THE PERSEPHONE Ecosystem: Uncovering the Alliance Between VFVCT, RasCorp, and ClayRat
 |
Collaboration between cyber threat actors is not uncommon. Groups with different capabilities often form temporary alliances, combining technical expertise, infrastructure, and operational reach to strengthen their campaigns. In many cases, these collaborations operate through shared platforms or coordinated communication channels, allowing participants to contribute specialized roles while presenting a unified presence to the outside world. Such arrangements can make attribution more complex, as multiple actors may be operating within the same ecosystem rather than as isolated groups.
In early 2026, traces of a platform called “THE PERSEPHONE” began appearing across online channels associated with hacking and data leak activities. At first glance, the platform appeared to function as a website hosting various datasets and announcements. However, the way the site presented itself suggested that it might represent more than a single actor’s operation. References within the platform pointed toward multiple groups and hinted at a broader collaborative structure behind the scenes.
This raised an important question: was THE PERSEPHONE simply another leak site, or was it part of a coordinated ecosystem involving several actors working together? To answer this, the investigation focused on mapping the infrastructure, communications, and identities connected to the platform. What initially appeared to be a straightforward leak portal gradually revealed signs of a more structured collaboration, where different groups appeared to contribute distinct roles within the same operational environment.
Incident Trigger and Initial Investigation
The investigation into THE PERSEPHONE began when StealthMole’s Leaked Monitoring tool indexed several newly posted datasets associated with the name on 5 March 2026. The indexed entries pointed to a publicly accessible website hosting multiple files and announcements under the same banner. The platform was located at:
- https://thepersephone.*****.org/?i=1
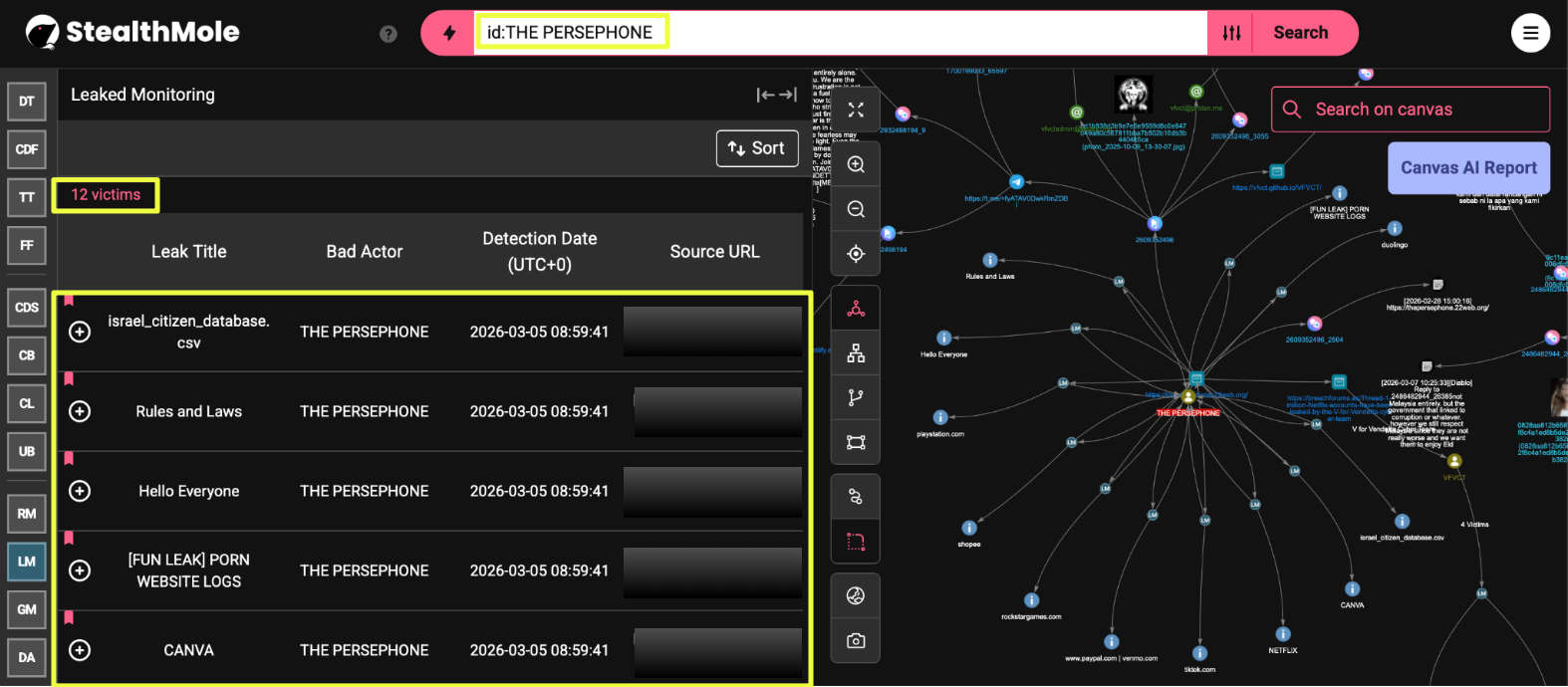 |
At first glance, the page appeared to function as a simple leak repository where datasets were organized and made available for download. Several entries were visible on the page, including files labeled “israel_citizen_database.csv”, “CANVA”, and “PORN WEBSITE LOGS.” The presence of multiple datasets suggested that the site was being used to publish and promote breach data in a structured manner.
A closer look at the website revealed that it introduced itself as a prototype platform named THE PERSEPHONE. In addition to listing leaked datasets, the site also contained introductory messages and operational guidelines, including statements outlining which types of organizations the operators claimed not to target. These elements resembled the structure commonly seen on leak portals used by cyber threat actors to showcase breaches and distribute stolen data.
Because the website appeared to be the central location where the datasets were being hosted, it became the starting point for further investigation. The domain https://thepersephone.******.org/ was subsequently analyzed using StealthMole’s tracking capabilities to determine whether the platform had been referenced elsewhere across underground forums or messaging channels.
This pivot quickly produced a relevant lead. A thread on BreachForums titled “1 million Netflix accounts have been leaked by the V for Vendetta cyber team” referenced the same domain and described it as “our website.” The thread was posted by the user VFVCT, who had joined the forum in March 2026. The mention of the Persephone domain within the forum post suggested that the leak platform might be connected to the group identifying itself as the V For Vendetta Cyber Team (VFVCT).
- https://breachforums.**/Thread-1-******V-for-Vendetta-cyber-team
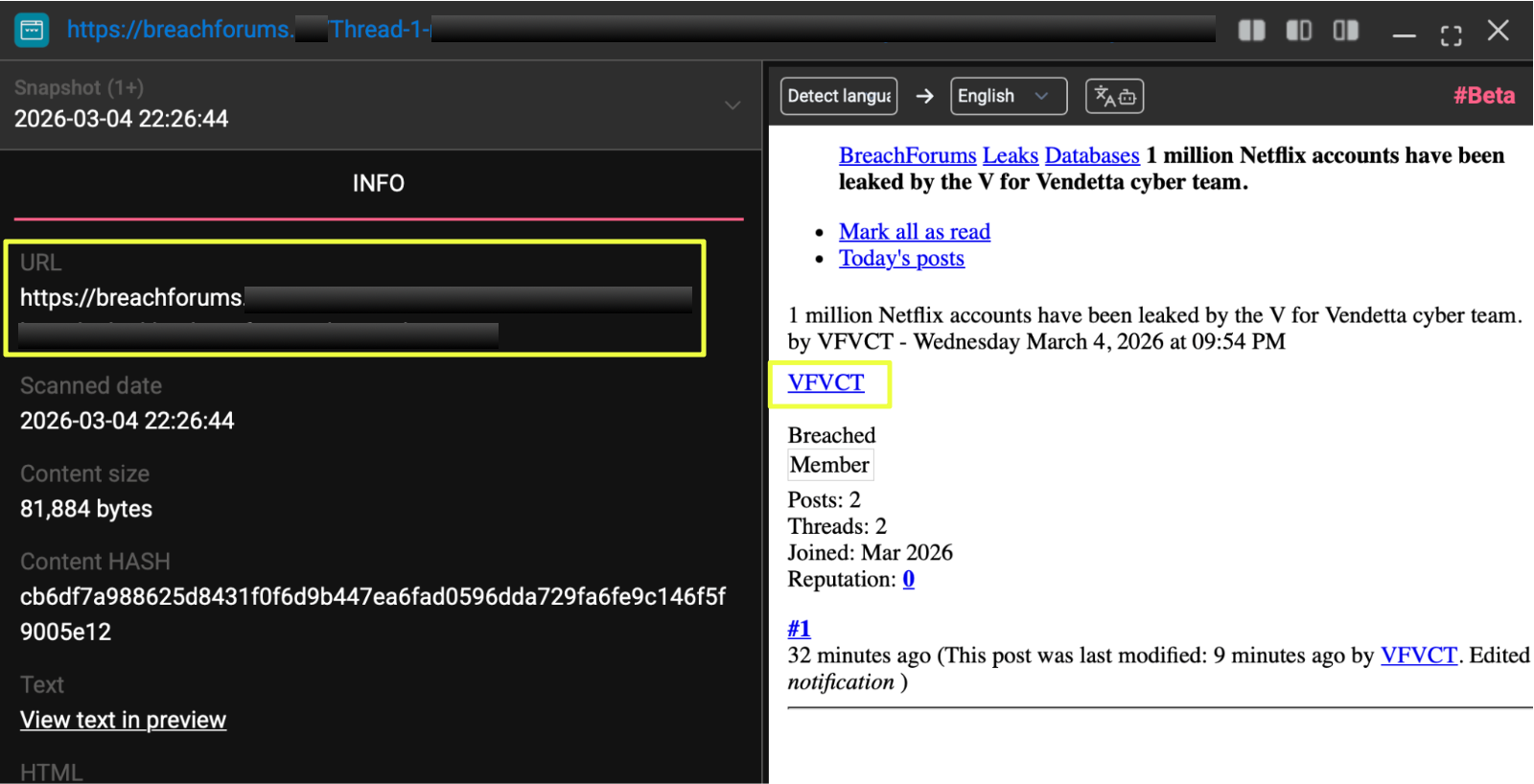 |
The appearance of the same website in both the indexed leak listings and the BreachForums post raised the possibility that the platform was being actively promoted by the actors responsible for the leaks. This discovery prompted further investigation into the infrastructure and communication channels linked to the Persephone site in order to identify the groups operating behind it.
