Behind the Mask: Mapping the ‘Anonymous Hackers’ Hack-for-Hire Infrastructure
 |
Services offering hacking capabilities for hire are not new to the dark web. Over the years, numerous hidden services have emerged claiming to provide everything from website intrusions and social media account takeovers to DDoS attacks and data extraction. These platforms often present themselves as professional teams of hackers, advertising a wide range of services while encouraging potential clients to communicate through encrypted channels.
At first glance, many of these sites appear to operate independently. They carry different names, use different domains, and present themselves as separate groups. However, the line between independent actors and shared infrastructure is often difficult to see. Operators frequently rotate domains, change branding, and introduce new contact channels, making it harder to determine whether these services truly belong to different groups or are simply different faces of the same operation.
Using StealthMole, this investigation explored several Tor-based websites advertising hacking services. As the analysis progressed, a series of unexpected connections began to surface: linking domains, contact information, and cryptographic identifiers across multiple sites that initially appeared unrelated.
What began as a routine review of a single service eventually led to a broader investigation into a network of hacking-for-hire platforms operating across several Tor domains.
Incident Trigger and Initial Investigation
The investigation did not initially begin with hack-for-hire services. Instead, the discovery emerged while analyzing infrastructure connected to a separate Android malware case. During that analysis, StealthMole surfaced a Tor hidden service advertising professional hacking services under the name “Anonymous Hackers.”
- hackd******************************************qyd.onion
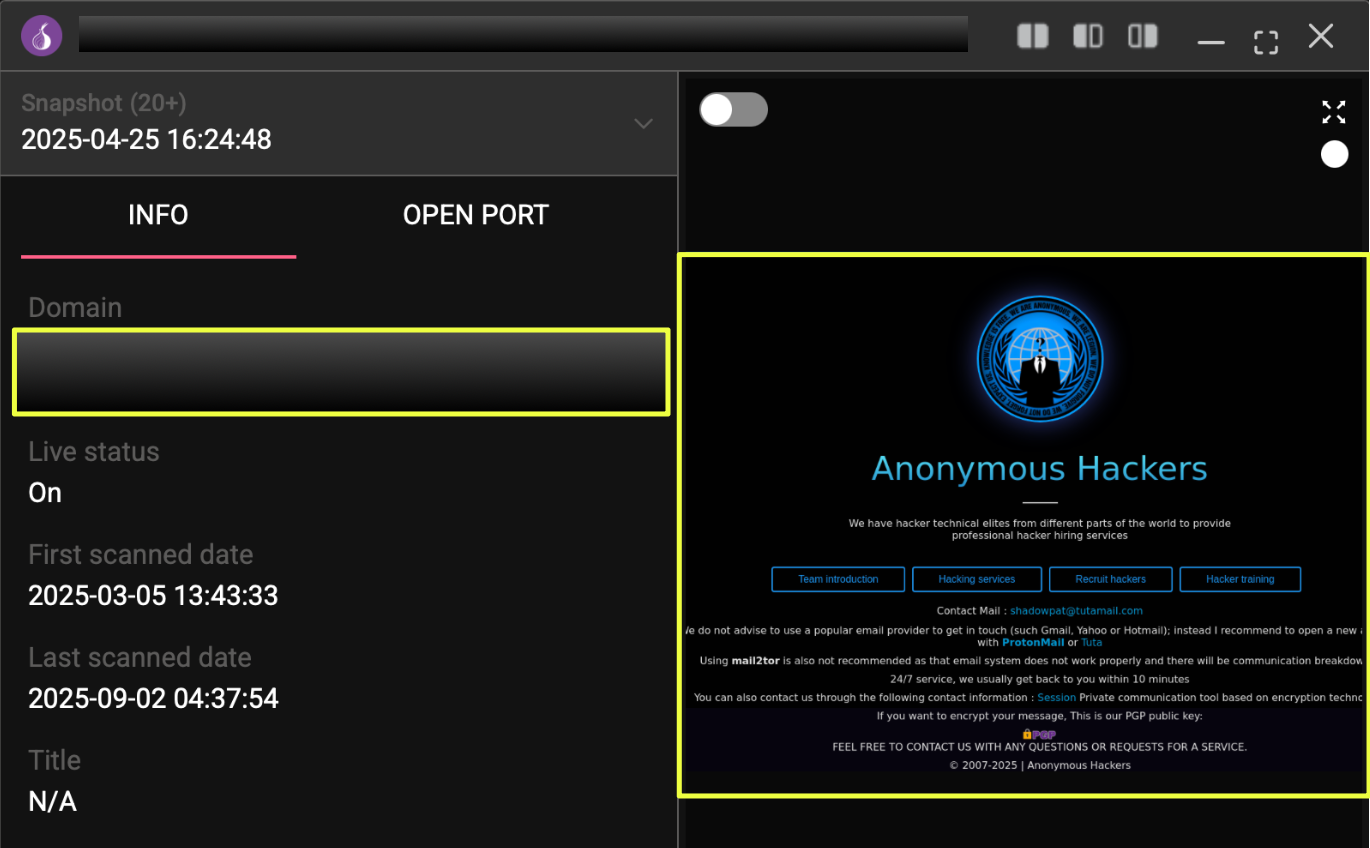 |
The platform presented itself as a professional hacking service provider, offering a wide range of capabilities including website intrusions, DDoS attacks, social media account compromise, database leaks, email hacking, phone monitoring, and even services such as background checks and cryptocurrency recovery. The interface also provided several communication channels intended for potential clients, including encrypted messaging and email contact options.
