HellCat Ransomware Group: Infrastructure, Affiliations, and Activity on the Dark Web
 |
In early 2024, a series of data leak posts began appearing across underground forums, gradually drawing attention to an actor operating under the name HellCat. What initially seemed like isolated disclosures soon revealed a more consistent pattern: one that pointed toward an emerging presence within the ransomware and data extortion ecosystem.
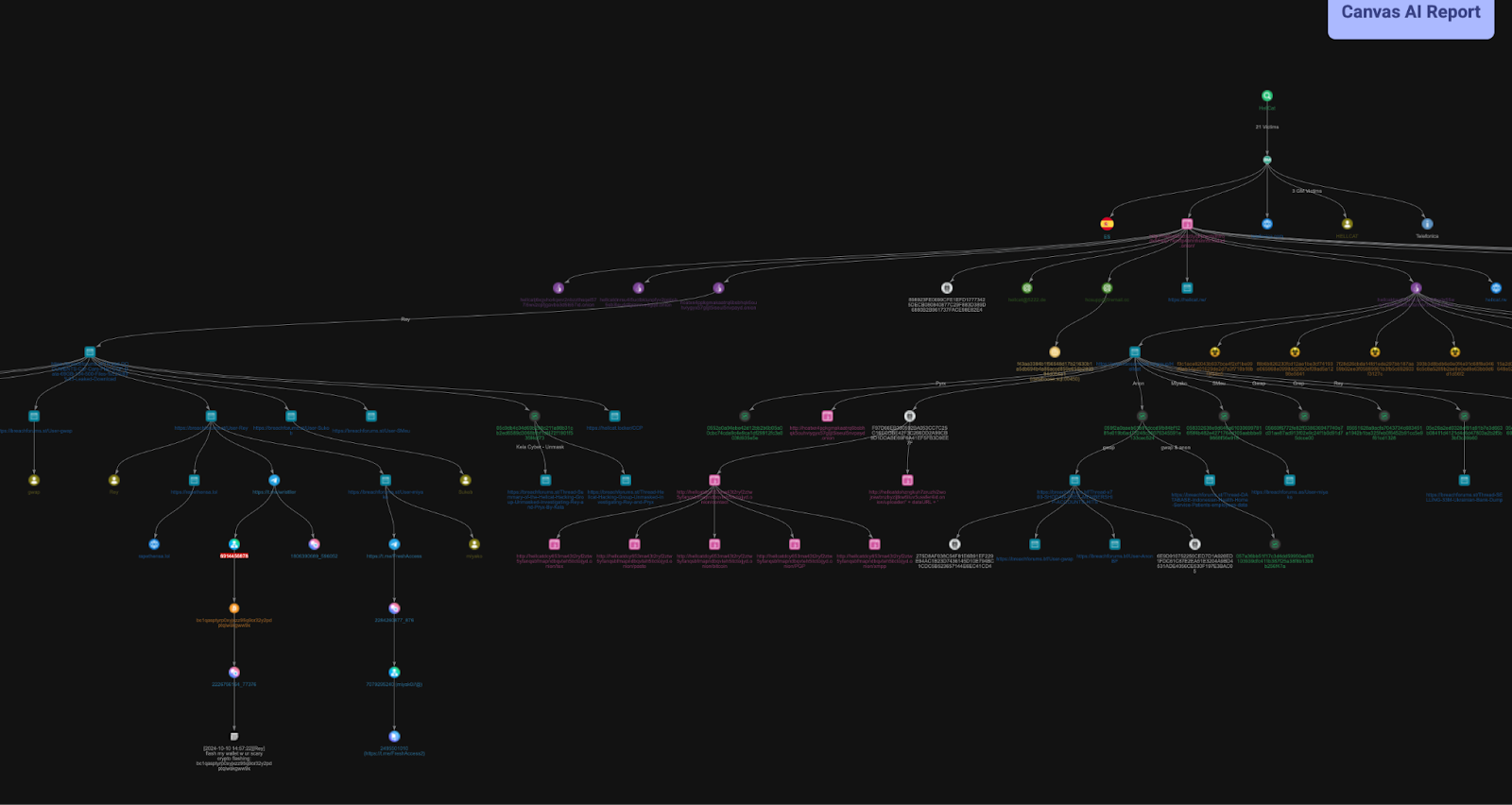
Unlike well-established ransomware groups that rely on polished branding and structured operations, HellCat’s activity appears more fluid, with traces scattered across multiple platforms including breach forums, Telegram channels, and publicly accessible paste services. These fragments, when viewed in isolation, offer limited insight. However, when correlated through StealthMole’s monitoring capabilities, a clearer picture begins to take shape.
This report examines HellCat not as a single isolated entity, but as part of a broader underground environment: one where aliases, shared resources, and overlapping communities often blur the lines between individual actors and collective operations. By following these traces across platforms, the investigation uncovers patterns of activity, communication, and potential affiliations that suggest a more interconnected presence than initially apparent.
Incident Trigger and Initial Investigation
To move from scattered observations to something more concrete, the next step was to test how consistently the HellCat name appeared across monitored data sources.
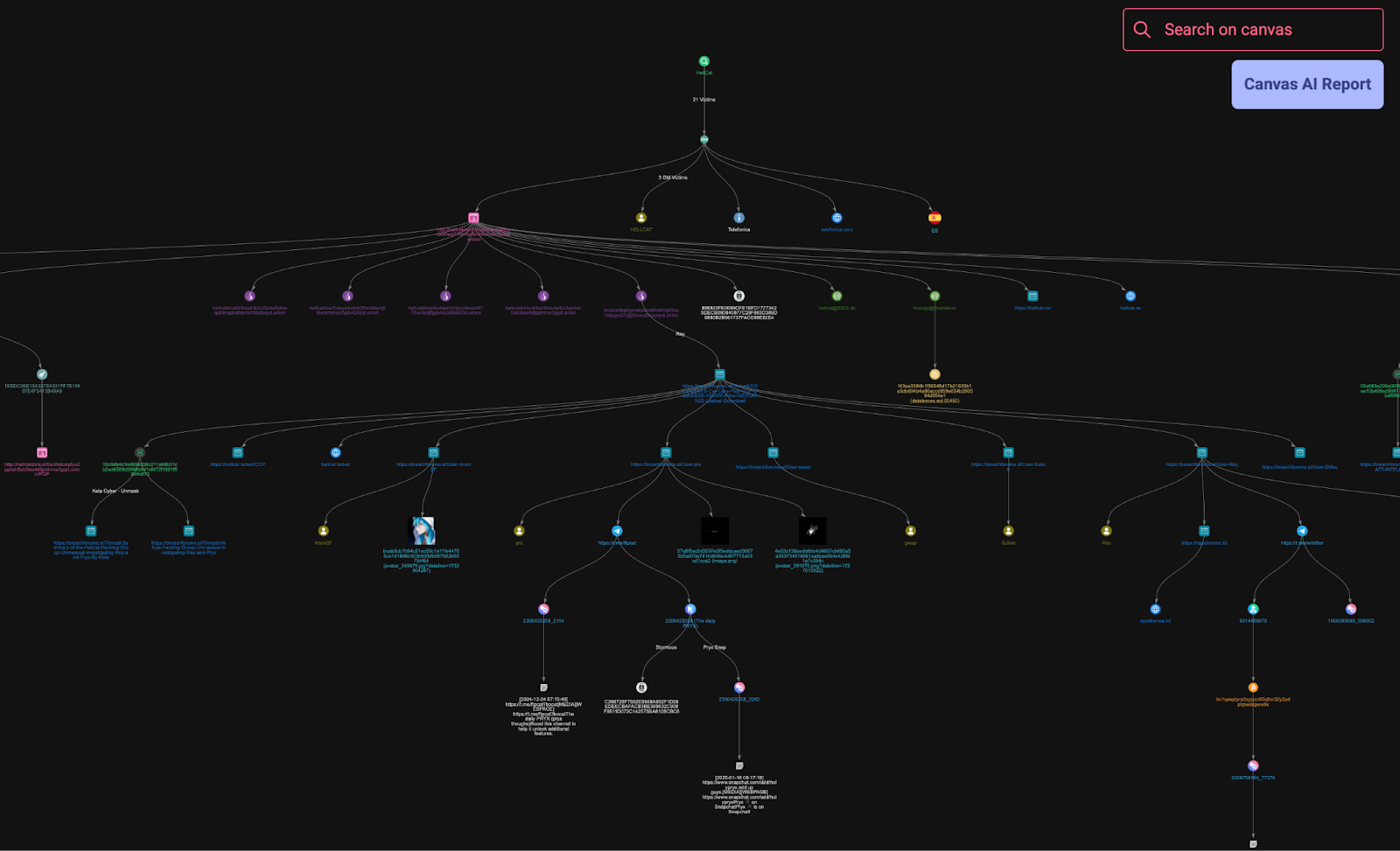
The investigation began by running the keyword “HellCat” within StealthMole’s Ransomware Monitoring module. This immediately surfaced 21 victims, all attributed to the same name, with activity recorded between October 2024 and May 2025. What initially looked like isolated mentions started to align into a more consistent pattern, reinforcing the idea that this was not a one-off actor.
