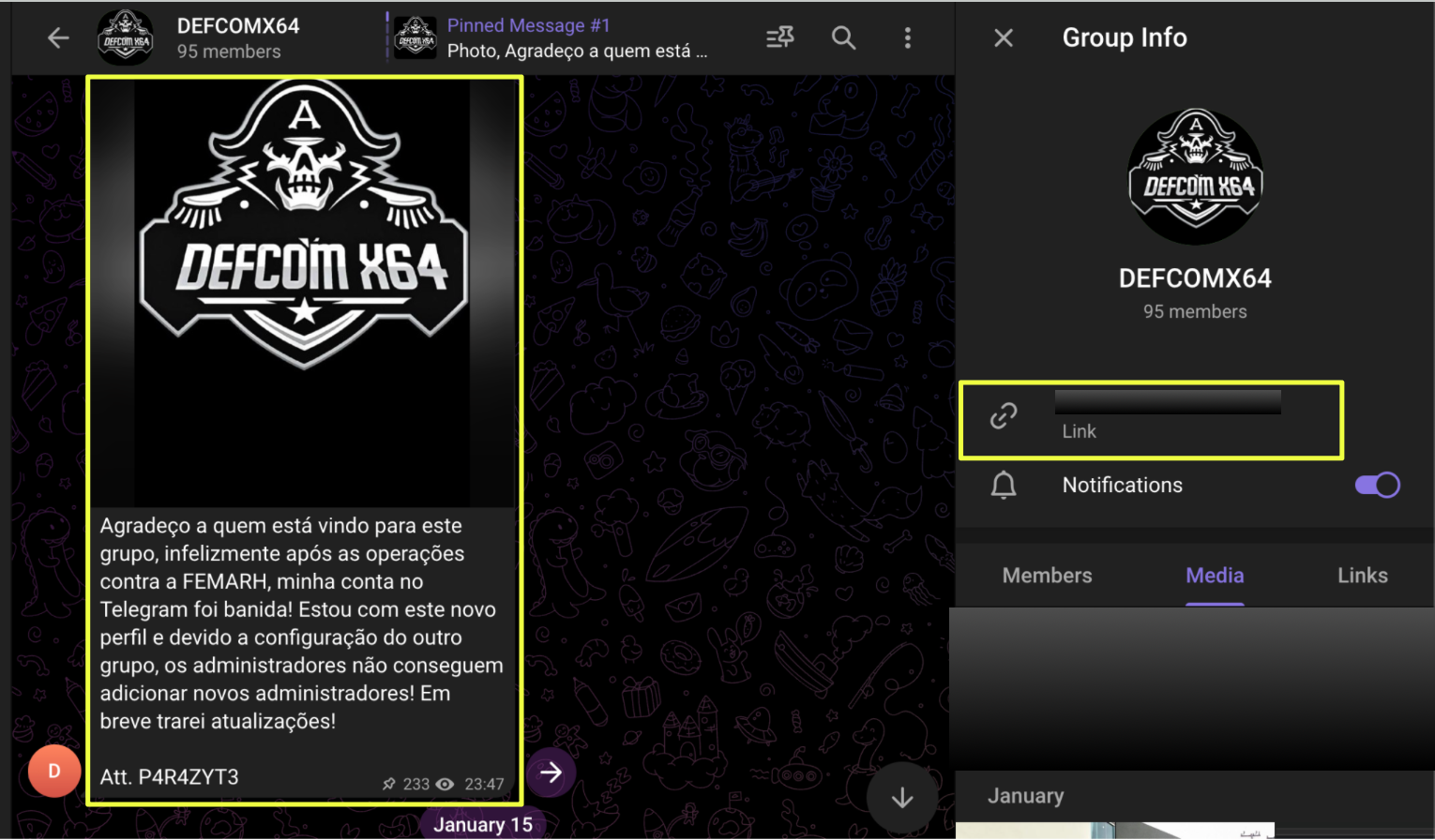 |
This channel was created on 14 January 2026, shortly after the F*******H breach announcement. Its first message stated that the group’s primary Telegram account had been taken down following the breach activity and that this new channel would serve as its continuation. The message was signed “Att. P4R4ZYT3.”
