From RuSilkRoad to Hydra: Tracking Darkweb’s Largest Market Consolidation and Its Afterlife
What began as a routine attempt to map the remnants of the Russian Silk Road, a short-lived and relatively obscure darknet marketplace, quickly shifted into a far more revealing investigation. Although the Russian Silk Road never grew into a major ecosystem, its scattered traces pointed us toward a web of successor markets, abandoned infrastructure, and resurfaced domains that continued to circulate long after the platform itself faded. Those early breadcrumbs became the starting point for uncovering a much broader Hydra-branded shadow network.
As we followed these links, we found that the real story was not the Russian Silk Road itself, but the way its era overlapped with the rise and later fragmentation of Hydra Market. Former mirrors, leaked user discussions, and forgotten onion domains began connecting to modern Telegram channels, “rebuild” forums, and opportunistic brand hijacks, some positioning themselves as Hydra’s legitimate successors, others disguising ransomware operations beneath the Hydra name. What emerged was a picture of a darknet landscape where infrastructure never fully disappears; it simply reappears repurposed, rebranded, or weaponized.
This report traces that unexpected evolution: from dead markets resurfacing in 2020-era DWH threads, to Hydra-linked domains active as late as 2023, to Telegram groups hosting data leaks, wallet sales, and donation addresses under the Hydra banner. The goal is not to retell the history of these marketplaces, but to illustrate how old brand identities continue to be exploited long after takedowns. The full investigation uncovers an ecosystem where the Hydra name, once tied to a massive criminal enterprise, has become a tool leveraged by threat actors seeking legitimacy, attention, or profit.
Incident Trigger & Initial Investigation
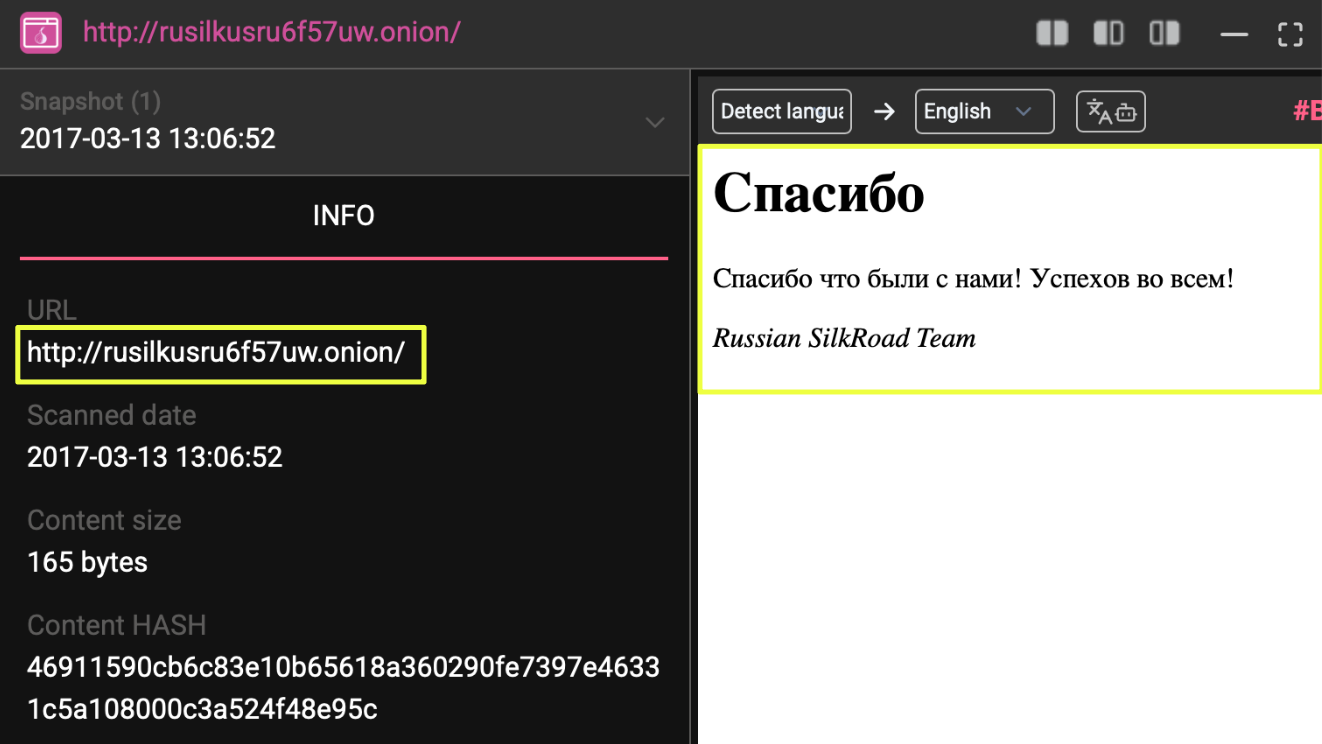
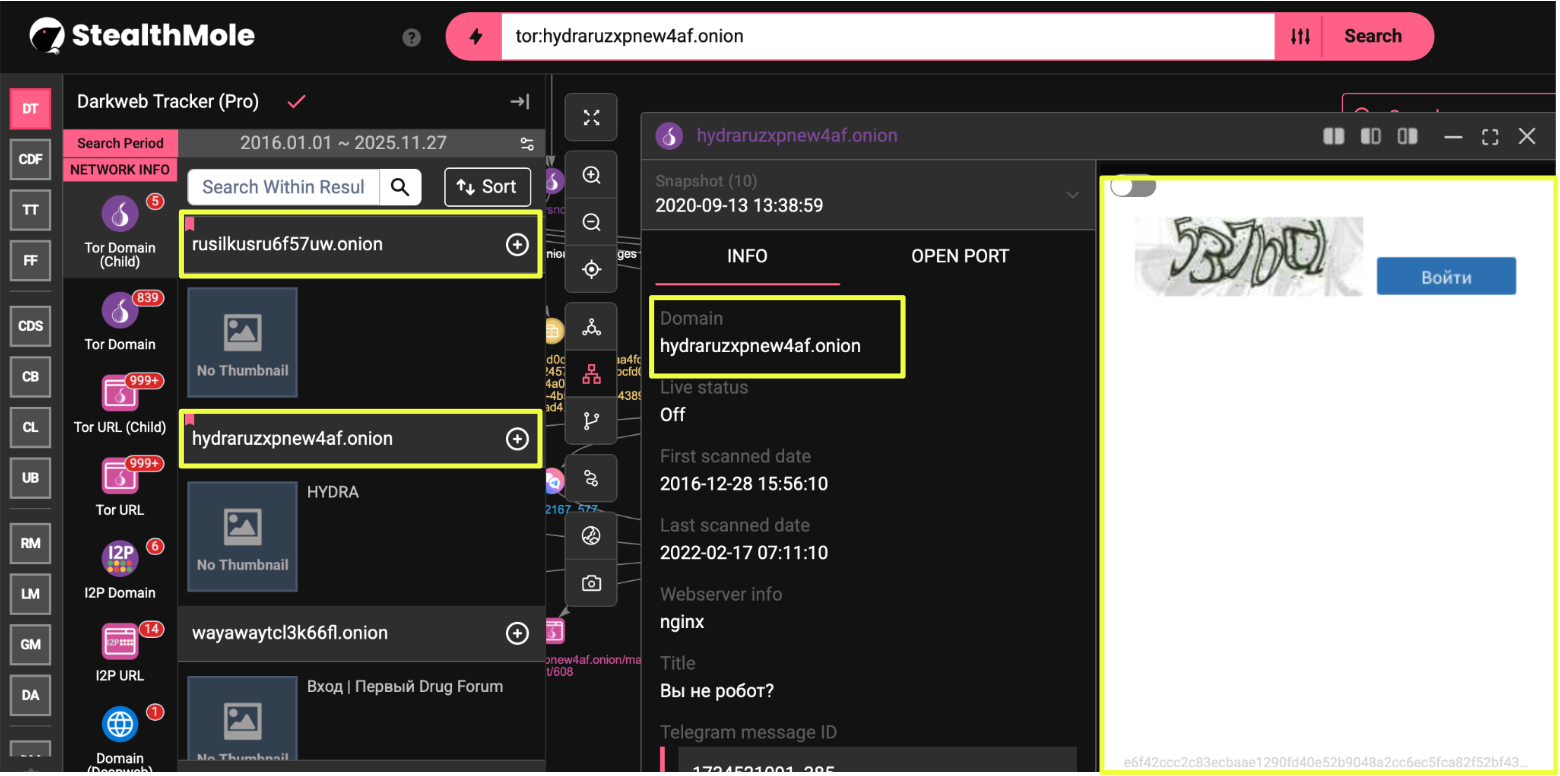
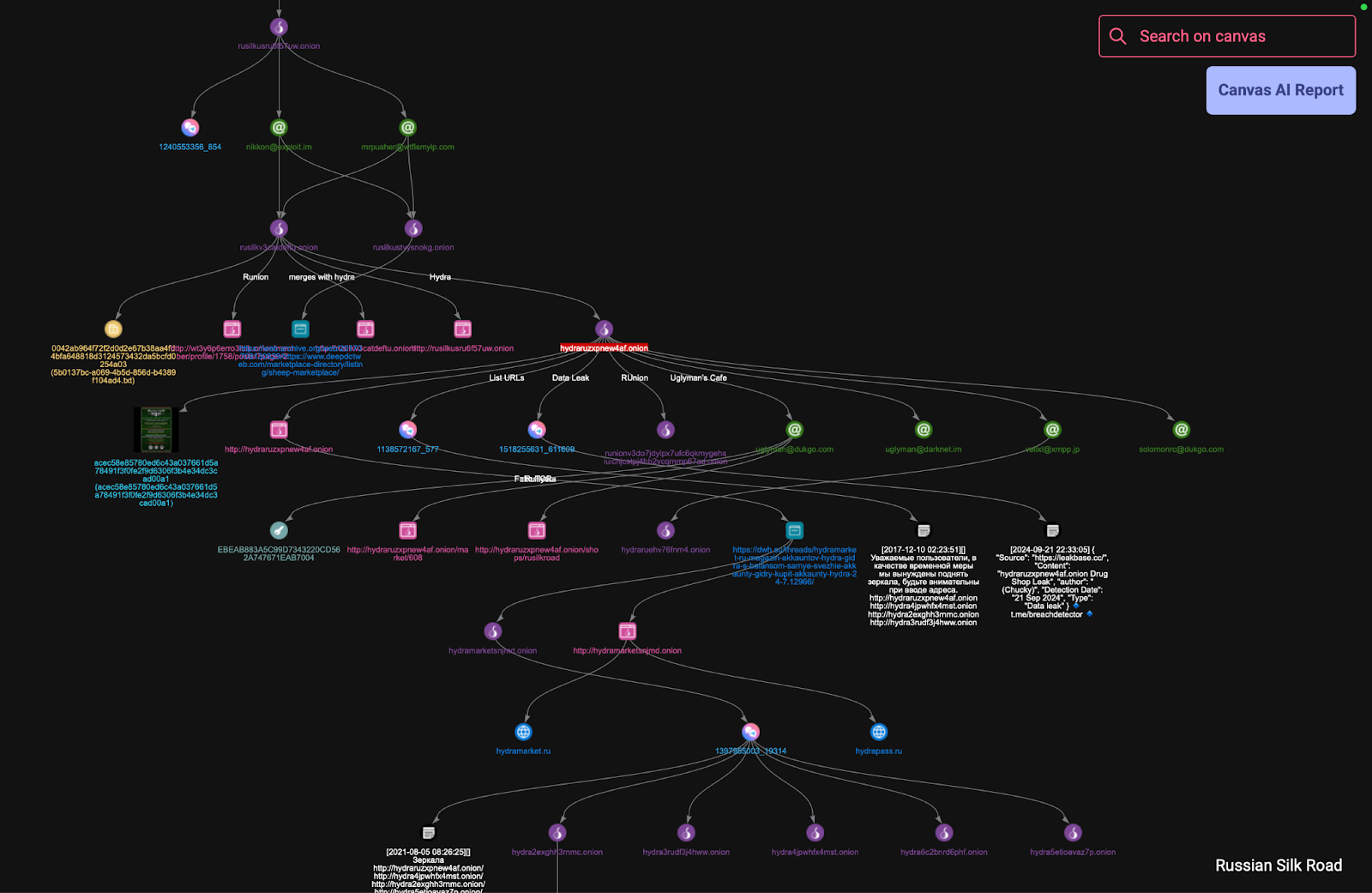
The initial focus on the Russian Silk Road was intended to be a contained assessment of a small, relatively inactive darkweb marketplace. Its limited footprint and short operational lifespan suggested that whatever remained would be minimal, likely a handful of dormant domains and outdated references. However, even the earliest pivots indicated that the platform’s residual infrastructure extended further than expected. The primary marketplace domain, http://rusilkusru6f57uw.onion, and its associated forum at http://rusilkustvysnokg.onion, continued to appear across darkweb years after the marketplace itself had dissolved.