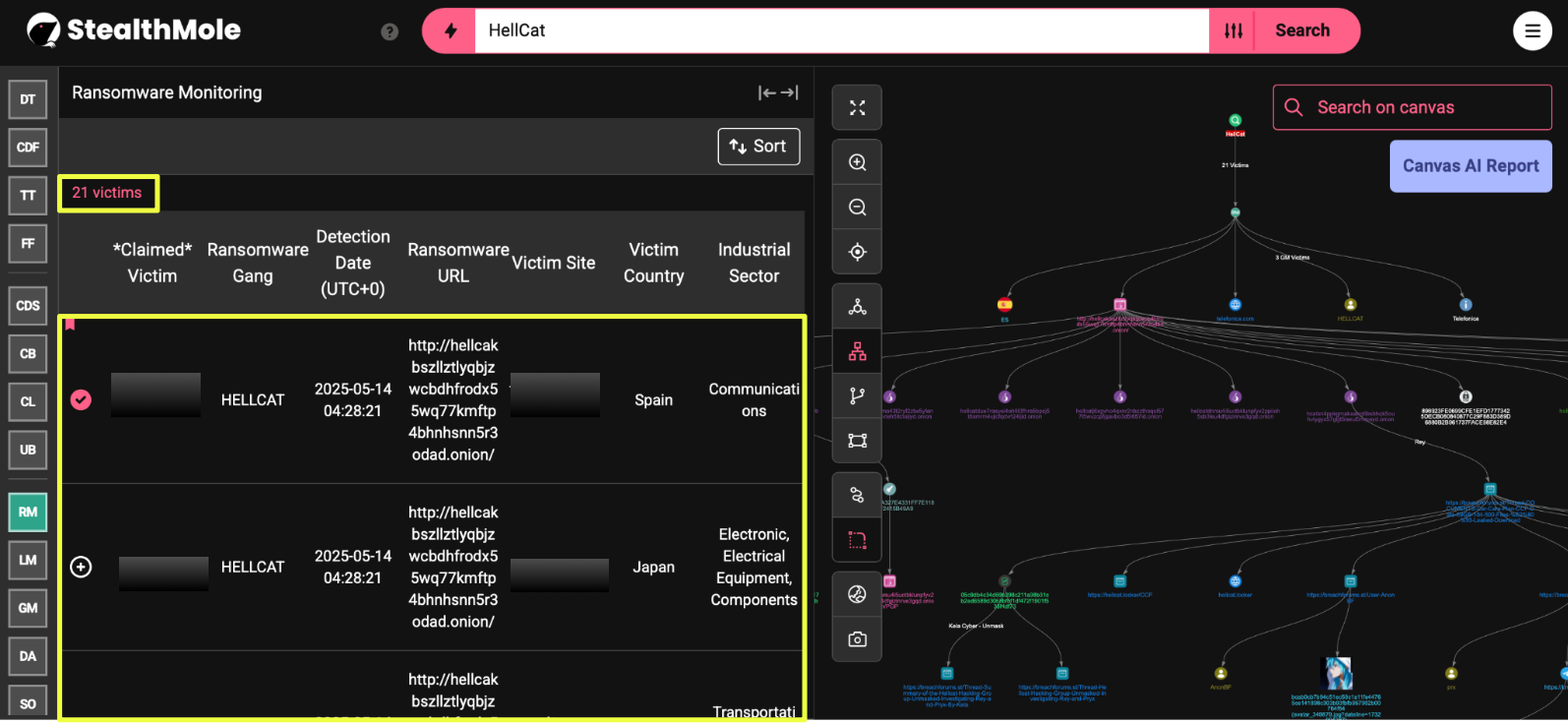 |
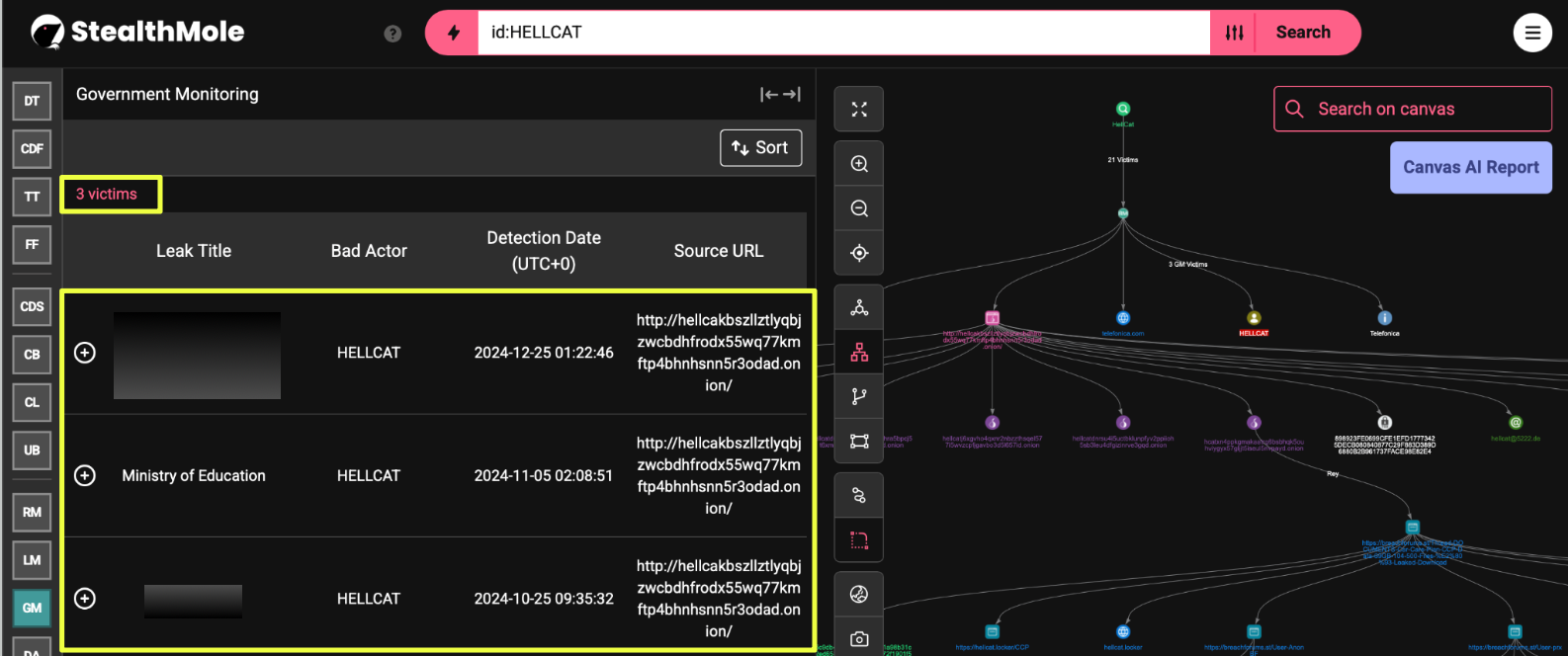
To see whether this activity extended beyond corporate targets, the same keyword was then queried in the Government Monitoring module. This returned 3 additional incidents, dated between October 2024 and December 2024, indicating that the activity wasn’t limited to a single sector.
 |
At this stage, the focus was still on the name itself. But a closer look at the results revealed something more useful than the victim listings.