Initial examination of the site revealed multiple contact identifiers embedded within the platform. These included the following email addresses:
- sha****t@tutamail.com
- 3*********@anmail.org
- ano******ers@tuta.com
- sh********c@proton.me
The website also displayed a public PGP fingerprint intended for encrypted communication with customers:
- 25AD**********************************E0
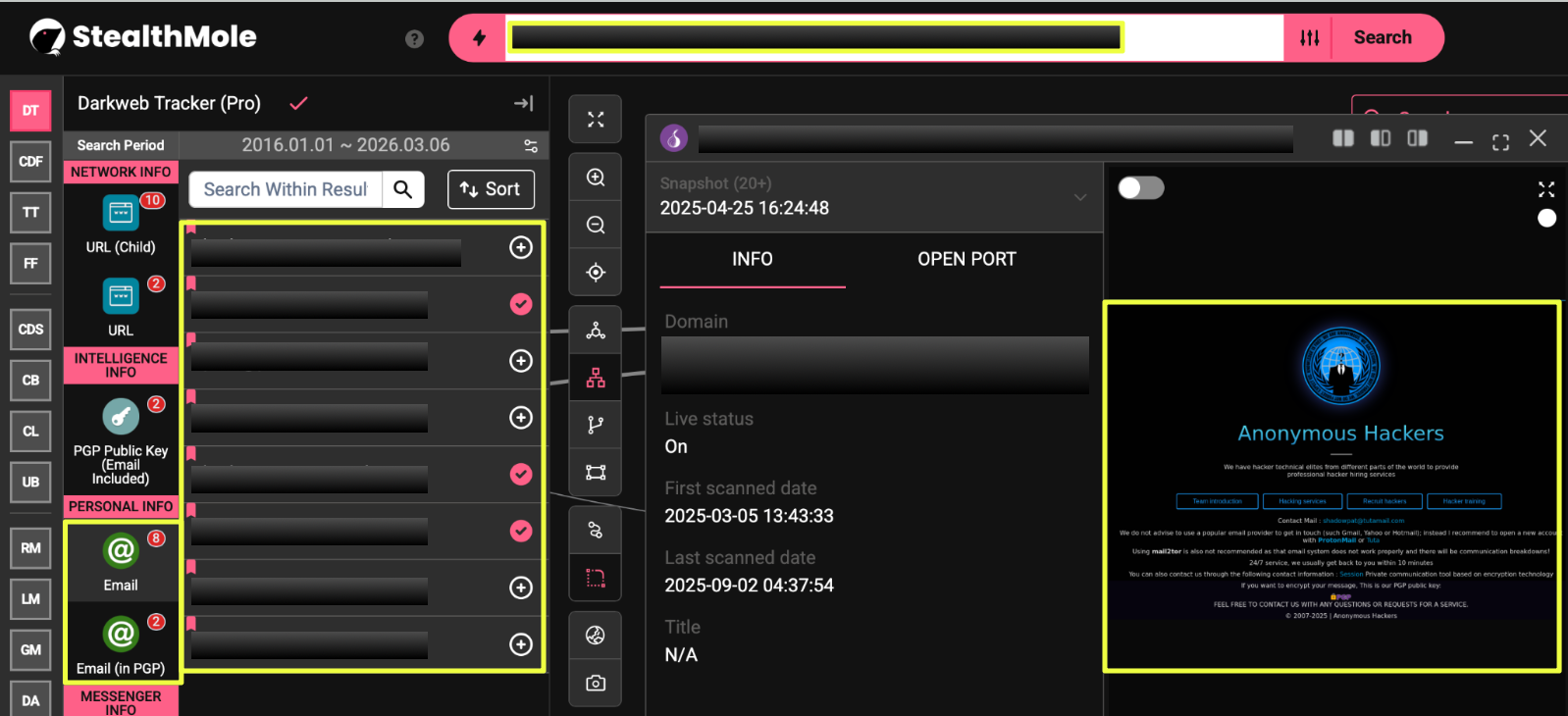 |
Given that dark web service providers often reuse contact information or cryptographic identifiers across multiple platforms, these artifacts provided an opportunity to pivot further using StealthMole. By investigating these identifiers, additional hidden services, contact channels, and infrastructure elements associated with the same ecosystem began to emerge.
Expanding the Infrastructure
With the initial artifacts identified, the investigation shifted toward determining whether the “Anonymous Hackers”website operated as an isolated service or if it was part of a larger infrastructure. Using StealthMole’s dark web monitoring tools, the investigation began by pivoting on the contact identifiers discovered on the site, particularly the email addresses and the PGP fingerprint.