Tracing the Communication Infrastructure
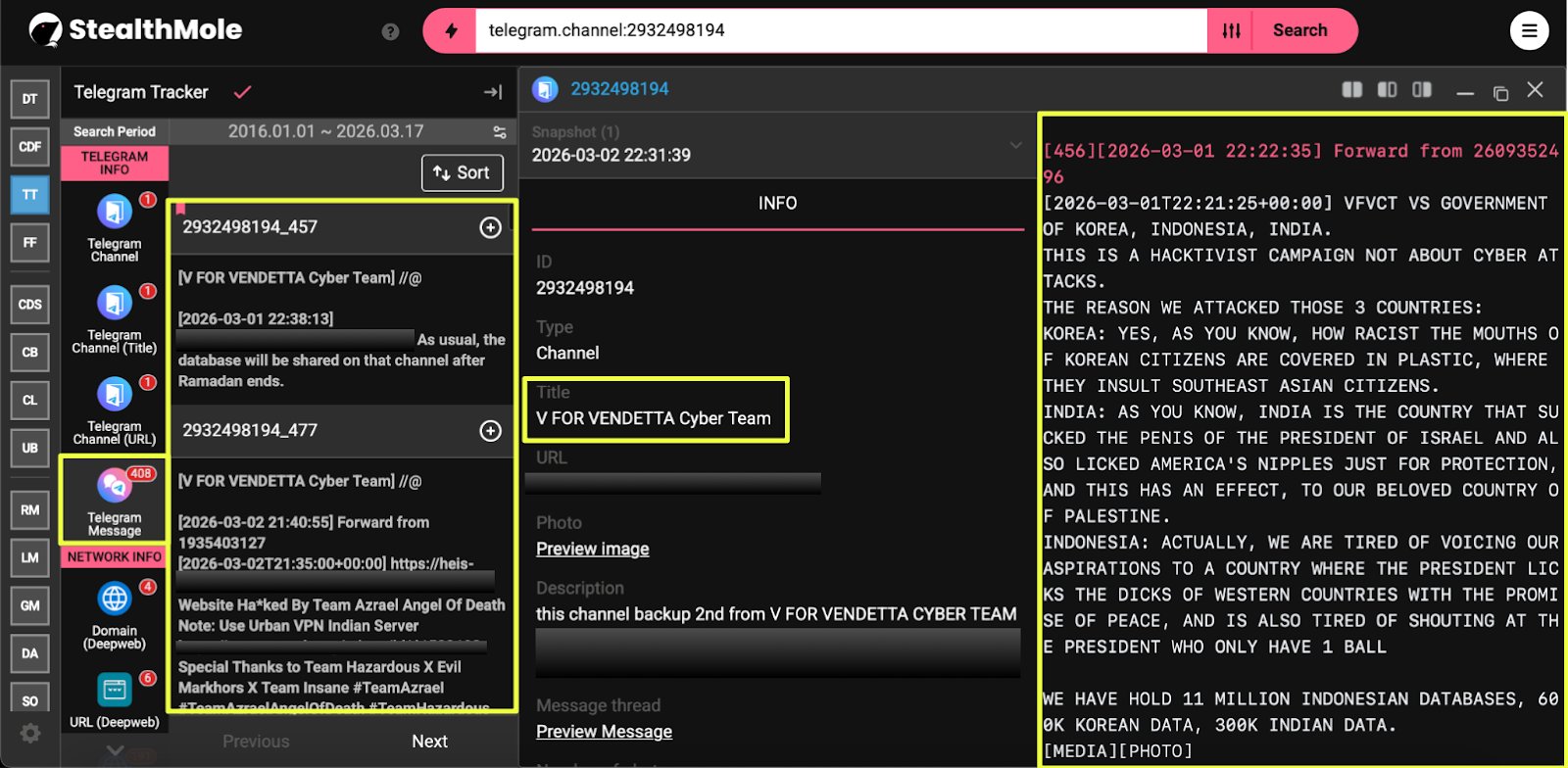
Following the discovery of the Persephone website and its reference within the BreachForums thread, the investigation shifted toward identifying communication channels where the platform might be promoted or discussed by the actors themselves. The domain https://thepersephone.******.org/ was therefore queried through StealthMole’s Telegram Tracker, which indexes Telegram messages and channel content for investigative analysis.
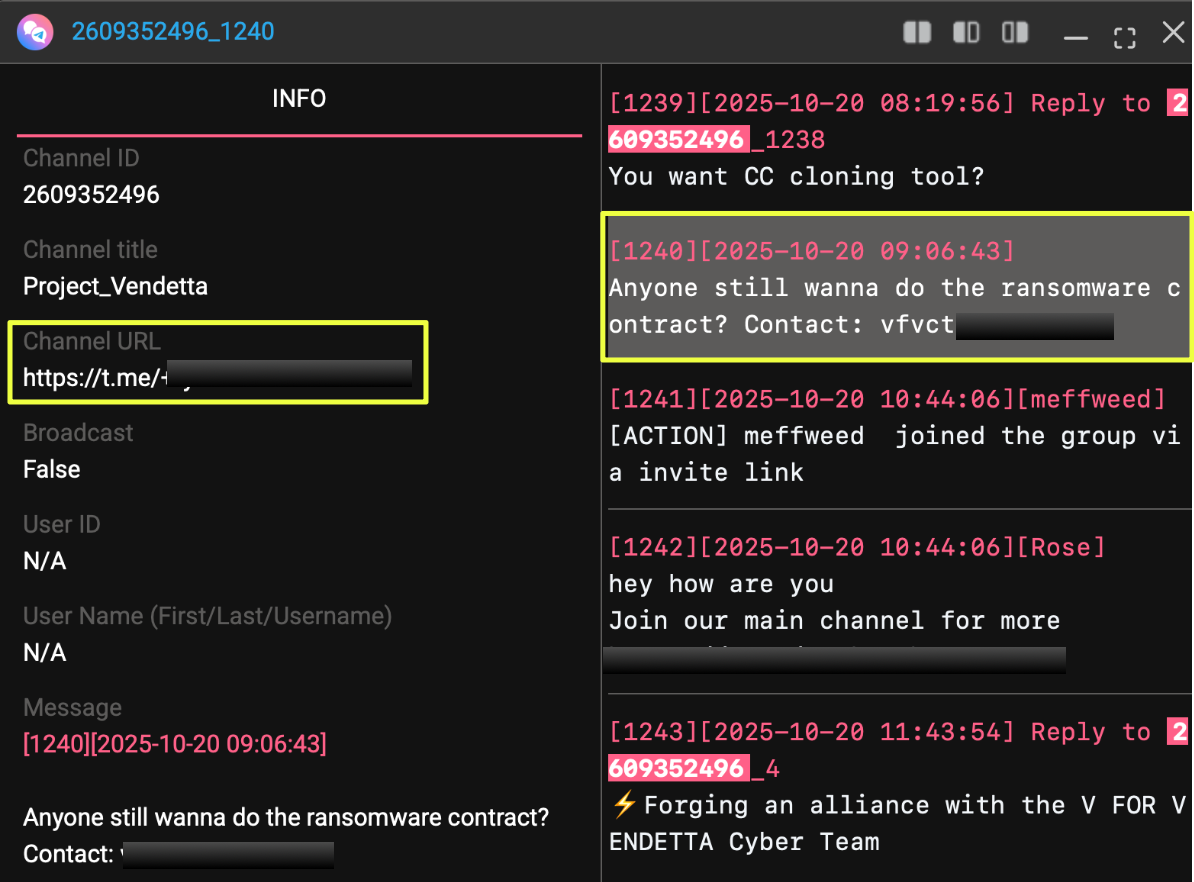
This pivot revealed a private Telegram group titled Project_Vendetta, accessible through the invitation link:
- https://t.me/+fyA*********Bl
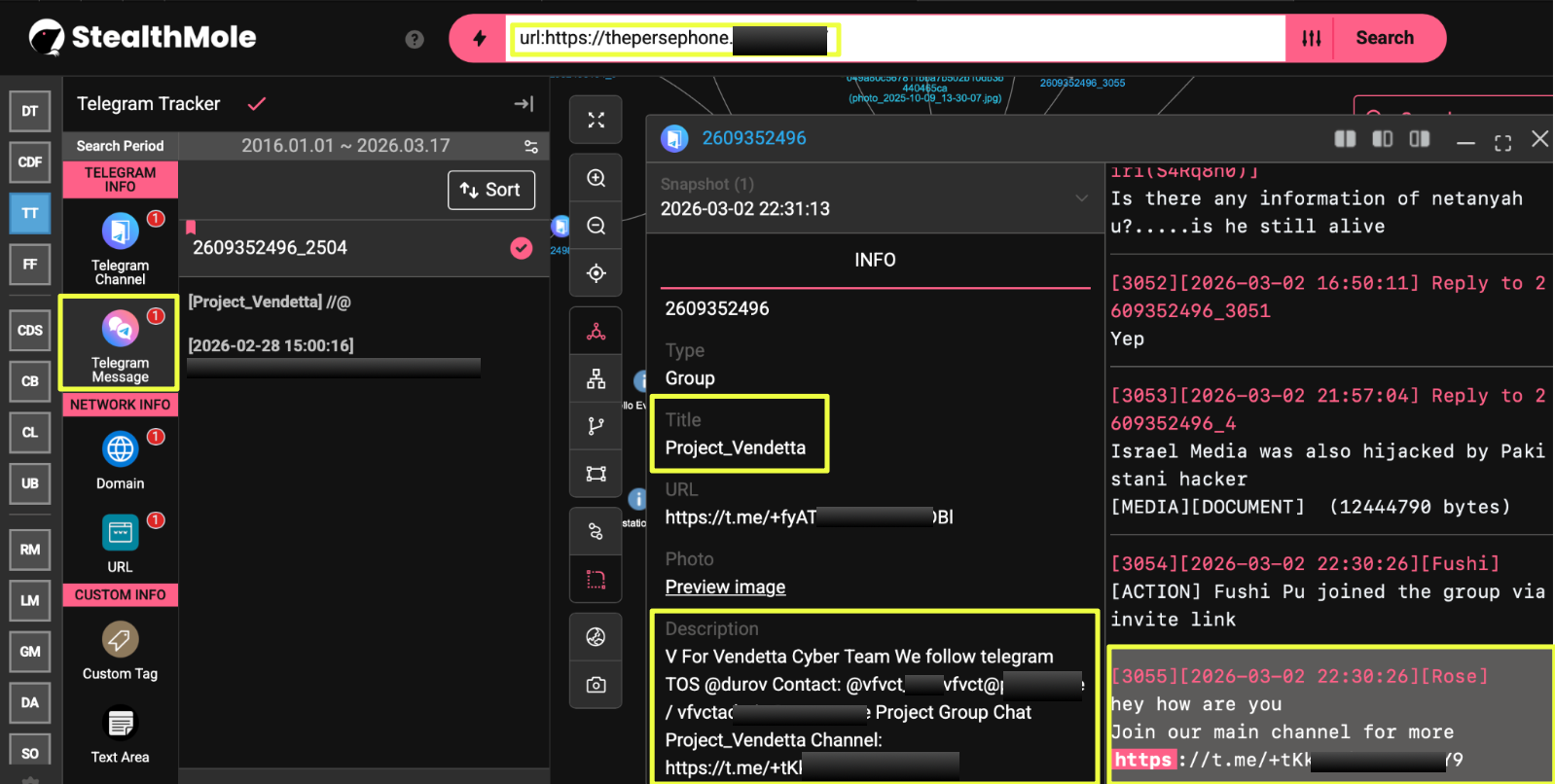 |
The group’s description referenced “V For Vendetta Cyber Team” and listed several contact points, including the Telegram bot @vfvct**** and the email addresses vfvct@****** and vfvct*****@*******.
The same description also pointed to another Telegram channel associated with the group:
- https://t.me/+tKk**********Y9