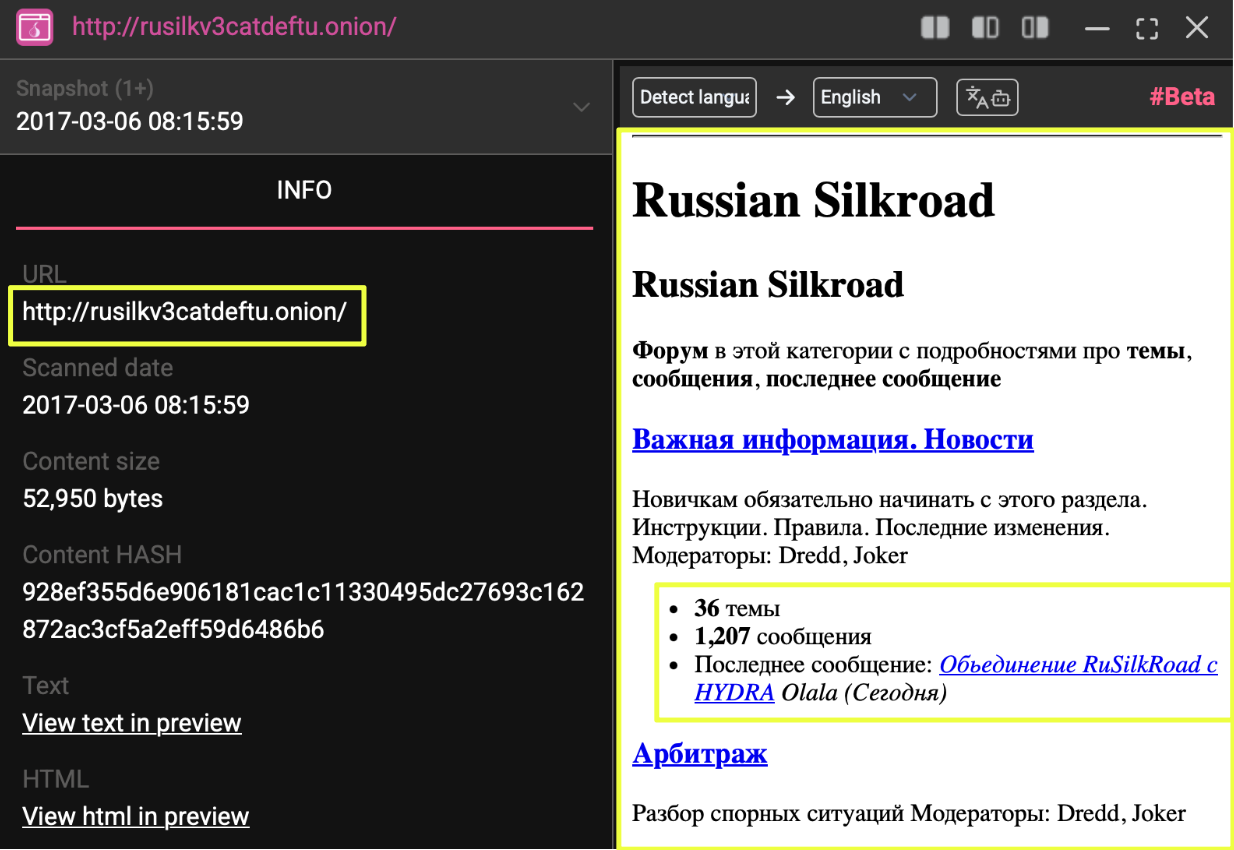
The repeated appearance of these connections suggested that Russian Silk Road’s remnants did not simply expire with the marketplace. Instead, they appeared absorbed into a broader ecosystem, with certain operational elements persisting across multiple successor sites. This became most evident when one of the linked Russian Silk Road domains, http://rusilkv3catdeftu.onion, displayed a merger notice involving Hydra Market. While the Russian Silk Road never achieved significant scale in its own right, the presence of this announcement provided a direct and verifiable bridge into a much larger and more organized darknet environment.
This pivot reframed the investigation. Rather than cataloging the final artifacts of a minor marketplace, the analysis shifted toward understanding how its infrastructure had been repurposed or integrated into Hydra’s operational footprint. The value of the Russian Silk Road was no longer in its individual activity, but in how the traces it left behind helped reveal transitions within the Russian-speaking darkweb ecosystem as a whole.
