From XpertTechy to BlackHat Tools: Uncovering a Multi-Layered Malware Distribution Network
 |
The underground market for hacking tools has grown into a structured ecosystem, where ready-made malware, remote access tools (RATs), and obfuscation techniques are openly advertised and distributed across forums and messaging platforms. What once required technical expertise is now increasingly packaged into accessible, “plug-and-play” offerings, lowering the barrier for entry into cybercrime. These tools are often promoted with claims of being fully undetectable, easy to deploy, and capable of bypassing modern security protections.
In this environment, actors rarely rely on a single platform. Instead, they operate across a mix of Telegram channels, cybercrime forums, and surface web websites, creating interconnected networks that serve different purposes, from promotion and trust-building to delivery and monetization. This layered approach not only expands their reach but also helps them maintain persistence even if one part of their infrastructure is disrupted.
This investigation began with the identification of one such distribution point and gradually uncovered a broader network of activity spanning multiple platforms. What initially appeared as isolated tool advertisements revealed deeper connections between forum identities, communication channels, and supporting web infrastructure, pointing toward a more organized operation than it first seemed.
Incident Trigger and Initial Investigation
With this broader landscape in mind, the investigation began during routine monitoring of Android RAT activity. While reviewing discussions on DarkForums, a thread was identified:
- https://darkforums.me/Thread-EagleSpy-v5-LifeTime-Activated-Latest-Android-RAT
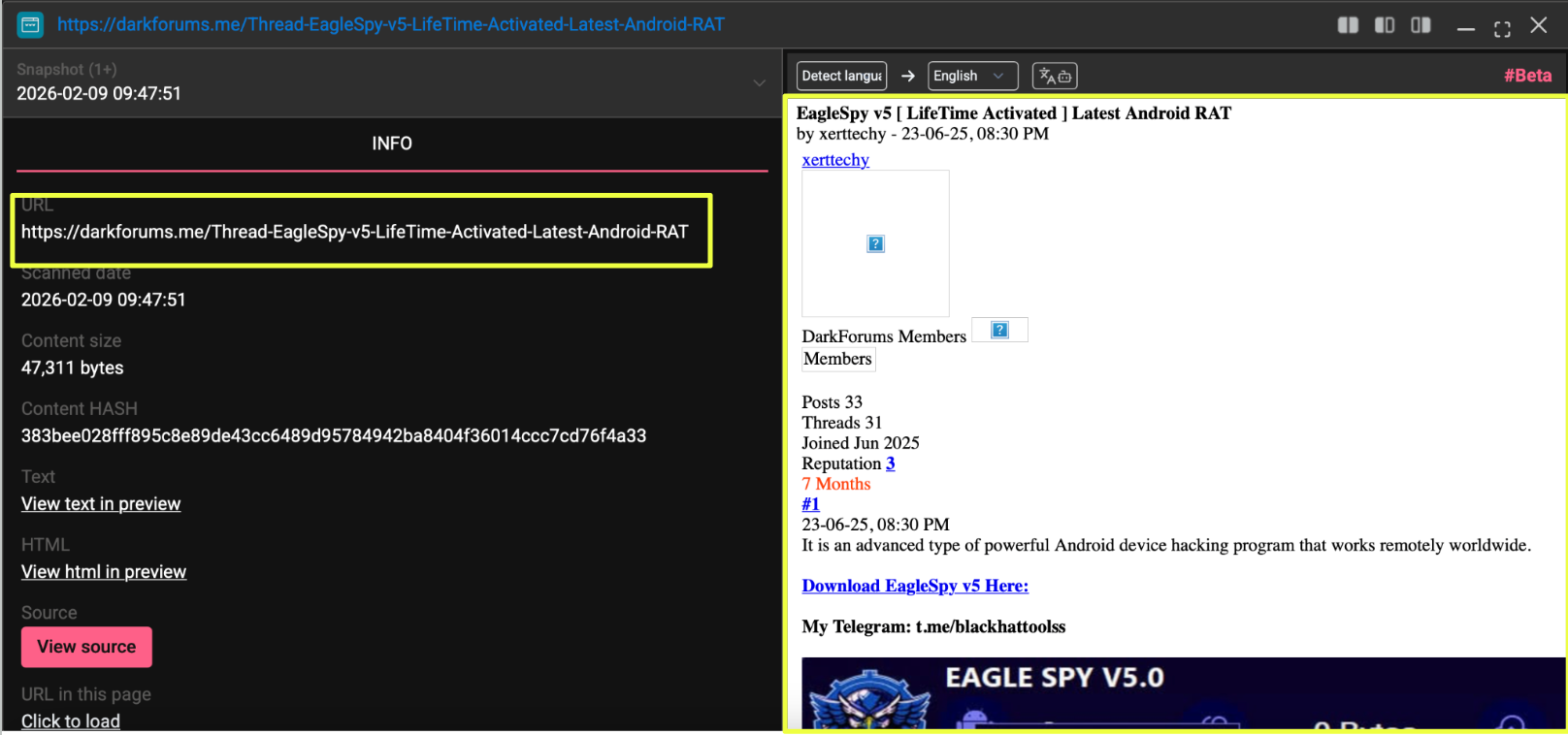 |
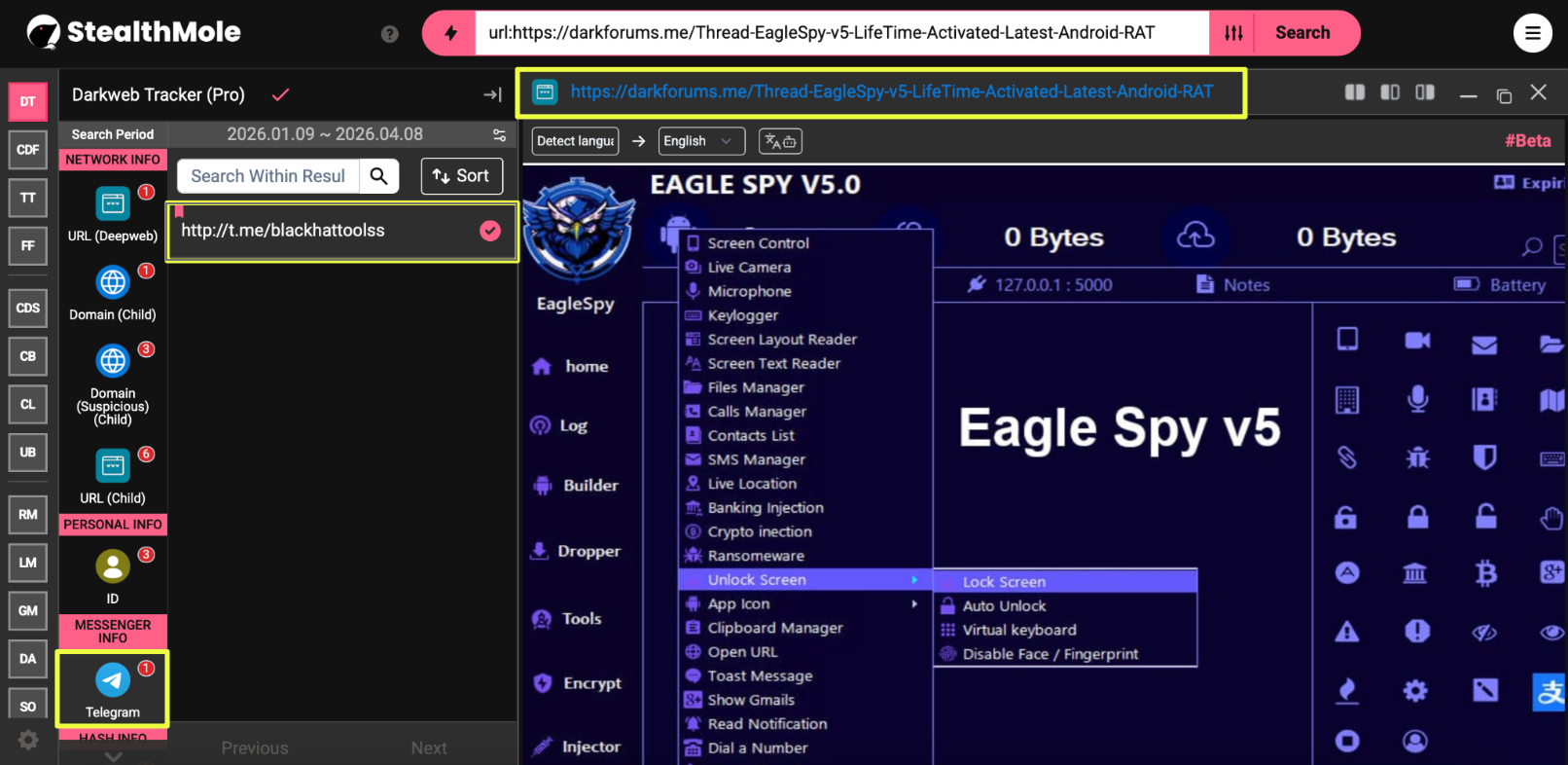
The post promoted “EagleSpy v5” as a lifetime-activated Android RAT, presented as a ready-to-use tool. Its structure and messaging were consistent with many similar listings seen across underground forums: emphasizing ease of use and accessibility rather than technical complexity.