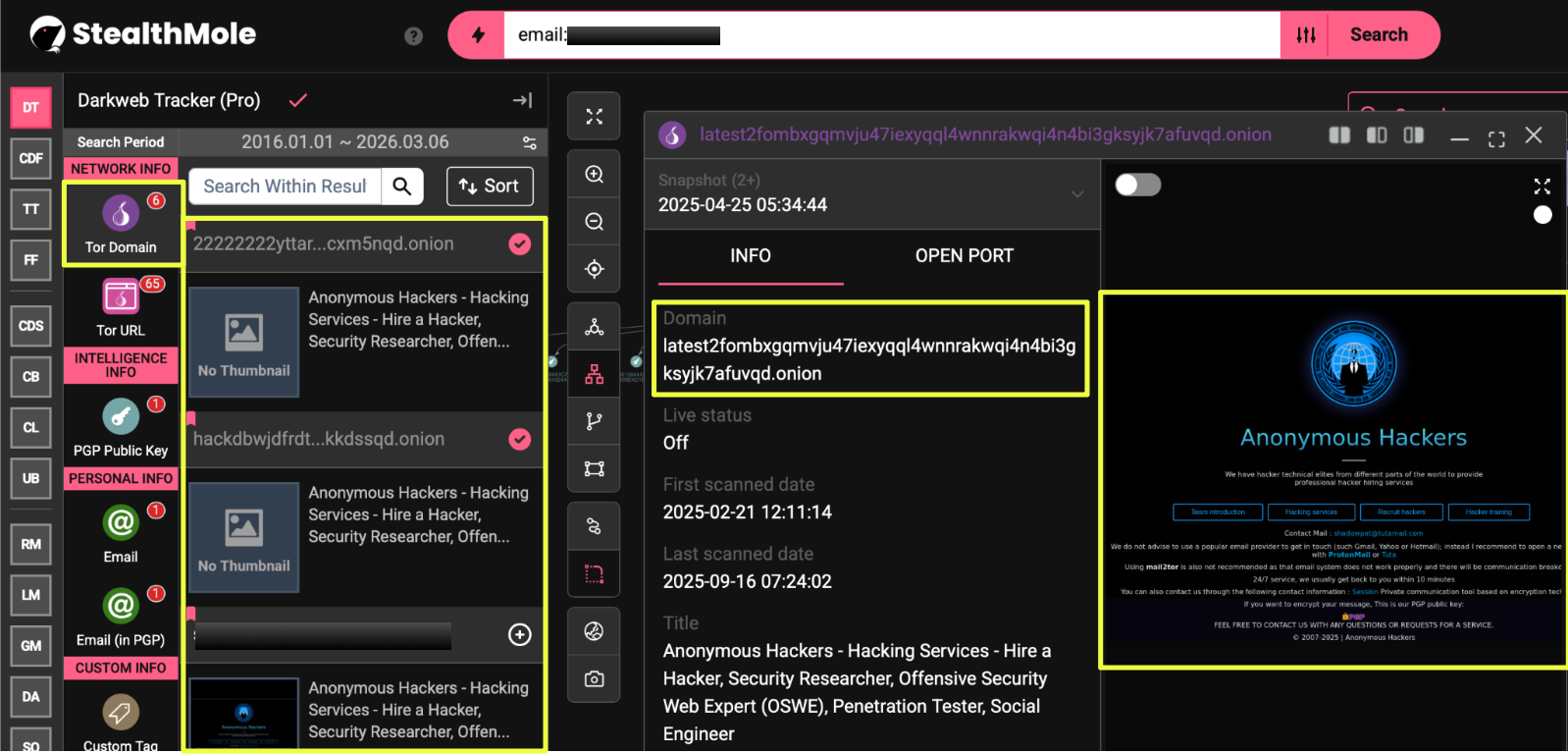
One of the earliest pivots focused on the email address 3389@anmail.org, which led to the discovery of several additional Tor hidden services. These domains shared similar naming structures and page titles, suggesting that they advertised the same type of hacking services. The domains identified through this pivot included:
- hackdbwjdfrdty6wo5uuthaqbw4i6polnoithj4nup7ulqv6ikkdssqd.onion
- 22222222yttarxo4r6kxpqfduphh2bjy24xflod4ikft7l62dcxm5nqd.onion
- latest2fombxgqmvju47iexyqql4wnnrakwqi4n4bi3gksyjk7afuvqd.onion
 |
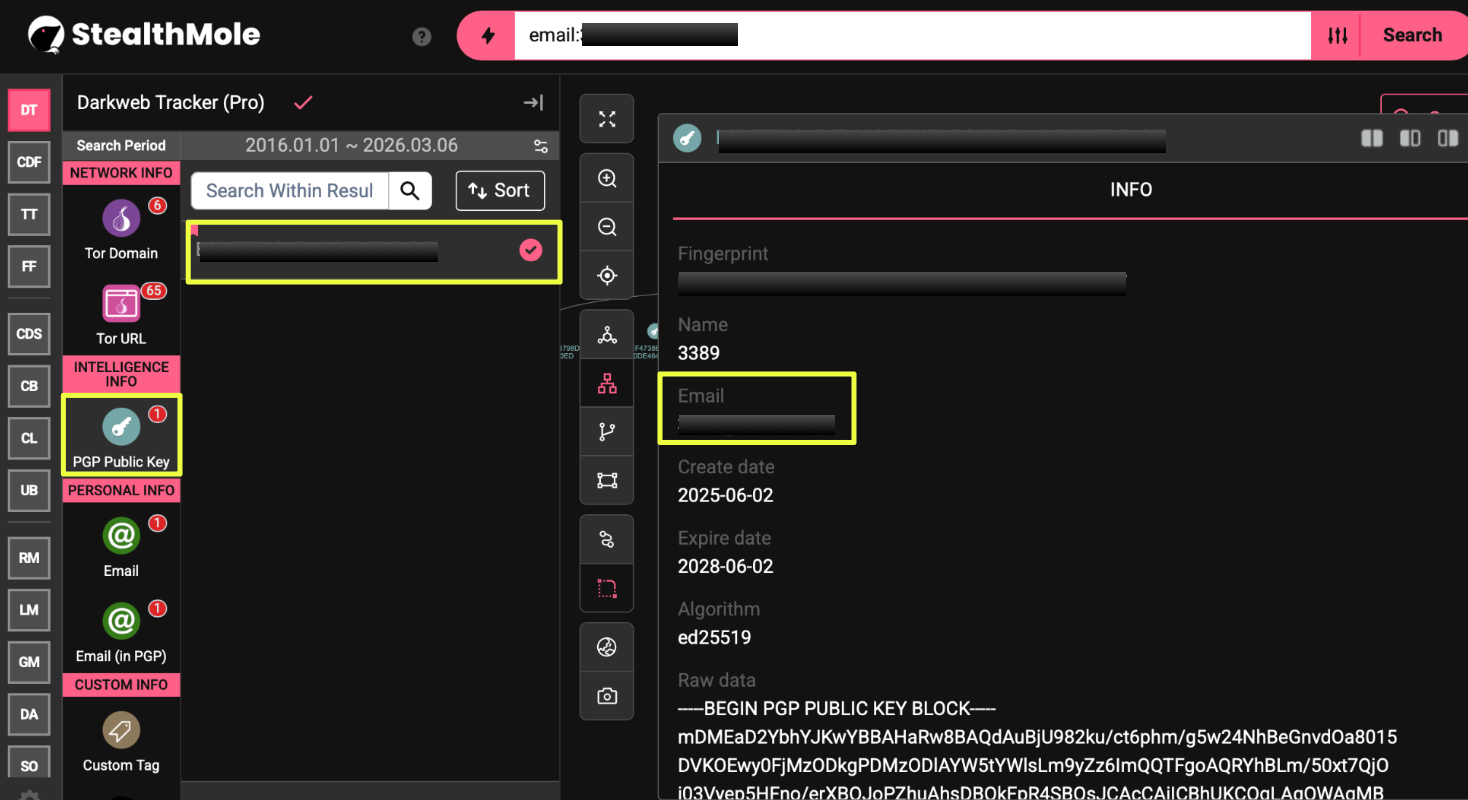
Further examination of the same pivot also surfaced another PGP fingerprint associated with the infrastructure:
- B9BF*********************************AD7
 |
The appearance of additional domains and cryptographic identifiers suggested that the original site might be part of a larger group of hidden services rather than a standalone operation. Each newly discovered artifact provided another point for investigation, allowing the analysis to continue mapping the infrastructure connected to these hacking platforms.