Across both datasets, the same onion domain appeared repeatedly as the source where these incidents were originally posted:
- http://hellcakbszllztlyqbjzwcbdhfrodx55wq77kmftp4bhnhsnn5r3odad.onion/
This overlap shifted the direction of the investigation. Instead of treating each listing as a separate data leak, the focus moved to the underlying source. The repeated reference to a single domain suggested that these posts were not randomly distributed, but were being published from a centralized location.
That domain became the starting point for deeper analysis.
Onion Infrastructure and Leak Platform Analysis
With the onion domain identified as a recurring source across both ransomware and government-related incidents, the next step was to examine it more closely through StealthMole’s Dark Web Tracker.
- http://hellcakbszllztlyqbjzwcbdhfrodx55wq77kmftp4bhnhsnn5r3odad.onion/
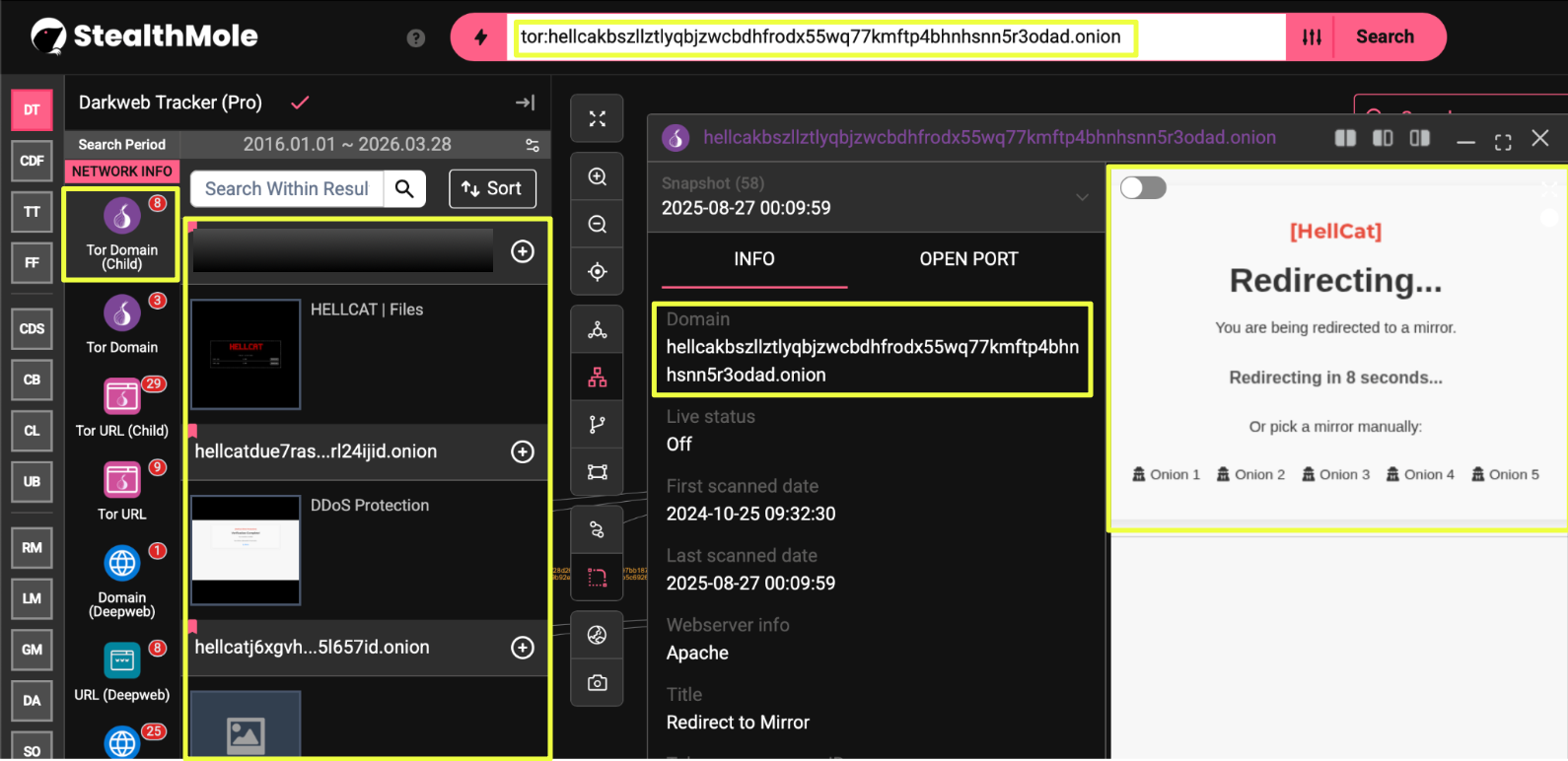 |
The domain did not exist in isolation. When pivoted within the tracker, it revealed a cluster of seven related onion domains, all associated with the same naming pattern and likely part of the same infrastructure.