At this stage, the thread itself did not appear unusual in isolation. However, a closer look at the content revealed a direct contact point provided by the user “xerttechy,” including a Telegram link:
- http://t.me/blackhattoolss
 |
This detail became the first pivot in the investigation. Rather than focusing solely on the tool being advertised, attention shifted toward the identity of the user and the communication channel being promoted.
To build initial context, the username “xerttechy” was queried using StealthMole’s Dark Web Tracker. This revealed multiple additional threads associated with the same user across DarkForums, including posts promoting other tools such as Craxs RAT, XWorm HVNC RAT, crypto-related stealers, and mining utilities. Despite variations in the tools being advertised, the structure of these posts remained consistent, suggesting a pattern rather than isolated activity.
The repeated promotion of different tools under the same identity, along with the presence of a shared contact channel, indicated that the initial finding was likely part of a wider distribution effort rather than a standalone post.
Expansion of Actor Activity Across Forums
Following the initial pivot on the username “xerttechy,” the investigation focused on understanding how widely this activity extended beyond DarkForums. Using StealthMole’s Dark Web Tracker, additional posts linked to this identity began to surface across multiple threads and platforms.
On DarkForums itself, the same user was found promoting a range of tools, including:
- Craxs RAT
- XWorm HVNC RAT
- Crypto-related stealers
- Monero (XMR) mining builders
- APK encryption and bypass methods
While the tools varied, the overall pattern remained consistent: short promotional posts, emphasis on functionality, and a clear intent to attract users looking for ready-made solutions.
One thread in particular stood out:
- https://darkforums.me/Thread-Craxs-RAT-Best-Android-RAT-Fully-Activated
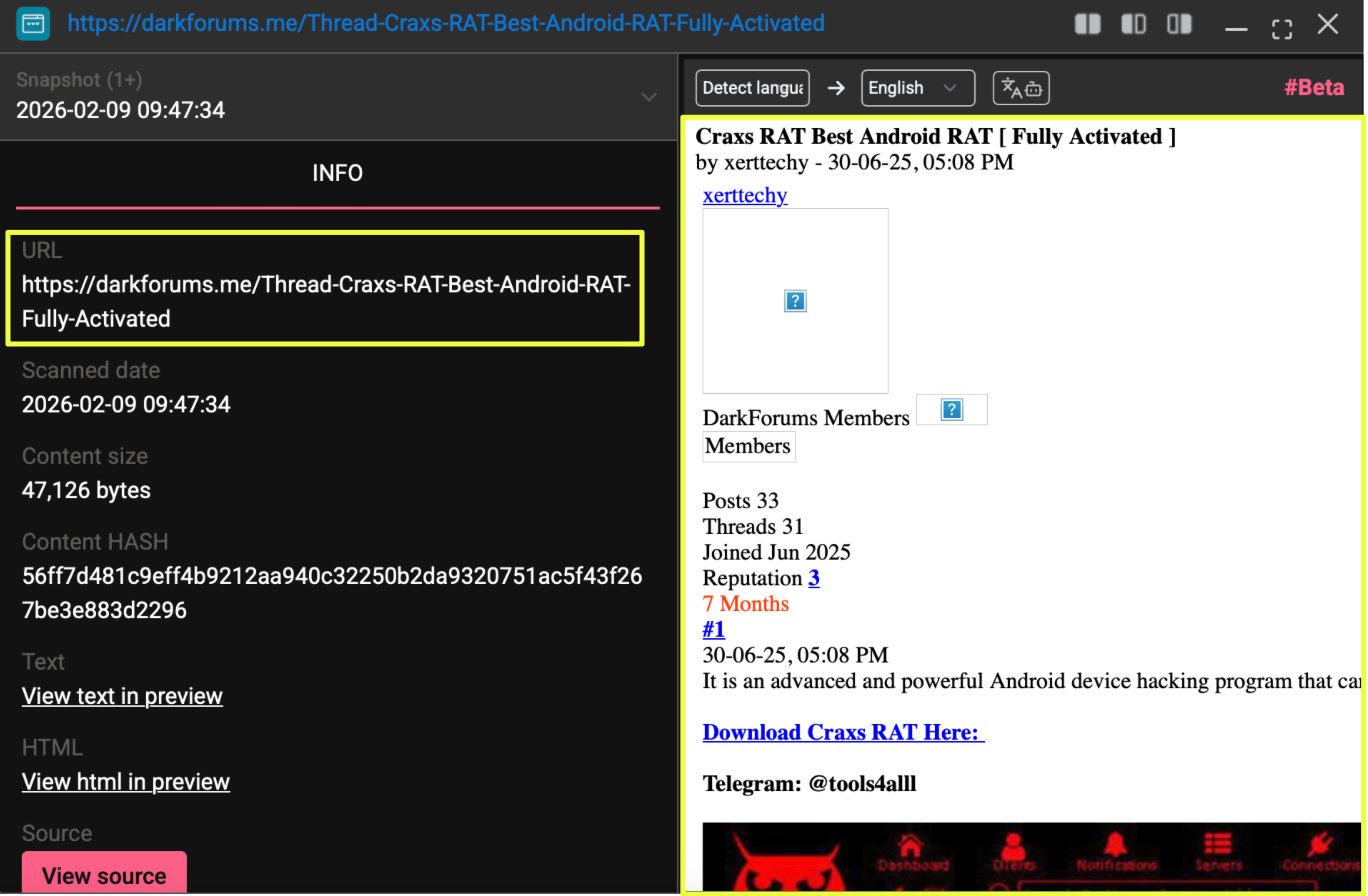 |
Unlike the earlier EagleSpy post, this thread referenced a different Telegram contact:
- t.me/tools4alll
This introduced a second communication channel into the investigation, suggesting that the actor was not relying on a single point of contact. Whether this reflected multiple channels under the same control or a broader distribution setup was not immediately clear, but the overlap in behavior and posting style indicated a connection worth tracking.
