Handala’s Digital Battlefield: Uncovering the Infrastructure of an Anti-Israel Hacktivist Campaign
 |
In recent years, geopolitical tensions have increasingly spilled into cyberspace, giving rise to a wave of hacktivist groups that frame cyberattacks as acts of political resistance. Among these actors, Handala has emerged as a particularly visible presence within the pro-Palestinian cyber ecosystem. Named after the iconic Palestinian cartoon character created by Naji al-Ali, the group draws heavily on the symbolism associated with the figure: a barefoot child who stands with his back turned, representing resistance, displacement, and a refusal to accept injustice. By adopting this name and imagery, the group positions its cyber activities as part of a broader ideological struggle rather than purely criminal operations.
Handala began appearing in online spaces around late 2023, as the Israel–Hamas conflict intensified and hacktivist activity surged across multiple regions. Like many politically motivated cyber groups, its messaging blends propaganda, political statements, and claims of cyber intrusions. Over time, the group has targeted a range of Israeli institutions and organizations, frequently publishing announcements or alleged data leaks across forums, messaging platforms, and dedicated leak sites. These activities have gradually drawn attention within both cybersecurity circles and online hacktivist communities.
Despite its growing visibility, much about Handala remains unclear. The group operates under shifting online identities, frequently moving between platforms and channels while maintaining a steady stream of announcements and leak claims. This fluid online presence makes it difficult to understand how the group organizes itself, where it communicates, and how its operations are distributed across the internet.
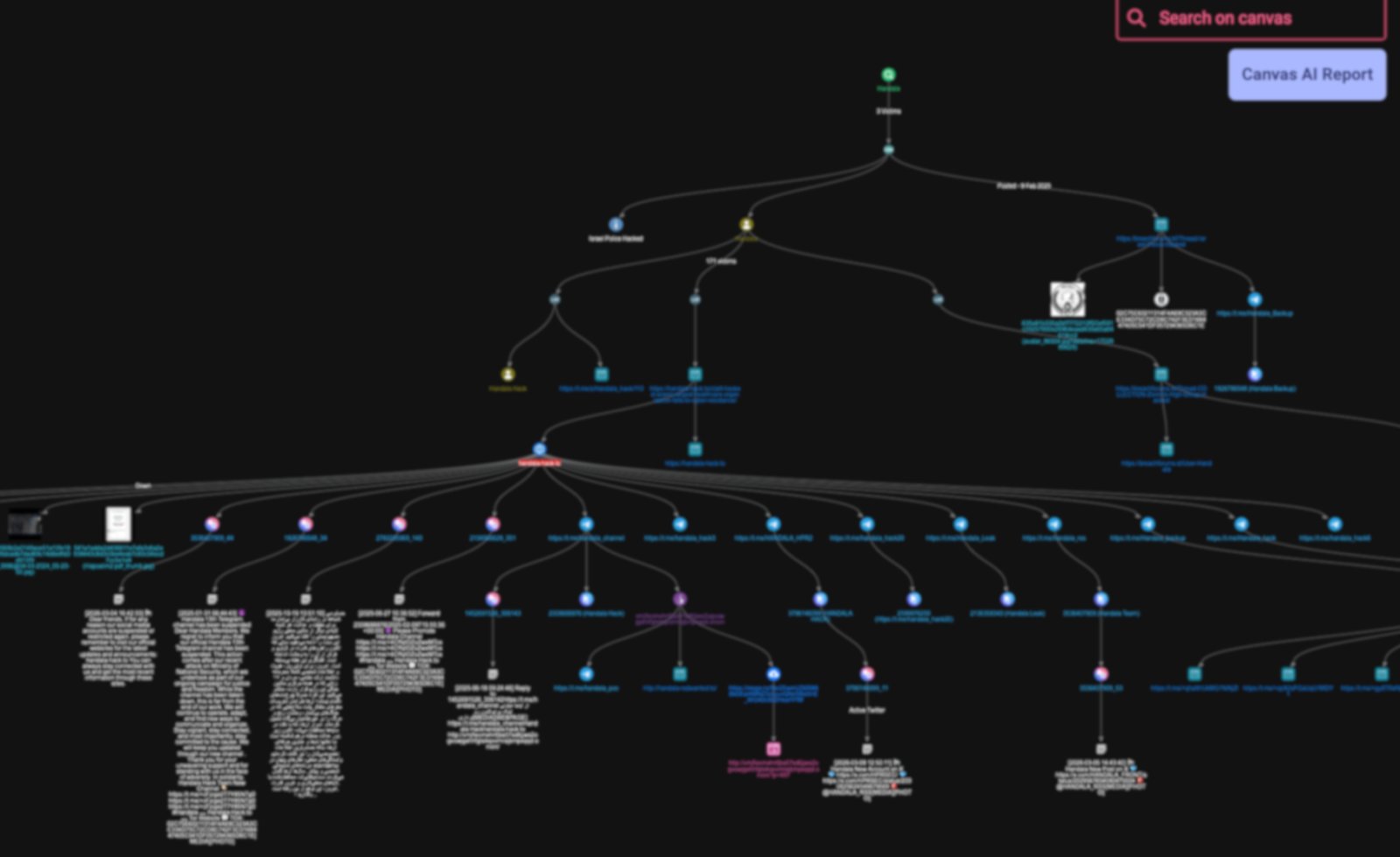
This investigation began with a simple question: how does Handala sustain its cyber campaign online? By tracing the group’s digital footprint across forums, messaging platforms, and dark web infrastructure, the analysis gradually reveals a broader network of channels, domains, and communication pathways that support its activities. What initially appeared to be isolated leak posts ultimately points to a far more interconnected ecosystem operating behind the scenes.
Incident Trigger and Initial Investigation
The investigation began with a keyword search for “Handala” within StealthMole’s Government Monitoring tool. This initial query surfaced several posts linked to the group that referenced alleged cyberattacks targeting Israeli government entities. Among the indexed results were three incidents published on BreachForums between 2024 and 2026, indicating that the group had previously used underground forums to publicize its activities.