Discovering “Shadow Hacker” Infrastructure
As the investigation continued, StealthMole pivots began revealing additional hidden services connected to the previously identified artifacts. One of the domains uncovered during this stage was:
- hackvkgcbnm5wbgadmmn4hzt5rnraaxcmuycud56uuyze5jvdrl26gad.onion
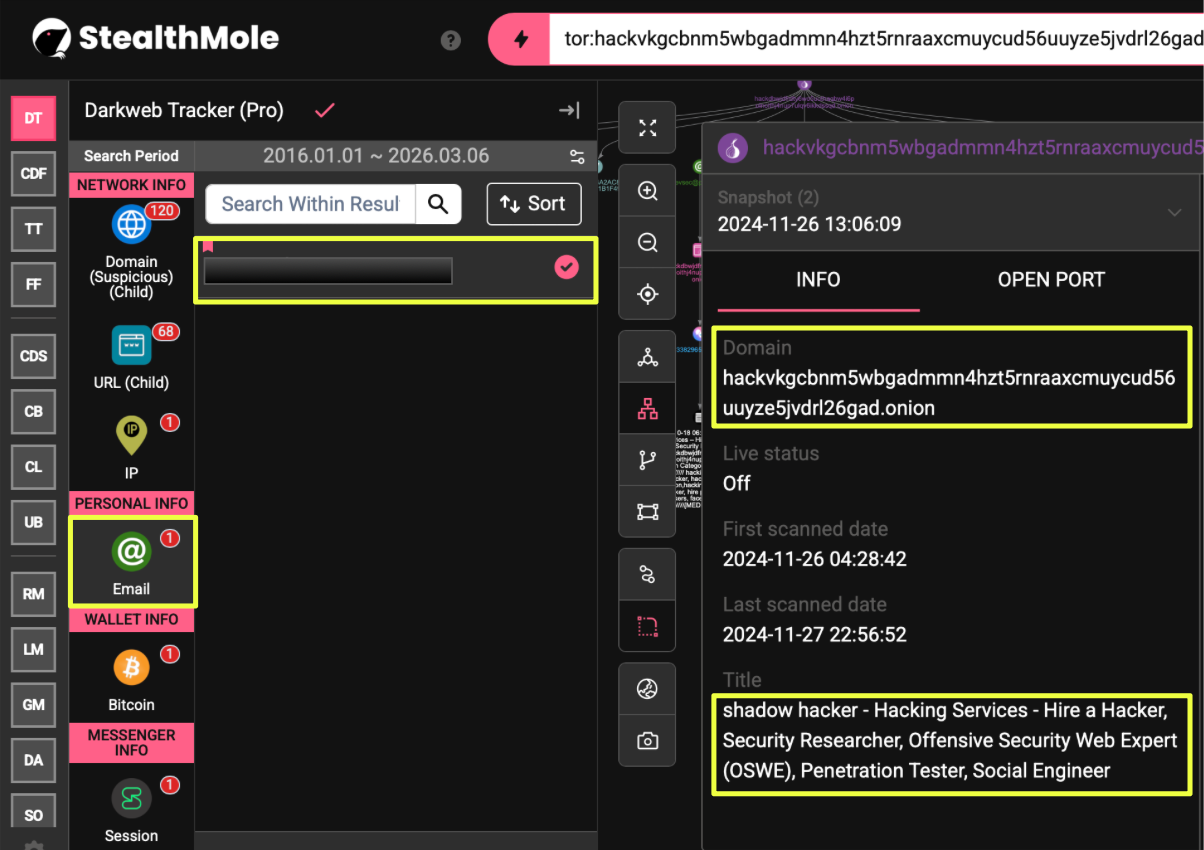 |
Unlike the earlier domains that used the “Anonymous Hackers” branding, this hidden service operated under the name “Shadow Hacker.” The site advertised a similar set of hacking services and followed a comparable structure, including service descriptions, pricing information, and contact channels for potential clients.
The page also exposed several additional artifacts that could be used for further investigation. These included the email address:
- co*******n@privatemx.org
as well as a Bitcoin wallet listed for payments:
- bc1*************************3e0
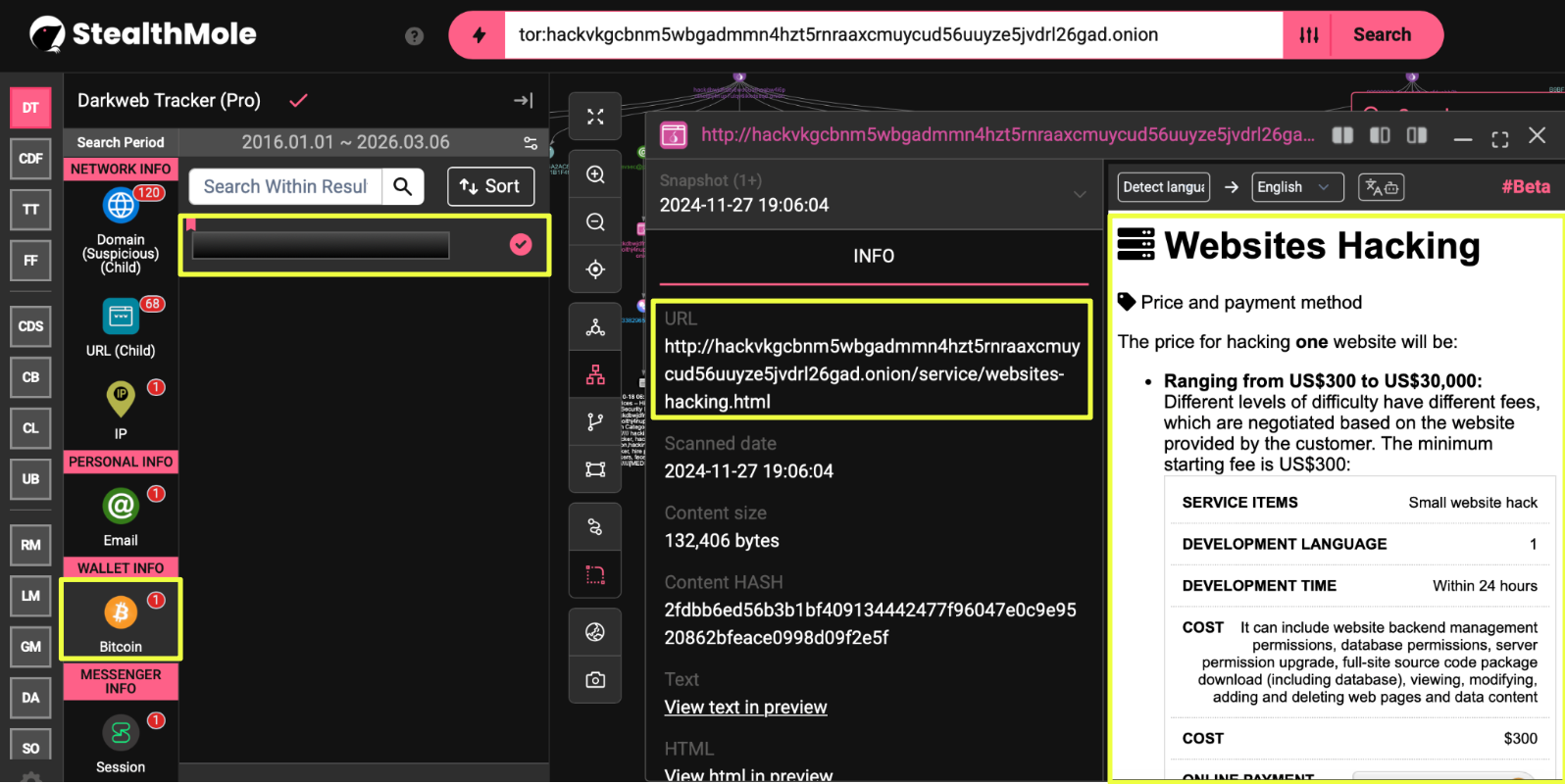 |
The wallet appeared on a service page describing customized hacking operations, where clients were instructed to contact the operators, receive a quote, and then provide a deposit before work would begin. Although the wallet did not show any confirmed transactions during the analysis, its presence indicated that the service accepted cryptocurrency payments for its operations.