The Craxs RAT thread also led to an external website:
- https://www.xperttechy.**/craxs-rat-cracked/
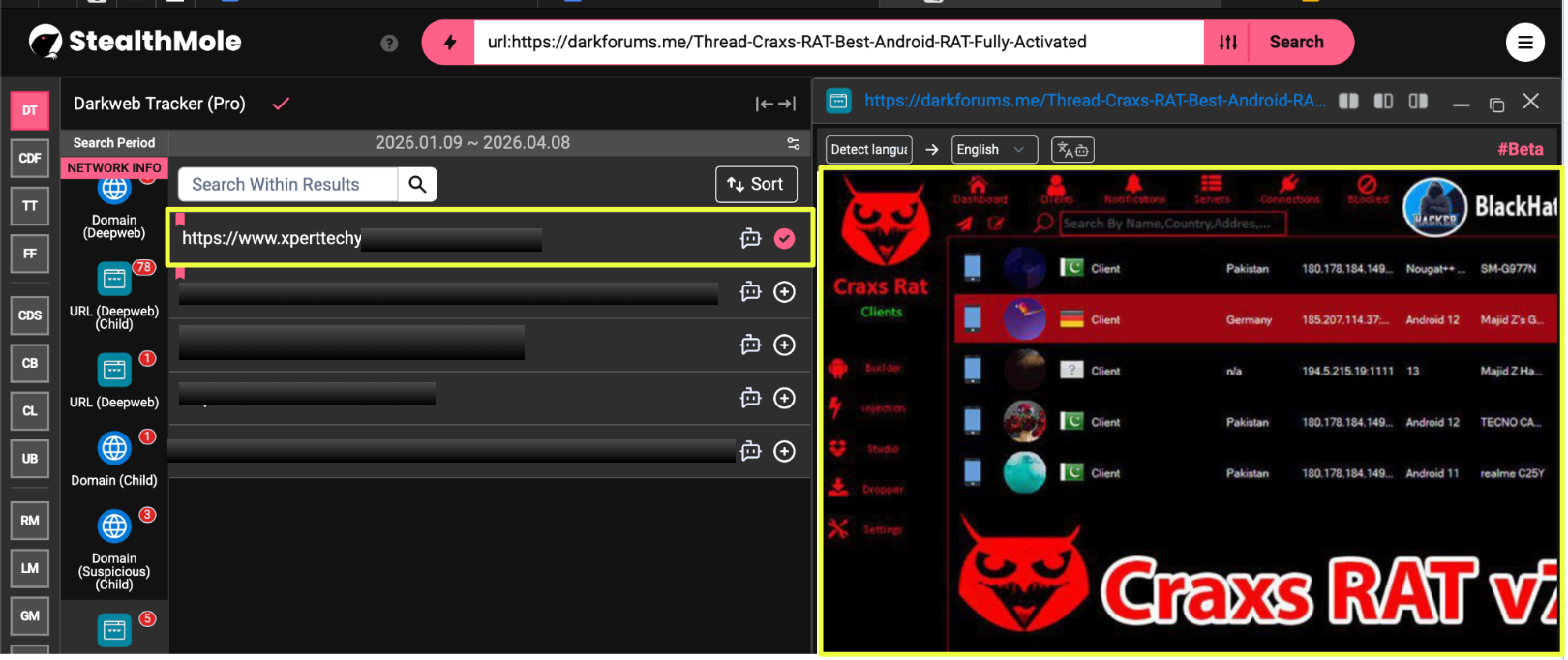 |
This was the first instance where the activity extended beyond forums and messaging links into a standalone web domain, adding another layer to the investigation.
Linking External Infrastructure and Additional Identities
The discovery of the Craxs RAT page marked a shift in the investigation, as activity was no longer confined to forum posts. The website appeared to host similar content, promoting cracked versions of tools that had already been observed on DarkForums.
Using this page as a pivot, further searches revealed the same Craxs RAT promotion appearing on other platforms:
- https://nulledbb.com/thread-Craxs-RAT-Best-Android-RAT-Full-Activated
- https://craxpro.to/threads/craxs-rat-best-android-rat-lifetime-activated.1757907/
On Nulled, the thread was posted by a different user:
- https://nulledbb.com/profile/726093/ (“markoliver”)
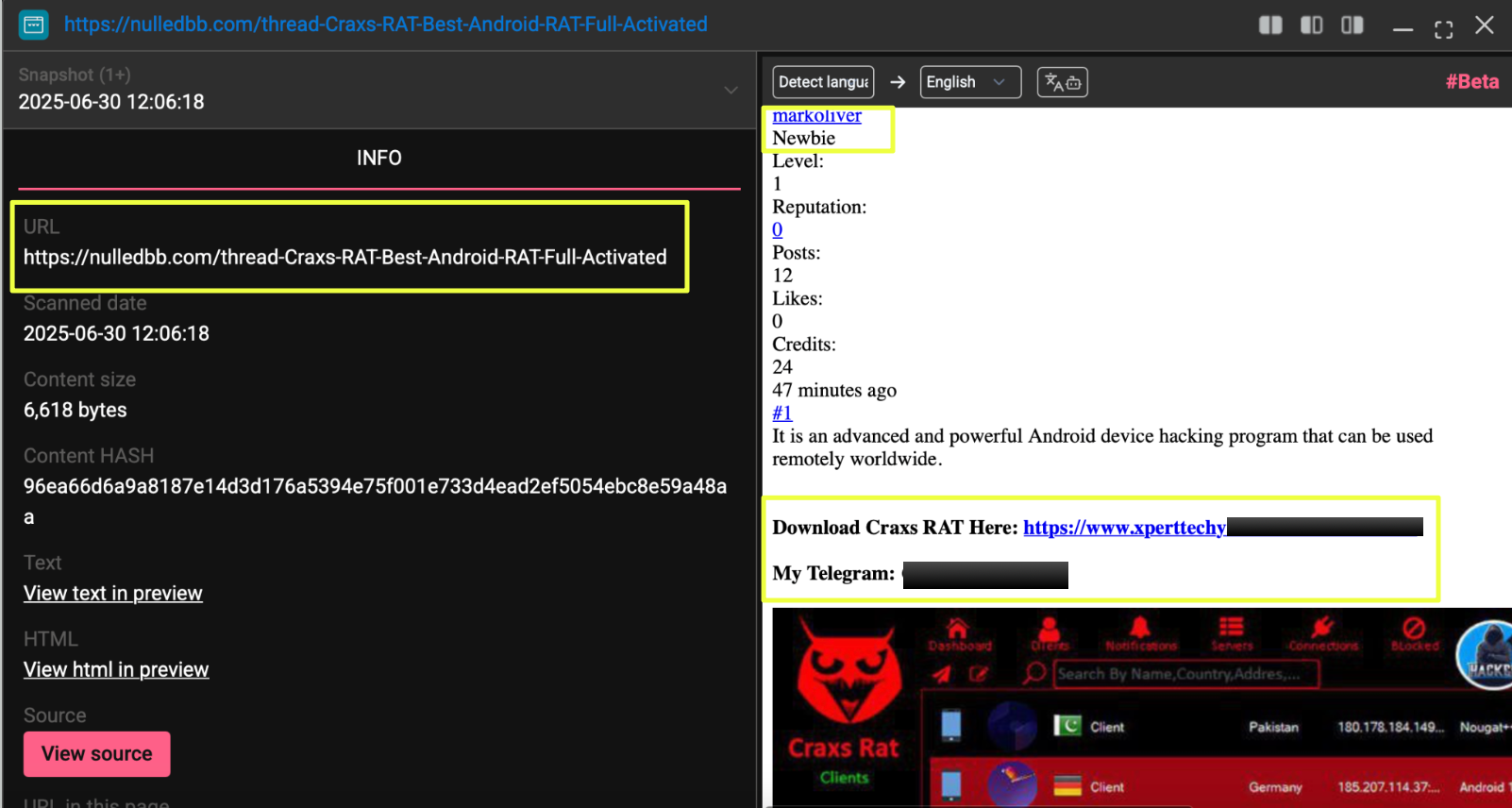 |
This introduced a new identity into the investigation. To understand whether this was a separate actor or connected activity, the username “markoliver” was queried in StealthMole’s Dark Web Tracker.