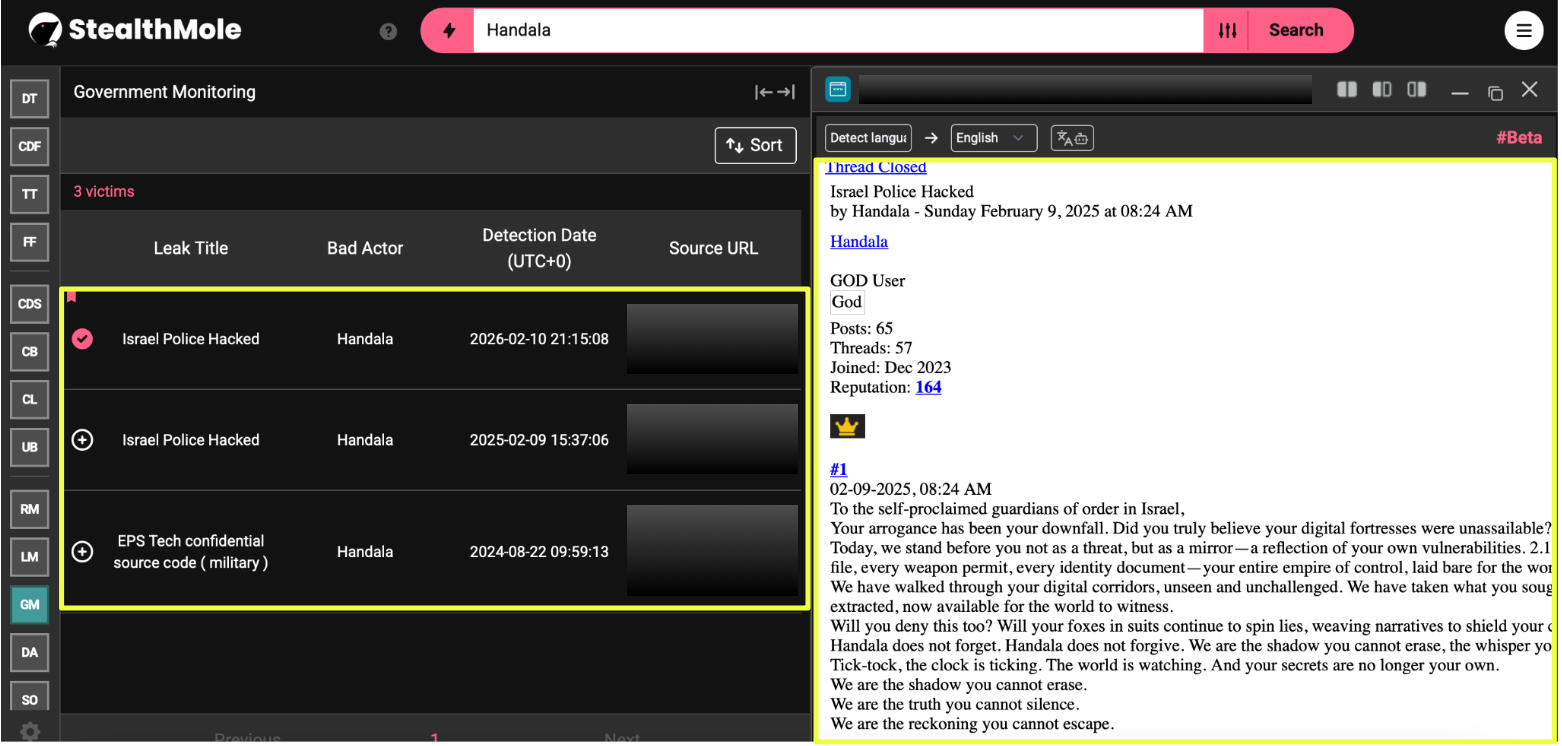 |
One of these threads, titled “Israel Police Hacked,” was particularly notable. Although it appeared in StealthMole monitoring results during 2026, the original forum post dated back to 9 February 2025, suggesting that the content had resurfaced through reposting or renewed attention within underground communities.
To determine whether these forum posts represented isolated claims or part of a broader pattern of activity, the investigation expanded to StealthMole’s Leaked Monitoring tool. This search revealed a much larger dataset associated with the group, identifying 176 potential victims linked to Handala-related leak announcements.
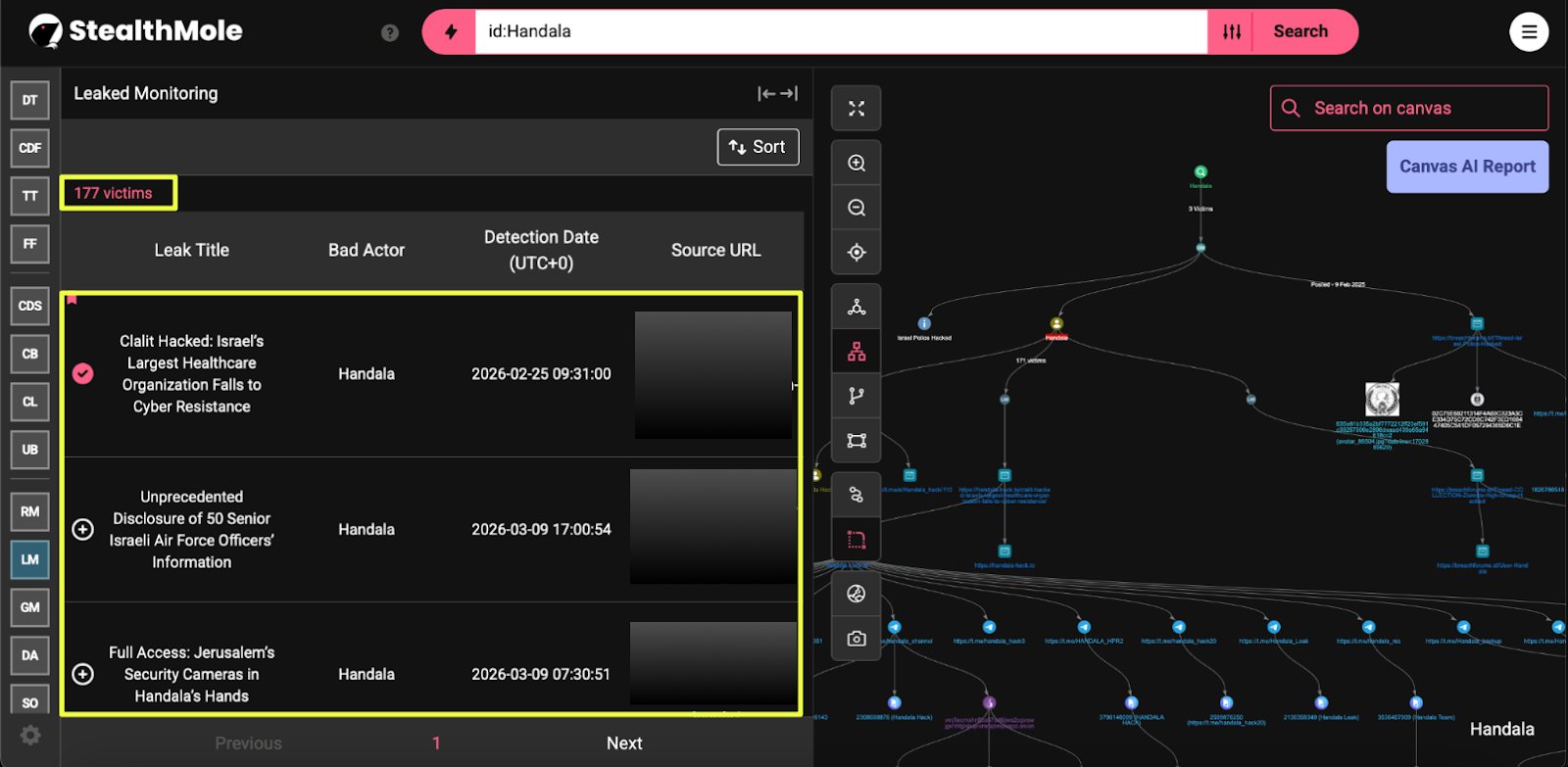 |
The results also showed a clear shift in how the group published its disclosures. Earlier posts were distributed primarily through underground forums and Telegram channels, but more recent entries pointed to a dedicated leak platform operated by the group itself.
Two key communication channels repeatedly appeared in connection with these announcements:
- https://t.me/s/Handala_hack
- https://t.me/Handala_Backup
 |
Among the leaked monitoring results, the most recent entry stood out as a significant development. Unlike earlier disclosures that relied on forums or messaging platforms, this post was hosted directly on the group’s own website.