Following the Merge Into Hydra’s World
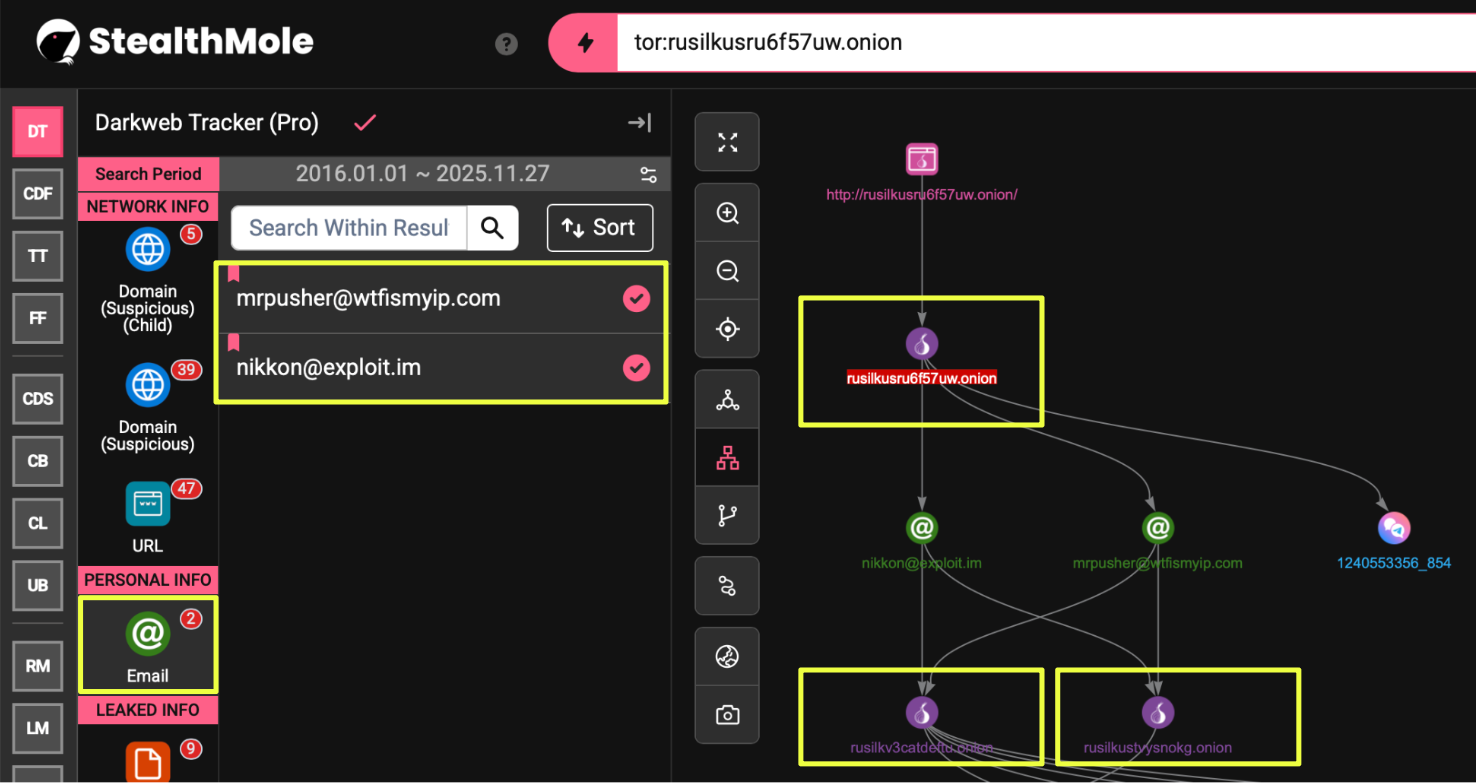
Once the merger reference surfaced on the Russian Silk Road–linked domain rusilkv3catdeftu.onion, the investigation naturally shifted toward examining how its infrastructure intersected with the early operational footprint of Hydra Market. At that point, the objective became understanding why multiple Russian Silk Road–related onion addresses, including rusilkusru6f57uw.onion (marketplace) and rusilkustvysnokg.onion (forum), continued to appear in correlation results long after the marketplace itself had faded.
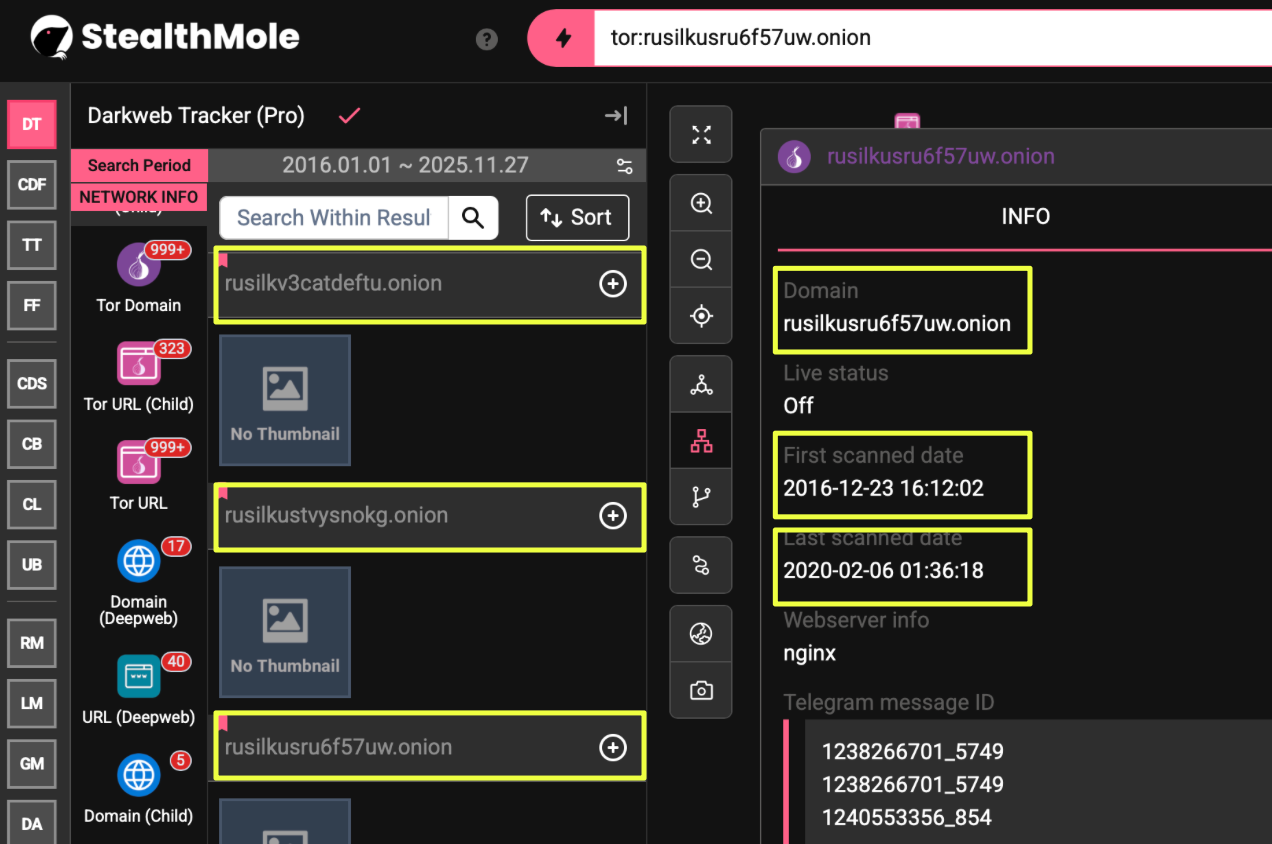
Early pivots revealed that identifiers associated with Russian Silk Road, particularly the emails nikkon@exploit.im and mrpusher@wtfismyip.com, were also tied to other domains that were clearly part of the Hydra-era landscape. These included rusilkv3catdeftu.onion itself as well as additional domains that connected outward into Hydra’s broader ecosystem. The appearance of these same identifiers across multiple onion services suggested that, during the transition, certain operational components or actors migrated alongside the marketplace merger rather than disappearing with the Russian Silk Road.