Monitoring activity within the Project_Vendetta group revealed messages where participants directly referenced the Persephone website. In one instance, the domain https://thepersephone.******.org/ was shared within the group chat, indicating that the platform was actively circulated among members of the channel. Additional messages contained discussions related to hacking activities, recruitment, and geopolitical commentary, suggesting that the group functioned as a coordination space for the actors involved.
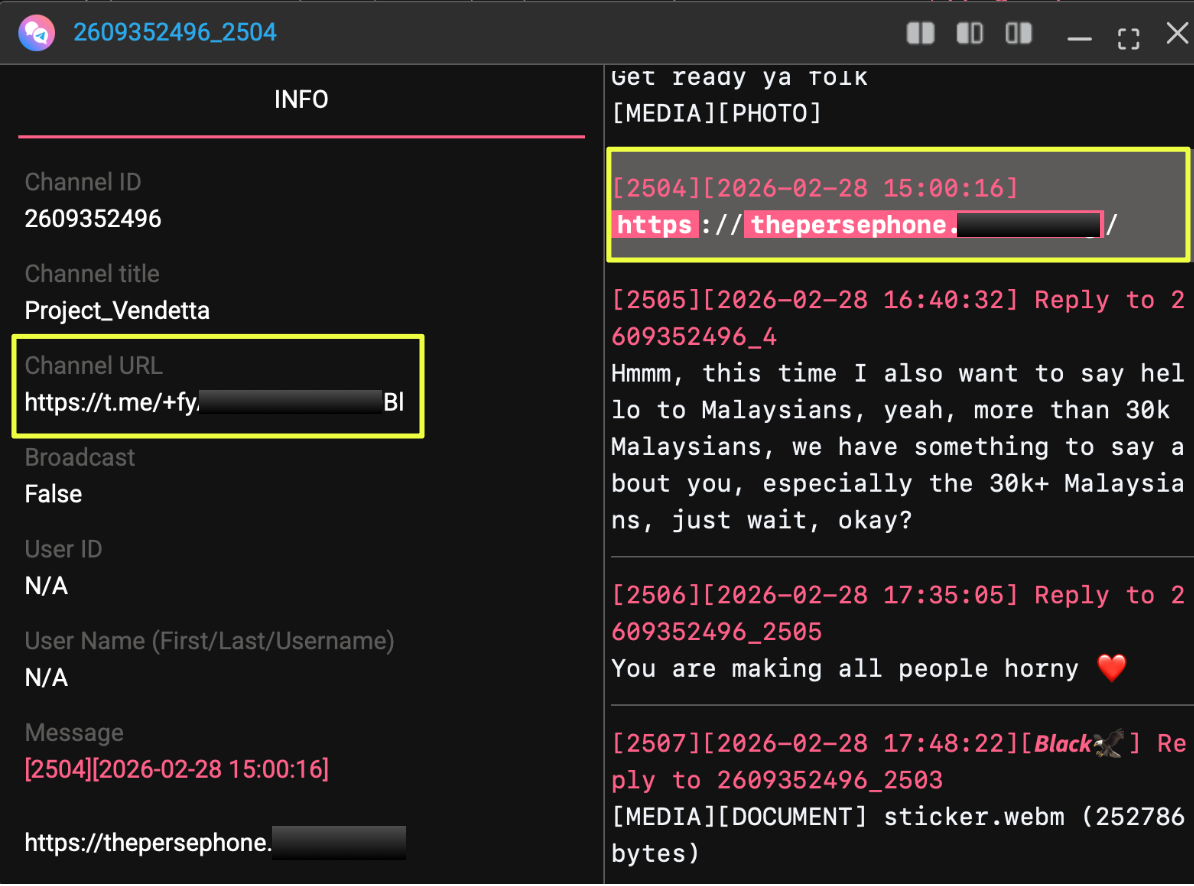 |
The presence of the Persephone domain within this Telegram group strengthened the link between the leak platform and VFVCT, indicating that the website was not operating in isolation but was instead connected to a broader communication infrastructure maintained by the group. The discovery of these channels provided a new direction for the investigation, allowing further analysis of how the actors organized their activities and interacted with collaborators across the Telegram ecosystem.