In addition to the hidden service, the site also referenced a surface web domain:
- https://shadowhacker.**/
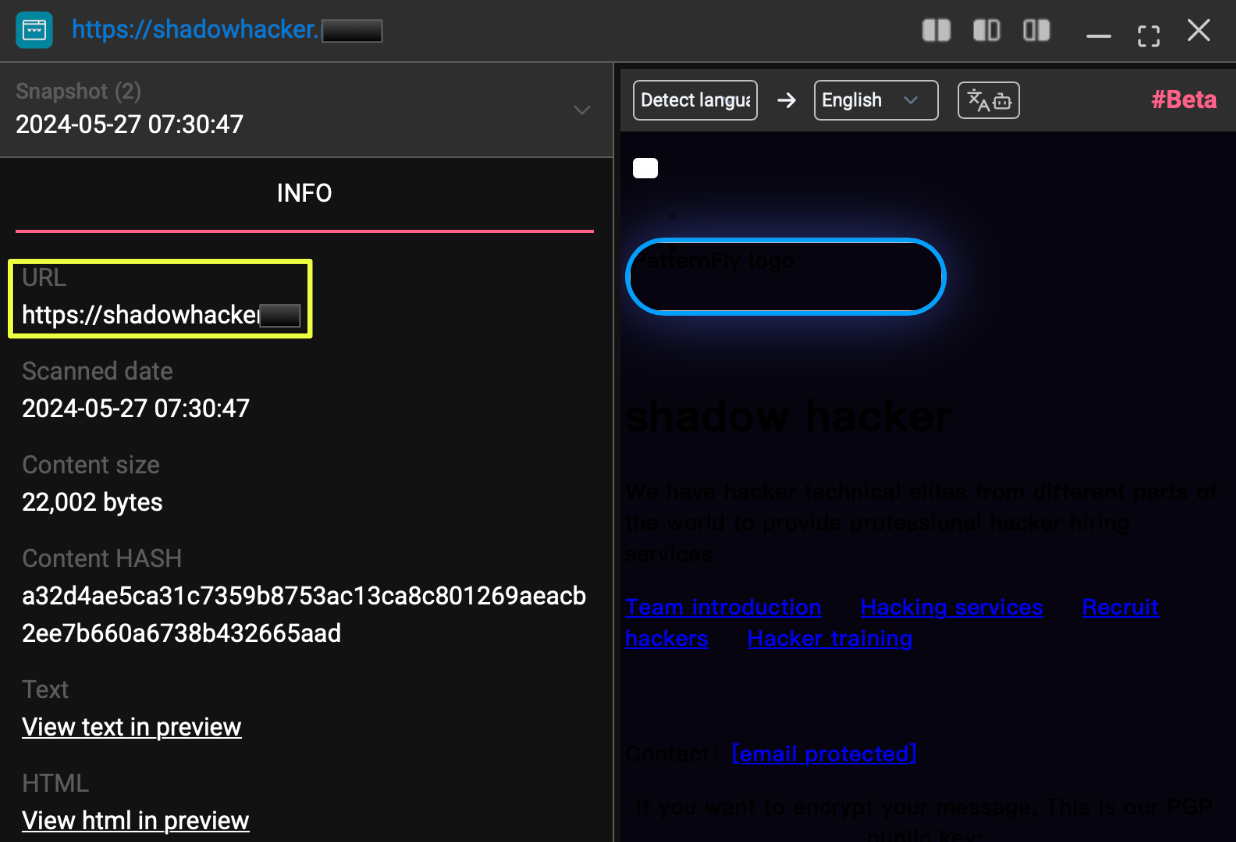 |
The discovery of a separate brand advertising nearly identical services raised an important question: whether “Shadow Hacker” represented a completely different group offering similar services, or whether it was connected to the same infrastructure previously observed in the “Anonymous Hackers” platform.
To answer this question, the investigation continued by pivoting on the newly discovered artifacts, including the email addresses, PGP keys, and associated domains linked to the Shadow Hacker infrastructure.
Mapping Additional Shadow Hacker Artifacts
Following the discovery of the Shadow Hacker service, the investigation shifted toward identifying additional infrastructure connected to this brand. Using StealthMole, pivots were performed on the domains, contact emails, and identifiers discovered on the Shadow Hacker pages. These searches quickly revealed that the Shadow Hacker ecosystem extended across multiple Tor hidden services.
One of the domains identified during this phase was:
- shadowmpqfj37rd3zlaakurssypadpyh52siaeqkt5vmi423xuj4xgid.onion
This hidden service hosted an “About” or introduction page that presented the individuals behind the operation. The page listed several hackers along with brief descriptions of their alleged specialties, including areas such as website exploitation, database extraction, social media account compromise, and network intrusion.