As the pivots expanded, Hydra’s infrastructure quickly became the dominant presence in the dataset. Several Hydra-linked domains surfaced through StealthMole’s historical tracking, most notably hydraruzxpnew4af.onion, which displayed long-term activity from 2016 through early 2022. Additional mirrors (see below) reinforced the pattern of a distributed and resilient network of Hydra entry points, many of which circulated through user discussions and Telegram channels. These domains were not isolated; they consistently intersected with the same clusters of references in darknet forums, mirror lists, and archived Hydra-related content.
- hydraruehv76fnm4.onion (active April–May 2017)
- hydramarketsnjmd.onion (active January 2020–June 2021)
These findings made it clear that the remnants of Russian Silk Road acted less like an abandoned marketplace and more like an embedded pathway into Hydra’s expanding operational footprint. Instead of a clean break between the two platforms, the investigation revealed a gradual blending of infrastructure, where older Russian Silk Road domains persisted as part of the wider Hydra ecosystem. This shift marked a turning point in the analysis, redirecting the effort toward mapping Hydra’s distributed presence and understanding how these interconnected domains contributed to the marketplace’s overall resilience.
Hydra’s Operational Footprint and Infrastructure Indicators
As the investigation moved deeper into Hydra-linked domains, the scale and structure of the marketplace’s operational footprint became increasingly visible through surviving artifacts. The domains identified through historical tracking were not simply isolated mirrors but part of a broader configuration that reflected how Hydra maintained accessibility, redundancy, and distribution across its user base. Several of the active domains displayed consistent marketplace layouts, product listings, vendor interfaces, and regional segmentation that aligned with Hydra’s known operational model prior to its takedown.
The primary domain uncovered, hydraruzxpnew4af.onion, provided the clearest representation of Hydra’s core marketplace structure. Archived views of the site showed extensive drug listings, vendor storefronts, localized distribution options, and an interface built around standardized categories and regional filtering. Additional pages referenced affiliated forums, communication channels, and partner marketplaces, one of which explicitly listed “RuSilkRoad” among its associated communities, aligning with the merger announcement discovered earlier. These elements demonstrated that Hydra had incorporated and centralized activity from multiple smaller markets, forming an ecosystem where former independent services operated under a consolidated framework.
Other recovered mirrors, including hydraruehv76fnm4.onion and hydramarketsnjmd.onion, displayed varying degrees of functionality but consistently pointed back to the same marketplace identity. Although the content depth varied across domains, the recurrence of Hydra’s branding, interface patterns, and operational language suggested a coordinated system of alternate entry points rather than unrelated impersonations. The presence of promotional material, such as product posters and vendor advertisements, further illustrated how Hydra maintained an extensive network of user-facing resources distributed across multiple hidden services. These artifacts reinforced the understanding that Hydra operated with a deliberate focus on infrastructure elasticity, allowing the marketplace to remain accessible despite frequent disruptions and targeted pressure from law enforcement.
This cluster of findings established Hydra not as a single domain but as a multi-layered infrastructure that leveraged mirrors, partner communities, and distributor networks to maintain continuity.
Post-Takedown Activity and the Emergence of Hydra-Branded Imitators
The formal takedown of Hydra in April 2022 should have marked a clear endpoint in its operational lifecycle, yet the infrastructure uncovered during this investigation demonstrated the opposite. Instead of disappearing, Hydra’s name and visual identity began reappearing across a new set of onion services, Telegram channels, and clearnet domains that were active months, and in some cases more than a year, after the marketplace was seized. These services did not replicate the original marketplace structure; rather, they adopted Hydra’s branding to establish credibility while promoting activity unrelated to the platform’s historical purpose.