Expanding the Telegram Network
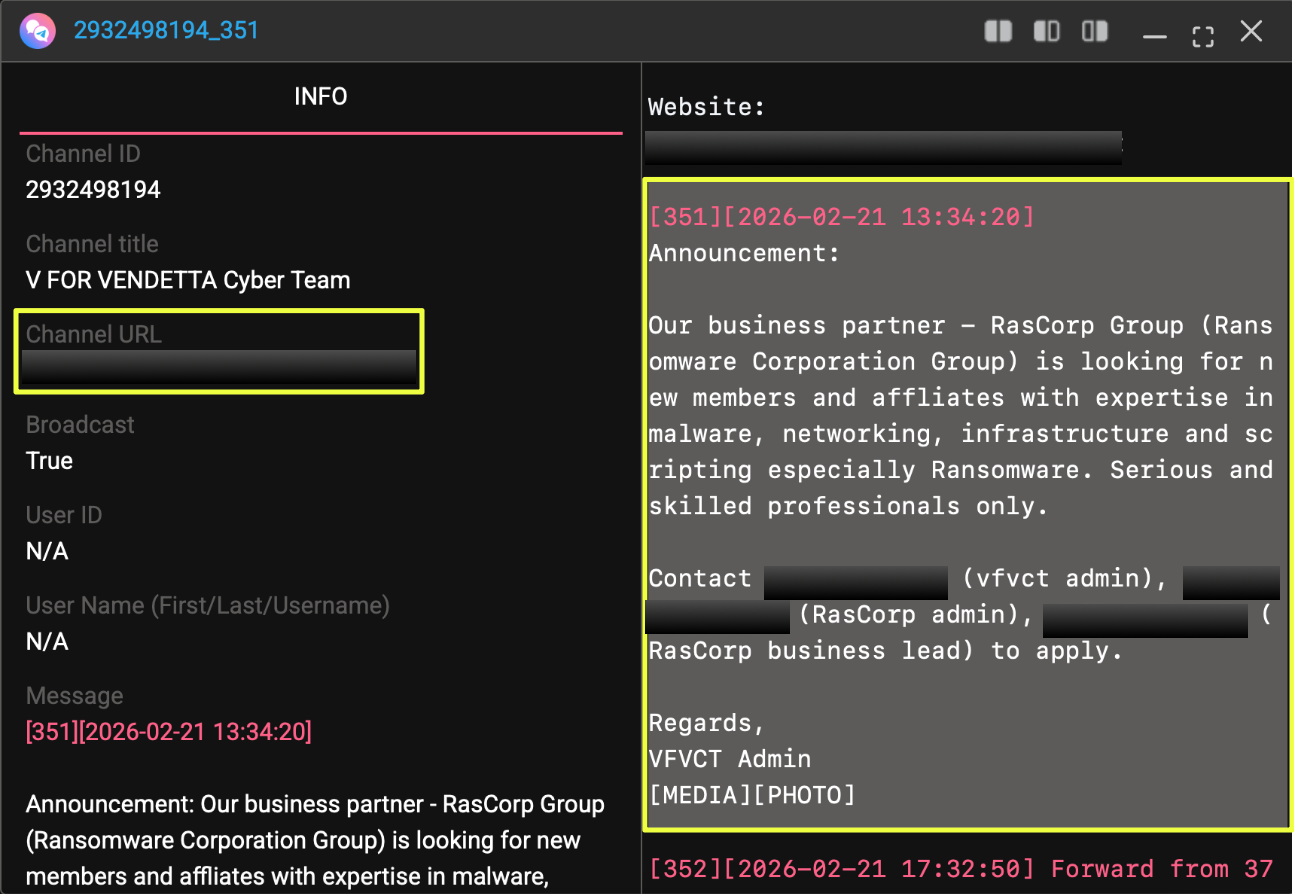
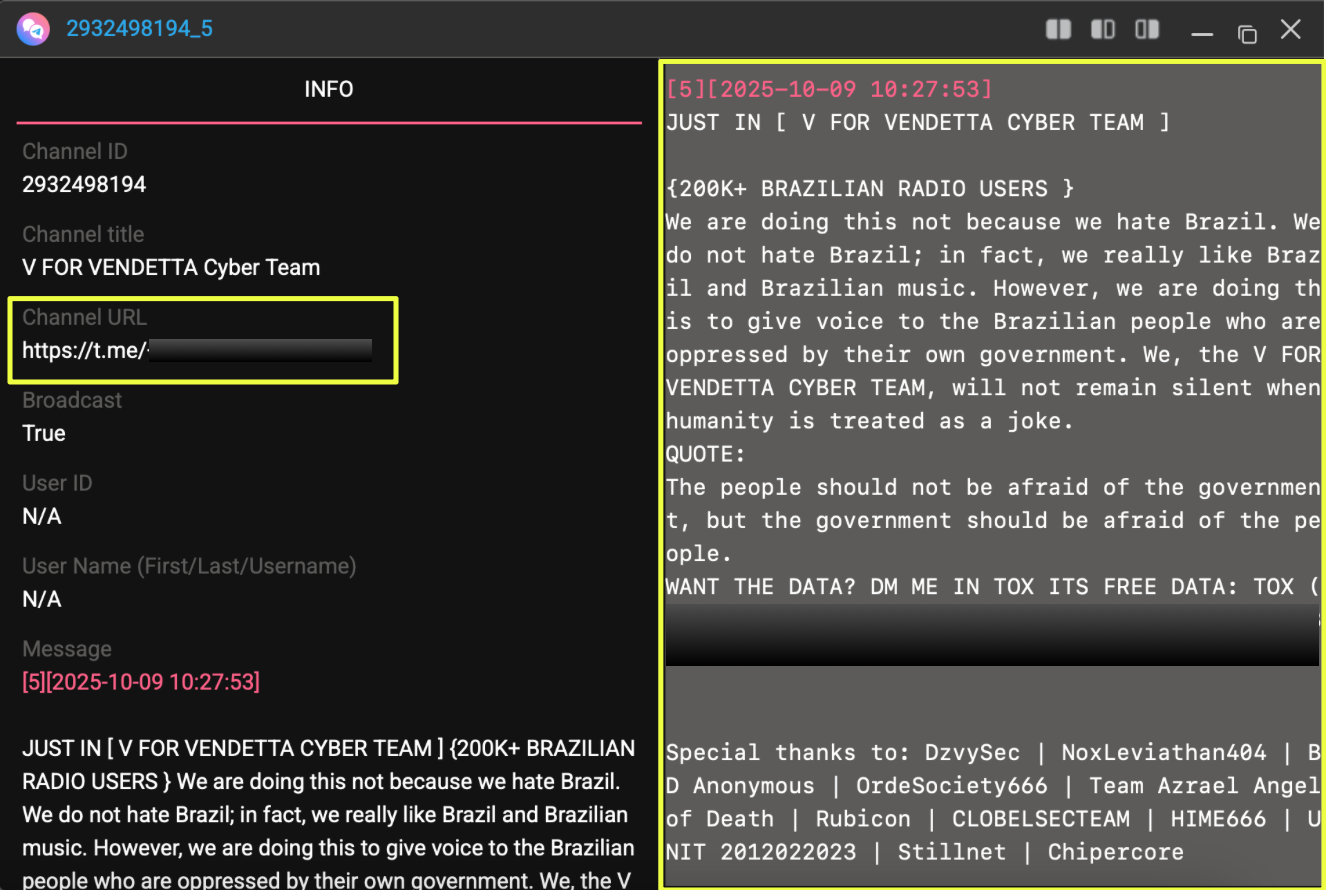
Further examination of the Telegram infrastructure linked to VFVCT revealed another channel associated with the group. The channel presented itself as a backup channel for the V For Vendetta Cyber Team. The channel description reiterated the same contact information observed earlier, reinforcing its connection to the same operational ecosystem.