The results showed that this user was active across multiple forums, including:
- https://demonf*******s.net/Thread-FUD-K-G-B-RAT-Crypter-HVNC-Fully-Undetectable
- https://darkne*****y.com/threads/bitrat-advanced-windows-rat-fully-activated.37563/
- https://sini*****r.***/Thread-FUD-Windows-Crypter-Bypass-All-Antiviruses-Avanced
- https://h***.org.**/index.php?threads/venom***t-pro-hvnc****r-rat-latest-version.1***9/post-1***1
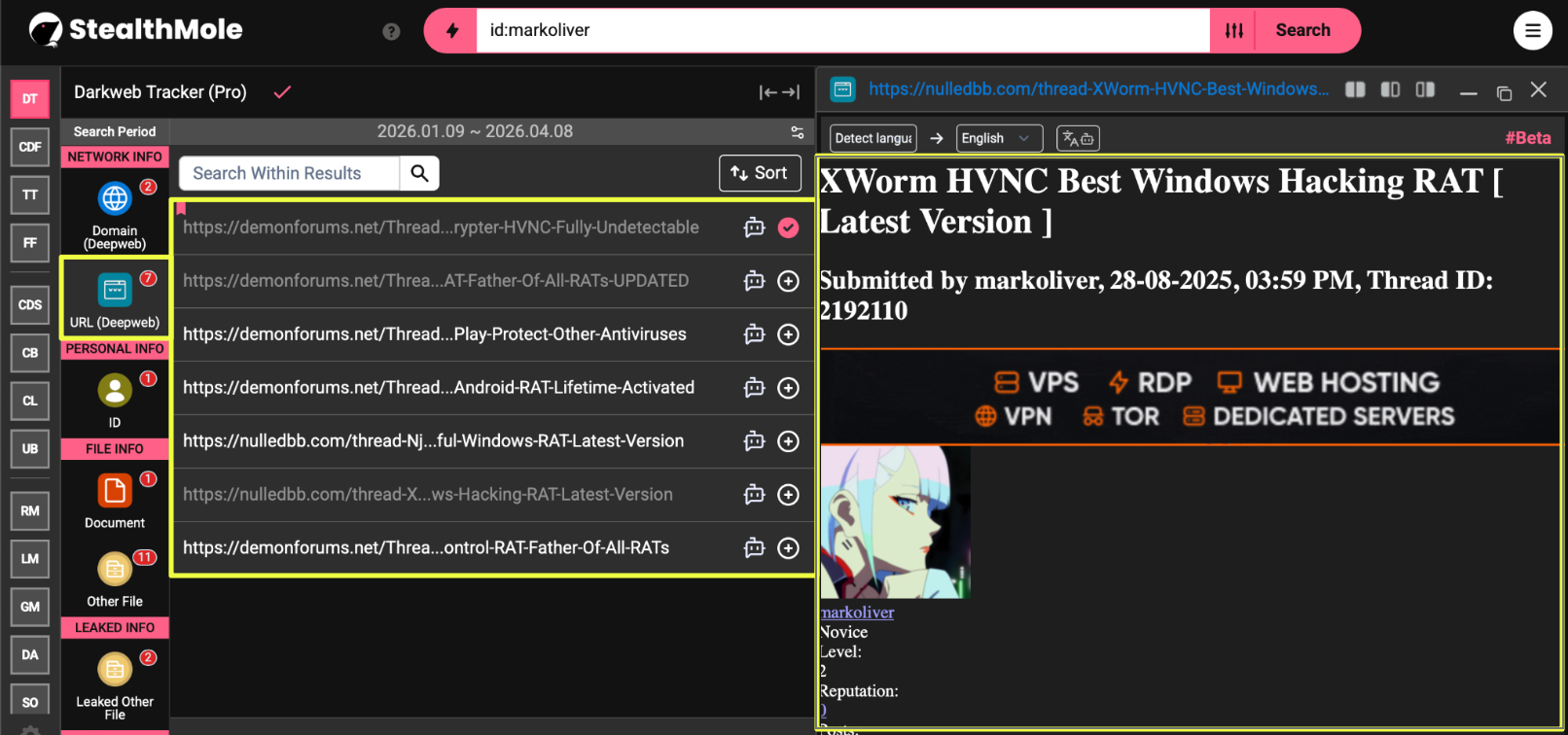 |
Across these threads, the same pattern continued: promotion of RATs, crypters, and related tooling. More importantly, the Telegram contact t.me/tools4alll appeared repeatedly across these posts, matching the contact seen earlier in the Craxs RAT thread linked to “xerttechy.”
Alongside this, another domain surfaced:
- https://www.xperttechy.***/
The naming similarity with the previously identified xperttechy.*** domain suggested a possible connection between the two, indicating that the activity might be supported by more than one web asset.
At this point, the investigation had established a consistent overlap between forum identities, external websites, and a shared Telegram contact, tying together activity that initially appeared to come from different users.
Telegram Infrastructure and Distribution Layer
With multiple forum posts pointing toward Telegram, the investigation shifted to examining how these channels were being used in practice. Two links had already surfaced during earlier steps:
- http://t.me/blackhattoolss
- http://t.me/tools4alll
Opening t.me/blackhattoolss provided a clearer view of how the operation was structured. The channel was actively used to promote hacking tools, with posts advertising Android RATs, APK-based payloads, and related utilities. Instead of detailed explanations, most posts followed a simple pattern: brief descriptions, screenshots or claims of functionality, and links for download or contact.
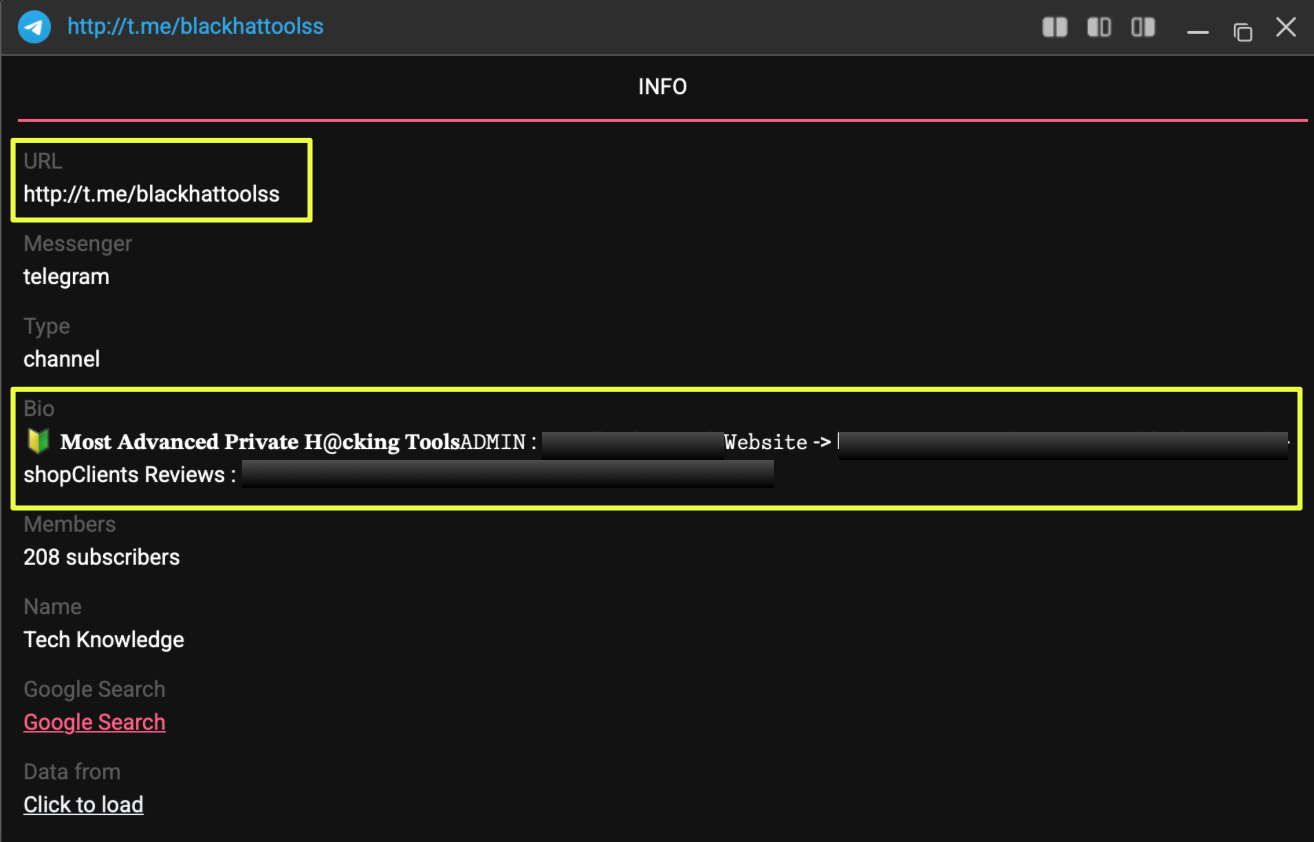 |
The channel bio included a direct point of contact:
- @real*******ls
Alongside this, it referenced external pages:
- https://sites.google.com/view/black-hat**********p
- https://shop.blackhat***********p.cc/p****s/
These appeared to support the channel’s activity by acting as landing pages and “proof” repositories, reinforcing trust for potential buyers.