- hellcatj6xgvho4qxnr2nbzzthsqel577i5wvzcpfjgavbo3d5l657id.onion
- hellcatdohzngkuh7zruzhi2wojrawbnzbyzljtkw6iluv5ussfer4id.onion
- hellcatdcy653ma43t2ryf2ztw5yfanqsbfmapndbqvteh5itctoijyd.onion
- hellcatdue7rasyoi4oh6t3fhra5bpcj5t6xmrm4vjicfqdvrl24ijid.onion
- hellcatdnrsu4i5uctbklunpfyv2ppiioh5sb3leu4dfgizinrve3gqd.onion
- hellcakbszllztlyqbjzwcbdhfrodx55wq77kmftp4bhnhsnn5r3odad.onion
Among these, only one domain was observed to be active at the time of analysis:
- hcat*************************************************ayd.onion
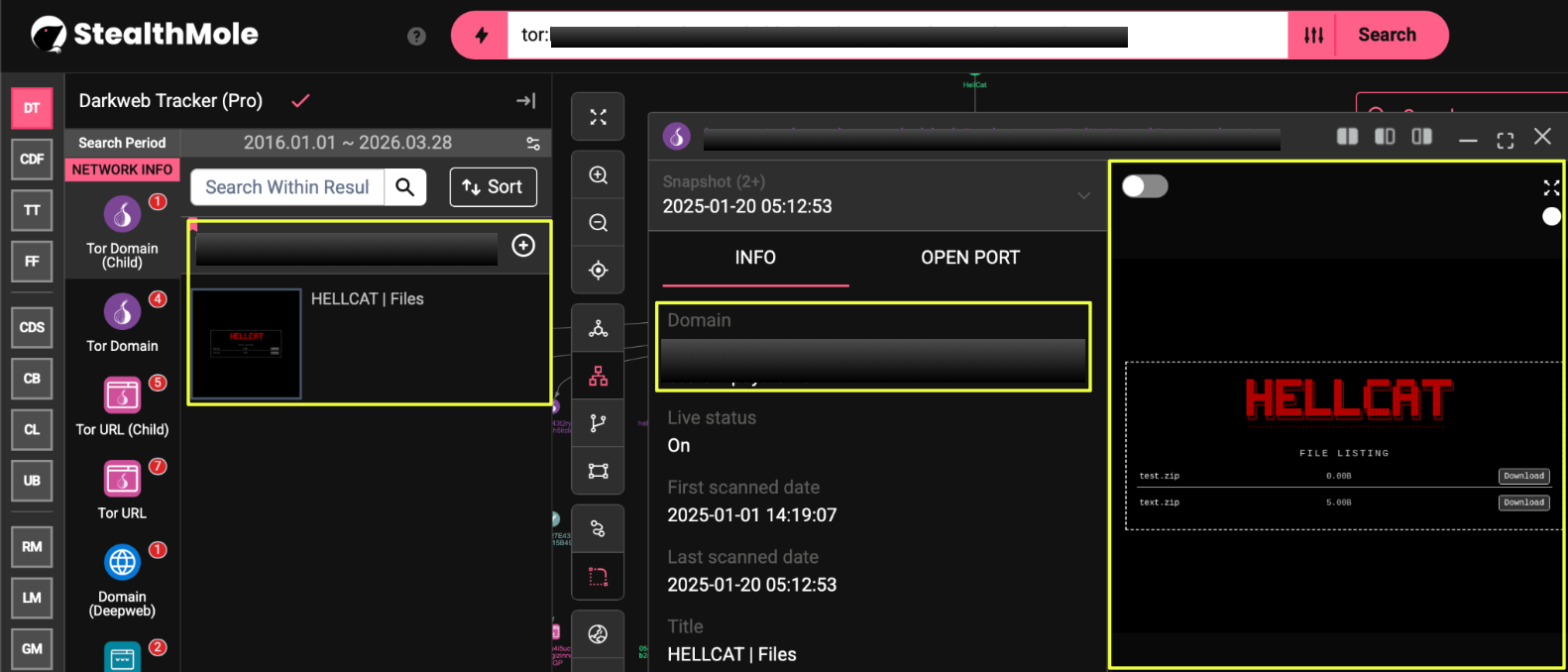 |
This instance was labeled as “HellCat Files” and presented a simple file-listing interface. The structure was minimal, with entries such as compressed files (.zip) available for download, without detailed descriptions, victim context, or negotiation interfaces typically seen in more mature ransomware leak sites.
The presence of multiple inactive domains suggests that the group has either rotated its infrastructure over time or experimented with different hosting instances. Rather than maintaining a stable, persistent leak site, the setup appears fragmented, with several domains no longer in use.
The active panel itself did not resemble a conventional ransomware data leak site. There were no visible victim listings, countdown timers, or negotiation mechanisms. Instead, the interface functioned more like a basic file repository, where content could be uploaded and accessed directly.
This shift, from victim listings to a simplified file distribution model, adds an important layer to understanding HellCat’s operations. It suggests that the group’s infrastructure is not built around structured extortion workflows, but rather around flexible and low-complexity content hosting.
At this point, the investigation moved beyond identifying the infrastructure itself and focused on uncovering the communication channels and identifiers embedded within it.
Communication Channels and Operational Setup
Following the identification of HellCat’s onion infrastructure, the next step was to examine what was embedded within these domains beyond file hosting. Using StealthMole’s Dark Web Tracker, several communication artifacts were identified across the indexed pages.
One of the first indicators was the presence of multiple TOX identifiers, including:
- 898************************************************************E4
- F97D**********************************************************E7F
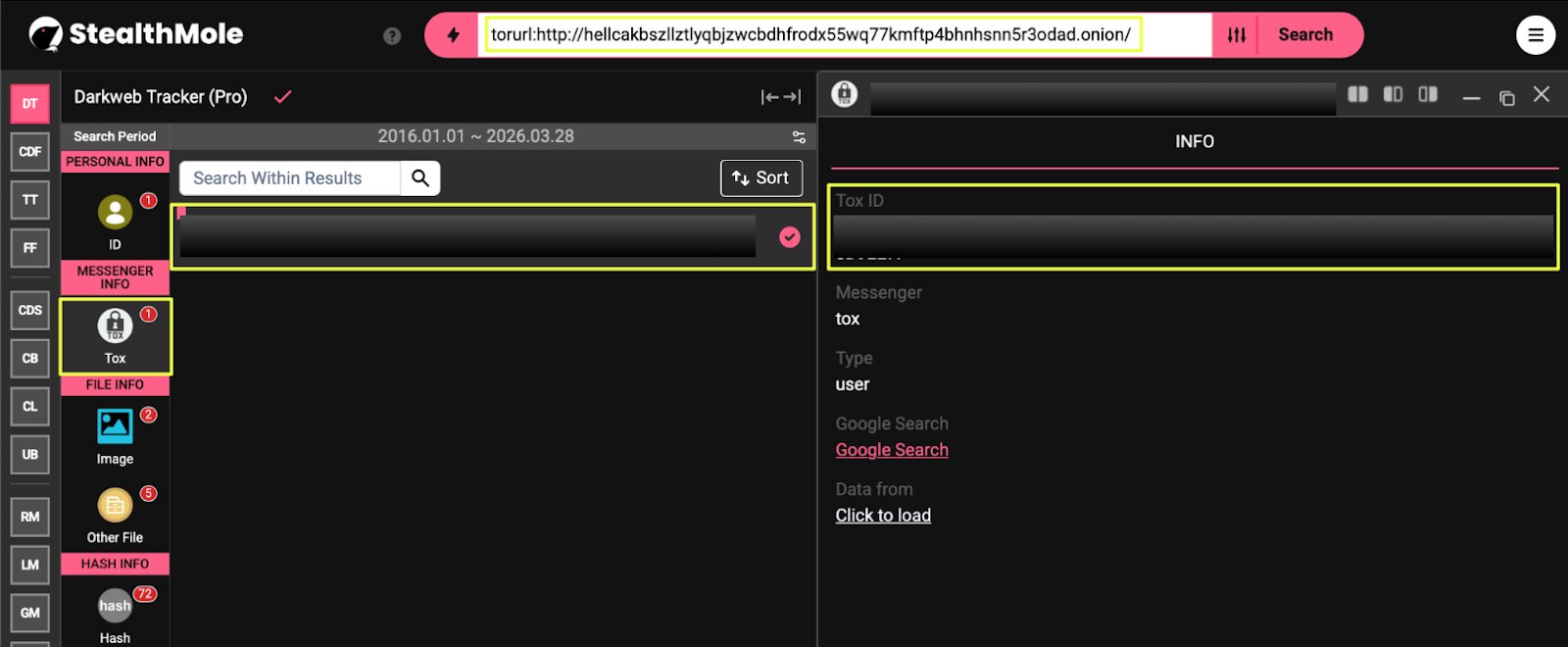 |
These were consistently referenced within contact pages and error panels, indicating their role as primary communication channels. The use of TOX, a decentralized and encrypted messaging protocol, aligns with common practices among underground actors seeking to avoid traceable communication platforms.