- https://t.me/+tKk***********Y9
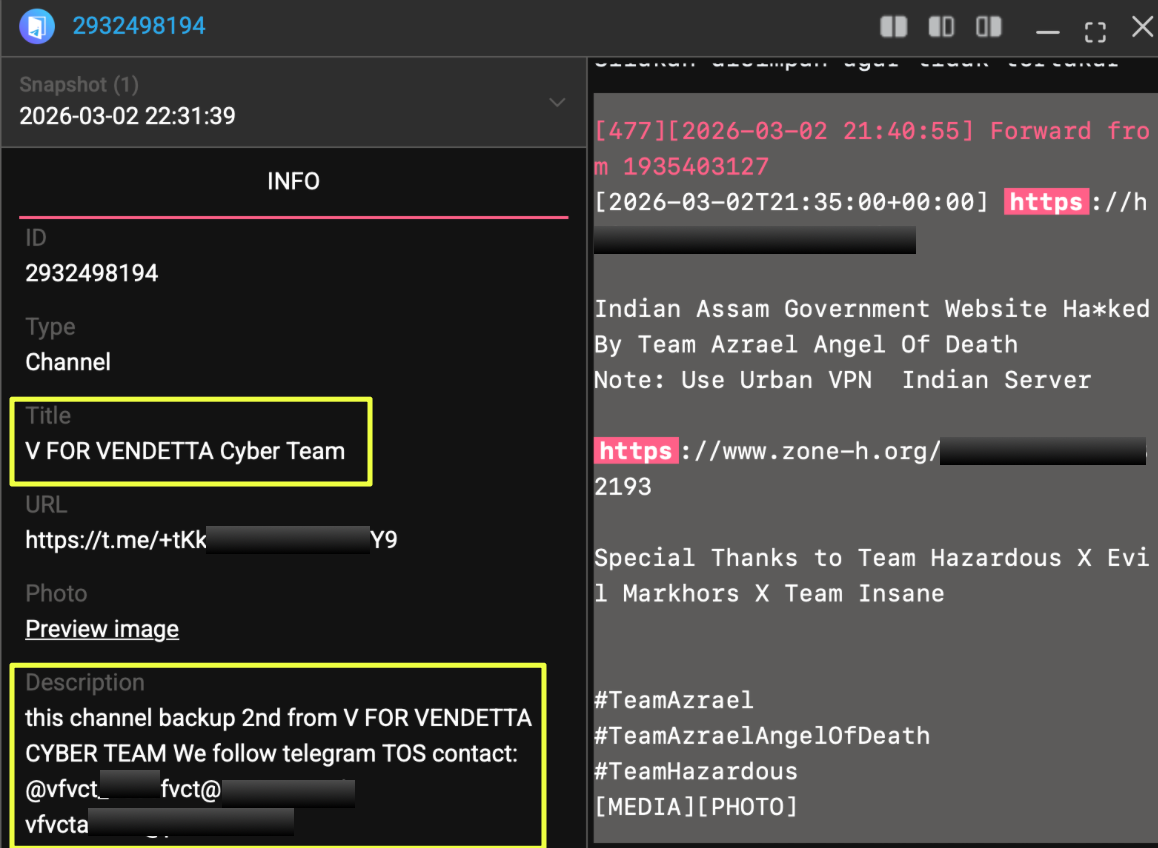 |
Activity within the channel provided additional insight into how the group communicated announcements and coordinated activities. Several posts referenced ongoing operations, recruitment efforts, and upcoming data releases. In one message, the operators announced the existence of a dedicated database-sharing channel, stating that datasets would be distributed through:
- https://t.me/DbShare************a
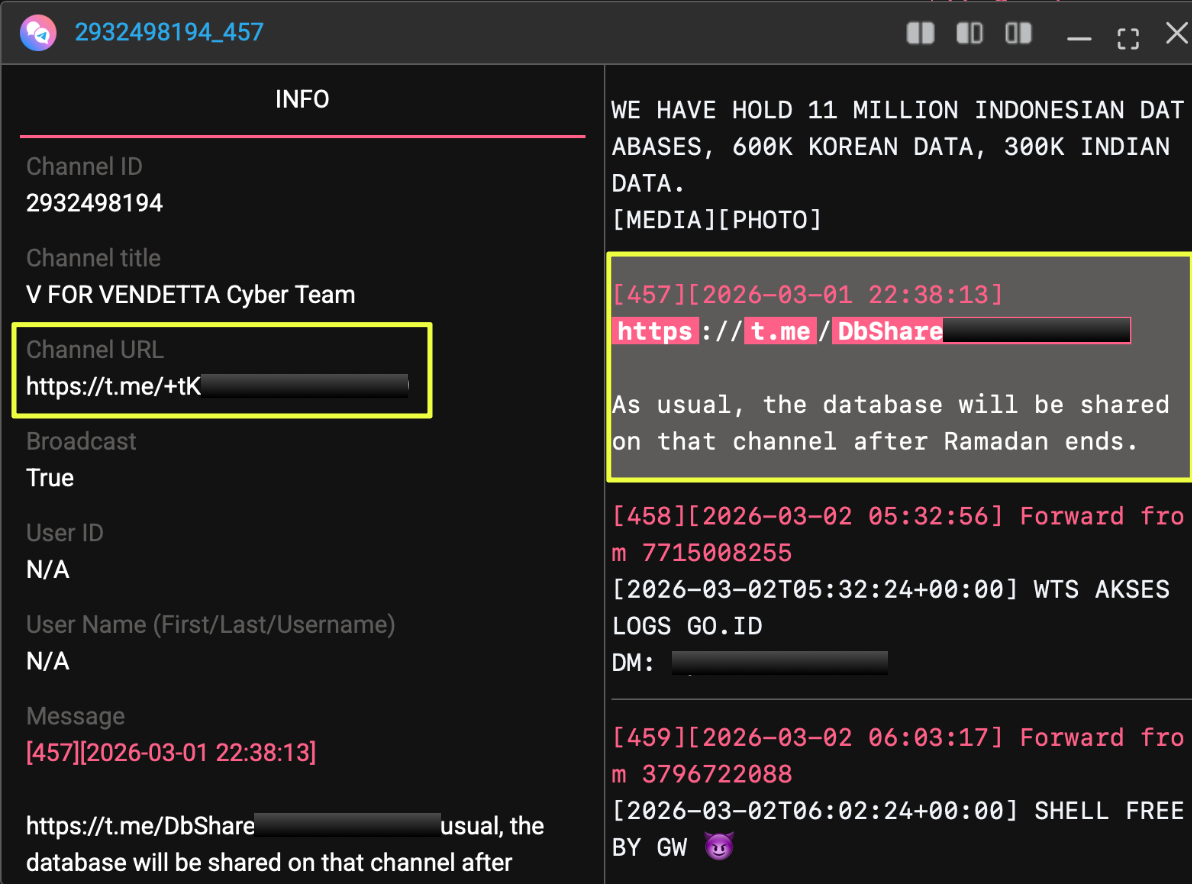 |
The same message indicated that a VFVCT database release was planned for the end of Ramadan, suggesting that the group used Telegram not only for communication but also for scheduling and promoting future leak activities.
Other posts contained statements outlining the group’s adversarial stance toward several governments. One message described a campaign targeting South Korea, India, and Indonesia, claiming possession of large datasets associated with each country. While the claims themselves could not be independently verified at the time of investigation, the language and messaging style were consistent with the rhetoric often used by hacktivist-oriented groups attempting to frame their operations as politically motivated campaigns.
 |
The presence of these announcements and operational messages demonstrated that the Telegram channels served as a primary communication layer for the actors behind the Persephone platform. Rather than being limited to leak announcements, the channels functioned as a space for recruitment, messaging, and coordination, providing further visibility into the ecosystem surrounding the platform.
Identifying Additional Infrastructure and Contact Channels
Continued monitoring of messages within the VFVCT Telegram channels revealed further references to infrastructure and contact methods used by the group. Several posts shared links and identifiers that appeared to support the group’s operations beyond Telegram itself.