Looking at the content more closely, some posts included direct download links, such as APK files hosted on third-party platforms (e.g., MediaFire). This indicated that Telegram was not just being used for communication, but also as a distribution point where users could access tools with minimal friction.
The second channel, t.me/tools4alll, was repeatedly referenced across multiple forum threads tied to both “xerttechy”and “markoliver.” Its presence across different platforms suggested that it served a similar role, acting as a consistent contact layer that connected otherwise separate posts.
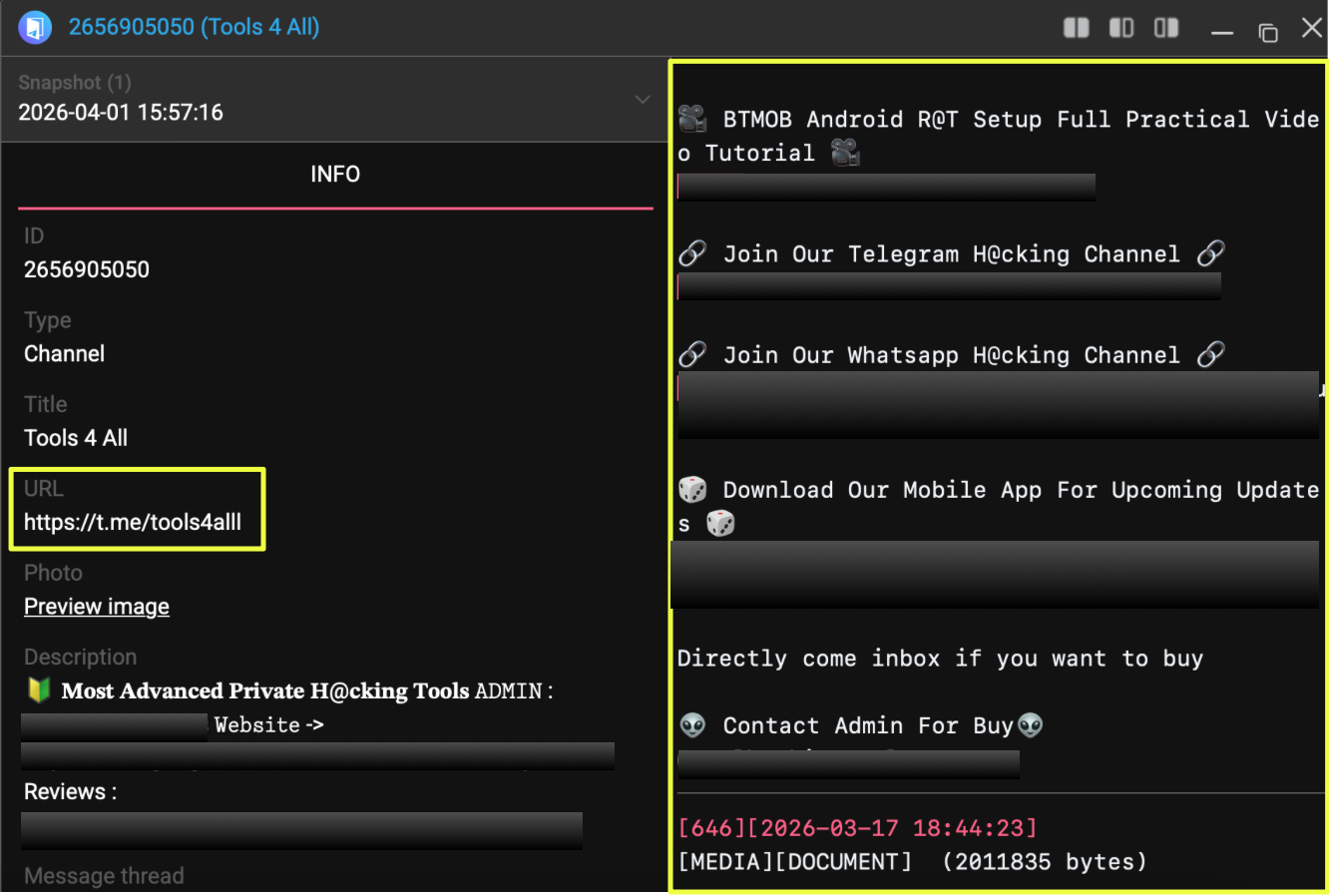 |
What stood out here was not just the existence of these channels, but how frequently they appeared across unrelated threads and identities. Whether a tool was being promoted on DarkForums, Nulled, or other platforms, the path often led back to Telegram. This made it a central point in the overall setup, linking together forum activity, tool promotion, and user interaction in one place.
Web Infrastructure and Identity Signals
Beyond forums and Telegram, the investigation also uncovered supporting web infrastructure that appeared to be tied to the same activity. One of the key domains identified earlier, https://www.xperttechy.***, provided additional context when explored beyond the initial Craxs RAT page.