- https://handala******.**/un********/
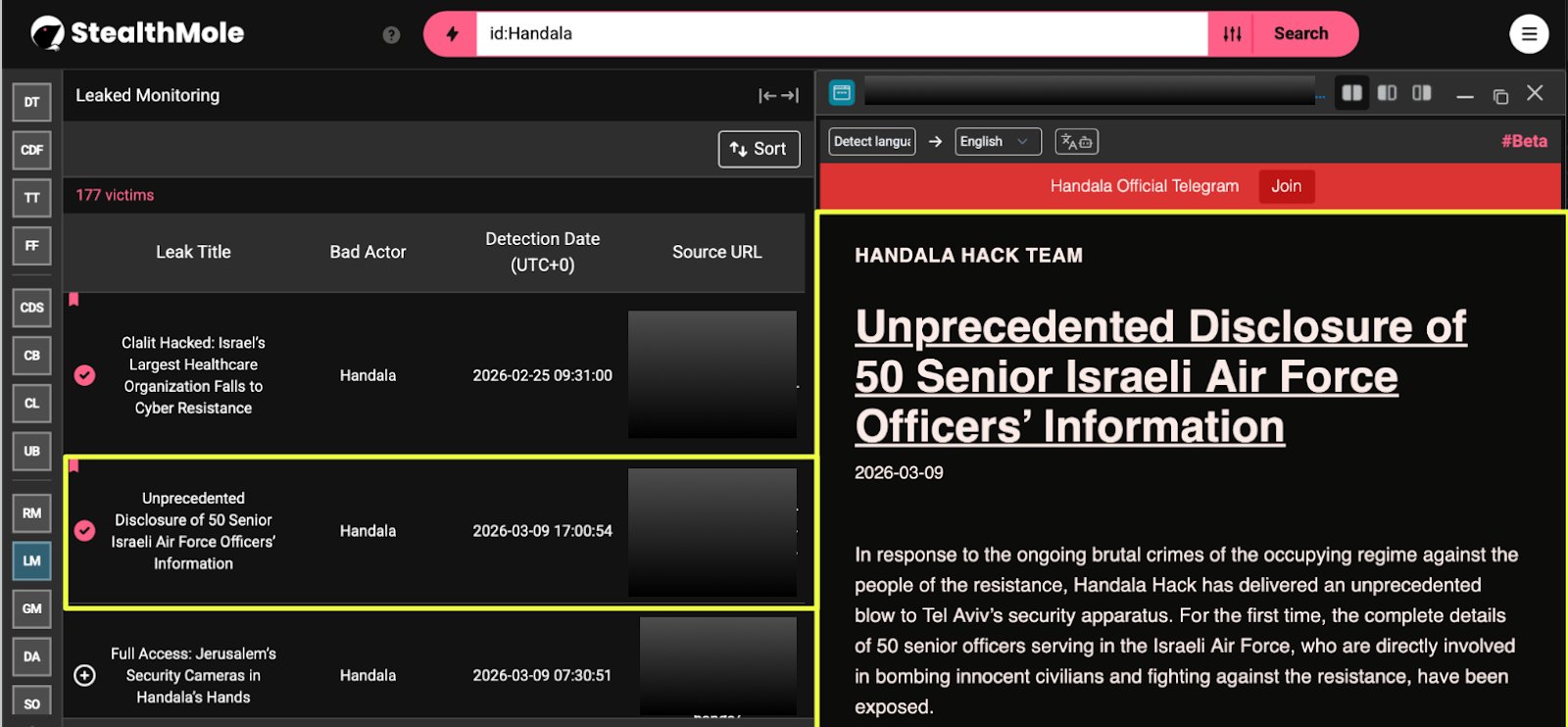 |
The page carried the title “Unprecedented Disclosure of 50 Senior Israeli Air Force Officers’ Information” and presented the announcement as a major data exposure linked to Israeli military personnel. Because this disclosure represented the latest activity attributed to the group and was hosted on infrastructure directly controlled by the actors, it became the primary focal point for further analysis.
With the source of the announcement identified, the investigation pivoted to the domain hosting the leak. By running the domain through additional StealthMole tools, including Dark Web Tracker and Telegram Tracker, the analysis began mapping the broader ecosystem connected to the group. What initially appeared to be a single leak announcement soon expanded into a much larger network of domains, messaging channels, and communication platforms supporting Handala’s online operations.