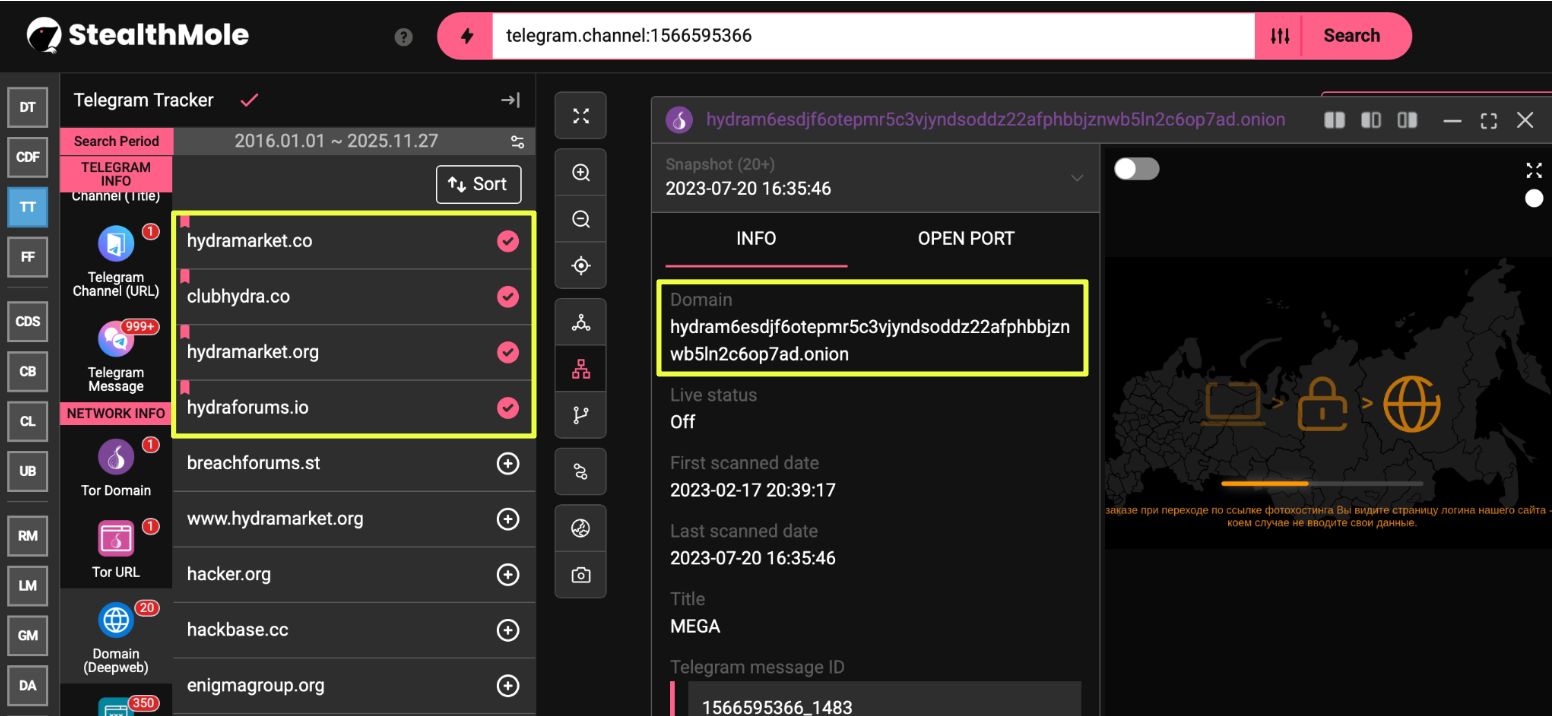
A key pivot came from the discovery of a domain listed in OFAC records, which StealthMole data showed operating between February and July 2023. Although positioned as a Hydra-associated address, its interface and content diverged sharply from legitimate Hydra mirrors. The domain displayed a graphic-heavy landing page without marketplace functionality, suggesting it was a later-stage impersonation rather than an operational continuation of the original marketplace. Its appearance on sanctions lists further indicated that post-takedown Hydra branding attracted a mixture of opportunistic operators and unrelated threat actors attempting to benefit from the platform’s historical notoriety.
- hydram6esdjf6otepmr5c3vjyndsoddz22afphbbjznwb5ln2c6op7ad.onion
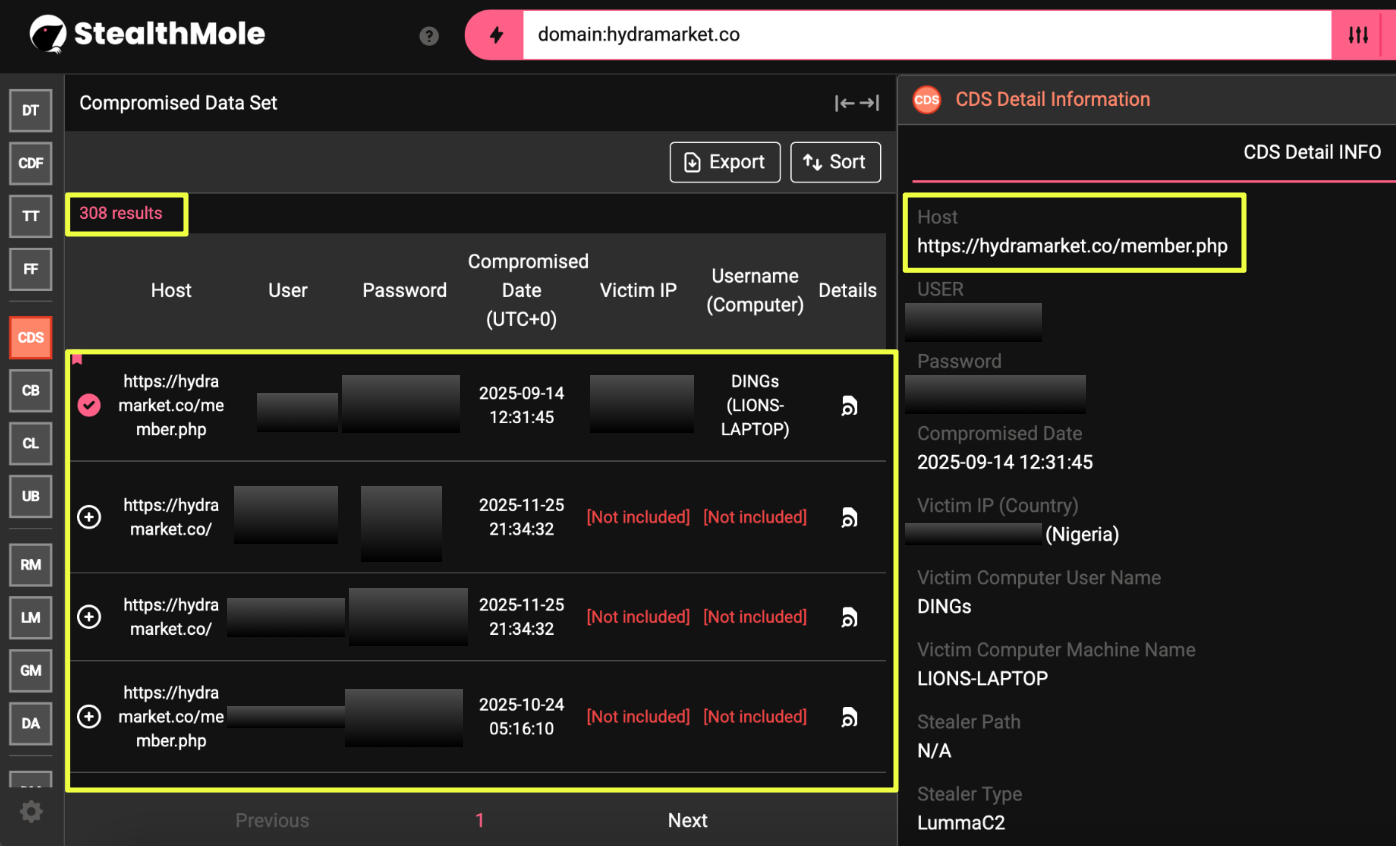
The associated Telegram channel, @hydramarketrebuild, reinforced this trend. Messaging within the channel referenced supposed “restructuring” and portrayed the group as a continuation of Hydra Market, despite the absence of any verifiable connection to its former administrators or vendors. The channel’s activity centered on database leaks, ransomware-style announcements, and offers involving stolen wallet.dat files, none of which aligned with Hydra’s traditional marketplace operations. Additional channels promoting the same ecosystem linked users to clearnet domains such as hydramarket.co, hydraforums.io, clubhydra.co, and hydramarket.org, indicating a coordinated attempt to rebuild a Hydra-branded presence outside of Tor.