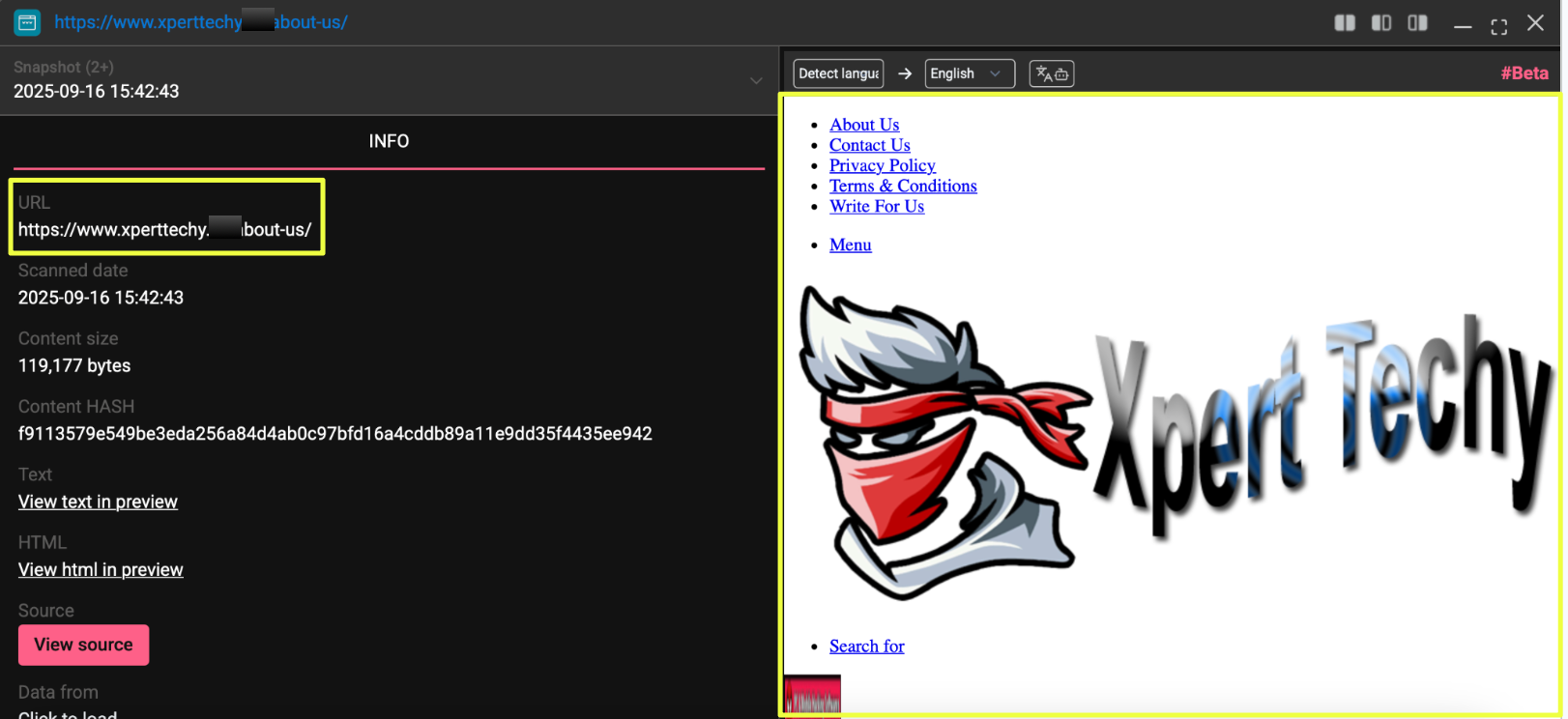 |
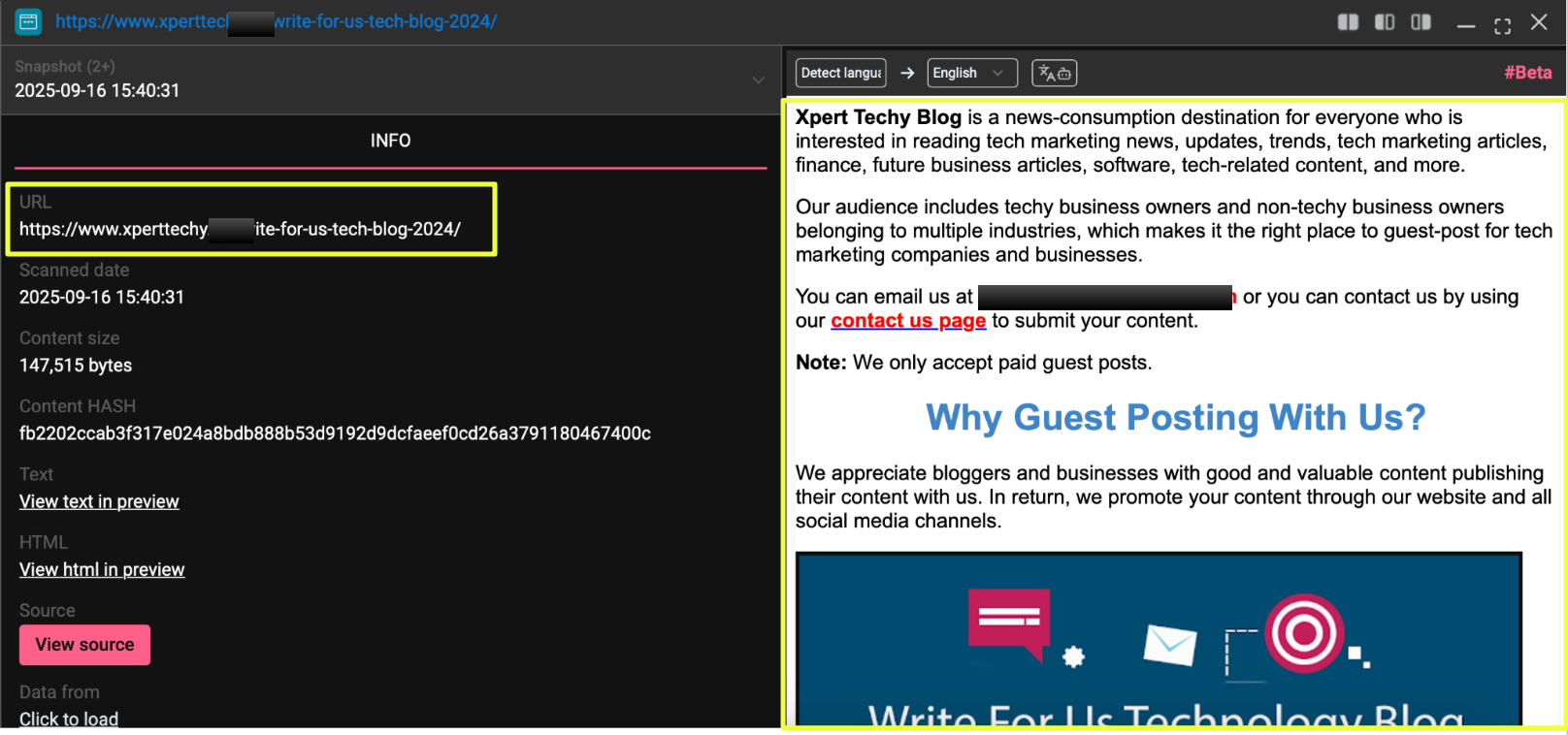
The site was not limited to tool-related content. Some sections presented it as a general-purpose technology platform, offering blog content, guest posting opportunities, and services typically associated with legitimate web development or tech publishing.