Expanding the Investigation: Mapping Handala’s Online Infrastructure
With the leak page identified, the investigation shifted toward understanding the infrastructure supporting Handala’s operations. The domain hosting the disclosure was used as the first pivot point, allowing StealthMole tools to identify additional communication channels and online platforms connected to the group.
The domain handala*******.**, which hosted the March 2026 disclosure, appeared to function as a central hub for the group’s announcements and leak posts.
- https://handala**********.**
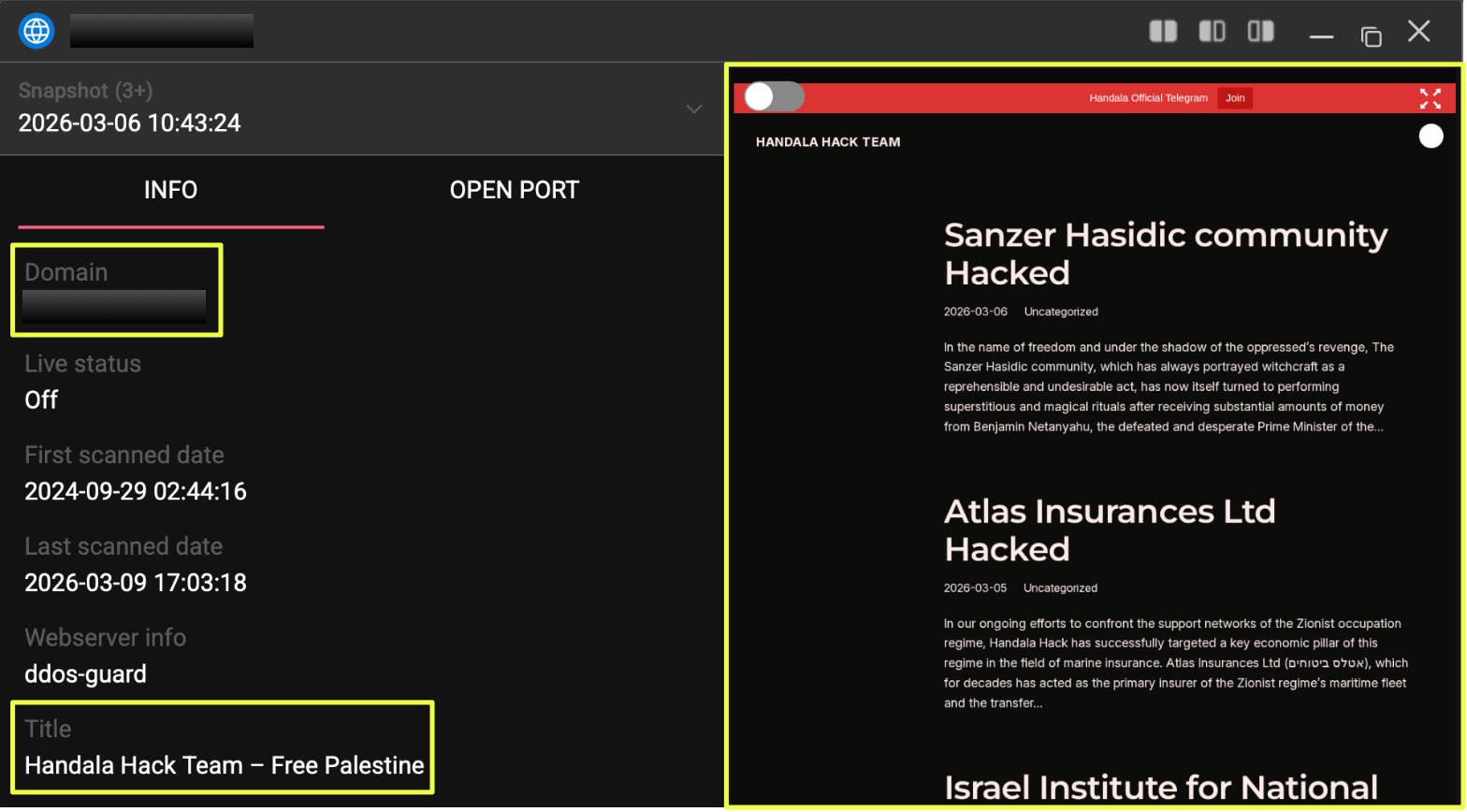 |
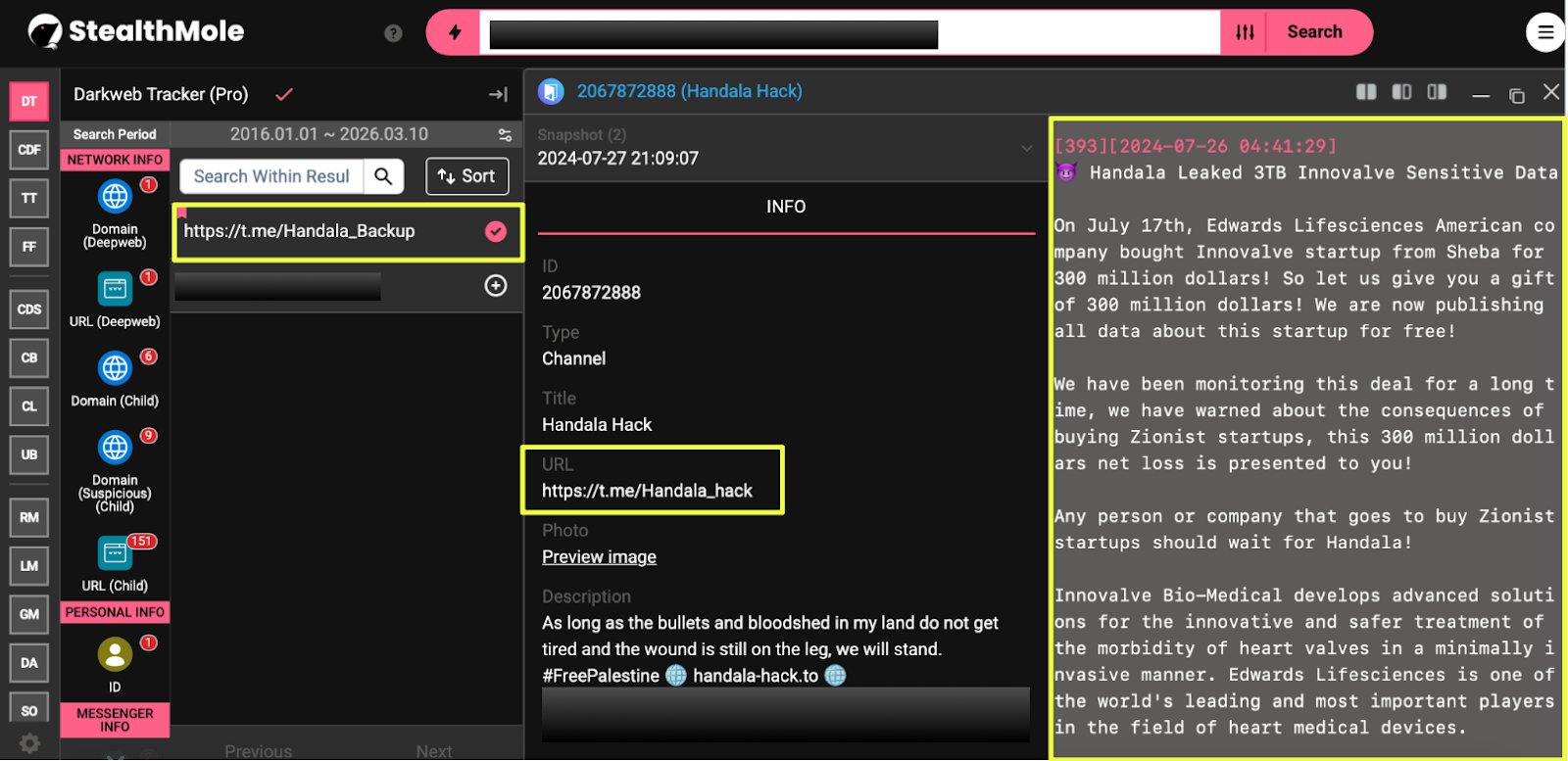
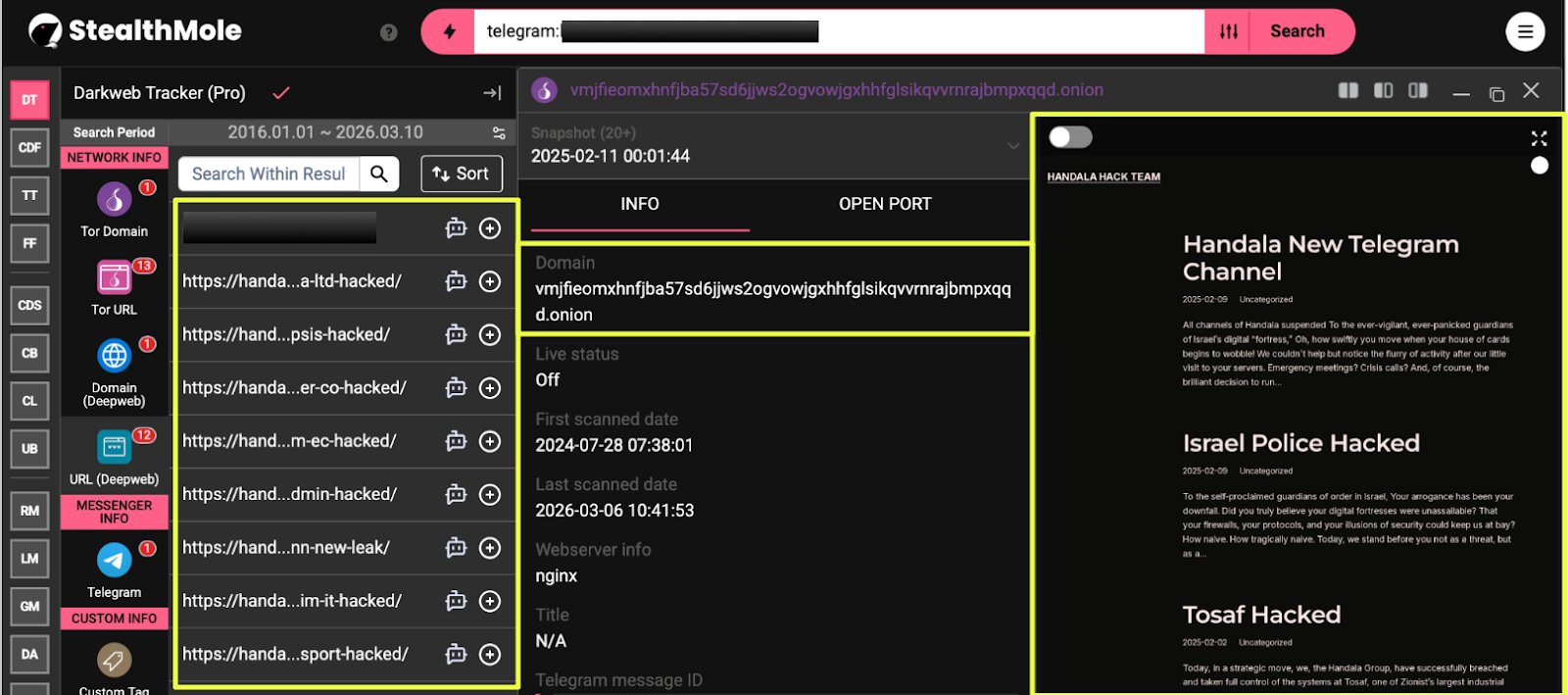
Running this domain through StealthMole’s Dark Web Tracker revealed multiple associated communication channels and identifiers linked to the group’s online presence.