In addition to TOX, multiple email addresses were identified:
- he*******t@5**2.de
- h****p@firemail.cc
- h*****p@h****t.*w
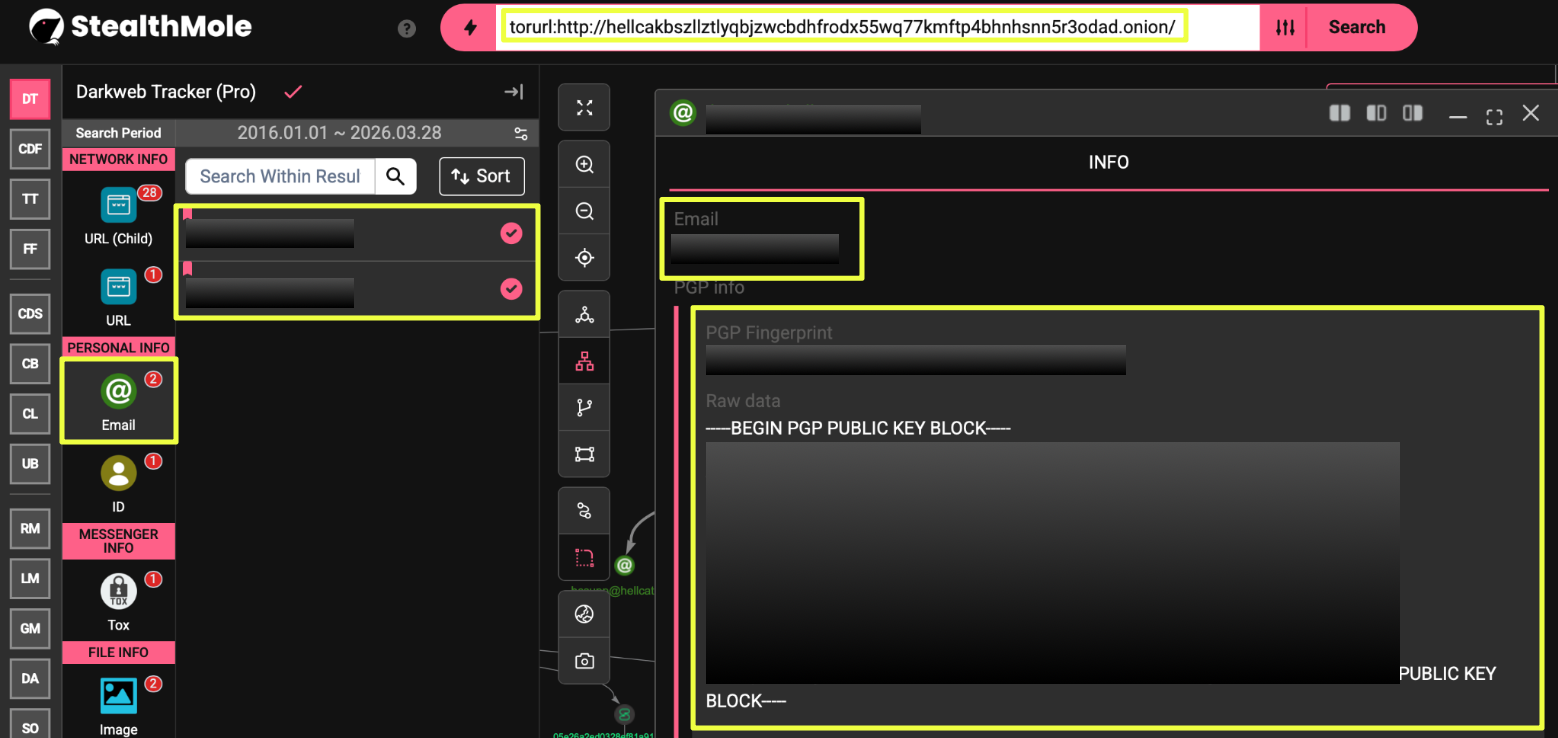 |
These addresses followed a consistent naming pattern, suggesting they were part of a coordinated communication setup rather than isolated contacts. One of these entries was further linked to a PGP fingerprint:
- 2A0**********************************F81
- 1EE**********************************9A9
The presence of PGP keys indicates that encrypted communication was supported, likely for exchanging sensitive information such as data samples, credentials, or negotiation details.
Further exploration of the infrastructure revealed that HellCat maintained a broader operational interface beyond simple leak hosting. Certain onion pages included sections dedicated to:
- Instructions on setting up TOX
- Guides for using XMPP-based messaging
- Basic walkthroughs on acquiring Bitcoin
- A temporary note-sharing service for exchanging information
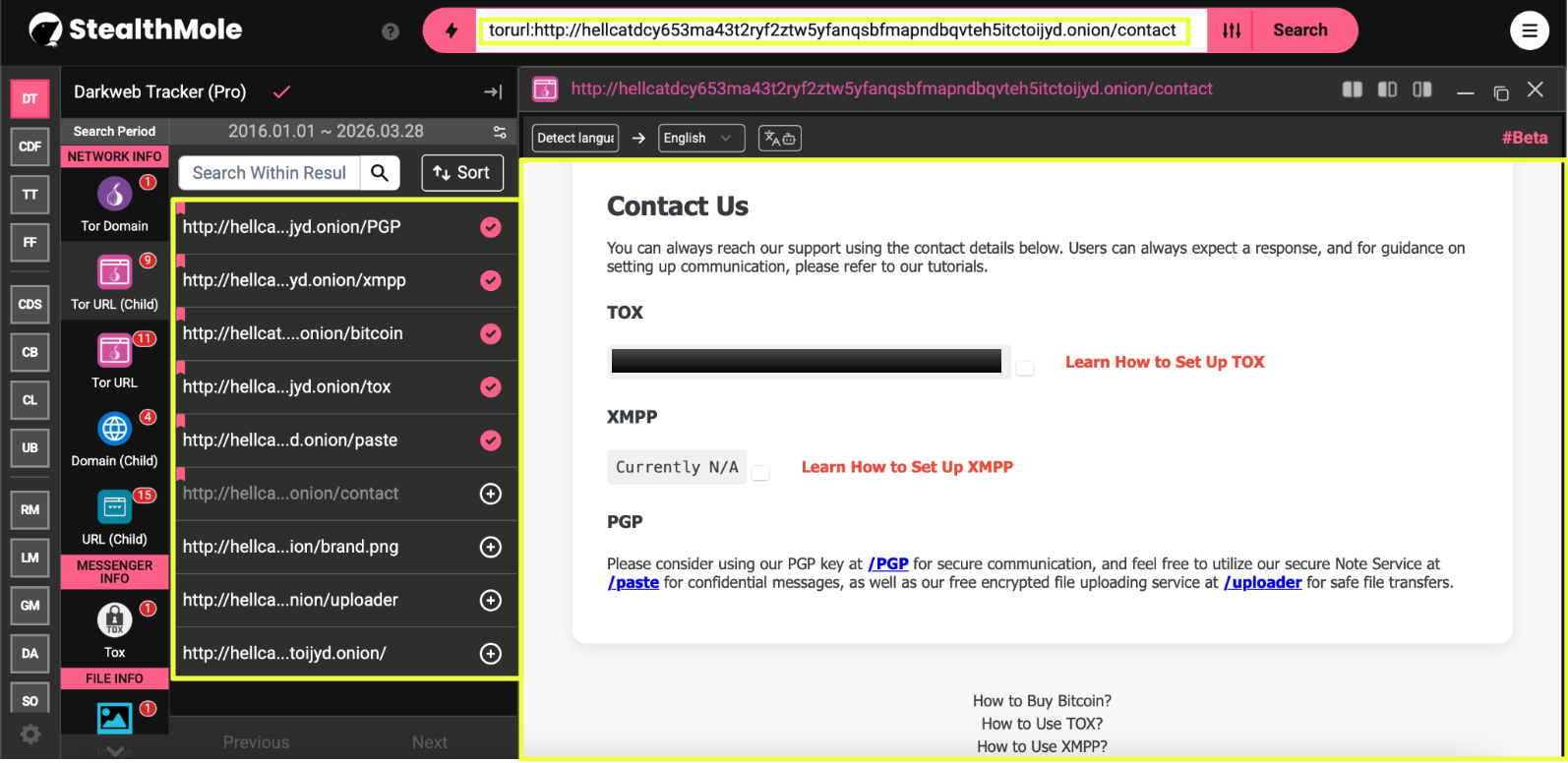 |
This combination of tools suggests an environment designed not only for publishing data, but also for facilitating interaction with external parties. The inclusion of step-by-step guides, particularly for cryptocurrency usage, indicates that the setup may be intended for users with varying levels of technical familiarity.