StealthMole’s compromised-data results further confirmed the nature of these imitators. Queries against hydramarket.co produced over 300 leaked credentials across both the Compromised Data Set and ULP Binder, suggesting that the platform had either been breached or was designed to harvest user information from the outset. Unlike the controlled environment of the original Hydra, these services displayed limited operational security and overlapping infrastructure indicative of loosely organized groups leveraging Hydra’s brand value rather than reconstituting its marketplace. These findings marked the beginning of a clear divergence between Hydra’s authentic legacy and the fragmented ecosystem of post-takedown imposters.
Ransomware-Linked Activity and Cryptocurrency Signals
As the investigation expanded across the Hydra-branded imitator network, a consistent pattern emerged: the services adopting Hydra’s name were no longer attempting to recreate a marketplace. Instead, much of the observable activity aligned more closely with ransomware operations, data extortion channels, and opportunistic monetization schemes.
The Telegram ecosystem associated with these domains provided the clearest window into this shift. Channels tied to the impersonator network, such as @hydramarketrebuild and related repost hubs, regularly circulated breach announcements, corporate data leaks, and promotional material unrelated to narcotics or marketplace activity. Mentions of compromised infrastructure belonging to organizations in France, Italy, and other regions appeared alongside offers for stolen wallet.dat files, reinforcing that these groups were operating within a ransomware or data-broker model rather than attempting to restore Hydra’s original service structure.
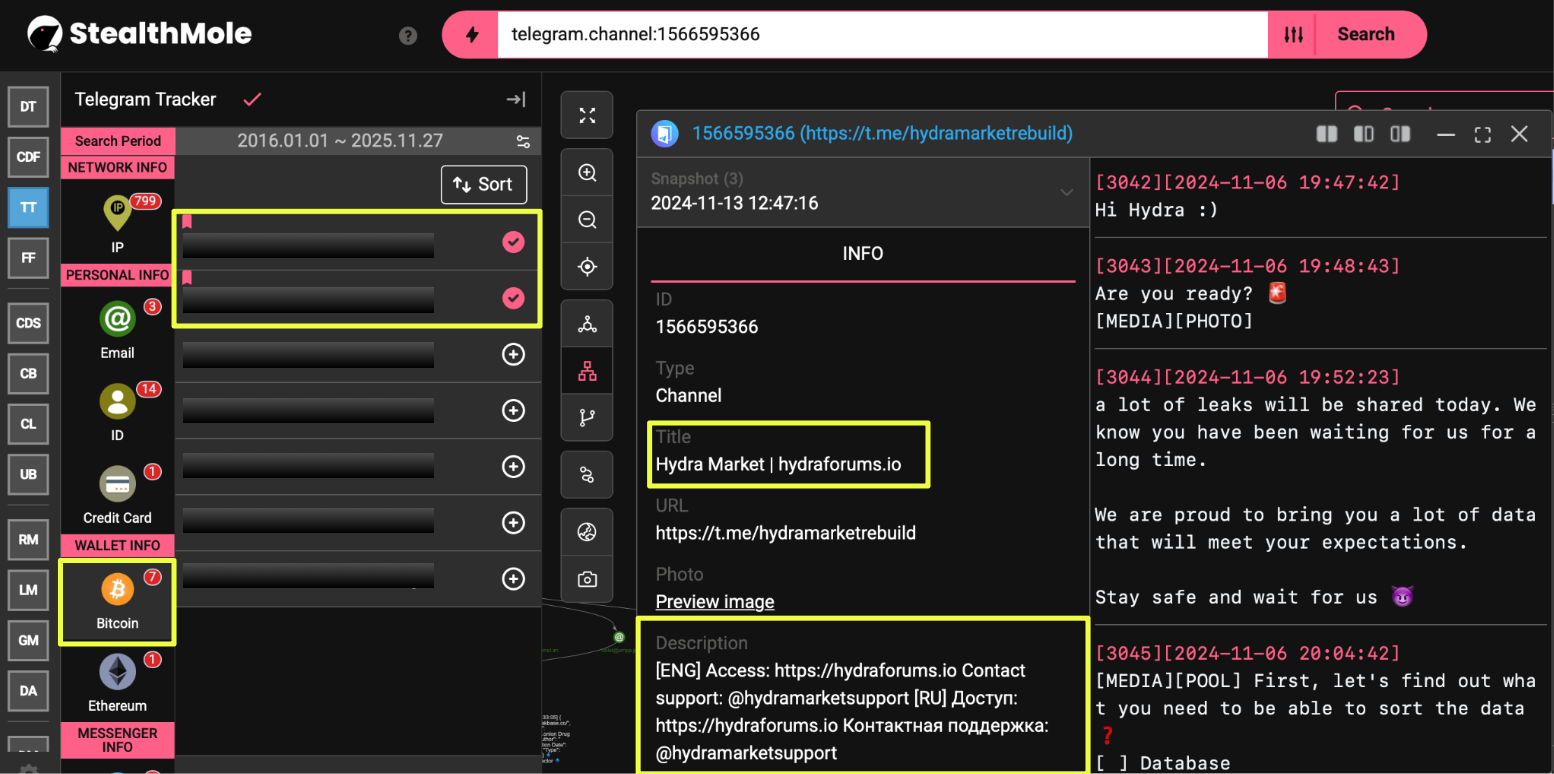
Cryptocurrency activity within the imitator ecosystem supported this assessment. While the original Hydra marketplace avoided public donation addresses and handled payments internally, the impersonator network openly displayed Bitcoin wallets for contributions and transactional use. The wallet 1Hydra**************v, identified within the Telegram channel, was framed as a “Hydra donation wallet,” a practice inconsistent with the operational behavior of the pre-takedown marketplace. Additional wallets surfaced alongside posts advertising wallet recovery, private key access, or cryptocurrency-related tools, further indicating a pivot toward financially motivated cybercrime rather than marketplace facilitation.