One of the most significant findings was a network of Telegram channels connected to the Handala ecosystem. These channels appear to serve different roles, including announcements, backup communication channels, and distribution of leak-related content.
Telegram Channels Identified
- https://t.me/Handala_Leak
- https://t.me/handala_hack3
- https://t.me/handala_hack6
- https://t.me/Handala_backup
- https://t.me/handala_hack20
- https://t.me/handala_channel
- https://t.me/Handala_hack
- https://t.me/handala_rss
- https://t.me/HANDALA*****
 |
 |
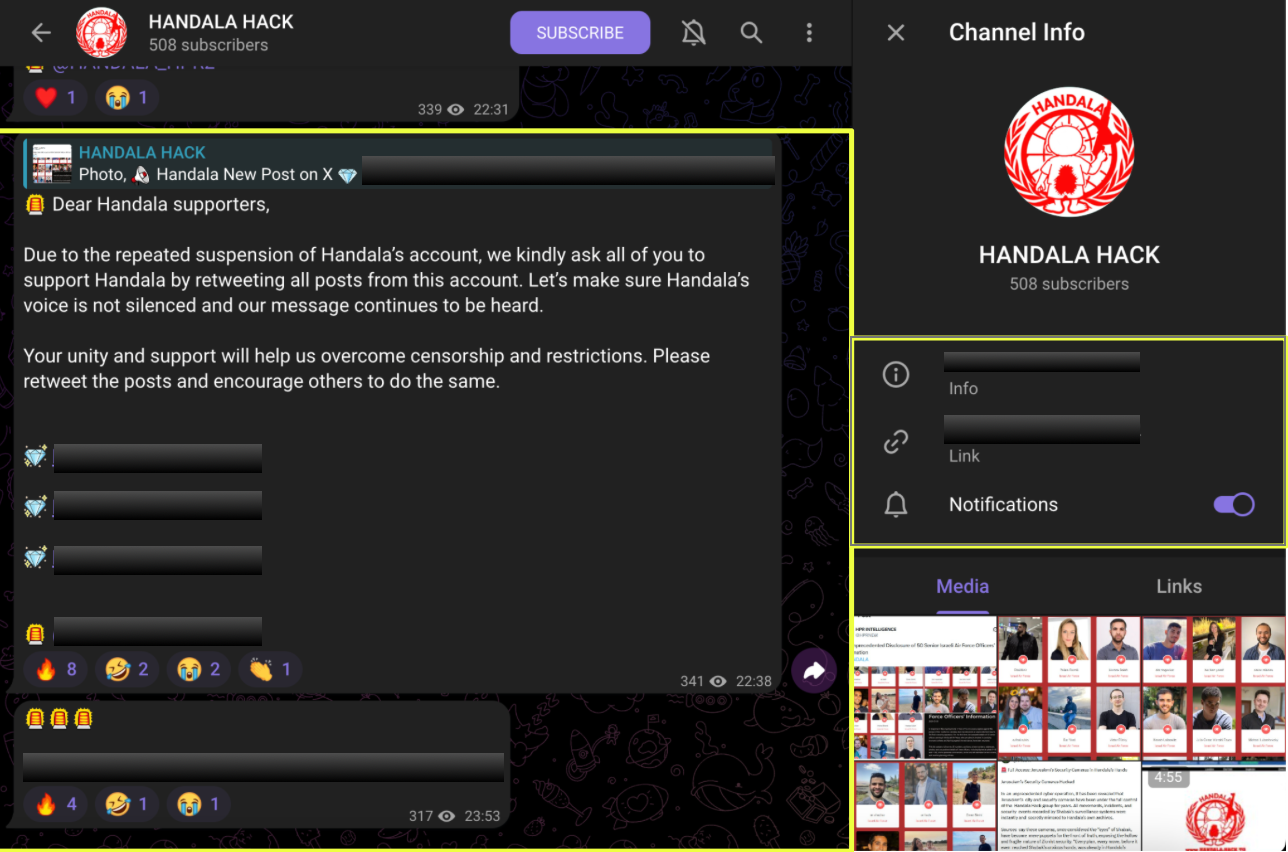
The presence of numerous channels suggests that the group relies heavily on Telegram as its primary communication platform. Hacktivist groups frequently maintain multiple channels to ensure continuity of operations, especially when primary accounts are suspended or removed by platform moderators.
In addition to Telegram channels, StealthMole also identified a Session messenger ID, indicating that the group provides alternative encrypted communication methods.
Session ID
- 05402*************************************************c929
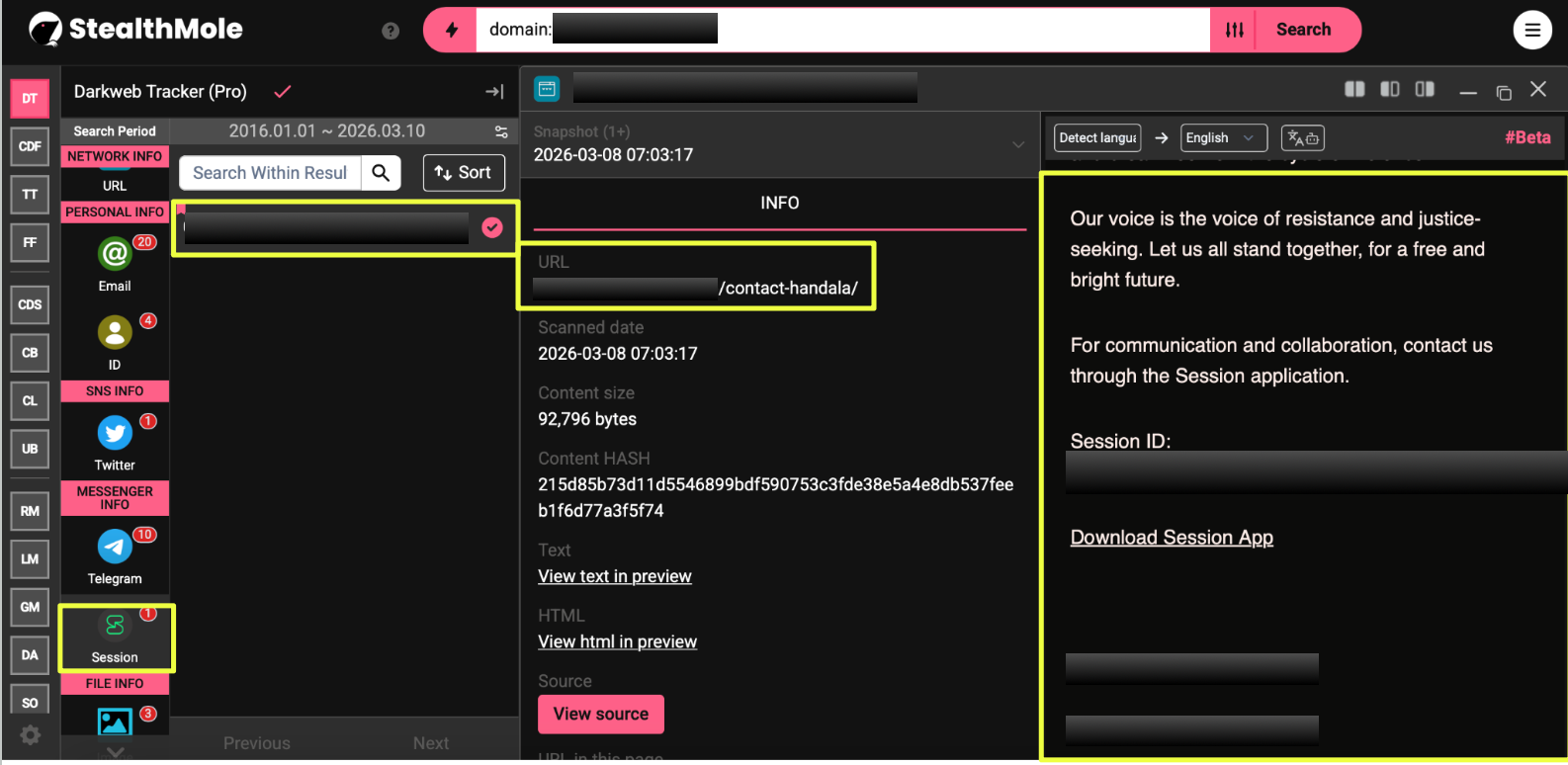 |
The discovery of this identifier suggests that the operators offer additional channels for private communication beyond public messaging platforms. Privacy-focused messaging services such as Session are often used by online communities seeking to maintain anonymity while coordinating activities or communicating with external contacts.