At the same time, parts of the interface appeared incomplete or templated. For example, generic placeholders such as user@jabber.com were present, suggesting that some components were not fully configured or were reused across deployments without customization.
Overall, the communication layer reflects a structured but relatively lightweight setup. Rather than relying on a single channel, HellCat appears to maintain multiple parallel methods of interaction, combining encrypted messaging, email, and public-facing interfaces to support its operations.
Associated Actors and Forum Presence
With the onion infrastructure and communication channels mapped, the next step was to identify whether this activity could be tied to specific actors operating across underground forums.
The pivot began from the active onion link:
- hcat********************************************ayd.onion
When this domain was further investigated using StealthMole’s Dark Web Tracker, it led to a BreachForums thread associated with a dataset leak:
- https://breachforums.**/Thread-DOCUMENTS**********Leaked-Download
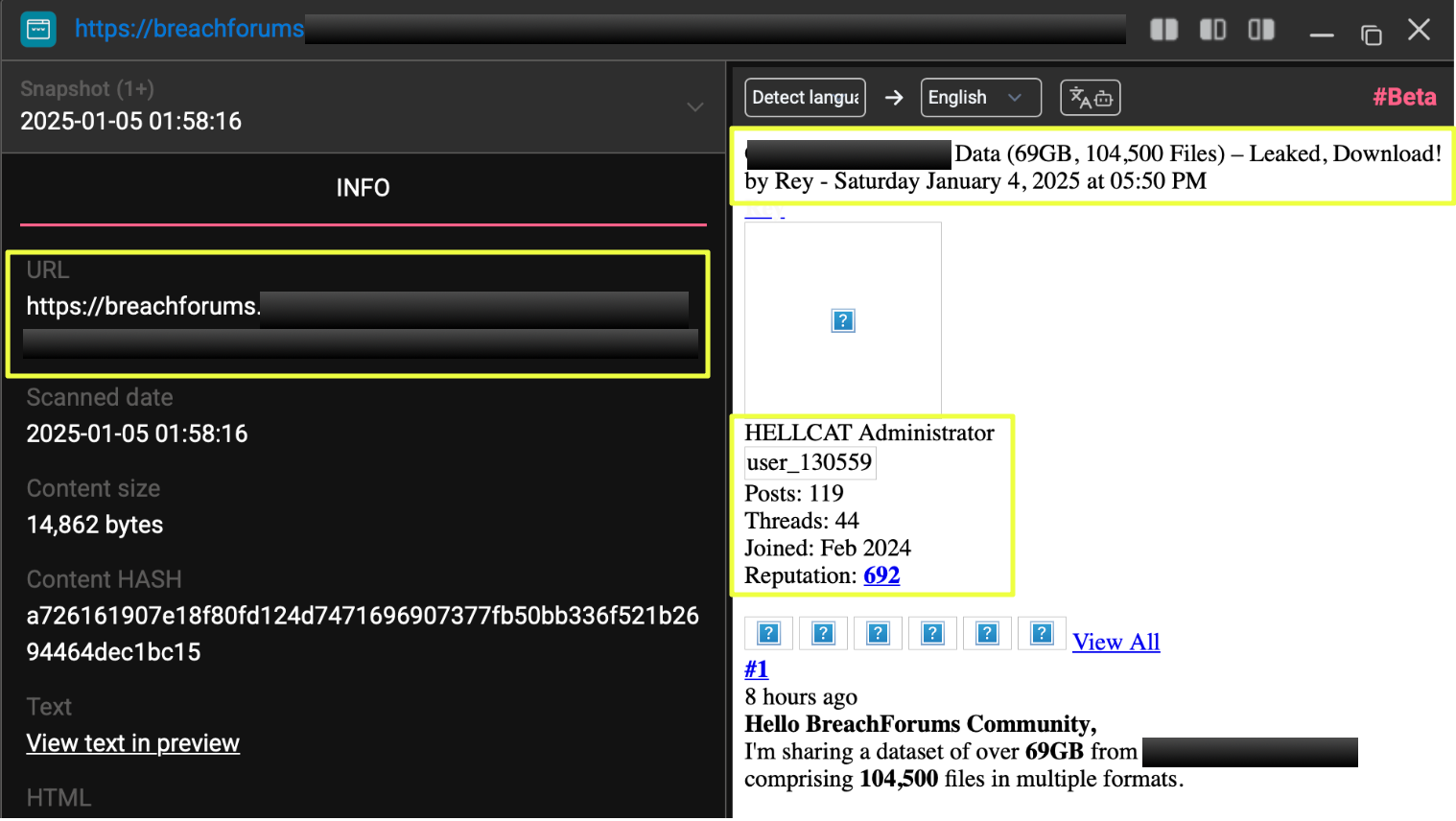 |
This thread became a key entry point into identifying the actors operating around HellCat-related activity. From this thread and related pivots, multiple user profiles were identified:
- https://breachforums.**/User-prx
- https://breachforums.**/User-gwap
- https://breachforums.**/User-Rey
- https://breachforums.**/User-SMeu
- https://breachforums.**/User-miyako
- https://breachforums.**/User-AnonBF
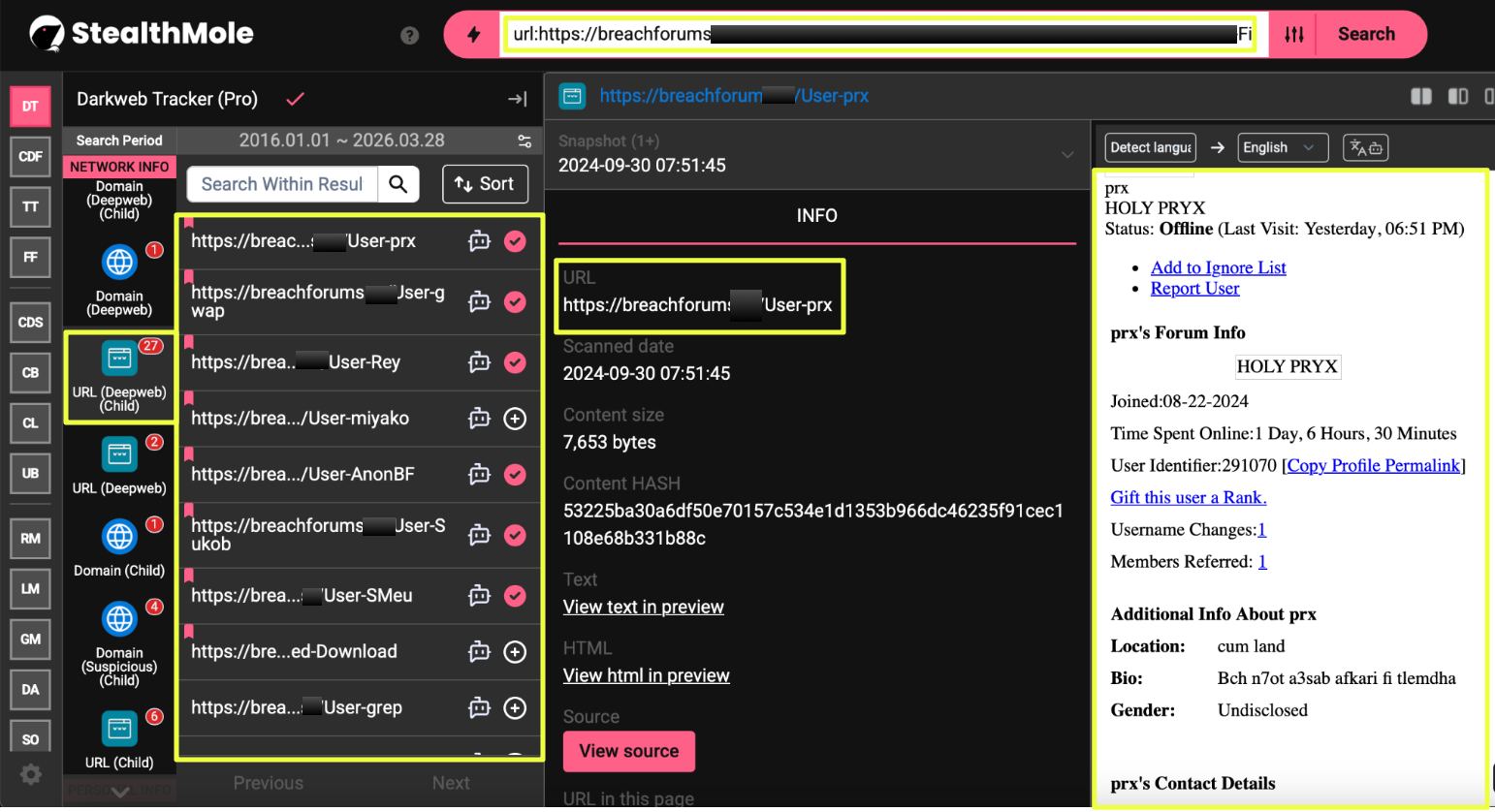 |
These profiles were not randomly selected. Each of them appeared either directly within the thread, in associated discussions, or through cross-references observed during further navigation.