One such reference pointed to a GitHub Pages site:
- https://******.github.**/******/
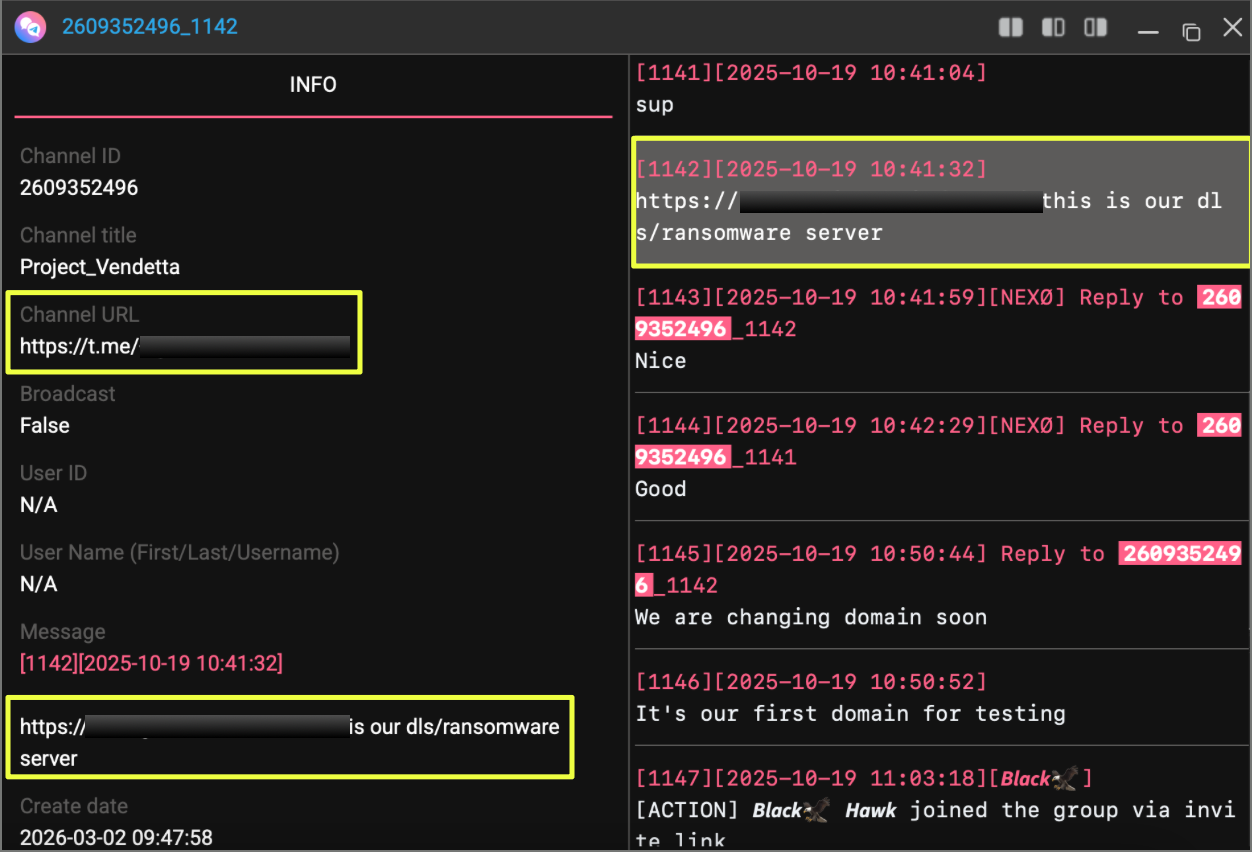 |
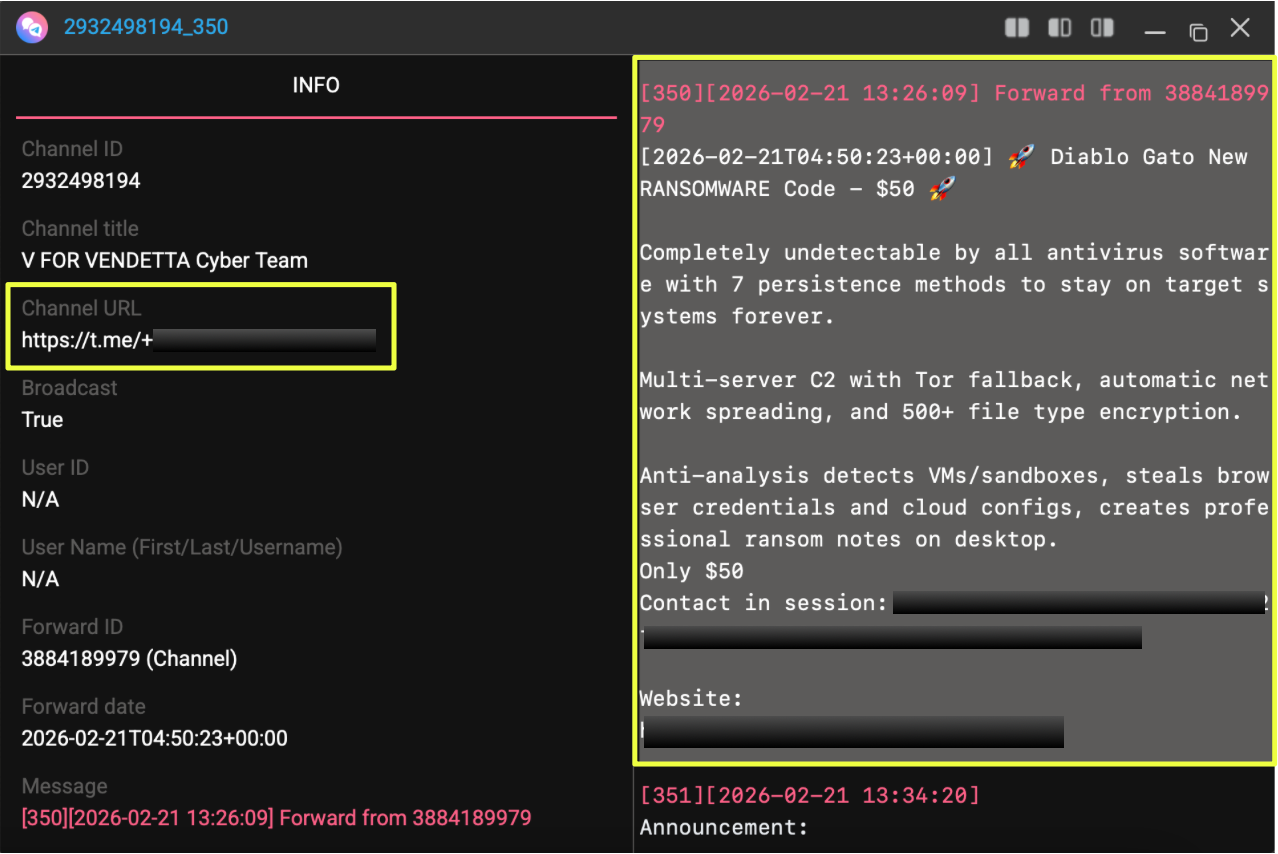
In a message shared within the channel, this site was described by the actors as part of their DLS (data leak site) or ransomware-related infrastructure. While the domain is hosted through GitHub’s static website service, the link was circulated by the actors themselves as an operational resource connected to their activities.
Additional references surfaced during the monitoring of the channel’s historical messages. Some posts promoted collaboration opportunities and invited individuals with technical expertise to participate in ransomware operations. In one instance, a message encouraged interested participants to contact the group through vfvct@******.** regarding potential ransomware partnerships. These posts suggested that the actors were actively seeking individuals with skills in malware development, networking, or infrastructure management.
 |
The Telegram channels also contained branding elements used by the group. Among them was a logo associated with the V For Vendetta Cyber Team, featuring imagery consistent with hacktivist-style symbolism. Such visual elements are commonly used by cyber groups to establish recognizable identities across multiple platforms.
Understanding the Role of THE PERSEPHONE Platform
While the Telegram channels clearly demonstrated the involvement of VFVCT, an important question remained: what exactly was the role of THE PERSEPHONE itself? To better understand the platform, the investigation returned to the website:
- https://thepersephone.******.org/
A closer examination of the site revealed that it was not presented as the project of a single group. Instead, the landing page prominently displayed references to three separate actors: VFVCT, RasCorp Group, and ClayRat. The page introduced THE PERSEPHONE as a shared platform associated with these groups and described their cooperation under the banner of “United Cyber Operations.”
This presentation suggested that THE PERSEPHONE functioned as a collaborative leak platform rather than the independent operation of one threat actor. The site included several sections containing introductory messages, operational rules, and lists of datasets attributed to different actors participating in the ecosystem. In this structure, the platform appeared to act as a centralized location where breaches and announcements could be published collectively.
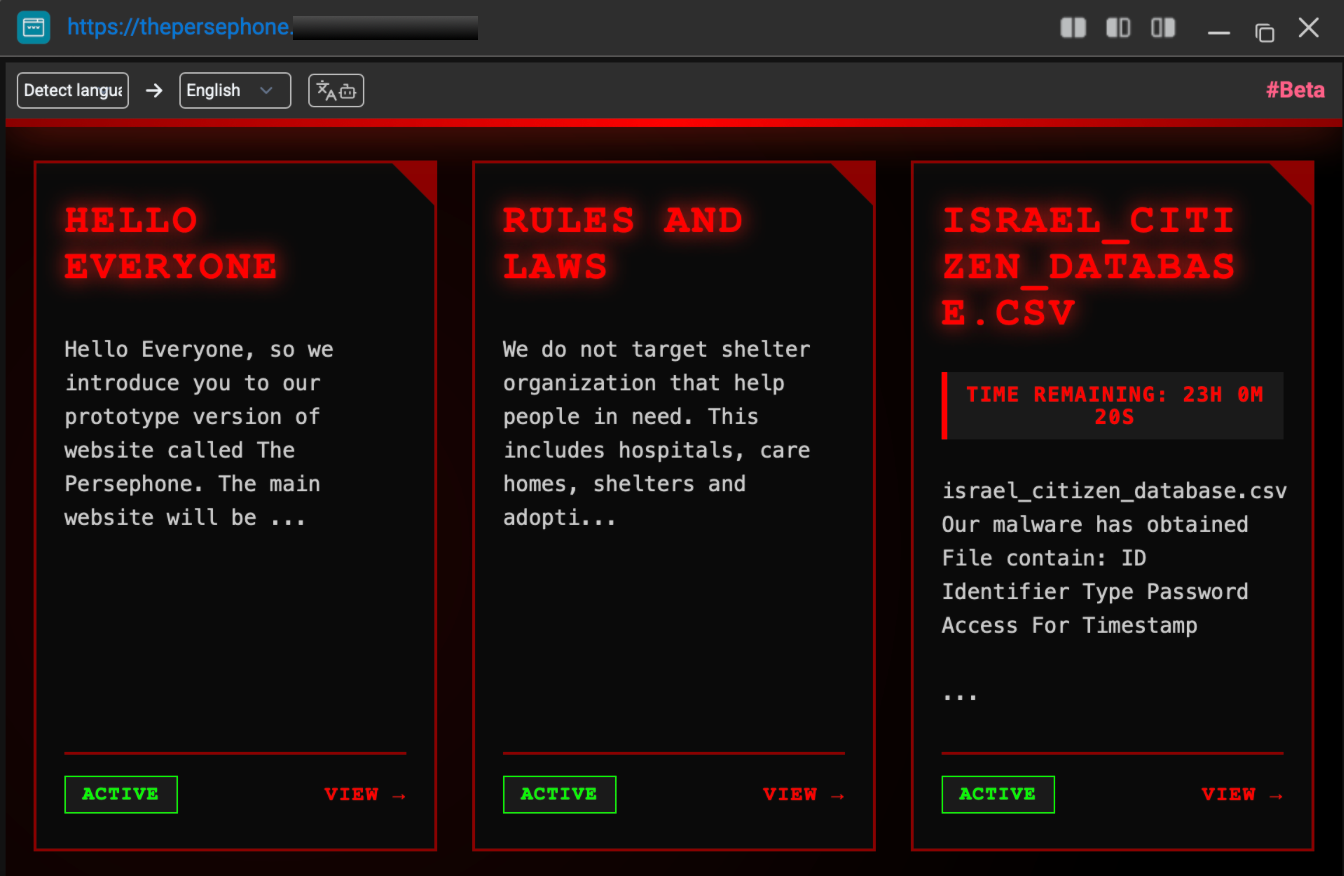 |
Among the entries visible on the site were datasets such as “israel_citizen_database.csv”, alongside other leak announcements attributed to actors connected with the ecosystem. Each entry included brief descriptions and timestamps indicating when the data had been published. The presence of multiple datasets under a single platform reinforced the idea that the site was intended to aggregate leaks from the participating groups.