Together, these findings indicate that the leak website is only one component of a larger communication ecosystem. The group appears to rely on a distributed network of platforms, ranging from public messaging channels to encrypted communication identifiers, to promote its announcements and maintain contact with followers.
Telegram Activity and Platform Migration
Further analysis of the identified Telegram channels provided additional insight into how Handala manages its online presence and adapts to platform restrictions. Several messages within the channels referenced the suspension of social media accounts associated with the group, indicating repeated moderation actions against its online profiles.
For example, activity observed within the channel HANDALA_HPR2 referenced a Twitter account linked to the group:
- https://x.com/HPRSEC
At the time of investigation, this account had been suspended on 9 March 2026, illustrating the ongoing disruption faced by the group on mainstream social media platforms.
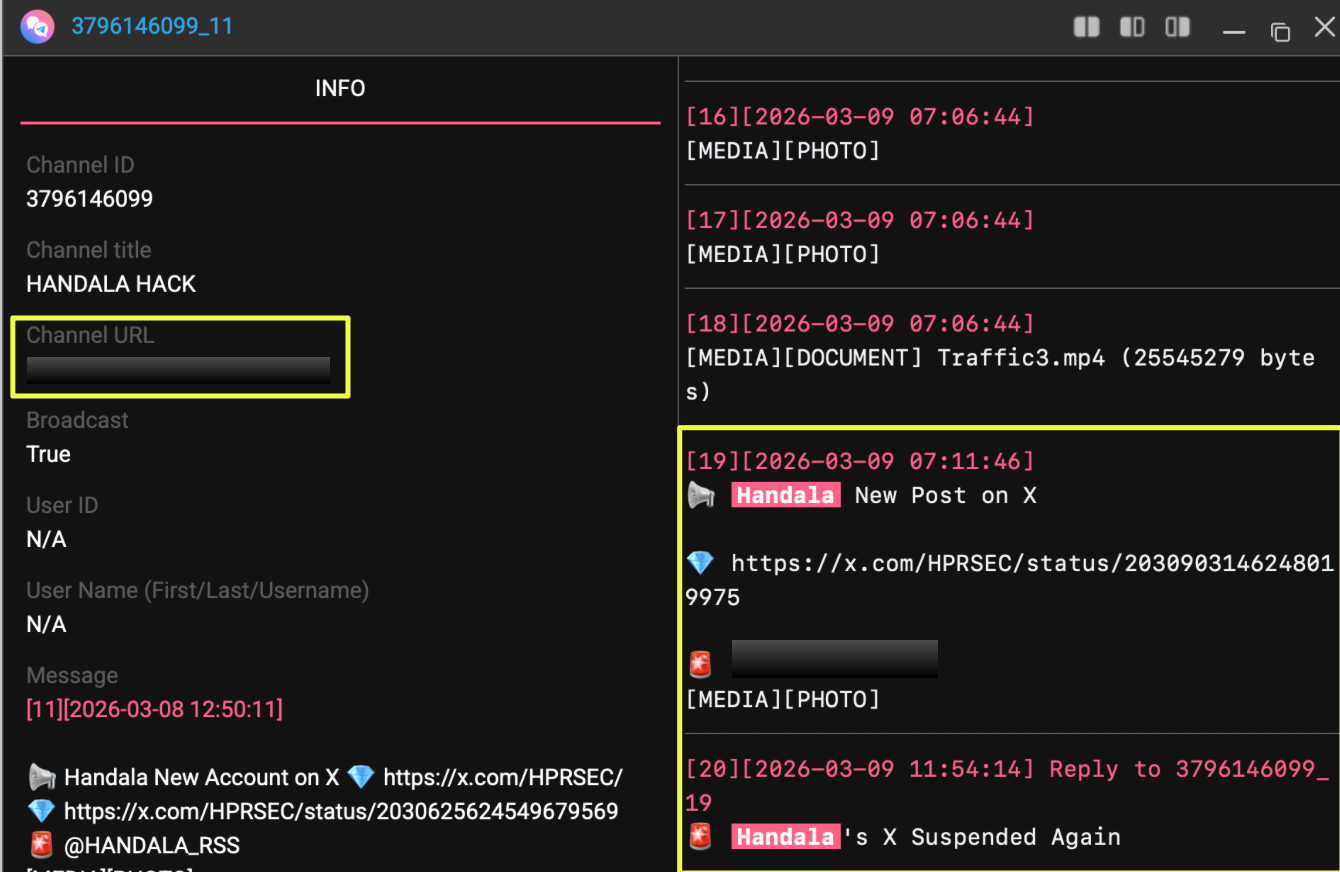 |
Additional evidence of these disruptions appeared within another Telegram channel:
Telegram Channel
- https://t.me/handala_rss
Messages in this channel reported that another account associated with the group had also been suspended earlier that week.
 |
Suspended Account
- https://x.com/HANDALA_FRONT
The suspension was reported on 6 March 2026, suggesting that multiple Handala-affiliated social media profiles had been removed in a short period of time. Earlier investigations had also identified the following account linked to the group’s activities:
Previously Identified Account
- https://twitter.com/handala_hack
The repeated suspension of these accounts appears to have contributed to the group’s increasing reliance on Telegram as its primary platform for announcements and communication.