A closer review of these profiles revealed several points of overlap:
- The user Rey maintained visible references to other accounts within their forum signature, including mentions of prx and SMeu.
- The profile miyako was categorized as an Initial Access Broker, indicating involvement in selling or providing access to compromised systems rather than just sharing leaked data.
- Multiple profiles referenced external communication channels (Telegram, Session), aligning with the communication infrastructure previously identified.
Beyond visible interactions, a more concrete layer of linkage emerged through communication identifiers. Several of these actors were associated with Session-based messaging IDs, which appeared across profiles and external communication references, including:
- 05651**************************************************1328 (Gwap)
- 05833*************************************************e918 (Miyako)
- 0552e***************************************************5e5e (Pryx)
- 05669***************************************************e00 (SMeu)
- 05e5d**************************************************c9849 (Rey)
 |
These identifiers provide a stronger technical basis for linking forum personas to off-platform communication channels. Unlike usernames, which can be easily changed or reused, Session IDs tend to remain consistent, making them useful for tracking continuity across environments.
In addition to forum activity, certain posts linked to external resources, including dataset previews and download links, reinforcing the connection between forum discussions and the onion-based file hosting infrastructure.
The same cluster of usernames was also observed in relation to data sale and leak posts beyond a single thread. For example, activity linked to HellCat-related datasets appeared in threads offering large-scale data packages, often accompanied by sample files and escrow-based transactions.
This pattern indicates that the activity is not limited to a single post or campaign, but instead reflects ongoing participation within underground data exchange environments.
While none of these accounts explicitly declare themselves as part of a formal “HellCat group,” the repeated overlap in forum threads, shared references, communication channels, and proximity to HellCat-linked infrastructure suggests the presence of a loosely connected cluster of actors.
Rather than operating as a tightly structured organization, HellCat appears to exist within a network where different individuals contribute to different parts of the workflow, from access acquisition to data distribution.
Technical Artifacts and Cross-Platform Indicators
As the investigation moved deeper into HellCat’s infrastructure and forum activity, additional artifacts began to surface that helped connect different parts of the ecosystem. These were not isolated findings, but recurring identifiers that appeared across onion sites, forum profiles, and communication channels.
One of the more significant observations came from the analysis of the primary onion domain, where seven different malware hashes were indexed. These were associated with the same infrastructure.
- f9c1*********************************************************5e5
- f8b6*********************************************************641
- 7f28*********************************************************27c
- 393b*********************************************************6f2
- 15a2*********************************************************f0b
- dcd7*********************************************************ac2
- b8e7*********************************************************be7
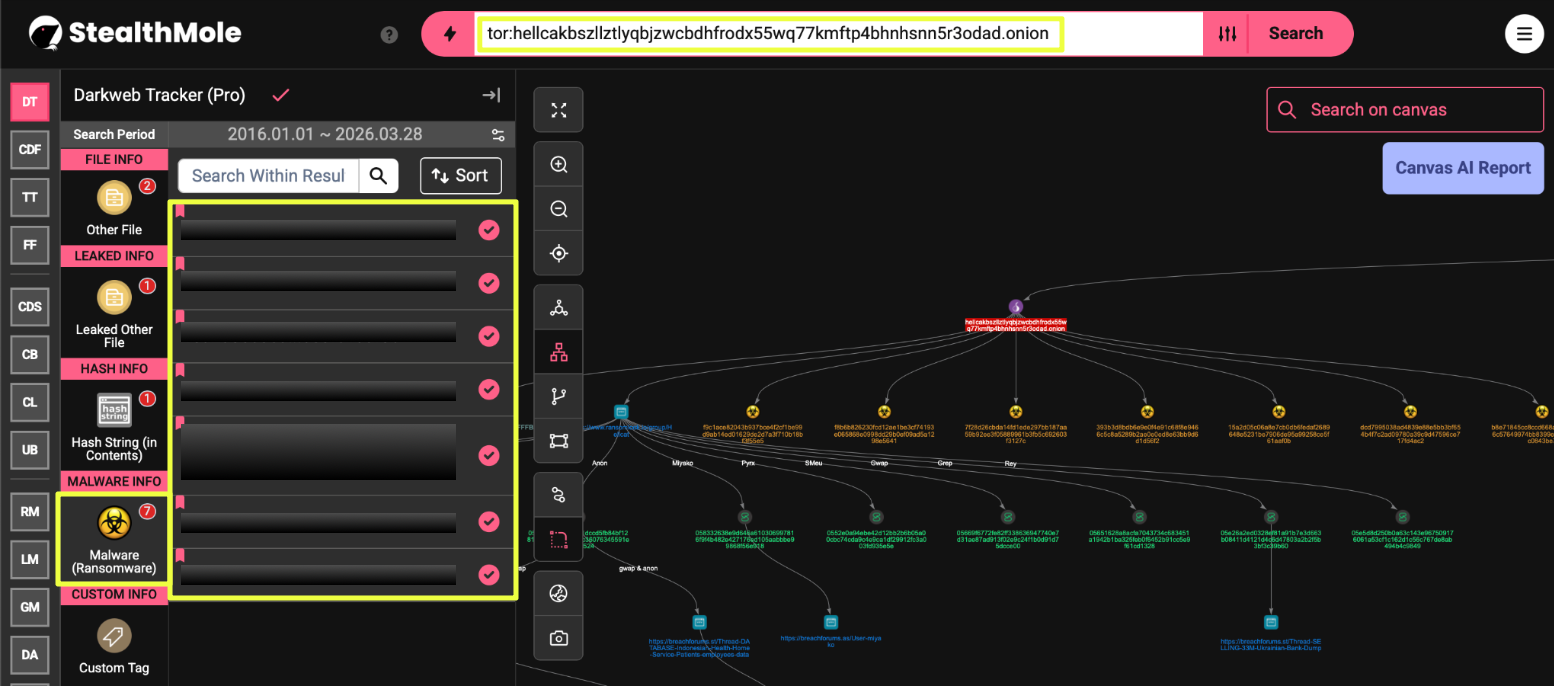 |
These hashes are particularly important because, unlike domains or usernames, they remain consistent even if the actor changes infrastructure. Their presence suggests that HellCat is not only distributing leaked data but is also associated with ransomware files.