A separate wallet identified during the investigation appeared within the ecosystem but did not correspond directly to any established Hydra function. Activity patterns and transactional context suggested its use in vendor-level or opportunistic services rather than a continuation of Hydra’s original payment infrastructure. The presence of multiple, publicly posted wallets demonstrated that these entities were not reviving Hydra but leveraging its name to draw traffic into ransomware-aligned operations.
- bc1*********************************q
Taken together, the intersection of visible ransomware activity and loosely controlled cryptocurrency endpoints indicated that the Hydra brand was being retooled to support a different category of threat actor. These groups appeared to rely on Hydra’s recognizability to create an initial layer of credibility before directing users toward activities centered on data theft, extortion, and opportunistic financial gain. This emerging pattern helped clarify that the Hydra-branded environment active post-2022 represented not a true successor marketplace, but a cluster of actors using the brand as a convenient launching point for broader cybercriminal campaigns.
Assessment
The combined evidence indicates that the modern Hydra-branded ecosystem does not represent a continuation of the original marketplace but rather a loose collection of opportunistic actors leveraging the name for visibility. The surviving Hydra infrastructure identified in earlier stages, particularly the long-running mirrors and pre-takedown sites, reflects the operational practices of the authentic platform. In contrast, the entities active after 2022 lack the structural coherence, vendor networks, and transactional depth that defined Hydra during its operational peak.
The services currently using the Hydra name operate with markedly different priorities. Their focus on breach data, ransomware-style announcements, and cryptocurrency solicitation suggests a shift toward short-term extraction rather than marketplace facilitation. These channels present none of the hallmarks of established vendor ecosystems or user-driven market governance. Instead, they exhibit characteristics typical of opportunistic cybercrime groups: public-facing cryptocurrency addresses, inconsistent branding, and infrastructure that changes frequently, likely to minimize exposure or capitalize on fleeting interest.
The appearance of Hydra-associated clearnet domains with large volumes of leaked user credentials further underscores the absence of operational integrity among the impersonator groups. Whether these compromised datasets resulted from platform breaches or deliberate credential harvesting, their existence demonstrates a lack of security practices and highlights the risks faced by individuals attempting to engage with these services. The fragmentation and inconsistency across these domains reinforce the conclusion that no unified or coordinated successor to Hydra is currently active.
Overall, the collected data suggests that the Hydra name has transitioned from a marketplace identifier to a general-purpose brand co-opted by unrelated actors. These groups appear to rely on the residual recognition associated with Hydra to legitimize their operations, attract victims, or frame themselves as credible entities within the broader criminal landscape. While some infrastructure carries forward traces of earlier domains, there is no evidence that any post-takedown activity is linked to authentic Hydra operators or maintains continuity with the platform’s former structure.
Conclusion
What initially appeared to be a set of isolated, outdated domains instead revealed how infrastructure can persist, reattach itself to newer ecosystems, and form unexpected connections long after a marketplace becomes inactive. These artifacts helped clarify transitions within the Russian-speaking darkweb, particularly the way smaller communities were absorbed into Hydra’s network during its expansion.
After Hydra’s dismantling, the environment changed again. Instead of a central marketplace emerging to replace it, the Hydra name fragmented across unrelated groups and services that repurposed the label for their own objectives. These actors adopted familiar branding but lacked the organizational cohesion, merchant activity, or stable infrastructure that once defined Hydra. Their operations, spread across onion sites, Telegram channels, and clearnet domains, reflect the opportunism that frequently follows the collapse of major darknet platforms.
What becomes clear through this investigation is that major darknet identities tend to persist in fragmented forms long after their core infrastructure is gone. The reputation of a platform can outlive its operators, creating opportunities for unrelated actors to reattach themselves to a familiar label. The modern Hydra-branded environment fits this behavior, its components function independently, using the name as a recognizable symbol rather than maintaining any operational link to the original market.
Editorial Note
As with all darkweb investigations, the findings in this report represent only what could be observed and correlated at the time of analysis. Marketplace infrastructure, impersonator networks, and affiliated communication channels frequently shift, disappear, or re-emerge under new identifiers, and visibility into hidden services is inherently partial.
The conclusions presented here reflect a snapshot of Russian Silk Road and Hydra-linked activity based solely on verifiable domains, timestamps, and artefacts surfaced through StealthMole’s tracking capabilities. The aim is not to capture every possible branch of this ecosystem, but to demonstrate how structured, evidence-based analysis can reveal meaningful patterns within environments that are, by design, unstable and continuously evolving.
To access the unmasked report or full details, please reach out to us separately.
Contact us: support@stealthmole.com
Labels: Darkweb Marketplace

.svg)
.svg)
.svg)