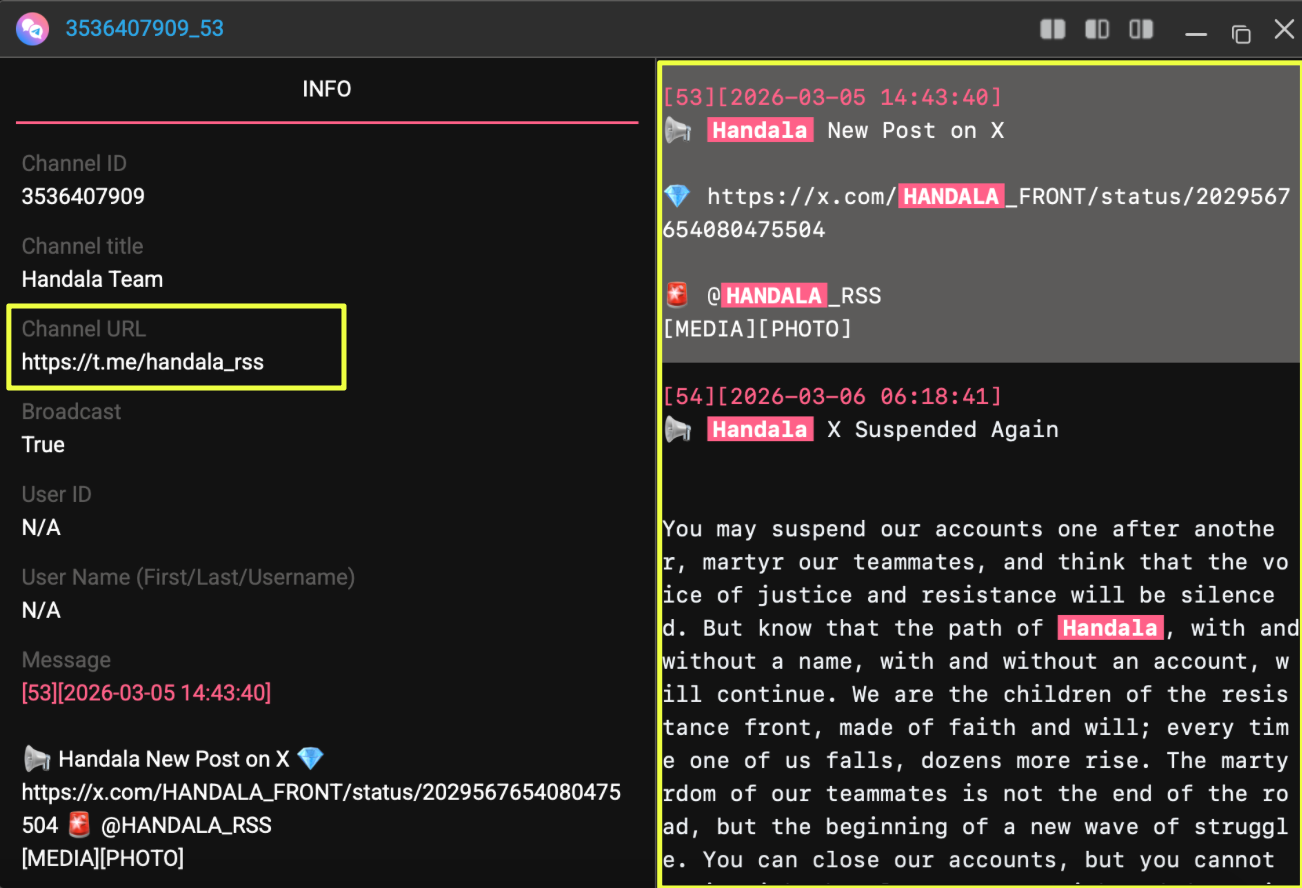
Further examination of the group’s backup Telegram channel also revealed a series of invite links pointing to additional private or temporary groups that had been used at various points over the past year.
Telegram Invite Links Identified
- https://t.me/+gy8TRxf4pVljMzI0 (February 2025)
- https://t.me/+cFjcge2T7Y85NTg0 (February 2025)
- https://t.me/+drbzBna3Bis1ZTM0 (January 2025)
- https://t.me/+qhaXhUkMG1NiNjZl (December 2024)
 |
These invite links suggest that the group periodically creates new channels or private groups, possibly in response to account suspensions or to maintain restricted communication spaces for specific audiences.
Overall, the findings highlight a pattern of platform migration, where Handala shifts its communication channels whenever accounts are suspended or restricted. Telegram appears to function as the central hub of this ecosystem, while other platforms are used intermittently for broader outreach before eventually being abandoned or removed.
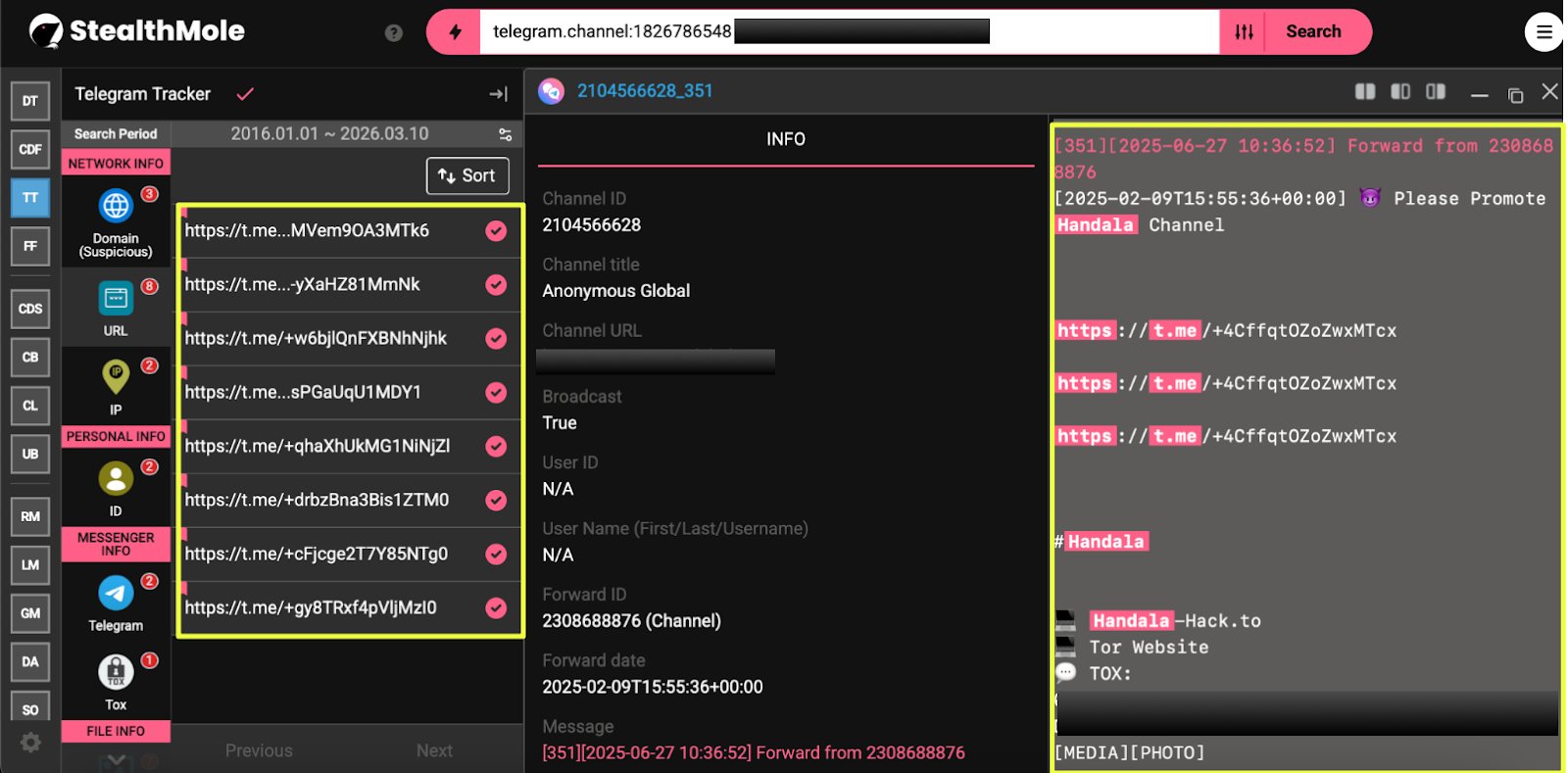
Dark Web and Supporting Infrastructure
As the investigation continued, further analysis of the Telegram channels uncovered additional infrastructure associated with Handala’s operations. One of the most notable discoveries emerged from the Telegram channel:
Telegram Channel
- https://t.me/handala_channel
Messages within this channel referenced an onion service associated with the group, indicating the presence of infrastructure hosted within the Tor network.