At the time of review, the channel contained eight messages and 95 members. The branding, tone, and signature matched the forum identity.
Unlike the earlier Telegram interactions, the channel messaging shifted from conversational to declarative. Statements referenced intensifying actions against the state government and announced a specific timeline for renewed activity.
At this point, Telegram was no longer a peripheral communication platform. It had become the central hub for identity consolidation, escalation messaging, and public signaling.
Escalation Messaging and Campaign Signaling
The creation of the de********s Telegram channel marked a visible transition in tone.
Earlier activity linked to P4R4ZYT3 largely centered on breach announcements, forum promotions, and participation in underground discussions. The messaging was reactive, reporting past actions or directing attention to previously released datasets.
That posture shifted in February 2026.
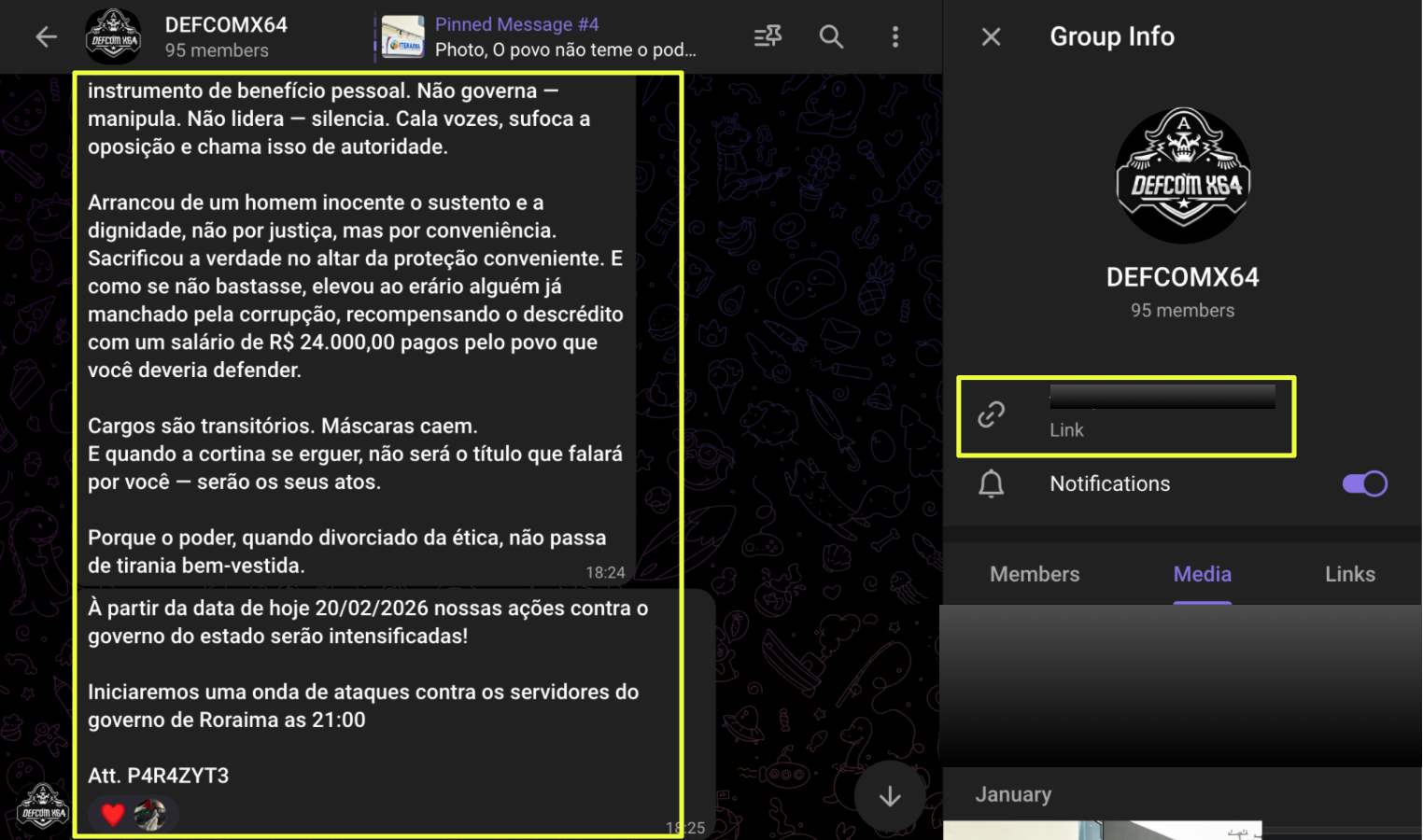 |
On 20 February 2026, the DEFCOMX64 Telegram channel published a message declaring that actions against the state government would be intensified. The statement referenced a “wave of attacks” targeting government employees in Roraima and specified a time for the start of renewed activity. The message was signed “Att. P4R4ZYT3.”