Alongside these technical indicators, multiple communication identifiers were observed across platforms. Session-based messaging IDs appeared repeatedly in connection with forum profiles and external communication channels, including:
- 05e5d********************************************************9849
- 05c9d********************************************************df73
 |
These identifiers provided a consistent thread between different environments, linking forum activity to off-platform communication methods. Their reuse across contexts suggests continuity rather than isolated accounts, reinforcing the idea of a connected operational layer.
Similarly, the investigation identified one more TOX identifier used for encrypted communication:
- 1F571****************************************************8F
The presence of multiple TOX IDs suggests either role separation or multiple individuals operating within the same environment. Rather than relying on a single communication channel, HellCat appears to maintain parallel options, which aligns with the fragmented infrastructure observed earlier.
Financial indicators also emerged during the investigation. A Bitcoin wallet was identified in connection with HellCat-linked activity:
- bc1q****************************9x
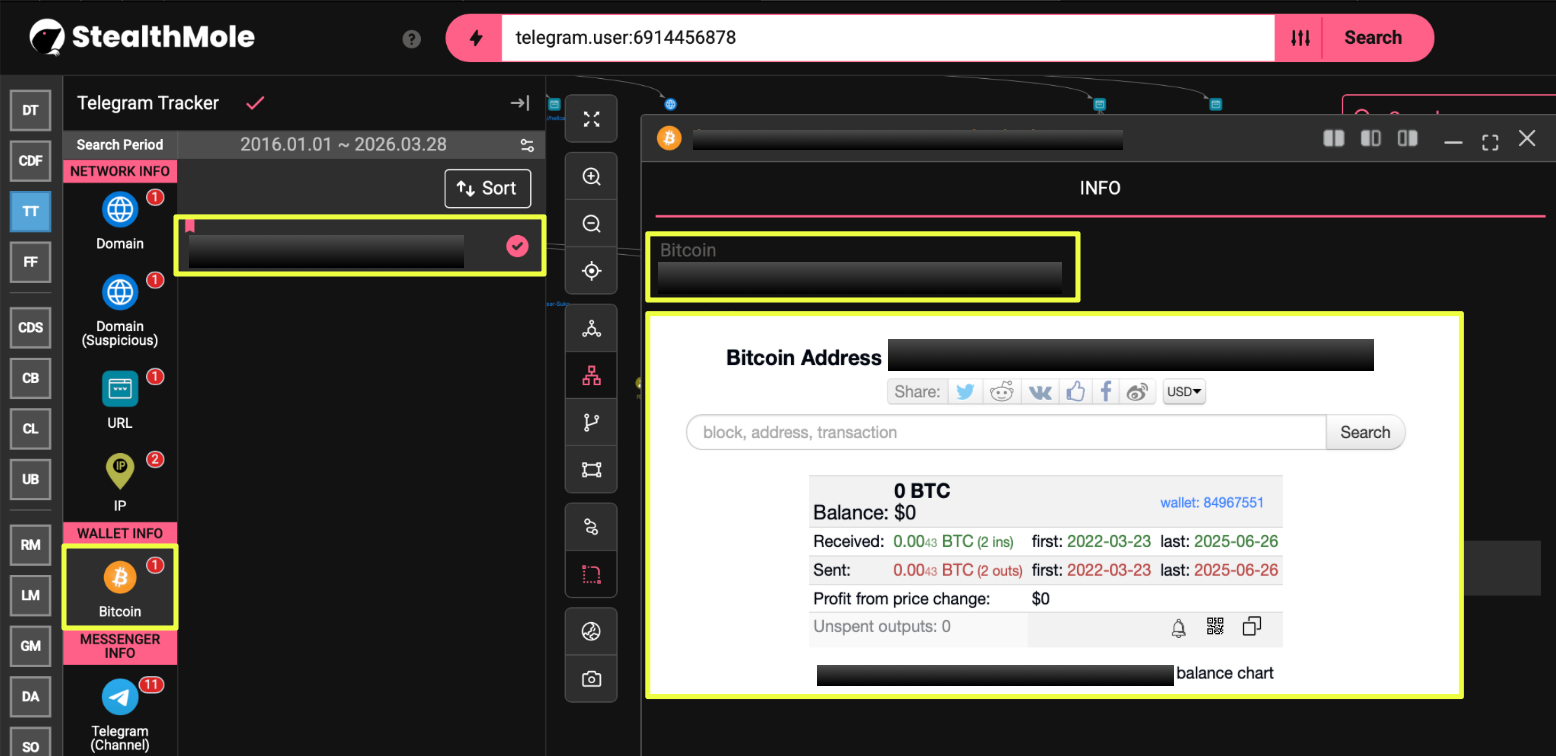 |
The transaction activity associated with this wallet was limited and relatively low in value. This stands in contrast to the large-scale financial flows typically observed in established ransomware operations, where payments are often substantial and frequent. The modest activity here suggests that monetization may not be fully developed, or that the actor operates at a smaller scale than more mature ransomware groups.
Finally, Telegram activity provided additional context. Accounts associated with HellCat-related operations were observed sharing leaked content and interacting with other users. In several cases, content posted on forums was later redistributed through Telegram channels, indicating a pattern of cross-platform amplification. Some of these accounts were subsequently deleted, which may reflect attempts to reduce visibility or adapt to increased scrutiny.
 |
Overall, these artifacts do more than just confirm presence, they help define the nature of the operation. The combination of persistent technical indicators, reused communication channels, and limited financial activity points toward an environment that is active but not fully structured. Rather than a tightly controlled ransomware operation, HellCat appears to operate within a flexible setup where tools, identities, and platforms are reused as needed.
Conclusion
What initially appeared as a series of isolated leak posts linked to the name HellCat gradually revealed a more structured pattern when examined through StealthMole. The activity traced back to a shared onion-based infrastructure, supported by multiple communication channels and a recurring set of forum actors operating in close proximity to one another.
At the infrastructure level, the environment does not follow the conventions of established ransomware operations. Instead of maintaining a stable and structured leak site, HellCat relies on a fragmented setup, with multiple inactive domains and a single active instance functioning as a simple file repository. This suggests a level of operational inconsistency and a preference for flexibility over permanence.
In contrast, the communication layer shows a more deliberate approach. The use of multiple TOX identifiers, Session IDs, email addresses, and PGP keys indicates that the actors maintain several parallel channels, allowing them to adapt if any single method becomes unavailable. This balance between loosely maintained infrastructure and layered communication reflects a hybrid operational model.
The actor ecosystem further supports this interpretation. Rather than a clearly defined group, the activity is distributed across several forum profiles with different roles, including data sharing and access brokerage. These actors are connected not through explicit declarations, but through repeated overlap in threads, shared identifiers, and consistent proximity to HellCat-linked activity.
Technical artifacts add another dimension to this picture. While ransomware-classified files are present, the limited financial activity associated with identified cryptocurrency wallets does not align with large-scale extortion operations. This suggests that the activity may be driven more by data distribution and marketplace engagement than by structured ransom-based monetization.
Together, HellCat does not fit neatly into a single category. It operates within a fluid and loosely connected ecosystem where infrastructure, identities, and roles are reused and adapted as needed. Rather than functioning as a centralized ransomware group, it reflects an emerging model of underground activity that prioritizes flexibility over structure.
Editorial Note
Attribution in cyber and dark web investigations is rarely definitive. The findings in this report are based on observable artifacts, platform correlations, and patterns identified through StealthMole. While these connections provide a strong analytical foundation, they do not imply absolute ownership or control by any single entity. This case highlights how seemingly unrelated data points, when explored systematically, can reveal meaningful patterns, while also reinforcing the need for caution in drawing conclusions within complex and evolving underground environments.
To access the unmasked report or full details, please reach out to us separately.
Contact us: support@stealthmole.com
Labels: Ransomware
.svg)
.svg)
.svg)