The site also exposed several additional contact channels associated with the Shadow Hacker platform. These included the following email addresses:
- shadow*****e@proton.me
- shdw*******r@proton.me
- shadow***team@proton.me
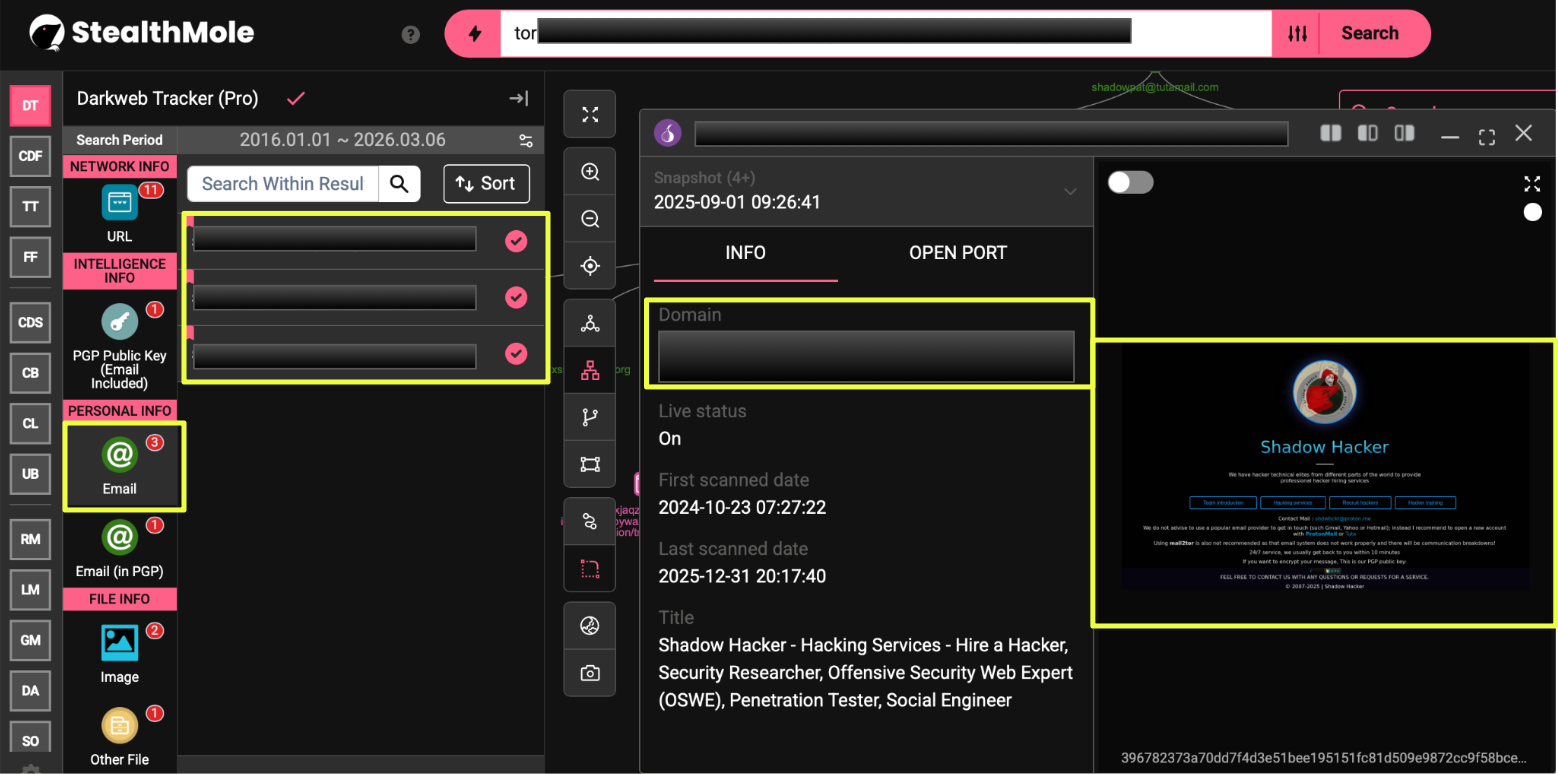 |
Alongside these contact details, the site referenced another PGP key used for encrypted communication:
- 242EC286F453F97C362FF1388B2F73CF1BEA8AA3
During the same stage of analysis, additional hidden services with similar naming patterns were identified. These included domains beginning with prefixes such as “shadow” or numeric strings like “222222.” Although many of these domains were inactive at the time of analysis, StealthMole’s historical data indicated that they had previously hosted pages offering the same categories of hacking services.
- shadowjjtyffuogtmpu3m3r66oiezh4ejahmyj5wojjeefn4gjqfdkqd.onion
- 2222222gdfw2ycyg5agpsnxcc6juuq5y2ozrtjnormjjbj5wy6hpsiqd.onion
- shadow45g2t4suurxnuwn2eutpfwoeq3xlvcgwnimevj2oqfonuehzqd.onion
- shadhy5mlcyyzso2cijxl5nb6kf5fxwgynoghw3waymvsuww22jqkzyd.onion
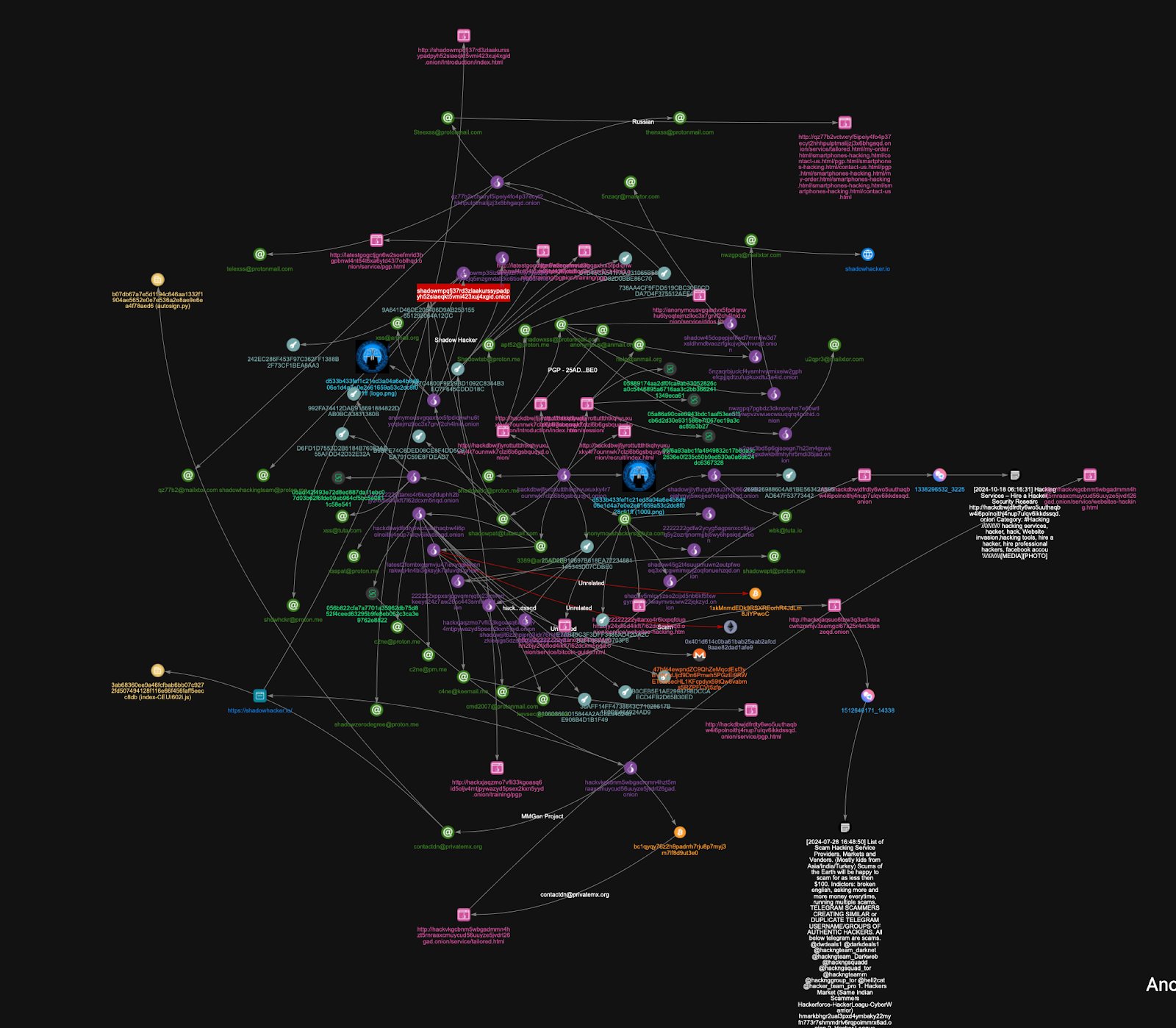 |
The discovery of multiple domains, rotating contact emails, and additional cryptographic identifiers suggested that the Shadow Hacker infrastructure was not limited to a single hidden service. Instead, it appeared to consist of several interconnected Tor domains that were periodically replaced or rotated while continuing to advertise similar hacking services.