This marked a change in operational posture.
Rather than announcing completed breaches, the messaging projected forward intent. The tone moved from disclosure to declaration. The language adopted ideological framing, referencing governance and positioning actions as retaliatory or corrective.
It is important to distinguish between declared intent and confirmed impact. The Telegram statements represent public signaling, not independently verified technical outcomes. However, in underground ecosystems, such declarations serve a strategic purpose. They build reputation, attract attention, and frame subsequent activity within a narrative of escalation.
The timing is also notable. The channel itself was created on 14 January 2026, shortly after the F*******H breach announcement and the reported takedown of a previous Telegram presence. Within days of re-establishing communication infrastructure, escalation rhetoric appeared.
This sequence suggests three observable behaviors:
- Rapid reconstitution after platform disruption
- Consolidation of identity under DEFCOMX64 branding
- Transition from breach reporting to campaign-oriented messaging
When combined with earlier defacement activity and prior Brazil-focused database releases, the February declaration does not appear isolated. Instead, it aligns with a trajectory moving from opportunistic breach exposure toward publicly framed, state-directed confrontation.
Whether such messaging translates into sustained operational capability remains subject to continued monitoring. What is clear, however, is that the actor has adopted a posture of escalation and is communicating that posture openly.
Conclusion
What began as a routine keyword search within StealthMole’s Government Monitoring tool ultimately revealed a structured pattern of activity centered around the alias P4R4ZYT3 and the DEFCOMX64 identity.
The progression was not abrupt. It unfolded across platforms, from forum-based database disclosures to visually branded defacements, from informal Telegram participation to consolidated channel creation, and finally to public declarations of intensified action against state-linked targets. The consistency of branding, repeated self-attribution, and cross-platform alignment demonstrate persistence rather than coincidence.
The February 2026 transition marks a notable inflection point. The creation of a new Telegram channel following reported account disruption, combined with forward-looking escalation messaging, indicates an attempt to shift from retrospective breach announcements to campaign-oriented signaling. Whether this shift translates into sustained operational capability remains subject to continued monitoring. However, the trajectory reflects deliberate identity consolidation and increasingly public positioning.
At present, observable behavior aligns with a visibility-driven, hacktivist-style posture focused on Brazilian government-linked entities. The actor openly claims affiliation, publishes branding consistently, and frames activity within ideological language. The absence of ransom demands or structured monetization channels suggests reputation and narrative influence may be primary motivators.
Continued monitoring of defacement indexing, Telegram messaging, and new breach disclosures will be essential to determine whether this escalation rhetoric evolves into sustained, coordinated activity or remains primarily declarative.
Editorial Note
Attribution and capability assessment in cyber investigations are rarely absolute. Online identities can be replicated, exaggerated, or strategically framed for visibility. This case demonstrates how fragmented signals can be methodically assembled to identify patterns without overextending conclusions using StealthMole.
To access the unmasked report or full details, please reach out to us separately.
Contact us: support@stealthmole.com
Labels: Breach, Threat Actor
.svg)
.svg)
.svg)