Identifying the Administrator Behind the VFVCT Channels
As the investigation progressed through the Telegram infrastructure linked to VFVCT, attention turned toward identifying the individuals responsible for managing the channels and coordinating communication within the ecosystem. Monitoring activity within the Project_Vendetta group and related channels revealed repeated references to a Telegram account operating under the username @D*********a.
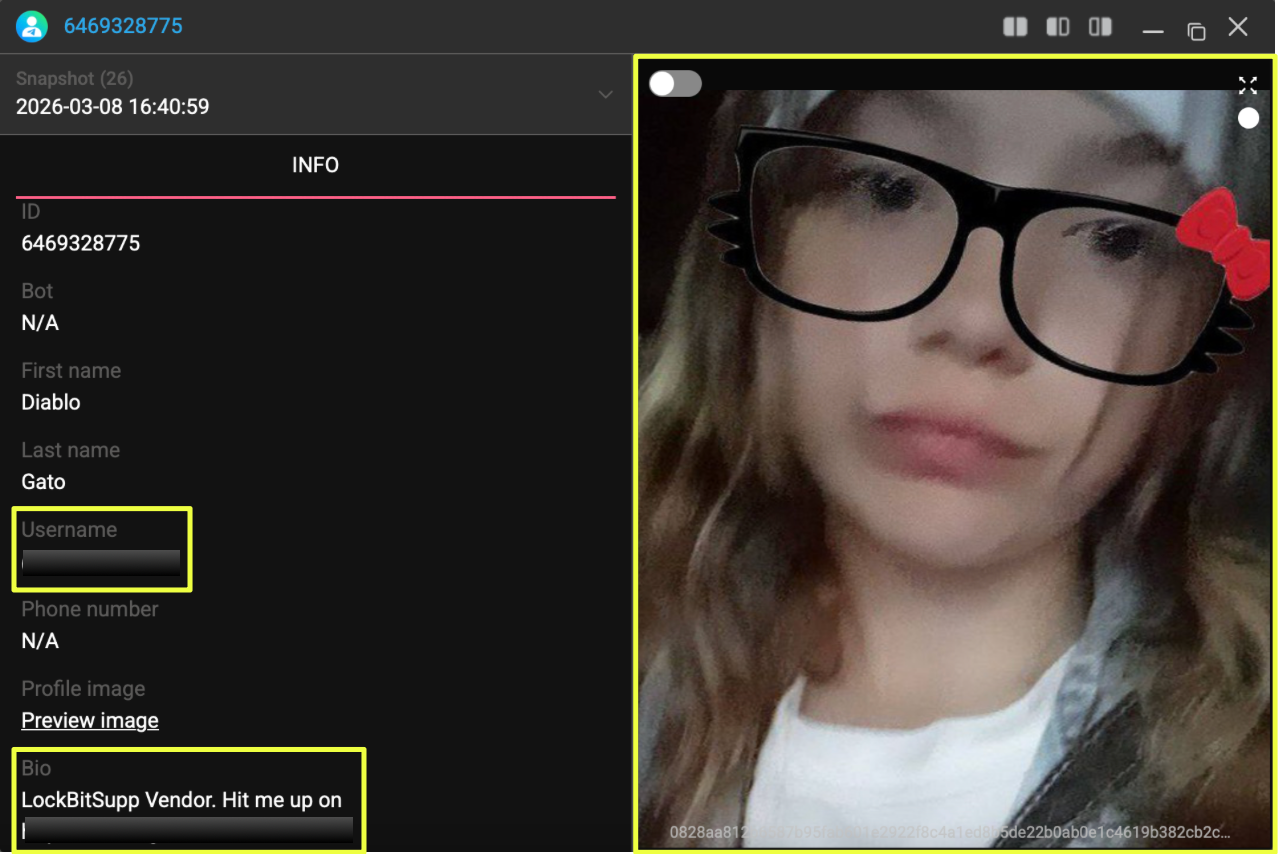 |
The account, displayed under the name “Diablo Gato,” appeared to play an administrative role within the VFVCT communication network. Messages circulated within the channels often directed potential collaborators or interested participants to contact this account, suggesting that it functioned as one of the primary points of contact for the group.
 |
To better understand the history of this account, StealthMole’s historical indexing feature was used to review earlier records associated with the profile. The historical data showed that the account had undergone multiple changes in both username and profile images, indicating attempts to periodically modify its online identity. Among the earlier identifiers linked to the account was the username Elisha24, which appeared in archived records dating back to October 2024.
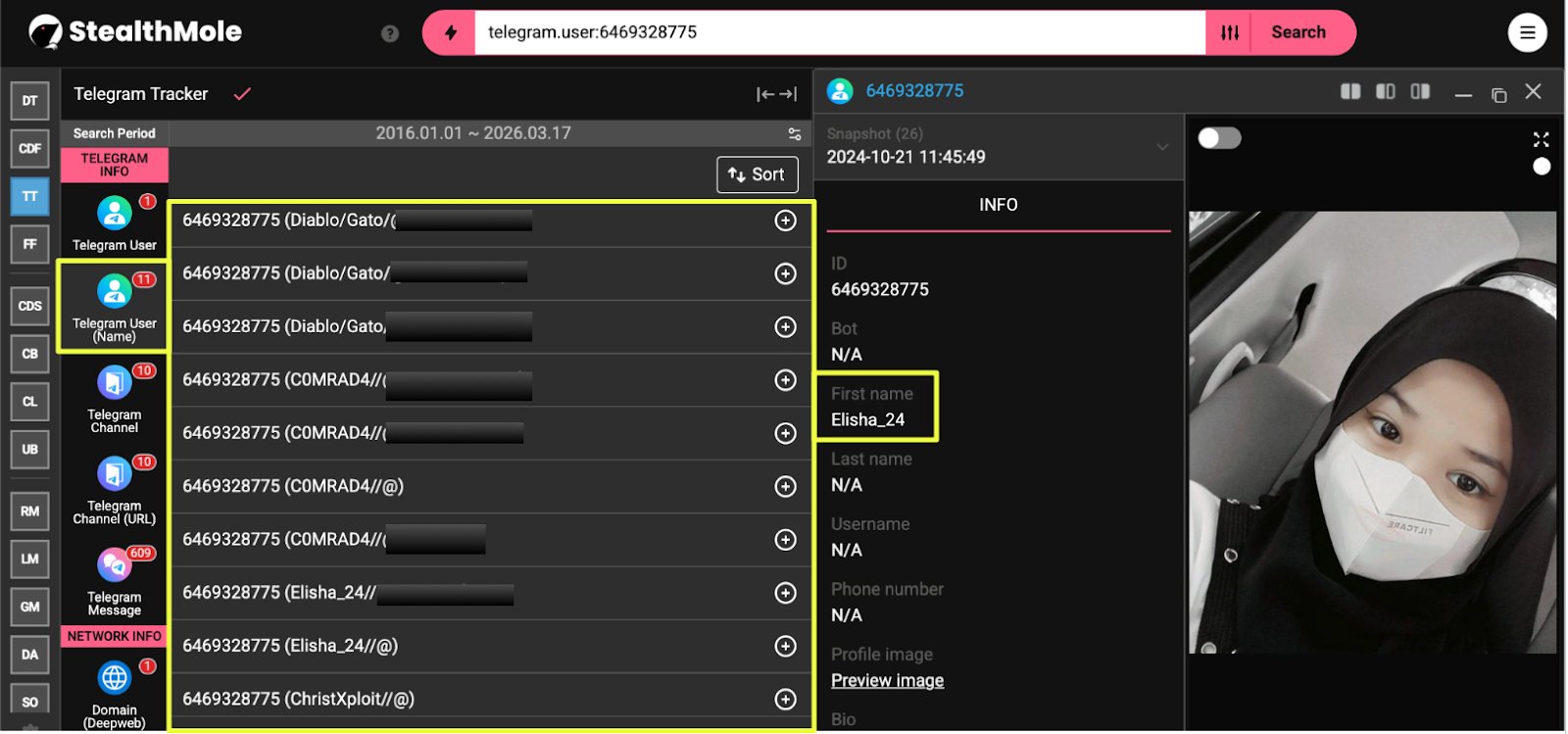 |
Further examination of the account’s activity across Telegram revealed that it was present in multiple channels related to hacking communities and cyber discussions. In at least one of these channels, RipperSec Chat, the account claimed to be located in Malaysia and communicated using the Malay language in certain exchanges. While such claims cannot be independently verified, they provide contextual clues regarding the persona behind the account.