Tracing Links Between Anonymous Hackers and Shadow Hacker Services
As additional Shadow Hacker domains and contact artifacts were uncovered, the investigation began to reveal clear overlaps with the infrastructure originally associated with the Anonymous Hackers platform. Several identifiers discovered during earlier pivots appeared again while exploring Shadow Hacker domains, suggesting that the two services might not be entirely separate operations.
One of the key artifacts connecting these platforms was the email address shado****t@tutamail.com, which led to another hidden service:
- anonymousvgqaxtvx5fpdiqnwhu6tyoqtejmzlloc3x7grvf2ch4lnid.onion
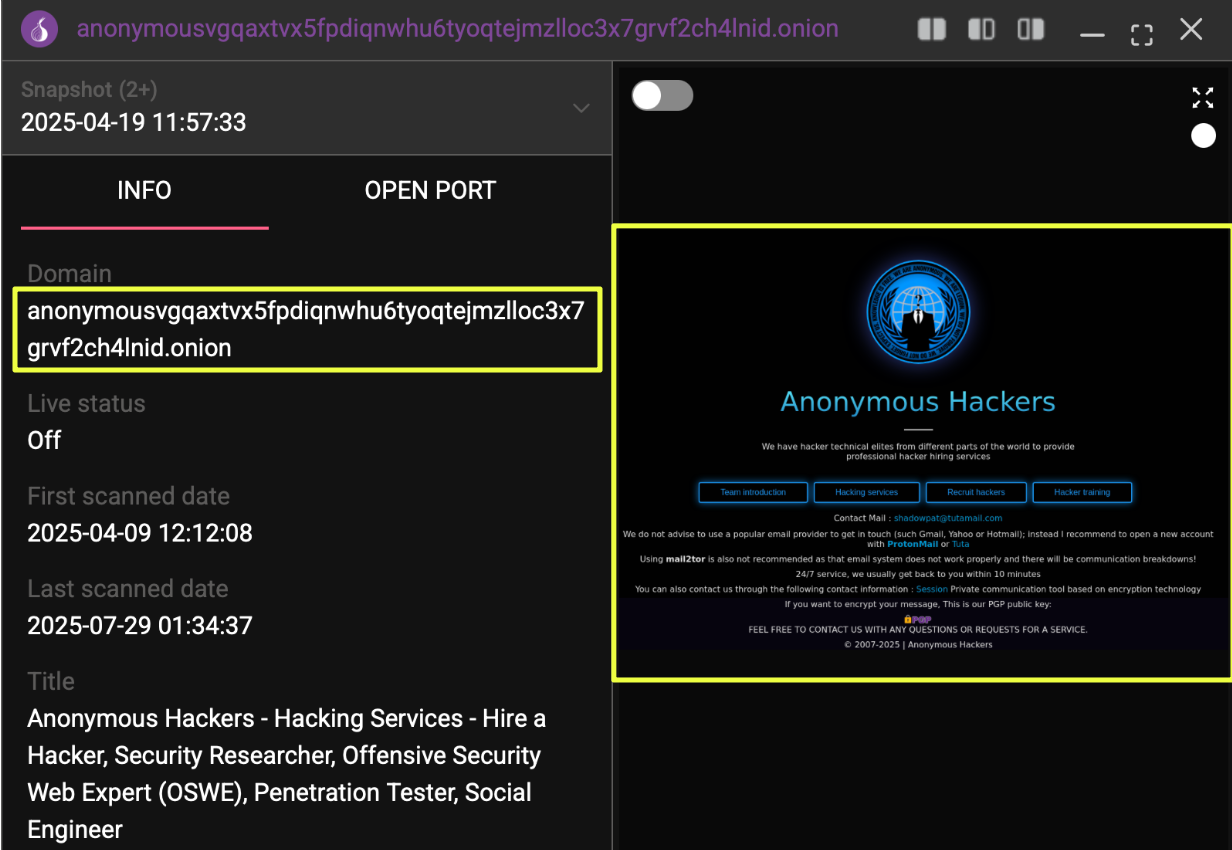 |
This domain hosted pages advertising hacking services similar to those previously observed. The site included service listings such as DDoS attacks and displayed pricing structures comparable to those used by the Anonymous Hackers platform.