- https://www.xperttechy.***/about-us/
- https://www.xperttechy.****/write-for-us-tech-blog-2024/
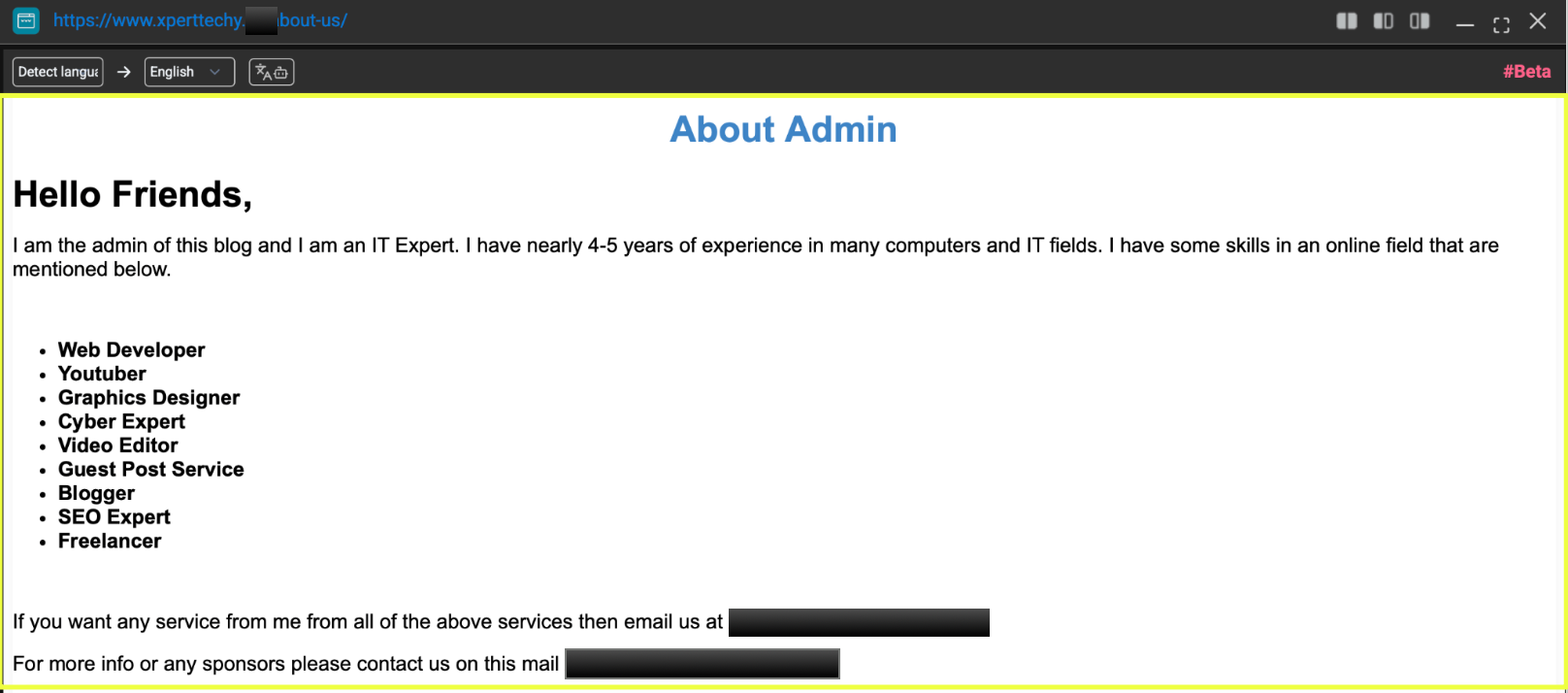 |
Within the “About” section, a contact email was listed:
- xpertt*******6@gmail.com
 |
This was the first instance where a direct email address could be associated with the broader activity observed across forums and Telegram. Unlike earlier findings that turned out to be placeholder data, this email appeared consistently within the site’s content, suggesting it was actively maintained by whoever controlled the domain.
At the same time, the positioning of the website stood in contrast to the earlier findings. While forum threads and Telegram channels focused on promoting RATs, crypters, and other tools, the website presented a more neutral and in parts, legitimate image. Pages encouraging guest contributions and tech blogging did not reference any of the tools seen elsewhere.
A second domain, https://www.xperttechy.***, also appeared during the investigation. While its exact role was less clear, the similarity in naming suggested a possible connection to the same operator or setup.
These elements point to a layered approach. On one side, there is visible activity across forums and Telegram focused on tool promotion. On the other, there is a surface web presence that presents itself as a standard tech platform, with identifiable contact details. The overlap between these layers provides additional signals that help connect what might otherwise appear as separate pieces of activity.
Cross-Platform Presence and Onion Activity
As the investigation progressed, the same patterns began appearing across a wider range of platforms, extending beyond the initial forums already identified. Using StealthMole’s Dark Web Tracker, additional threads were found on sites such as:
- http://www.n***t-o***x.**/threads/1***0/
- https://nif****m.w****/threads/silent-crypto-miner-builder-monero-xmr.124186/
- https://crd****w.**c/threads/port-forwarding-rdp-server-for-using-rats.33***4/
- https://www.turk****am.org/ko****r/silent-crypto-miner-builder-monero-xmr.20***5/
- http://www.cracki****.com/threads/50691/latest
- https://alphv.****/threads/96**7/
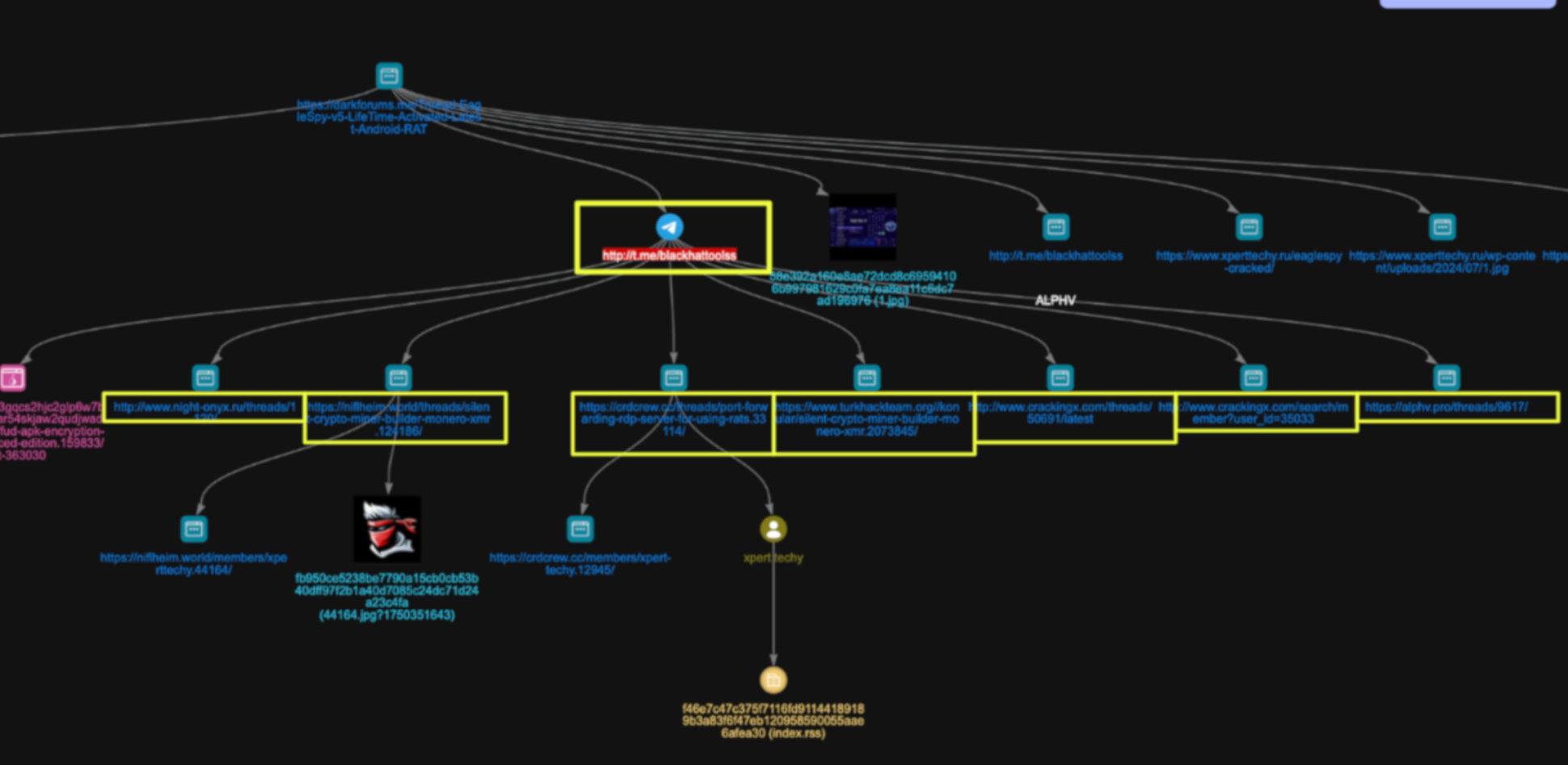 |
Across these platforms, the usernames varied slightly including “xpert techy,” “xperttechy,” and “mark oliver.” Despite these differences, the structure of the posts remained familiar: tool promotion, brief descriptions, and redirection toward Telegram for further interaction.