Onion Website
- http://vmjfieomxhnfjba57sd6jjws2ogvowjgxhhfglsikqvvrnrajbmpxqqd.onion/
 |
Running this address through StealthMole’s Dark Web Tracker revealed that the site appeared to function as another platform for publishing breach claims and distributing supporting materials. The page identified during the investigation included a post titled “Amos Spacecom Hacked,” which referenced an alleged compromise related to satellite communications infrastructure.
The page also contained links to files labeled as proof-of-concept (PoC) materials, suggesting that the group uses the onion site to distribute sample data or supporting evidence intended to validate its claims.
Further analysis of the onion infrastructure revealed additional resources connected to the group’s activity.
Additional Telegram Channel
- https://t.me/handala_poc
This channel appears to be associated with the distribution of proof-of-concept material or leaked data samples related to the group’s announcements.
In addition to messaging channels, the investigation also identified the use of external file-hosting platforms for distributing files linked to the group’s disclosures.
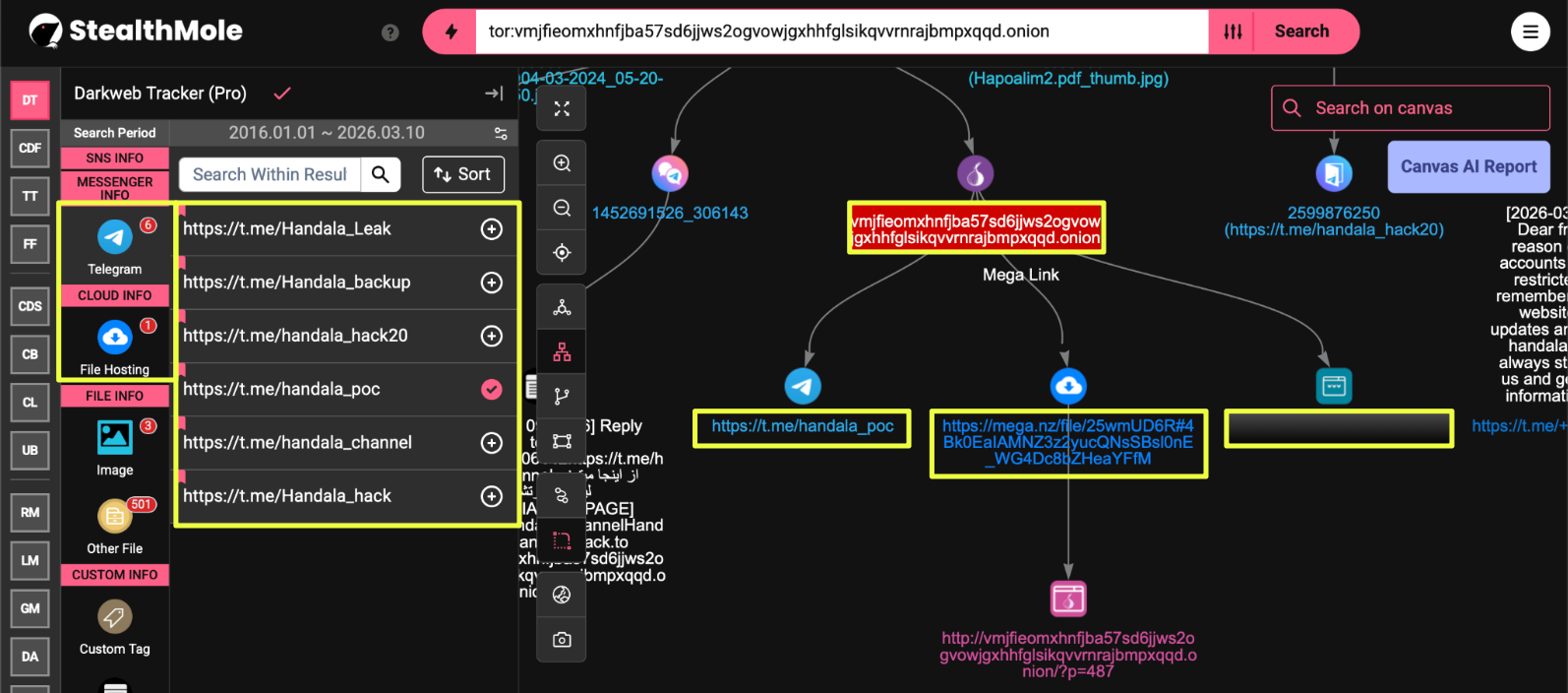 |
File Hosting Link
- https://mega.nz/file/25wmUD****************************fM
The presence of a Mega file link suggests that the group may use cloud-based storage services to distribute data samples or archive materials related to its leak announcements.
Another domain connected to the group’s ecosystem was also identified during the investigation.
Additional Surface Domain
- http://handala*******.***/
Although the exact function of this website could not be fully verified during the investigation, its appearance alongside other Handala-linked infrastructure suggests that it may serve as an additional platform for hosting announcements, propaganda, or related content.
These findings indicate that Handala’s online presence extends beyond messaging platforms and forums. Instead, the group appears to operate a layered infrastructure that includes surface web domains, Tor-hosted services, and external file-hosting platforms. This distributed approach allows the group to maintain the availability of its content even when individual platforms or accounts are suspended.
Conclusion
The investigation reveals that Handala’s activities are supported by a layered online ecosystem rather than a single platform or communication channel. Instead of relying on one outlet to publicize its operations, the group distributes its presence across multiple services, combining messaging platforms, dedicated leak websites, dark web infrastructure, and external file hosting services.
Among these platforms, Telegram appears to function as the central hub of the group’s communication network. The numerous channels identified during the investigation serve different roles, including public announcements, backup communication spaces, and distribution points for leak-related content. The existence of several backup channels and invite-only groups also indicates that the group anticipates disruptions and maintains alternative channels to ensure continuity of communication.
At the same time, Handala appears to rely on its own websites and Tor-hosted infrastructure to publish leak announcements. Hosting disclosures on actor-controlled platforms allows the group to retain control over its messaging while reducing dependence on third-party forums or social media services that may remove or restrict its content.
External file hosting platforms, such as Mega, appear to complement this infrastructure by enabling the distribution of sample datasets or supporting materials linked to leak claims. Separating file hosting from the main disclosure pages allows the group to share larger files while maintaining a lightweight publication platform for announcements.
Another notable pattern is the group’s repeated movement between platforms. Several social media accounts associated with Handala were found to have been suspended, indicating ongoing moderation actions on mainstream platforms. In response, the group’s communication appears to have shifted increasingly toward Telegram channels and dedicated websites, where the operators have greater control over their presence.
These findings suggest that Handala operates through a distributed digital ecosystem designed to maintain visibility and resilience. By spreading its activities across multiple platforms and infrastructure layers, the group is able to continue publishing announcements and promoting its campaigns even when individual accounts or channels are disrupted or removed.
Editorial Note
Investigations into cyber and dark web activities rarely produce absolute certainty. Hacktivist groups frequently operate under pseudonyms, rotate communication channels, and shift infrastructure over time, making definitive attribution and operational assessment inherently challenging. This case illustrates how StealthMole’s monitoring capabilities can help analysts navigate that uncertainty by tracing connections across forums, messaging platforms, and hidden services, gradually revealing the broader ecosystem that supports such operations.
To access the unmasked report or full details, please reach out to us separately.
Contact us: support@stealthmole.com
Labels: Featured, Hacktivist Group
.svg)
.svg)
.svg)