Further examination of this domain revealed additional contact identifiers. Among them was the email address:
- x***8@anmail.org
The same domain also referenced another PGP fingerprint associated with encrypted communication:
- 9A64*******************************CC
Additional pivots during this stage surfaced two Shadow Hacker domains that followed similar naming patterns:
- shadow***********************************************gid.onion
- shadow************************************************ad.onion
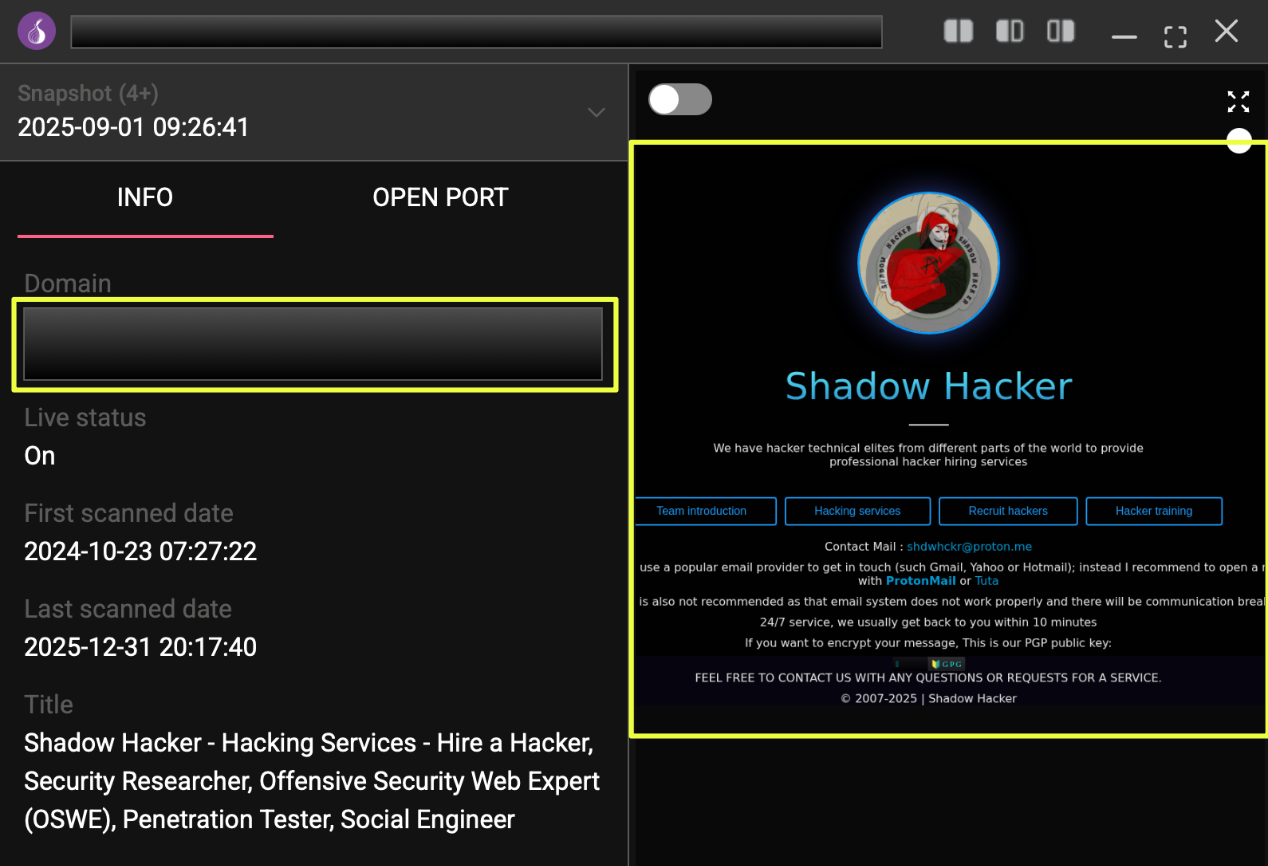 |
While these sites carried Shadow Hacker branding, their layout, service descriptions, and navigation structure closely resembled the Anonymous Hackers platform. Both sets of sites promoted comparable hacking services and relied on similar communication channels, including ProtonMail addresses and PGP encryption.
These overlaps indicated that the infrastructure behind the two brands was likely interconnected. Rather than operating as entirely independent groups, the Anonymous Hackers and Shadow Hacker services appeared to share elements of their operational setup, including domains, contact channels, and cryptographic identifiers.
Operational Patterns Across the Infrastructure
As more domains, emails, and identifiers were uncovered, several consistent patterns began to emerge across the investigated platforms. Although the sites appeared under different names and domains, many of their operational characteristics remained remarkably similar.
One of the most noticeable patterns involved the structure of the Tor domains themselves. Many of the discovered domains followed recognizable prefixes such as “shadow” or strings beginning with repeated numbers like “222222.”While the remainder of each domain consisted of randomized characters typical of Tor v3 addresses, the repeated prefixes suggested that the domains were intentionally generated or selected using similar naming conventions.
Another consistent element was the use of specific email providers for communication with potential clients. Across the different sites, contact addresses frequently relied on services such as ProtonMail, Tuta Mail, and temporary or anonymous email providers like Mailxtor. These addresses were often rotated across different domains, while maintaining recognizable naming patterns such as “shadow,” “xss,” or similar identifiers.
The investigation also revealed the use of multiple PGP keys for encrypted communication. Rather than relying on a single key, the sites displayed several different PGP fingerprints across their various domains. This approach may allow operators to compartmentalize communication channels or replace identifiers if a particular site becomes inactive.
Despite the changes in domains, emails, and cryptographic identifiers, the structure of the websites themselves remained largely consistent. Pages advertising hacking services often followed the same layout, with similar navigation menus, service categories, and pricing structures. Services such as website hacking, DDoS attacks, social media account compromise, and data extraction appeared repeatedly across the different domains.
In some cases, the same service descriptions and pricing models were presented on multiple sites, even when the platforms operated under different branding such as Anonymous Hackers or Shadow Hacker. This consistency suggested that the sites may have been built using the same template or maintained within a shared operational environment.
Another notable feature observed during the investigation was the presence of session-based communication pages, where users were provided with session identifiers or encrypted messaging options to contact the operators. These communication methods appeared across several domains and were likely intended to provide private channels for negotiating services with potential clients.
Overall, these recurring patterns indicated that the various domains and platforms were not simply isolated hacking services appearing independently on the dark web. Instead, the infrastructure displayed several shared characteristics that suggested a coordinated or closely related operational structure.
Conclusion
The investigation began with the discovery of a single Tor website advertising hacking services under the name Anonymous Hackers. Through successive pivots in StealthMole, additional hidden services, contact emails, and cryptographic identifiers were uncovered, revealing a broader infrastructure operating across multiple Tor domains.
During the analysis, several platforms advertising hacking services were identified under different branding, most notably Anonymous Hackers and Shadow Hacker. Although these sites presented themselves as separate services, they displayed overlapping operational elements, including shared contact patterns, similar communication channels, and closely matching website structures.
The presence of multiple domains, rotating contact emails, and several PGP keys suggests that the operators behind these services maintain a flexible infrastructure capable of shifting domains and identifiers while continuing to advertise similar hacking services. This approach allows the platforms to maintain operational continuity even as individual domains become inactive.
Editorial Note
Investigations involving dark web infrastructure rarely provide definitive attribution, as operators frequently rotate domains, communication channels, and identifiers to obscure their activities. This case highlights how pivoting across artifacts can reveal relationships between platforms that initially appear unrelated. Tools like StealthMole play an important role in navigating these complex environments, enabling analysts to uncover patterns and connections that might otherwise remain hidden.
To access the unmasked report or full details, please reach out to us separately.
Contact us: support@stealthmole.com
Labels: Featured, Hacktivist Group
.svg)
.svg)
.svg)