A notable addition during this phase was the identification of an onion-based forum thread:
- http://bdfclub********************qudjwad.onion/threads/fud**************advanced-edition.159833/post-363030
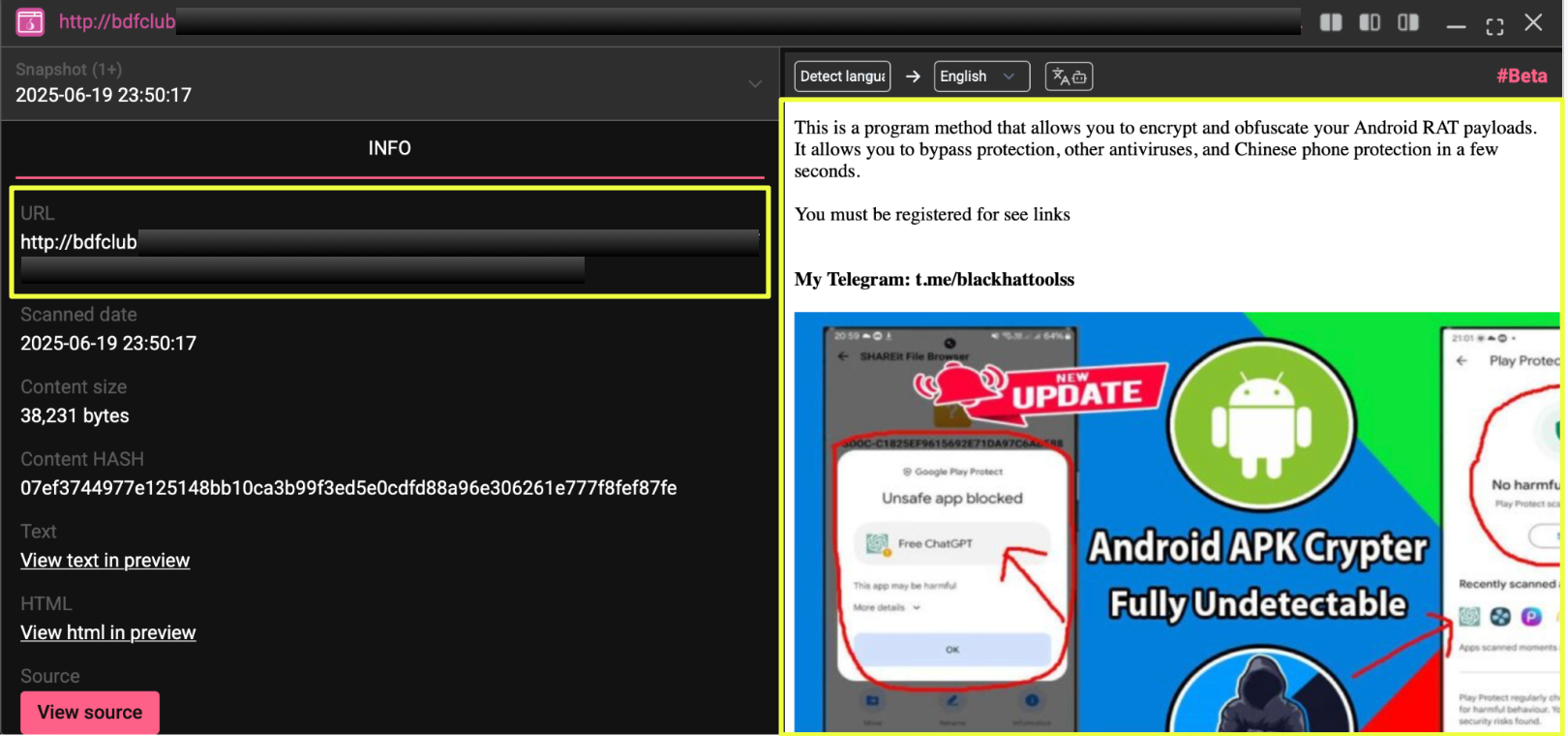 |
This thread, posted by “markoliver,” promoted an APK encryption method and included the same Telegram contact seen earlier. The presence of this activity on a Tor-based platform added another layer to the investigation, indicating that the same promotional approach was being used across both clearnet and dark web environments.
What stands out across all these findings is the consistency rather than the scale. The same types of tools, similar posting formats, and recurring contact points appeared regardless of the platform. Whether on regional forums, larger cracking communities, or onion services, the approach remained largely unchanged.
This consistency made it possible to connect activity across different usernames and platforms without relying on a single identifier. Instead, it was the repetition of patterns: how the tools were presented, where users were directed, and how contact was established, that tied these pieces together.
Operational Pattern and Tool Distribution Strategy
Looking across all the identified threads, channels, and websites, a consistent pattern begins to take shape in how the operation is structured. The activity does not rely on a single platform or identity. Instead, it follows a layered approach where each component plays a specific role.
Forum posts appear to serve as the entry points. Across platforms, the content is kept simple: short descriptions, feature highlights, and claims around functionality. These posts are not overly detailed, but they are frequent and spread across multiple communities, increasing visibility without drawing too much attention to any single account.
From there, users are directed toward Telegram. This is where interaction likely moves from public to private. The repeated appearance of channels such as t.me/blackhattoolss and t.me/tools4alll, along with the admin handle @real*********s, suggests that Telegram acts as the primary coordination layer: handling communication, follow-ups, and possibly transactions.
The inclusion of external websites adds another layer. Pages like the Google Sites storefront and the proofs page provide a sense of structure, giving the operation a more organized appearance. At the same time, domains such as xperttechy.*** introduce a different kind of presence, one that blends in with regular web content while still linking back to the broader activity.
Another noticeable aspect is the range of tools being promoted. Instead of focusing on a single product, the activity spans Android RATs, Windows RATs, crypto-related tools, crypters, and mining utilities. This suggests a distribution model rather than development, where the goal is to offer a variety of tools to attract a wider audience.
Overall, these elements point to a setup that is designed for reach and continuity. If one platform or account becomes inactive, others can continue operating without disruption. The repetition of the same structure across different environments makes the activity easier to trace, but also highlights a deliberate and reusable approach rather than isolated or one-off posts.
Conclusion
What started as a single forum thread gradually unfolded into a broader network of activity spread across multiple platforms. By following small but consistent details: usernames, contact links, and repeated posting patterns, it became possible to connect what initially appeared to be unrelated pieces.
The investigation shows that this activity is not limited to one identity or one platform. Instead, it relies on a combination of forum presence, Telegram-based communication, and supporting web infrastructure. Each layer plays a role, whether it is attracting users, maintaining contact, or reinforcing credibility.
A key takeaway is the reuse of the same elements across different environments. Variations in usernames or platforms did not change the underlying structure. The same types of tools were promoted in similar ways, and users were consistently directed toward shared communication channels. This consistency made it possible to map connections without relying on a single definitive identifier.
The presence of both overt tool promotion and a more neutral-looking web platform adds another layer to the activity. Rather than operating entirely in one space, the setup blends into different environments, making it less obvious when viewed in isolation.
Overall, the findings point toward a coordinated distribution effort rather than scattered activity. The strength of this operation lies not in any single component, but in how these components work together to create a connected and persistent presence across platforms.
Editorial Note
Investigations involving underground forums and fragmented online identities rarely provide absolute certainty, especially when actors deliberately reuse aliases and operate across multiple platforms. What can be established, however, are patterns: consistent behaviors, repeated contact points, and overlapping infrastructure that, when viewed together, form a reliable picture of activity.
This case highlights how small, seemingly disconnected traces can be pieced together through StealthMole, allowing analysts to navigate uncertainty and build a structured understanding of complex, multi-layered operations.
To access the unmasked report or full details, please reach out to us separately.
Contact us: Support
.svg)
.svg)
.svg)