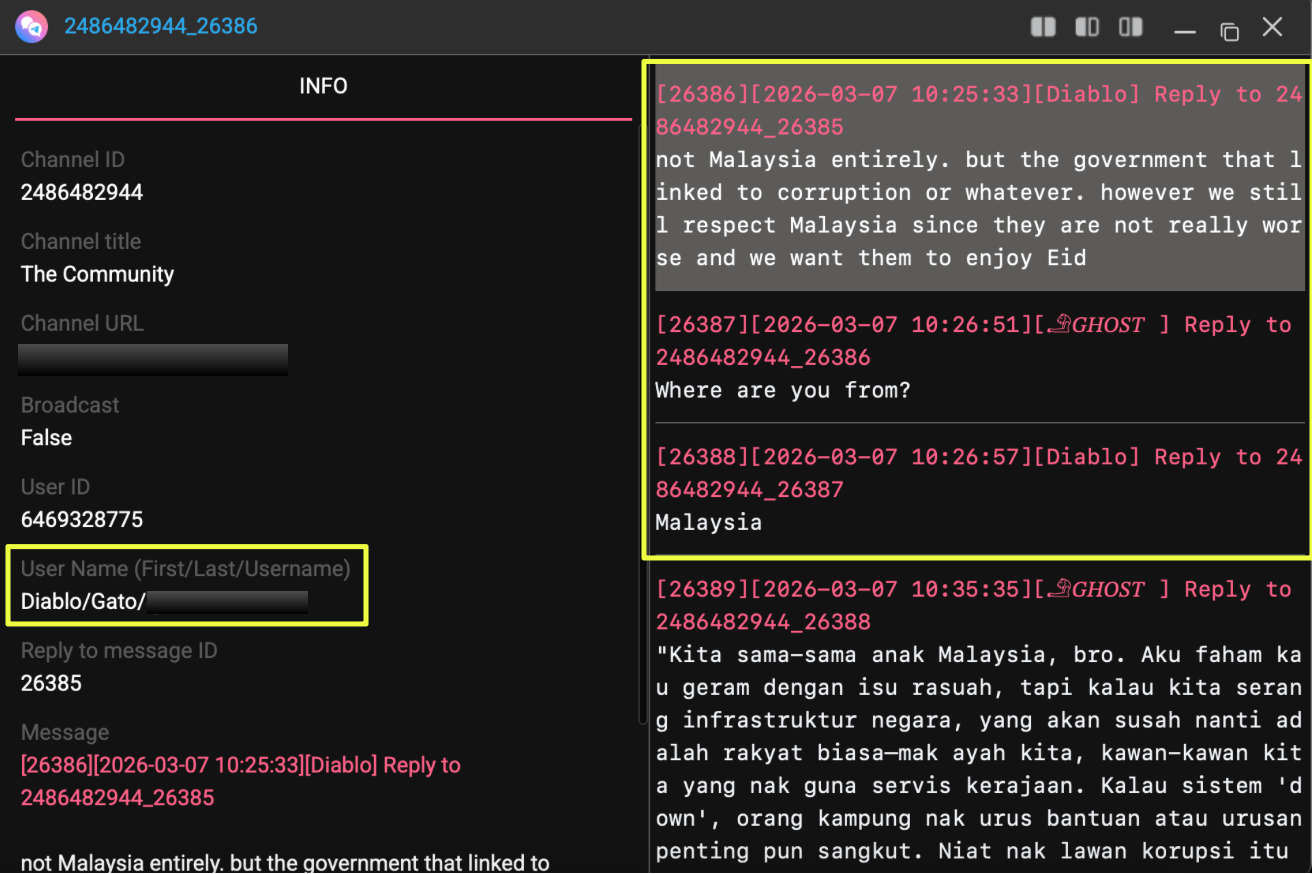 |
The account’s presence across several Telegram communities, combined with its role as a contact point within VFVCT channels, suggested that @D********a was likely involved in coordinating aspects of the group’s activities or managing communications within the broader ecosystem surrounding THE PERSEPHONE platform.
Additional Communication Channels and Operational Artifacts
Further monitoring of the VFVCT Telegram channels uncovered additional artifacts that appeared to be associated with the group’s broader communication and operational infrastructure. Among the identifiers shared within the channels was a TOX ID, a decentralized messaging protocol often used by threat actors seeking anonymous peer-to-peer communication. The identifier observed during the investigation was:
- 3574*****************************************************48
 |
The presence of this identifier indicated that the actors maintained communication options beyond Telegram, potentially enabling direct contact with collaborators through encrypted channels that do not require centralized services.
Another artifact identified during the investigation was a Session messenger ID:
- 0558************************************************57e
 |
Session is an encrypted messaging platform that routes communication through decentralized networks, providing an additional layer of anonymity. Its use is frequently observed among cyber actors who seek to avoid reliance on mainstream communication platforms.
In addition to these messaging identifiers, references were also found to a separate website:
- https://d********s.w******.net
The domain appeared to be hosted through a free web hosting provider, suggesting that it may have been used as a temporary or experimental resource by the actors. Such disposable infrastructure is commonly employed by cyber groups to host content, test tools, or distribute materials without maintaining long-term infrastructure.
Taken together, these artifacts indicated that the ecosystem surrounding THE PERSEPHONE extended beyond the visible leak platform and Telegram channels. Instead, the actors appeared to maintain a layered communication environment, incorporating multiple messaging protocols and externally hosted resources to support coordination and outreach within their network.
Conclusion
The investigation into THE PERSEPHONE began with the discovery of a leak website hosting multiple datasets under a single platform. What initially appeared to be a standalone leak portal gradually revealed a more complex structure as additional artifacts were identified across Telegram channels, underground discussions, and supporting infrastructure. Rather than representing the operation of a single group, the evidence indicated that THE PERSEPHONE functioned as a shared platform within a broader collaborative ecosystem.
Analysis of the website content and associated communications showed that VFVCT, RasCorp, and ClayRat were all referenced within the same operational environment. The platform appeared to serve as a central location where datasets and announcements could be published collectively, while Telegram channels, particularly the ones belonging to VFVCT, provided the communication layer used for recruitment, coordination, and promotion of activities.
Further investigation into the communication infrastructure revealed multiple identifiers connected to the ecosystem, including Telegram channels, bot accounts, messaging identifiers, and externally hosted resources. These artifacts illustrated how the actors maintained a distributed communication environment, relying on several platforms to coordinate activities and engage with potential collaborators.
Overall, the findings suggest that THE PERSEPHONE operates less as an independent threat actor and more as a collaborative hub, bringing together multiple groups that contribute different capabilities to the broader operation. By examining the infrastructure, communication channels, and identities surrounding the platform, the investigation provides insight into how such alliances can function within the cyber threat landscape and how shared platforms can enable coordinated activity among otherwise separate actors.
Editorial Note
Investigations involving cyber actors operating across multiple platforms rarely provide complete visibility into every aspect of an operation. Online identities, infrastructure, and affiliations can change quickly, and actors often obscure their roles within collaborative environments. As a result, attribution should be approached cautiously and treated as an evolving assessment rather than a final conclusion.
This case highlights how StealthMole’s monitoring capabilities can connect seemingly separate indicators, allowing analysts to trace relationships across different layers of an ecosystem and better understand how coordinated cyber operations take shape.
To access the unmasked report or full details, please reach out to us separately.
Contact us: support@stealthmole.com
Labels: Featured, Hacktivist Group

.svg)
.svg)
.svg)